Featured News
-

 136Opinion
136OpinionOperating System Vulnerabilities, Exploits and Insecurity
iOS and OS X the most vulnerable operating systems? Don't confuse vulnerabilities with exploits, or patch frequency with insecurity.
-

 235How To
235How ToHow to Build a Website – A Complete Guide
How to build a website? Short Bytes: Building a website is no big deal today. There are lots of technologies, frameworks, tutorials...
-
 245News
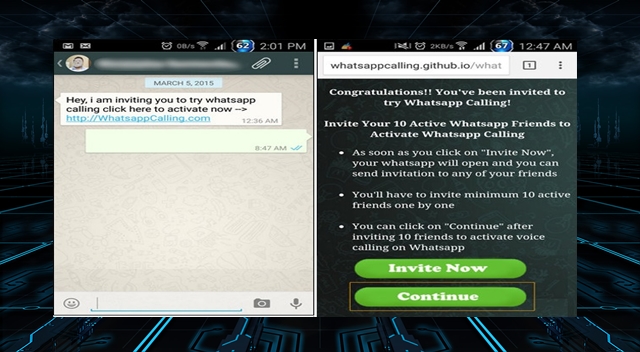
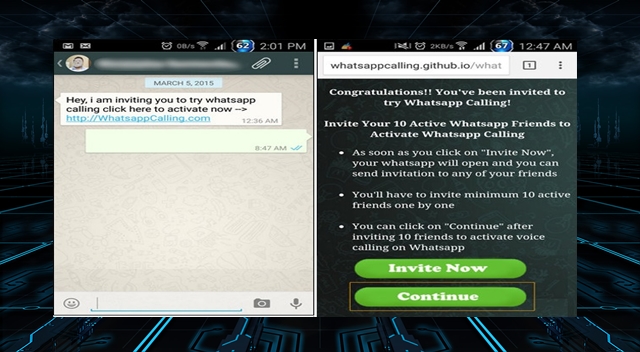
245NewsWhatsApp Voice Calling Invitation Text Spreads Malware on Smartphone
If you are using WhatsApp and have got a text message asking you to click a link in order to start using WhatsApp’s...
-

 296Cyber Crime
296Cyber CrimeBEWARE: ‘Thank You for Purchasing’ Email Delivers Malware
Don’t be Fooled – ‘Thank You for Purchasing ‘ Email Delivers Malware. Inboxes all over the world have been hit by another...
-

 342Geek
342GeekColor Blindness Curing Glasses Accidentally Invented by Scientist
It was during a Frisbee game with a friend in Santa Cruz (USA), when the Don McPherson discovered inadvertently that one of...
-

 77Cyber Crime
77Cyber CrimeThree men indicted in ‘one of the largest’ data breaches in US history
The US Department of Justice has charged three men with what is being described as “one of the largest reported data breaches...
-

 94Malware
94MalwareESET’s Mark James on 2015’s security trends
how is 2015 shaping up in security? We caught up with ESET security specialist Mark James to get his take on threats,...
-

 219News
219NewsCurious Case of M. Yousefi: How Iran Traps its Facebook users with “Black Spider” Program
A 27-year-old graduate student Mohammad Yousefi, was sent to prison in Iran as part of a crackdown on social media users by using...
-

 311Hacking
311HackingFBI investigating apparent ISIS attacks on Western websites
A number of seemingly unconnected Western websites were hacked over the weekend, with messages claiming Islamic State as the perpetrator.
-

 87Cyber Crime
87Cyber CrimeDDoS attack on feminist blog backfires on International Women’s Day
An attempt to silence feminism blog Femsplain backfires on DDoS attackers, as they only help to raise its profile.
-

 258News
258NewsUniversity of Chicago Computers Hacked, Social Security Numbers Stolen
Summary: The university of Chicago was hacked – The officials got to know in January 2015 that social security numbers and other sensitive information was...
-

 207Cyber Crime
207Cyber CrimeUK National Cyber Crime Unit nabs 56 cyber criminals over the last week
National Crime Agency, a London based law enforcement agency, has arrested as many as 56 individuals over the last week for various...
-

 286Geek
286GeekAndroid Users Receiving Amazon Gift Card Text Message Contains Gazon Malware
Have you received TEXT messages about Gift from Amazon? Beware it might be malware. Have you recently received a text message on...
-

 271Geek
271GeekHackaball : Programmable Toy that Teaches How to Code
Could a toy teach coding? Are we moving towards having Programming Languages in Kindergarten? Technology has advanced at every level. Now geeks...
-

 187Cyber Crime
187Cyber CrimeAustralia To Prosecute The Radio Voice of Anonymous Hacktivist @LoraxLive
A well-known figure known as the radio voice of Anonymous, LoraxLive, Adam Bennet who had also been arrested last year when he...
-

 307News
307NewsAnti-Israeli hackers target Louisiana’ Rapides Parish Police Jury, Bank websites
The online hacktivist AnonGhost is on a hacking spree with targeting websites of top law enforcement agencies in the United States. A...
-

 187Cyber Crime
187Cyber CrimeThree Hackers Charged with one of the largest data breaches in US history
The U.S Department of Justice announced that there has been the largest data breach in the history of U.S done by two...
-

 264Hacked
264HackedHow to Protect Your Windows Machine Against the FREAK Hack Attack
FREAK’s man-in-the-middle attacks are the result of the security mistakes made 20 years ago. Initially, it was thought that Windows machines are...
-

 330Data Security
330Data SecurityBEWARE: uTorrent Update Installs Bitcoin Mining Software
uTorrent is secretly installing Epic Scale Bitcoin Mining Software on users’ computer to get some bucks – They claim it’s a distributed computing platform, but that’s not...
-

 324Hacked
324Hacked56 Hackers Arrested in Anti-cybercrime Operations – “Strike Week”
According to the UK authorities, 56 hackers have been arrested across England, Wales and Scotland with accusations of carrying out anti-cybercrime operations....
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




