Featured News
-

 178Surveillance
178SurveillanceA CIA Funded Company Reportedly Scanning Chats but Facebook Rejects Claim
Facebook Privacy Debate: A CIA Funded Company Reportedly Scanning Chats but Facebook Rejects the Claim. A developer has claimed on Hacker News that...
-
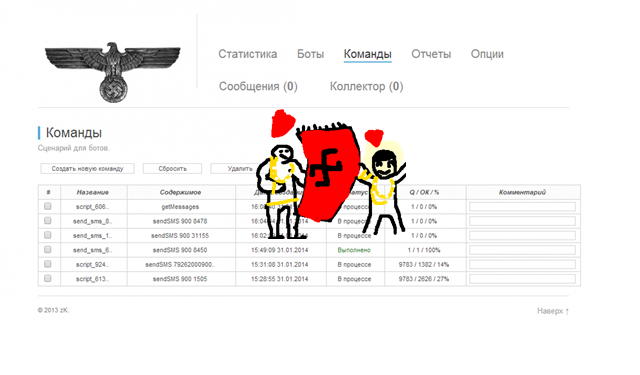
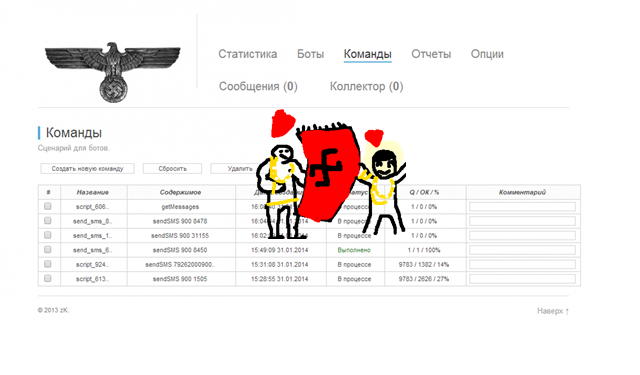 145Cyber Crime
145Cyber CrimeSuspects Behind Nazi-loving Android Malware Arrested in Russia
Suspected ‘Nazi’ Android FBI Ransomware Architect Detained In Russia – A Nazi-themed malware control panel was used by the Svpeng cybercriminal gang. It...
-

 81Cyber Crime
81Cyber CrimeHealthcare security shows little sign of improvement, finds Verizon report
Security in the healthcare sector has been making headlines for all the wrong reasons in recent months, and a new report has...
-

 105Mobile Security
105Mobile SecurityHow secure is your smartwatch?
Last week’s Apple Watch launch has put the spotlight back on the ‘smart’ inter-connected watches that are expected to change how we...
-

 138Hacked
138HackedChrome 42 Sends Notifications from Web Pages You Have Closed, Download Now
Today Google has launched Chrome 42 for Windows, Linux and Mac. This release can come bundled with new developer tools that will...
-
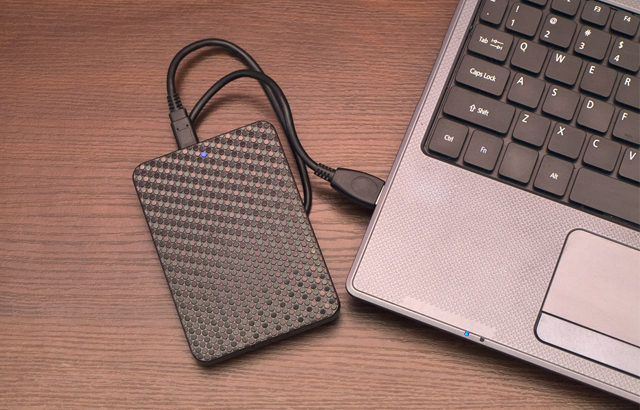
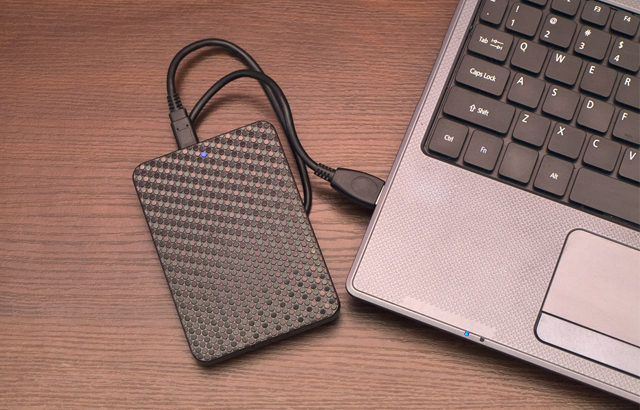 90Malware
90MalwareLawyer claims police placed malware on requested external hard drive
A lawyer in Arkansas is claiming that police planted three different pieces of malware on an external hard drive in a controversial...
-

 275Lists
275ListsApple’s Swift is the Most Loved Programming Language: New Dev Survey
Apple’s Swift, a relatively new programming language introduced to the world at Apple’s 2014 WWDC seems to have become a new favorite...
-

 444Malware
444MalwareAdvanced Persistent Threats: Using multi‑layered detection to defend against APTs
Advanced persistent threats (APTs) are a growing concern to the world's companies and networks. This recorded webinar looks at real-world data breaches...
-
 311Surveillance
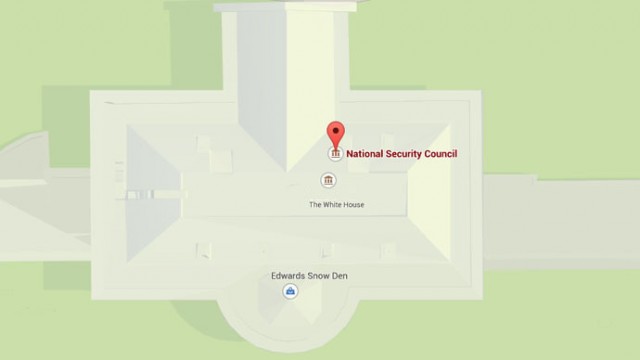
311SurveillanceGoogle Maps Shows Edward Snowden Has Moved to White House
Edward Snowden finally is home. After showing up as a sculpture at Brooklyn Park and appearing on John Oliver’s show Last Week...
-

 388News
388NewsGoogle Images, YouTube, Yahoo Malaysia Domains Hacked by Bangladeshi Hackers
Three Bangladeshi hackers (going with the handles of Ne0-h4ck3r, TiGER-M@TE and F0RTYS3V3N) hacked and defaced Google, Google Images, YouTube and Yahoo Malaysia domains on...
-
 261Hacked
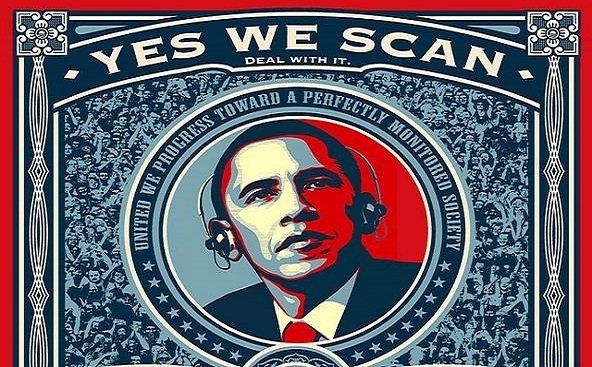
261HackedNSA’s Privacy Breach: We Are Coming From Your Front Door This Time
The head of NSA, Admiral Michael S. Rogers, addressing at Princeton University said: “I don’t want a back door. I want a...
-
 450Data Security
450Data Security18-year-old Vulnerability Lets Attackers Steal Data From All Versions of Windows
Researcher Aaron Spangler identified a bug in Internet Explorer back in 1997. This flaw allowed stealing of user credentials through Windows Server...
-

 96Cyber Crime
96Cyber CrimeFour Mortal Kombat moves cybercriminals use to attack your security
Some of the tricks employed by the characters in the Mortal Kombat series aren't a million miles away from those deployed by...
-

 245Cyber Crime
245Cyber CrimeThis Dude Hacked Lottery Computers to Win $14.3M Jackpot in U.S.
Former security director suspected for tampering with lottery computers to win $14.3m Jackpot. According to prosecutors there is strong evidence suggesting that...
-

 78Cyber Crime
78Cyber CrimeDutch government to launch Global Forum on Cyber Expertise
The Dutch government is to launch the Global Forum on Cyber Expertise, with the intention of capacity building in the fields of...
-

 228News
228NewsGoogle Malaysia Domain Hacked by Bangladeshi hacker
A Bangladeshi hacker (going with the handle of Tiger M@te) hacked the official Google Malaysia domain earlier today and redirected it to...
-

 266Scams
266ScamsTech Support Scammers with Teeth
Some support scammers and their assassination threats may seem dumb, but they're no joke.They can cause serious damage as we discuss it...
-
 262Cyber Events
262Cyber EventsHackers Shut Down Vatican City Website Against Pope’s Comment
Turkish hacker shutdown Vatican City official website against Pope Francis’ remarks in which he used the word ‘genocide’ to refer to mass...
-

 250Surveillance
250SurveillanceNSA Wants Tech Giants to give it ‘Front Door’ access to your encrypted data
The National Security Agency wants tech companies to provide it a front door access to your data so it can spy on millions of Americans...
-

 373How To
373How ToHow To Download SoundCloud Songs for Free
Hello, fossBytes readers! As many of you are already familiar with the fact that I frequently write how-to articles, I keep on...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




