Featured News
-

 448Privacy
448PrivacyPrivacy and security post‑Snowden: Pew Research parallels ESET findings
Privacy and security online are hot button topics in America today, as a new survey by the Pew Research Center confirms, mirroring...
-

 329News
329NewsAnonymous hacks Ku Klux Klan twitter over Ferguson threats
Summary: On Nov 14, 2014, the online hacktivist Anonymous released a YouTube video announcing a cyber attack on Ku Klux Klan, (a...
-

 266News
266NewsHere’s How To Disable WhatsApp’s Double Blue Ticks.
WhatsApp has made its new option ”blue ticks” an indication that a WhatsApp message has been read. The feature, introduced just a...
-

 524How To
524How ToPublic Wi‑Fi hotspots – know the risks
For ordinary laptop and smartphone users, Wi-Fi is not ideal - but it’s sometimes near-inescapable.
-

 218Mobile Security
218Mobile SecurityNexus 5, Galaxy S5 and iPhone 5s hacked at Pwn2Own event
The Samsung Galaxy S5, Apple iPhone 5s and Google Nexus 5 were amongst handsets to be successfully hacked during the Mobile Pwn2Own...
-

 290Banking
290BankingMasterCard and Visa to end password authentication
MasterCard and VISA have revealed their plan to end the use of passwords for online payments, reports The Telegraph.
-

 130Privacy
130PrivacyIT Pros also guilty of risqué selfies on mobiles
ESET study reveals many IT professionals are guilty of storing indecent material on their mobile phones, which would leave them embarrassed if...
-
 337Data Security
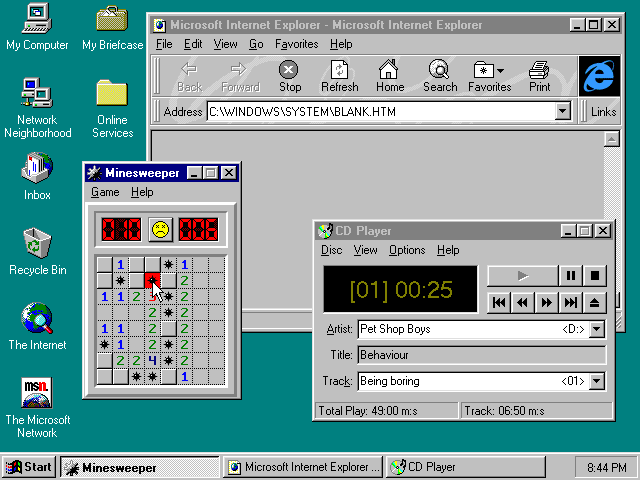
337Data SecurityMicrosoft fixes security flaw in Windows that existed for 19 years
Microsoft has released an emergency update on Tuesday to patch a security flaw in the Windows operating system (that remained unnoticed for 19...
-

 97Malware
97MalwareBadUSB potential not as widespread as originally thought, but remains difficult to avoid
The BadUSB malware which potentially turns any USB stick into a 'unpatchable' malware carrier doesn't quite have the potential for mayhem it...
-

 245Social Media Hacking
245Social Media HackingTracing your Facebook Profile visitors
Want to know who visits your FB profile? This works 100% , as you are examining your own FB source code. Follow...
-
 124Social Media
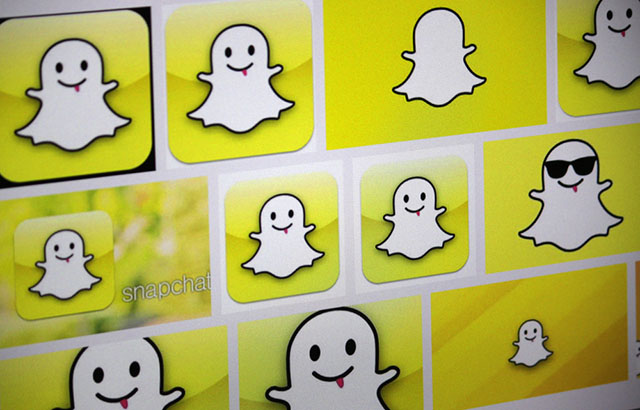
124Social MediaSnapchat urges users to disconnect third party apps after breach
Following last month's leak of 13gb worth of private Snapchat videos, the vanishing message service has announced a new policy whereby it...
-

 141Privacy
141PrivacyWebsite reveals 73,000 unprotected security cameras with default passwords
As we've reported before, users and businesses leaving their router username and passwords as the manufacturer's default are potentially leaving themselves open...
-

 407Malware
407MalwareSednit Espionage Group Attacking Air‑Gapped Networks
The Sednit espionage group, also known as the Sofacy group, APT28 or “Fancy Bear”, has been targeting various institutions for many years....
-

 116Password
116PasswordKickstarter campaigns wants your password on your wrist
A new wristband that aims to replace the password has launched a crowdfunding campaign on Kickstarter. At the time of writing, Everykey...
-

 141Scams
141ScamsRealistic looking phishing websites work 45% of the time, Google claims
Google has teamed up with the University of California in San Diego to publish surprising new research about phishing, how effective it...
-

 472Data Security
472Data SecurityCreepy website shows live footage from 73,000 Private Security Cameras
Security cameras with default passwords are a threat to your privacy — A site has indexed 73,011 unsecured cameras in 256 countries around...
-

 303Mobile Security
303Mobile SecurityApple Pay and security – what you need to know
Mobile payments look set to be one of the defining technologies of 2015, as the launch of Apple Pay catalyses a boom...
-

 183Cyber Crime
183Cyber CrimeDark Web drug trade site Silk Road 2.0 shut down
A year ago, Silk Road 2 appeared on the dark web, after the original Silk Road site's illegal drug trade was shut...
-

 235Data Security
235Data SecurityWireLurker: Apple Malware Infecting Mac and iPhone via USB
Apple is usually known for its top notch security but a US-based cyber security software developer Palo Alto Networks discovered a new...
-

 134Privacy
134PrivacyGoogle security – how to lock down your Google account
If you use Gmail as your ‘main’ email account - or rely on Google services such as Drive for work - it’s...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




