Featured News
-

 290News
290NewsUber USA customers hacked – Change your username and password ASAP
In March, Motherboard reported Uber accounts had been stolen by hackers who were selling them on public forums for as low as...
-
 436Hacked
436HackedHow To Make Incognito Mode the Default Browsing Mode In Chrome?
Today privacy is the greatest concern in our world dictated by our online presence. Those who are aware of the consequences of...
-
 237Geek
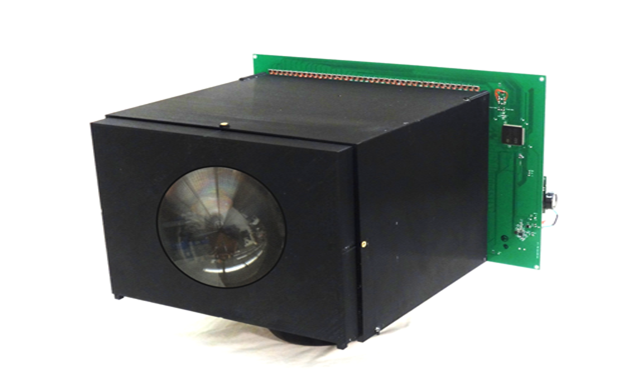
237GeekNo Battery required – Self-Powered Video Camera runs, records forever
Researchers have developed a video camera which can record non-stop — The camera is one of its kind. Columbia University researchers have developed...
-

 294Cyber Events
294Cyber EventsStatues of Snowden, Assange, Manning unveiled in Berlin’s Alexanderplatz square
Famous whistleblowers Chelsea Manning, Edward Snowden and Julian Assange can be seen standing in Berlin now as their life-size bronze statutes were...
-

 326Interview
326InterviewDavid Harley: “New scams are difficult to spot even for a trained eye”
Harley says that scams and social engineering have been a constant in cybercrime - but in the past few years, some scams...
-

 82How To
82How ToNational Small Business Week: a cybersecurity survival guide
It's National Small Business Week in the U.S. and, because properly protecting the digital assets of your small business could be vital...
-

 122Cyber Crime
122Cyber CrimeThe world’s most wanted hackers
The FBI is taking cybercrime seriously. Here are some of the most wanted hackers in the world, and what they're wanted for...
-

 271Hacked
271HackedHow To Become An Ethical Hacker? [Infographic]
Cyber-security is one of the major concerns of online users these days and hackers are an inevitable part of this discussion. Every...
-

 284Data Security
284Data SecurityBoeing 787s can lose control while flying due to Software bug
A warning has been issued by the FAA regarding the software glitch in the system of Boeing’s 787 Dreamliner — This glitch...
-

 341News
341NewsAnonymous Hacks World Trade Organization, leaks personal data of thousands of officials
Keeping Anonymous hackers out from news is simply impossible, the hacktivist movement is active 24 x 7 and you can always expect them...
-

 391Data Security
391Data SecurityBanking Malware Delivered via Macro in PDF Embedded Word Document
Delivering banking malware through Microsoft Word documents has been a less common method. However, it is currently being used for spreading malicious...
-

 132Hacked
132HackedNew Firefox Features Will Only Support Secure Websites
In a recent blog post, Mozilla has showed its intent to phase out the non-secure websites i.e. the HTTP. Earlier this week,...
-

 197Cyber Crime
197Cyber CrimeNigerians arrested for Laundering €2.5 Million through Online Scam
Ten individuals of Nigerian origin have been arrested by Guardia di Finanza for laundering millions of pounds acquired from frauds causing loss...
-

 246News
246NewsRed Bull Malaysia Website Hacked by Pro-Palestinian Hackers
After successful OpIsrael, AnonGhost is now targeting random but high-profile websites around the world. The latest in line is Red Bull Malaysia. The...
-
 242Geek
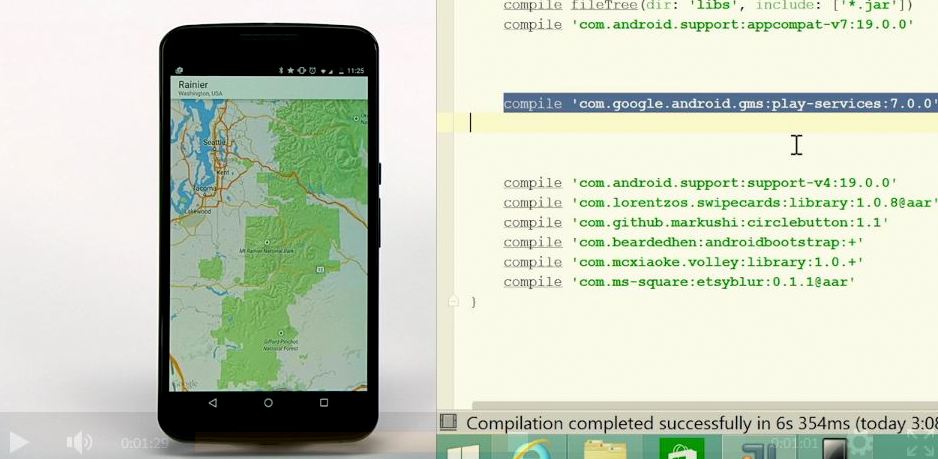
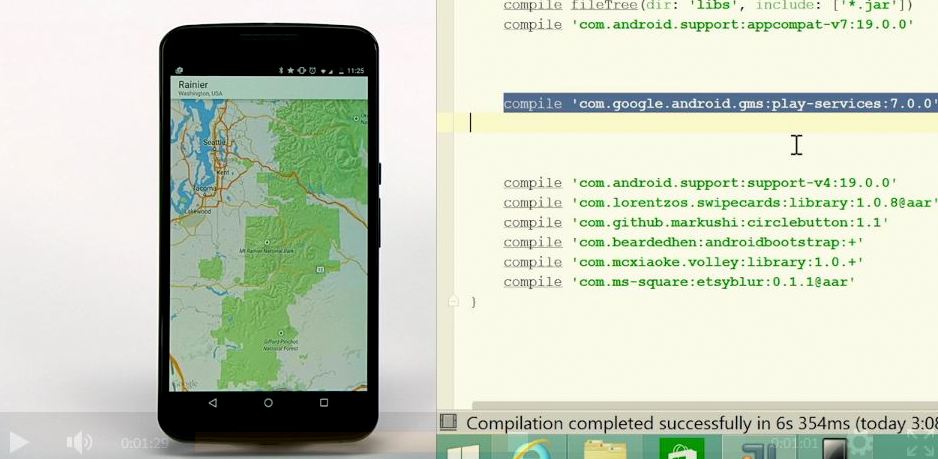
242GeekHow Android and iOS Apps Could be Ported to Windows for Mobile – Everything Detailed
Microsoft’s Build 2015 conference is now over and we were greeted with many pleasant surprises. According to me, one of the biggest...
-

 278Data Security
278Data SecurityWikiLeaks’ Anonymous Leak Submission Website Relaunched after 6 years
Expect exposure of confidential news pieces and government/corporate classified documents every now and then because WikiLeaks, the anti-secrecy group has re-launched its...
-

 228Hacked
228HackedMale Characters in The Sims 4 Are Getting Pregnant Due to a Bug
Last month released expansion pack “Get To Work” for The Sims 4 gave players the chance to actively control created characters if they...
-

 231Hacked
231HackedHacker Controls the Cellphones in GTA V With His Own Cellphone
If you are into gaming, then you would be well aware of the GTA V and how advanced it is in comparison...
-
 382Geek
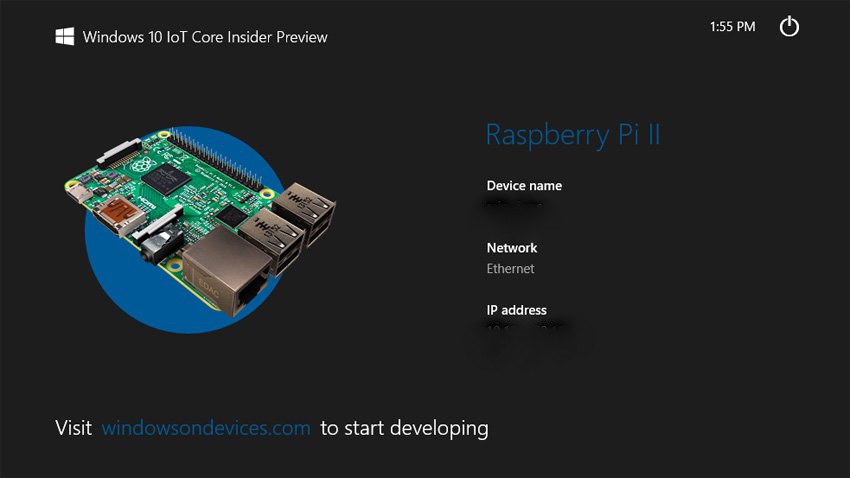
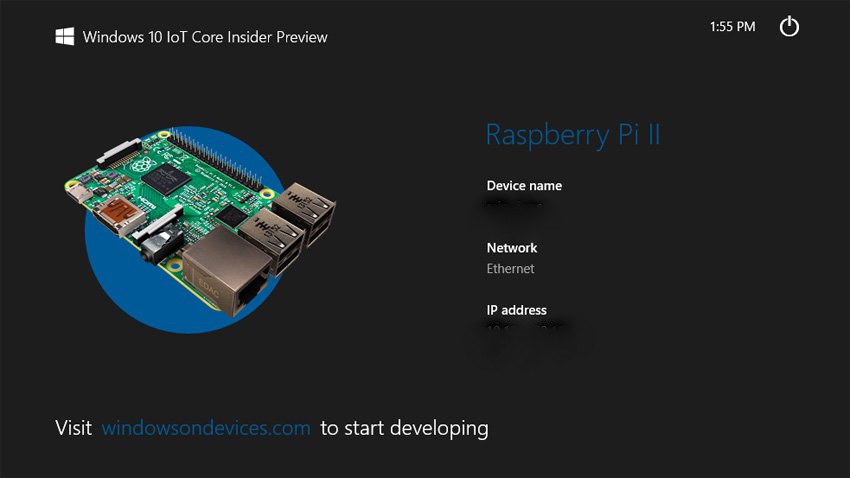
382GeekHow To Install Windows 10 on Raspberry Pi 2
Here I am going to tell you how to install Windows 10 IoT on our beloved Raspberry Pi 2. Microsoft has brought...
-

 161Cyber Crime
161Cyber CrimePayPal Users Hit with ‘ASDA Order’ Phishing Scam
A fake email from Paypal is used by hackers to carry out a phishing attack on users. The email says a transaction has...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




