Featured News
-
 226How To
226How ToFind Out What Your Name Would be if You Were Born Today
Our name is an integral part of our existence and this is our basic identity. But the way people name their children...
-
 263How To
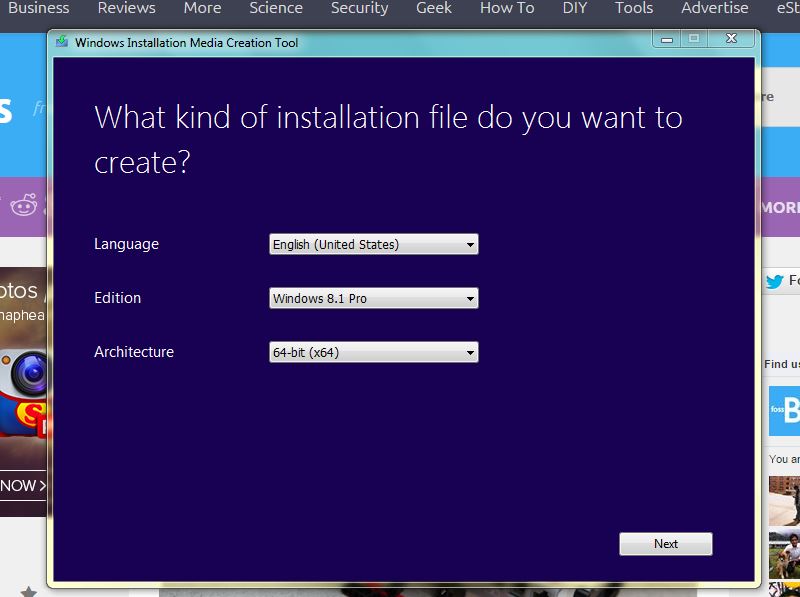
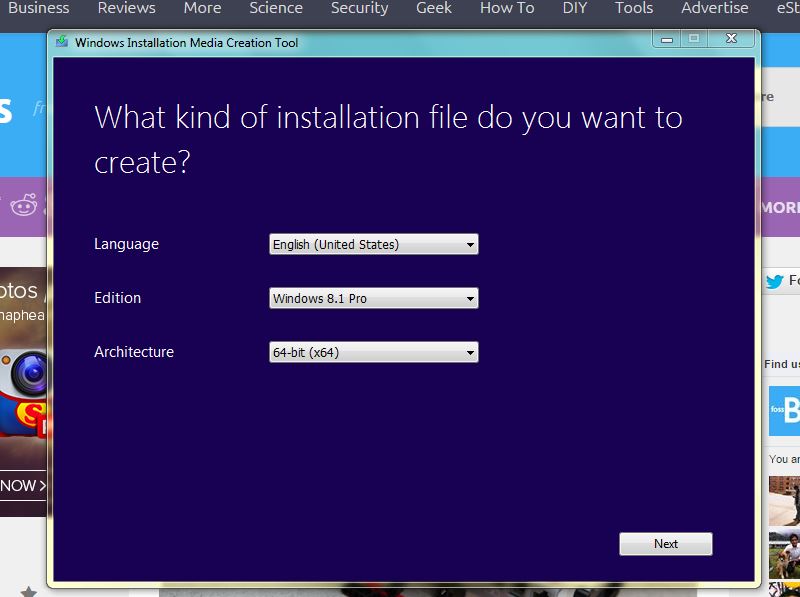
263How ToHow to Download Windows 8.1 Legally Without Product Key
Installing a fresh Windows 8.1 hasn’t been the easiest thing in the world till now as Windows 8 users needed a licensed...
-
 238Hacked
238HackedHack United Airlines Website and Get Paid in Million Miles
Are you good at programming and do you call yourself a computer expert? Here’s a chance to earn a million miles and...
-

 224Cyber Events
224Cyber EventsWhat is Enforced Transparency? A Western Trend?
The concept of Transparency carries a simple meaning, if practiced by governments it will empower the masses, place them in a position...
-
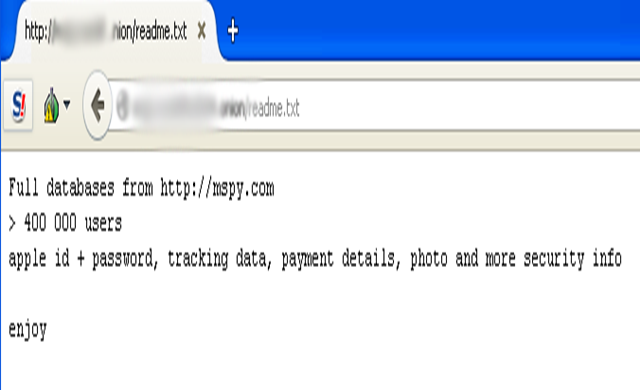
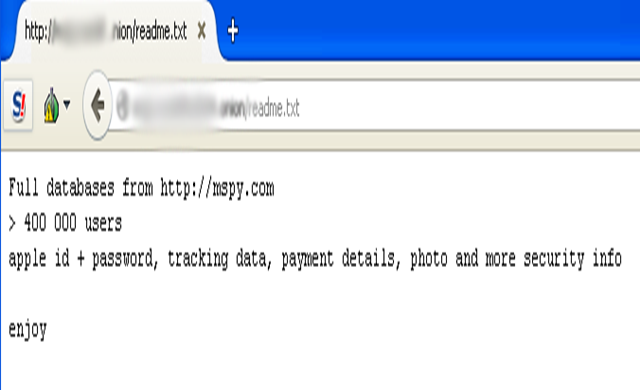 280News
280NewsMobile Spy Software Maker mSpy Hacked, Personal data of 400k users leaked
mSpy, the notorious software-as-a-device product which so far enabled two million plus people spy on their spouses and kids, is believed to...
-

 211Tricks & How To's
211Tricks & How To'sLive Stream Twitch in VLC to avoid buffering
Twitch has been making some very awful encoding and additional bad choices for streamers and viewers of Twitch.tv. This method has been...
-

 202How To
202How ToFree Microsoft Office alternatives
Many people feel the need to use Torrents to pirate software that would normally be paid for, however by doing this torrent...
-

 225How To
225How To10 Games That Teach Kids To Code
In this world 36 million kids have taken part in Hour of code activities, by helping them to develop their skill in...
-

 111Cyber Crime
111Cyber CrimeA Compromised .GOV URL Hosting Phishing Attacks on Apple Users
A couple of months ago we reported how [linked url=”https://www.hackread.com/app-store-phishing-email-stealing-apple-user-credentials/”]an app store phishing email is stealing Apple user credentials[/linked]. Now a government of Vietnam domain...
-
 240Data Security
240Data SecurityWhatsApp users hit with ‘You Just Got an Audio Recording’ Email Malware
The email apparently is sent from the popular messaging service WhatsApp and claims that you have received an audio recording. A malicious...
-
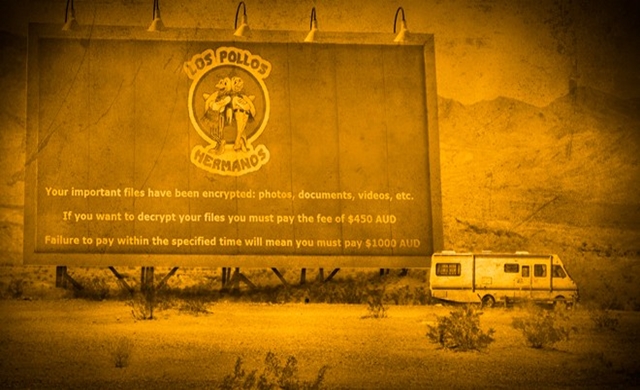
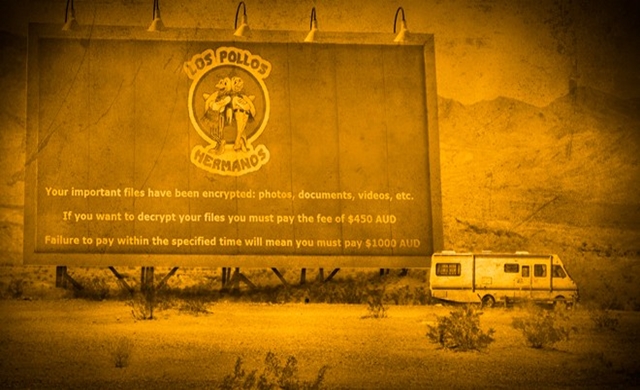 296Data Security
296Data SecurityInternet users hit with Breaking Bad Theme Crypto-Malware
To demonstrate their creativity cybercriminals have released a new ransomware equipped with file encryption abilities and this time they have chosen logo...
-

 99Privacy
99PrivacyApple seeks to block sale of RadioShack customer data
Apple has filed a court objection against the sale of RadioShack customer data for those who had purchased its products, reports Ars...
-
 206Interview
206InterviewHow did the Internet change the everyday work of a security researcher?
Aryeh Goretsky and David Harley talk to Sabrina Pagnotta about the internet's impact on security research.
-

 115Privacy
115PrivacyGoogle turns down 60 percent of ‘right to be forgotten’ requests
A year after Google introduced its controversial 'right to be forgotten' feature, the search giant has published some statistics about its implementation.
-
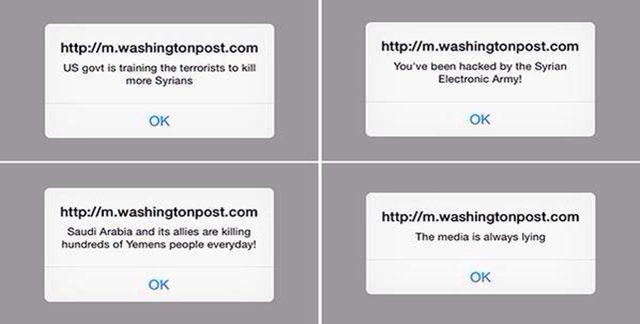
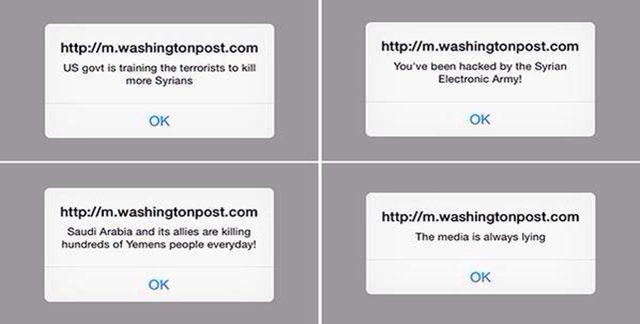 302News
302NewsSyrian Electronic Army Hacks Washington Post Mobile Site
The official mobile website of American daily newspaper The Washington Post was hacked by Syrian Electronic Army (SEA), a group loyal to Syrian President Bashar...
-

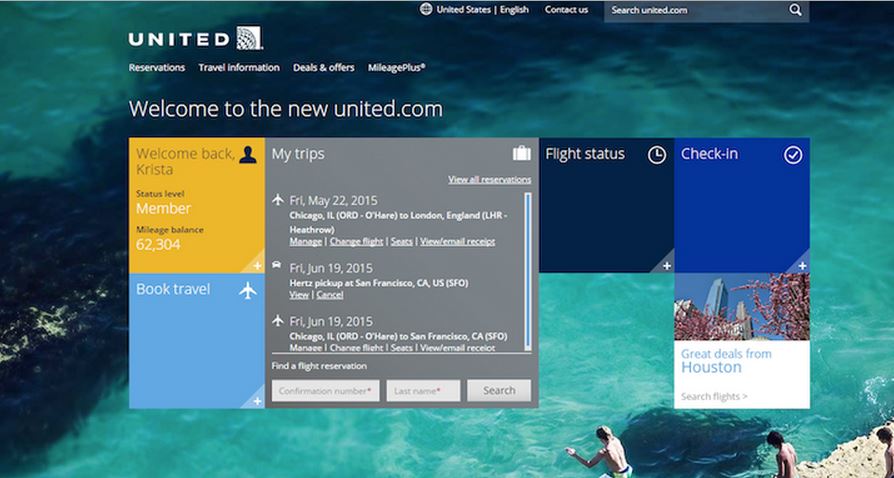
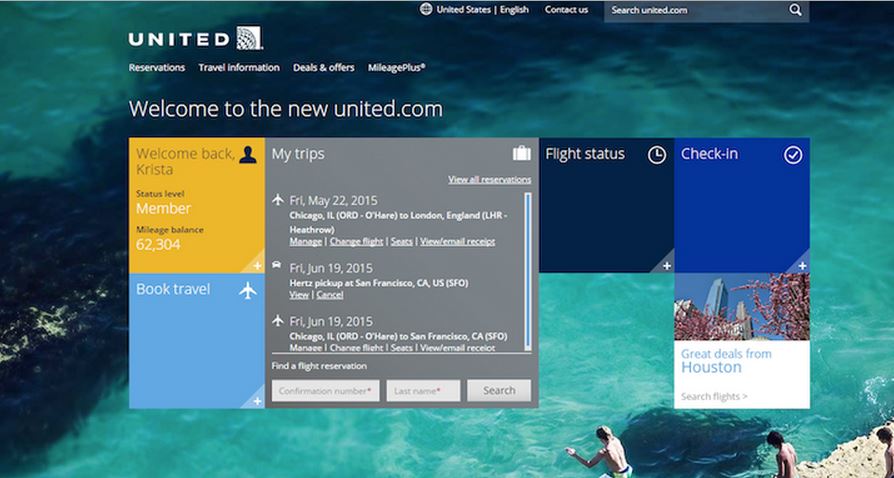
 362Data Security
362Data SecurityUnited Airlines Bug Bounty Program: Report Security Flaw, Get Rewards
If you are a hacker or an IT security researcher, United Airlines has announced its first ever Bug Bounty program for you...
-

 226Data Security
226Data SecurityAnonymous team hides malware in Nvidia GPUs, can harm Mac, Linux, Windows
Summary: In a bid to raise awareness regarding the way malware can affect GPUs, a team of developers recently created a Linux...
-

 323Hacked
323HackedAnonymous Hijacks Thousands of Insecure Routers to Power Its DDoS Tools
Lack of some elementary security measures can risk your router’s security and this has stemmed to grow into a large-scale denial-of-service (DDoS)...
-

 166Data Security
166Data SecurityResearcher claims Starbucks mobile app got hacked, credit card data stolen
Summary: Earlier this week Bob Sullivan reported that hackers can easily access Starbucks customer accounts by stealing their username and passwords and naturally Starbucks...
-

 223Data Security
223Data SecurityNotion of Cloud’s Unmatched Security Shattered by ‘Venom’ vulnerability
The CrowStrike researchers discovered that any attacker can burst out of specific virtual machines and exploit whatever is running nearby — The...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




