Featured News
-

 384News
384NewsPics of IDF women soldiers helped hackers to breach Israeli Military Servers
Arab hackers are using pictures of IDF’s women division to hack Israeli military servers — And it’s a success. Several computer networks belonging...
-

 328Geek
328GeekHow to use Google Search to locate lost Android Smartphone or Tablet
All you need to do is search for your Android device, mobile phone or tablet on Google – The search engine will...
-
 270Geek
270GeekWrite 1000 Lines Code in Just 50 Lines with New Programming Language “Picture”
Remember how we told you that Machine Learning is fast becoming the new buzzword in town. Rapid developments in this field are...
-
 358Data Security
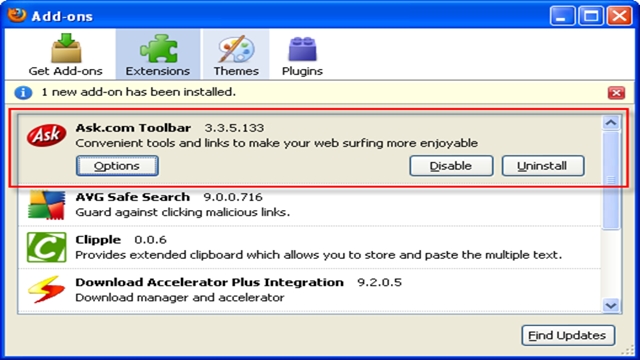
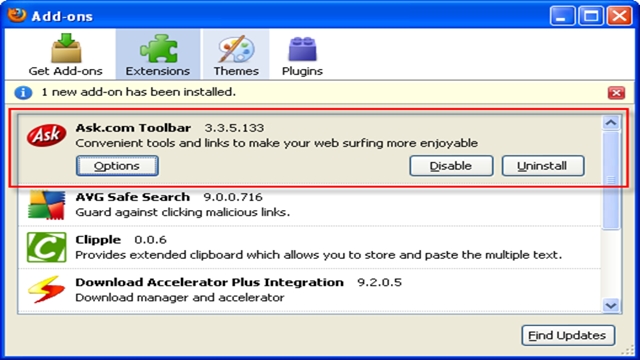
358Data SecurityAsk.com Toolbar Can Hijack Your Computer Through Java Updates
The Ask.com toolbar is not a handy tool — it’s a Curse because it never goes away. Apparently, Ask.com toolbar hijacks your...
-
 227Data Security
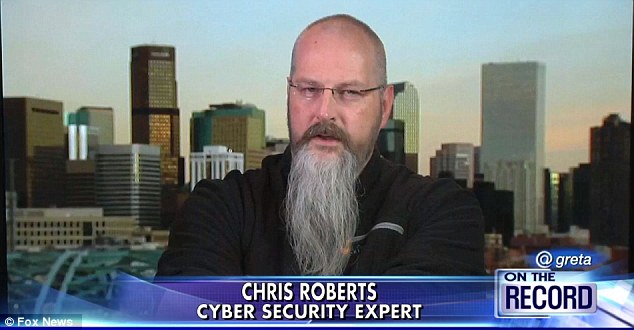
227Data SecurityHacker who revealed aircraft can be hacked offloaded by FBI
Chris Roberts (World Labs’ IT security expert) who recently identified risks in airplane in-flight entertainment systems became the target of FBI investigation himself....
-

 149Privacy
149PrivacyEmails and documents leaked during Sony hack released by WikiLeaks
Hundreds and thousands of documents and emails breached during last Christmas' cyberattack on Sony Pictures have been published on WikiLeaks, reports the...
-

 331Social Engineering
331Social EngineeringWill people always ignore security warnings?
How much of people's willingness to ignore security warnings is down to their brains?
-

 255Cyber Crime
255Cyber CrimeUS Citizens Targeted with Ransomware via Fake IRS Tax Return Emails
Tax Return-themed Emails make Users in America the Target of Ransomware – Attackers sending genuine-looking Internal Revenue Service (IRS) tax refund messages. Today,...
-

 385News
385NewsUniversity of Toronto Website Hacked by pro-ISIS Hackers
Team System DZ is known for hacking high-profile websites – Their latest target was the University of Toronto and they successfully achieved...
-

 302Cyber Events
302Cyber EventsWikiLeaks Publishes Searchable Database of 170,000 Hacked Sony Emails
The famous international, non-profit, journalistic organisation WikiLeaks published thousands of hacked Sony Emails. You can now access, read and search all the...
-

 259Data Security
259Data Security‘Guy Removes Blackhead’ Post Delivers Malware to Facebook Users
The new post that is spreading like wildfire around Facebook claims that click the picture and see how a ‘guy removes his...
-

 260Hacked
260HackedHijack Hack: Airplane WiFi Could be Used to Hack Planes
According to a new report, hundreds of commercial planes are vulnerable to hacking due to their very own airplane WiFi network for passengers....
-

 341Cyber Events
341Cyber EventsSpying Tools Being Bought Secretly by DEA from an Italian Surveillance Firm
DEA has been a client of the controversial Italian surveillance tech firm Hacking Team since 2012 — DEA has bought spyware capable...
-
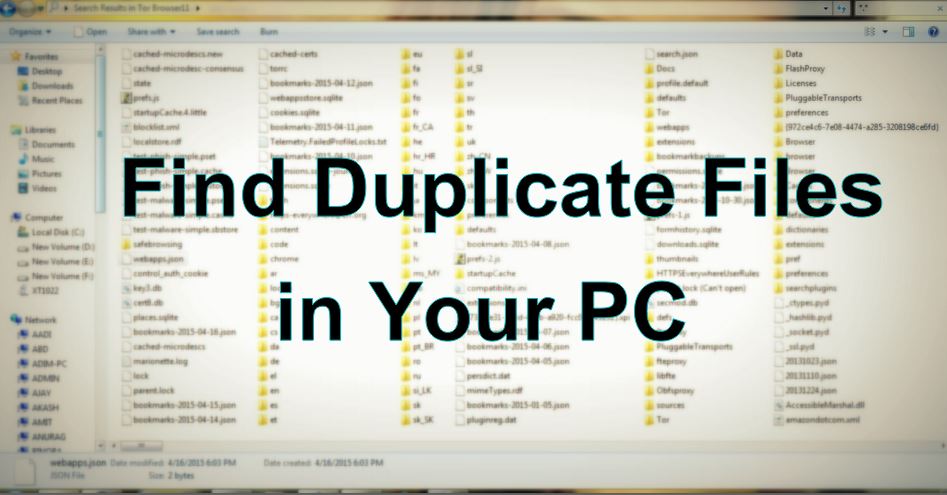
 449How To
449How ToHow to Find Duplicate Files Using Duplicate Files Finder
I am always a victim of lots of useless and redundant data in my PC. Out of all these useless files, a good...
-

 283Data Security
283Data SecurityVulnerable In-flight WiFi lets hackers to remotely takeover modern aircraft
The on-plane Wireless systems can easily be hacked by compromising the websites visited by travelers — This happens if same routers/wiring is...
-

 397Cyber Crime
397Cyber CrimeHackers could control planes over in‑flight Wi‑Fi, warns US government
Planes offering in-flight Wi-Fi are vulnerable to being hacked and controlled by onboard passengers, a US government watchdog has warned.
-

 113Privacy
113PrivacyData breach bill passes House committee despite concerns
The Data Security and Breach Notification Act has passed The House Energy and Commerce Committee by a vote of 29-22, reports The...
-

 202News
202NewsAnonymous Hacks San Bernardino County Sheriff Support Site Against Police Brutality
Anonymous GhostSec hacktivists have attacked the official support website of John McMahon (mcmahonforsheriff.com), who is a severing Sheriff in the San Bernardino County Police, California. Hackers have left...
-

 218Geek
218GeekNew Android App Lets You Unlock Your Phone with Your Voice
The new “Trusted Voice” Android app allows you to unlock your smartphone with your own voice — No pin, no password, just your...
-
 331Cyber Crime
331Cyber CrimeChild Abuse Images Sold by Paedophiles for Bitcoin
Paedophiles reportedly have been trading child sexual abuse images for bitcoin, revealed the Internet Watch Foundation/IWF in its annual report for 2014....
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




