Featured News
-
 144News
144NewsWebsite of Nepali Embassy in US hacked, left with anti-American content
The official website of embassy of Nepal in Washington was hacked by a group of Moroccan hacker not happy with American invasion of Iraq and...
-
 76Cyber Crime
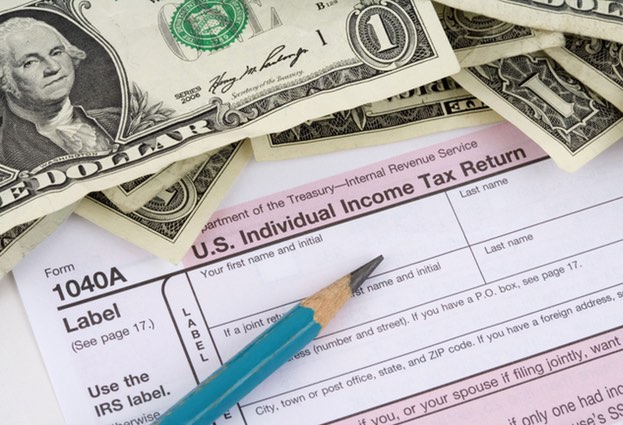
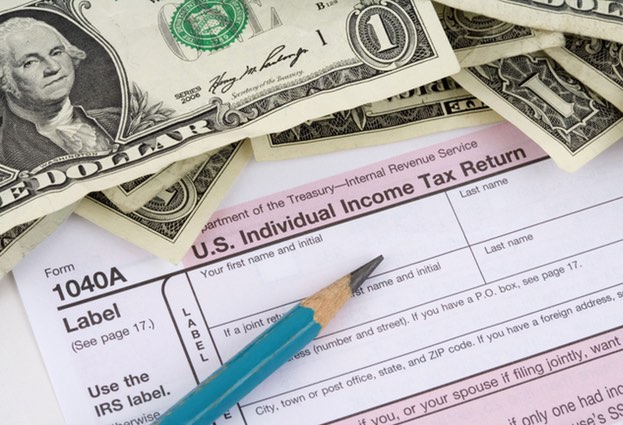
76Cyber CrimeIRS hacker attack puts US tax payers at risk
The IRS has admitted that for more than two months malicious hackers targeted its systems, and managed to gain access to information...
-
 333Cyber Crime
333Cyber CrimeUsing middle finger emoji in UAE: A crime that could land you in court
Dubai: If you are living in UAE, you should know the dangers of flipping middle finger at someone as it could land you in prison. Nonetheless,...
-

 215How To
215How ToHow To Add Pattern Lock Security On Windows
Every Android user should be familiar with pattern lock security system. Every Smartphone has the option called Patter Lock which is very popular...
-

 103Privacy
103PrivacyBluetooth fitness trackers ‘a threat to privacy’
Devices using Bluetooth Low Energy (BLE) to transmit their data can be intercepted by hackers, potentially exposing a trove of fitness data...
-

 389Password
389PasswordDissecting Linux/Moose: a Linux Router‑based Worm Hungry for Social Networks
A malware family that primarily targets Linux-based consumer routers but that can infect other Linux-based embedded systems in its path: Dissecting Linux/Moose.
-
 221Cyber Crime
221Cyber CrimeMoose – the router worm with an appetite for social networks
A new worm is infecting routers in order to commit social networking fraud, hijacking victims' internet connections in order to "like" posts...
-
 271Geek
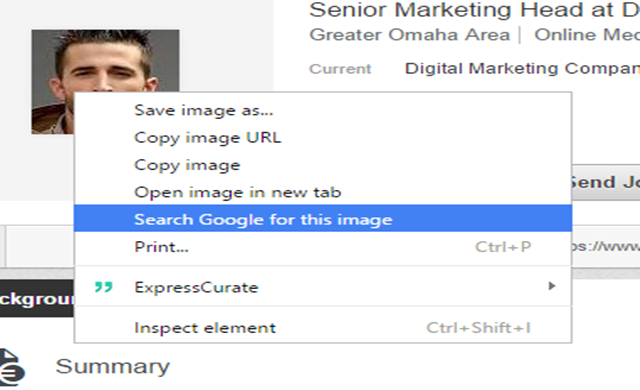
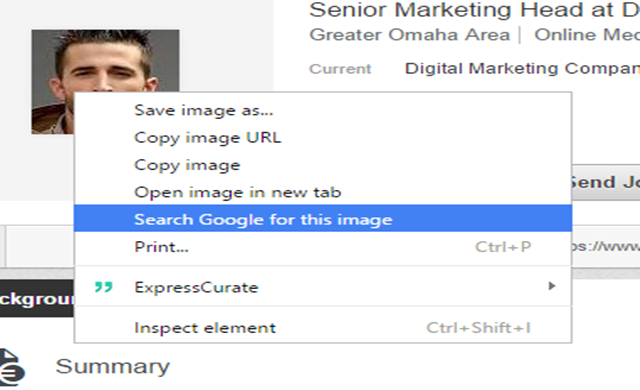
271GeekIdentifying Fake Social Media Profiles Possible with Google Image Search
Creating fake social media accounts has been the favorite trick of hackers and scammers for interacting with potential victims. However, thanks to...
-

 303Cyber Events
303Cyber EventsTeen hires attacker to DDoS his school district
A high school boy might have to face state and federal charges for allegedly hiring a third party and launching a DDoS...
-

 234Geek
234GeekDoes Wi-Fi Makes People Sick? Probably Yes!
From using PCs and cell phones to watch online movies and playing games, wireless technology has advanced greatly and made life easier...
-

 399News
399NewsHackers target Bitcoin Exchange BitFinex’ Hot Wallet
Reportedly BitFinex was hacked but due to strict security measures implementation just minimal amount was lost. BitFinex keeps more than 99.5% of...
-

 293How To
293How ToTips To Keep Your Android Device Safe and Sound
It would not be an exaggeration to say that the present age is the age of smartphones. They have invaded our lives...
-

 152Hacked
152HackedMozilla: Firefox Tracking Protection Speeds Up Web Pages by 44%
Do you know that not all web sites honor the native Do Not Track feature of your web browser? Even in the...
-

 69Cyber Crime
69Cyber Crime5 hackers who came over from the dark side
Five reformed hackers who turned their lives around to help in the fight against cybercrime, leaving their blackhat past behind.
-
 158Hacking Tutorials
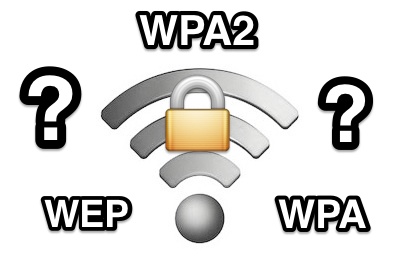
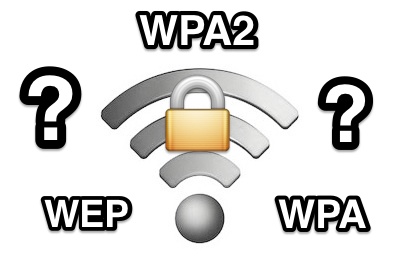
158Hacking Tutorials6 Ways to Secure a Wireless Wi-Fi Network
Wireless Networking (Wi-Fi) has made it so easy for anyone to use Internet on your computer, mobile phones, tablets and other wireless...
-

 266Hacked
266HackedNSA Prepares to SHUT DOWN Mass Phone Tracking Program
As a result of a midnight session, the American Senate has voted down the USA Freedom Act- the basis of NSA’s mass...
-

 289News
289NewsAnonymous Breaches Thailand Senate Website against Human Trafficking
The online hacktivist Anonymous breached into the official website of Thailand Senate and Public Health Ministry, ending up leaking login credentials against country’s alleged...
-

 241News
241NewsWebsite of Uzbek Embassy in Kuwait hacked by anti-Assad Hacker
The anti-Bashar Al Assad hacker from Syria hacked into the official website of Uzbekistan Embassy in Kuwait and demanded governments around the world...
-
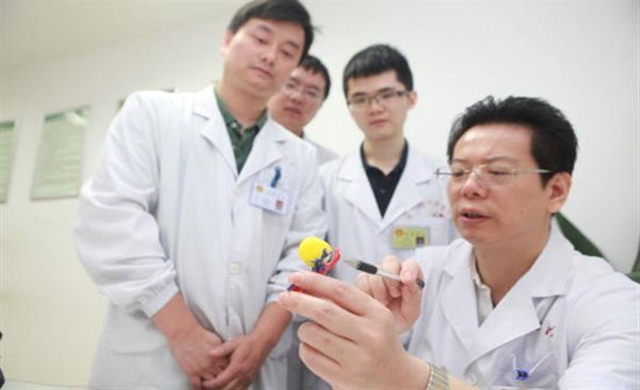
 290Geek
290GeekMiracle Miracle! A woman’s kidney tumor cured by 3D printing
When it’s about performing surgeries on vital organs, today’s advanced imaging techniques such as CT scans, MRIs and ultrasound machinery have made...
-

 319Surveillance
319SurveillanceThese Iris scanners can now identify people from 40 feet away
It’s a high point for “Biometric technology” as in the latest advancement now. It is possible to record data about an individual’s...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




