Featured News
-

 123Mobile Security
123Mobile SecurityGoogle outlines new security features in Android 5.0
Google has outlined the enhanced security credentials of the upcoming Android 5.0 - nicknamed Lollipop - in an official blog post.
-

 166Surveillance
166SurveillanceThis Camera-Covered Jacket Is Best Surveillance Tool To Record/Report Crime
Street crimes? not a problem now! With the newly designed jackets one can easily track down thieves and alert the respective authorities....
-

 229Tricks & How To's
229Tricks & How To'sRemotely shutdown computers
Note* For this to work you must be connected on the same network as the victim’s computer 1) Right-click on your desktop....
-

 327Information Gathering
327Information GatheringHow to get someones IP from facebook
When you’re talking with someone over chat, make sure your messages also notify you via email. Once someone sends a message and...
-

 173Privacy
173PrivacyBritish job centers to introduce biometric recognition
Job centers across the United Kingdom are due to get a technological makeover, courtesy of biometric and signature recognition pads, reports IT...
-

 310Information Gathering
310Information GatheringHow to find the IP of a Skype user
1.Log onto the computer as the “Administrator.” Go to “Start” > “Search.” 2.Enter “cmd” into the “Search” box. Press “Enter.” 3.Go to...
-

 102How To
102How ToHow do open source tools stay secure?
Security of open source code is a hot topic, what with Heartbleed, Shellshock, and Poodle making the news. Open source code is...
-

 97Cyber Crime
97Cyber Crime42% of Americans hit by regular online attacks
A study by Microsoft has revealed that 42 percent of Americans face 'weekly or daily' attacks by cybercriminals trying to access their...
-

 107Malware
107MalwareTor users targeted with exit node malware
An exit node on the Tor network has been discovered to be slipping malware on top of downloads, according to The Register....
-

 90Cyber Crime
90Cyber CrimeInternet trolls – how to deal with online abuse
Most internet users have faced some kind of problems with internet trolls - and a new study has thrown light on who...
-

 219News
219NewsIranian Hacker Defaces Website of UAE’s Telecom Regulatory Authority
An Iranian hacker going with the handle of MoHaMaD VaKeR hacked and defaced the official sub-domain ofTelecommunications Regulatory Authority (TRA) of United...
-
 360Geek
360GeekFlashlight Apps Stealing Personal Information Stored On Your Smartphone
It is our duty to protect our data— but are we ready? No one would have thought that the most practical invention...
-

 279News
279NewsAnonymous Shuts Down Top Israeli Govt Sites Against Killing Of 14-Yr-Old Kid
The online hacktivist Anonymous is back with yet another cyber attack. This time the group has taken down 43 top Israeli government...
-

 148Privacy
148PrivacyNew Tor routers seeking crowdfunding by Kickstarter
A selection of rival privacy conscious Tor routers have appeared on crowdfunding sites after the Anonabox was surprisingly pulled just days after...
-

 108Password
108PasswordTwitter: “We’re finally getting rid of the password”
Popular microblogging platform Twitter is taking bold steps to try and put an end to the password as we know it, according...
-
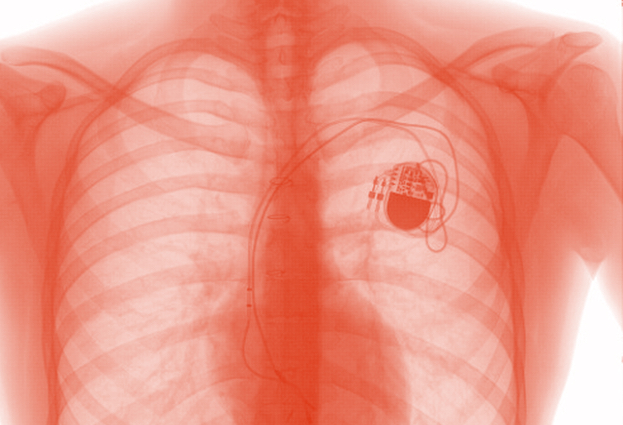
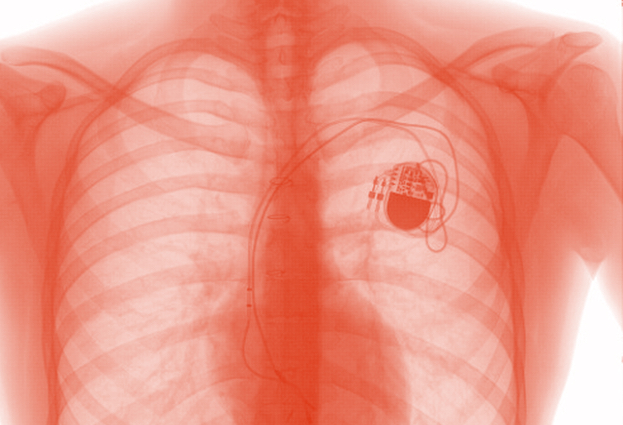 112Cyber Crime
112Cyber CrimeCould hackers give you a heart attack or drugs overdose?
There is growing concern that in the rush to embrace technology to save and improve the lives of patients, medical scientists may...
-
 197How To
197How ToReady, set, shop: 10 top tips for a safe shopping season
Tips for safe holiday shopping: whether you shop online or at the mall, there are some simple strategies that can protect your...
-
 411Privacy
411PrivacyCounter surveillance tech – can gadgets spy‑proof your life?
Over the past few years, counter surveillance gadgets which might have been the preserve of secretive government departments a decade ago have...
-

 240Exploitation
240ExploitationCreate your own USB Password stealer
This tutorial will walk you through setting up a USB flash drive to steal the saved passwords on a computer. Method 1...
-
 430Cyber Crime
430Cyber Crime10-Year-Old Filipino Virtual Girl “Sweetie” Takes Pedophile To Prison In Australia
An Australian citizen Scott Robert Hansen, 37, was sentenced to one year in prison for keeping obscene conversations with children on the internet. Hansen...
The Latest
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
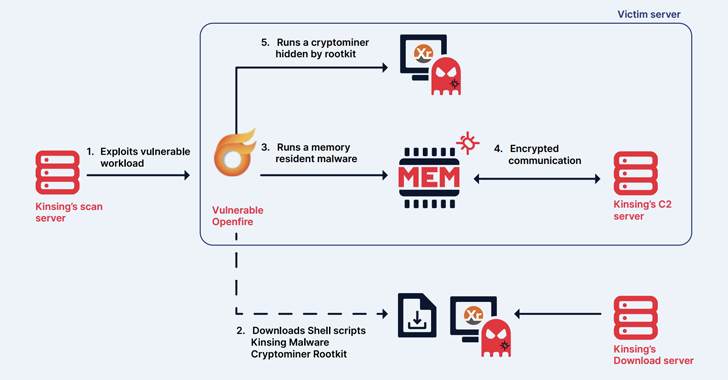 Malware
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
 Malware
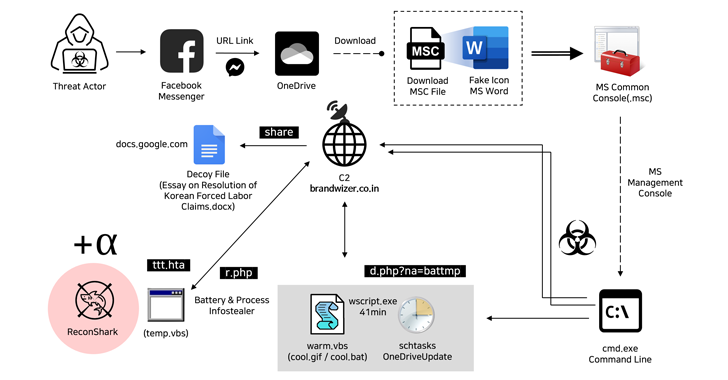
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Malware
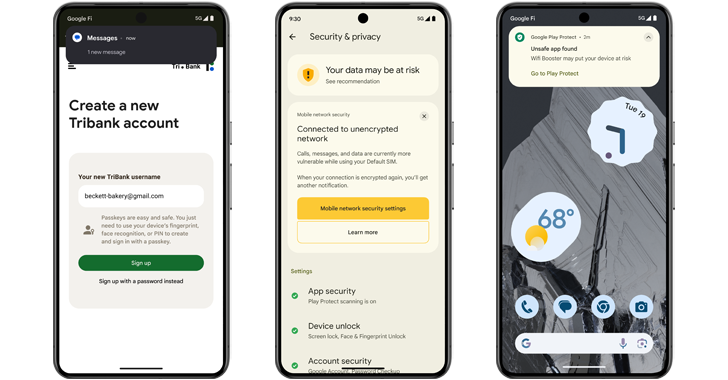
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions
-
 Vulnerabilities
Vulnerabilities(Cyber) Risk = Probability of Occurrence x Damage
-
 Malware
MalwareEbury Botnet Malware Compromises 400,000 Linux Servers Over Past 14 Years
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Vulnerabilities
VulnerabilitiesVMware Patches Severe Security Flaws in Workstation and Fusion Products
-
 Vulnerabilities
VulnerabilitiesNew Chrome Zero-Day Vulnerability CVE-2024-4761 Under Active Exploitation




