Featured News
-

 297Surveillance
297SurveillanceDrone caught delivering phones, knife and drugs at a high-security prison
Prison Security Breached by Drone to Transfer Knife, drugs and phones into the jail. This can easily pass as a very daring...
-

 299Cyber Crime
299Cyber CrimePoint-of-sale Systems Targeted By New PoSeidon Malware
Beware all you retailers, a new Trojan program dubbed as PoSeidon targets point-of-sale or PoS terminals and can potentially steal payment card...
-

 99Privacy
99PrivacyCanada’s “secret hacking tactics” exposed in new report
Canada has been using an array of cyberweapons to gather intelligence, spy on other governments and damage adversary infrastructure, says a new...
-

 121Mobile Security
121Mobile SecurityMobile security: IBM/Ponemon study finds enterprise app security weaknesses
Nearly 40 percent of large companies - including a significant number in the Fortune 500 - are not taking necessary precautions to...
-

 384Password
384PasswordTwitch backs down on 20‑character passwords in wake of hacking
Twitch has backed down on its attempts to force stronger password complexity on its site post-hacking, after multiple complaints from its userbase.
-

 270Hacking
270HackingFive hacker movies that got things badly wrong
5 hacker movies that got computer security well off the mark.
-

 97Privacy
97PrivacyHilton HHonors accounts put at risk of hijacking through simple web flaw
Security researchers discovered a vulnerability on the Hilton HHonors website, making it straightforward to hijack any other user's account.
-

 165Hacked
165HackedThousands of Popular iOS and Android Apps Still Vulnerable to FREAK
While whole world was worried about the FREAK vulnerability of the browsers, hundreds of popular apps of Android and iOS are still...
-
 291Hacking Tutorials
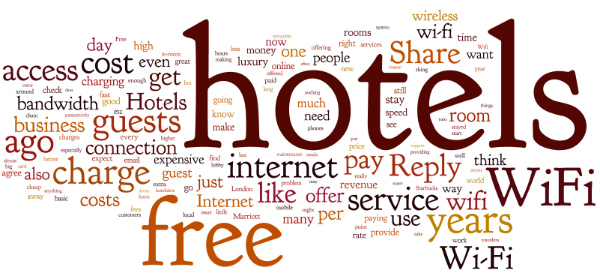
291Hacking TutorialsHow to hack a Hotel’s Wifi
Firstly, i would ask you whether or not you have had this situation before? Where for instance ,your phone is connected to...
-
 225Geek
225GeekFacebook Developer Tool for Slow Network App Testing is Now Open Source
Back in the year 2013, Facebook developed a tool to test its apps on slow connections named Augmented Traffic Control. Everyone is...
-

 194Tricks & How To's
194Tricks & How To'sHow to find a Wifi password with CMD
So, first start CMD. Most of the time CMD is built-in on the computer. Opened up CMD? Good. Now let’s go and...
-

 218Cyber Events
218Cyber EventsAnonymous Targets NYPD Captains Union Website with Malware
On Friday, a cyberattack on NYPD captains union website infected it with malware and forced it to shut down. According to union...
-

 195Malware
195MalwareMillions of computers left vulnerable to BIOS chip hack
A vulnerability has been detected in the BIOS chips found in millions of computers which could leave users open to hacking.
-

 152Privacy
152PrivacyCisco vulnerability could allow attackers to eavesdrop on private conversations
A vulnerability in Cisco's SPA300 and SPA500 IP phones could allow hackers to eavesdrop on private conversations from anywhere in the world,...
-

 258Data Security
258Data SecurityNew Snowden Documents Expose Canada’s Hidden Cyber Warfare Strength
On Monday, CBC News and The Intercept collaboratively disclosed for the very first time how Canada has endorsed aggressive strategies for attacking,...
-

 124Hack Tools
124Hack ToolsDecrypting a whatsapp account (Crypt7/8)
Use Whatsapp with Someone else’ number , this hack works by tricking the WhatsApp Verification Servers by receiving sms by a spoofer...
-

 93Surveillance
93SurveillanceFrance Announces New Spying Regulations After Terrorist Attacks
On Thursday, the Prime Minister of France Manuel Valls revealed debatable new laws that will allow intelligence agencies to gather cellphone and...
-

 222Cyber Events
222Cyber EventsPakistan Unblocks WordPress.com After Blocking It For One Day
Yesterday we reported how WordPress (WP) was banned in Pakistan due to internet security issues. We also revealed that the banned will be a...
-

 105Geek
105GeekGirl Poisons Mom Twice For Taking Away Her iPhone
A 12-year-old girl in Colorado has been arrested and charged for attempting to kill her mom through poisoning her with bleach just...
-
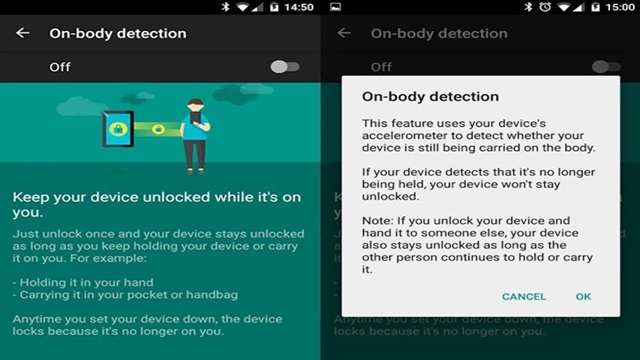
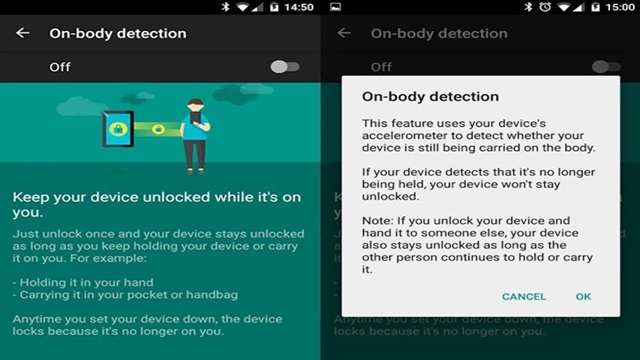 230Geek
230GeekAndroid On-Body Detection Feature Will Keep Your Phone Safe From Thieves
The new on-body detection feature will lock your phone when you set it down, so thieves who swipe it can’t access your...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




