Featured News
-

 108Malware
108MalwareTop 5 Scariest Zombie Botnets
An army of the undead, wreaking havoc on the Internet – it's a nightmare scenario that has played out many times as...
-

 341Lists
341ListsTop Five Best But Lesser Known Features of Android 5.0 Lollipop
As I’ve written in my earlier posts, Android 5.0 Lollipop is the most significant change in Android line-up since 2011’s Android Ice...
-

 189Malware
189MalwareYahoo, Match and AOL hit by ransomware
Cybercriminals taking advantage of a 'malvertising' attack on big name sites including Yahoo!, Match.com and AOL were making in the region of...
-

 334Banking
334BankingThe Evolution of Webinject
Last month, we presented “The Evolution of Webinject” in Seattle at the 24th Virus Bulletin conference. This blog post will go over...
-

 98Password
98PasswordWindows 10 to tighten security with prominent 2FA
Microsoft is taking aim at traditional single password systems with the upcoming version of Windows, by including build in two-factor authentication according...
-
 86How To
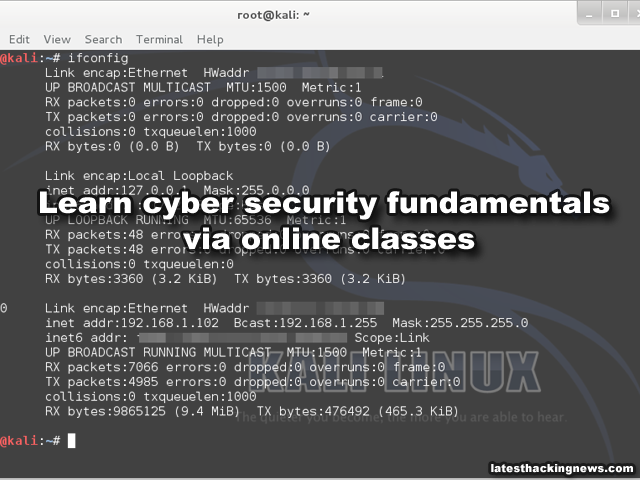
86How ToLearn cyber security fundamentals (Free course) (online classes)
SANS Cyber Aces Online makes available, free and online, selected courses from the professional development curriculum offered by The SANS Institute, the...
-
 200How To
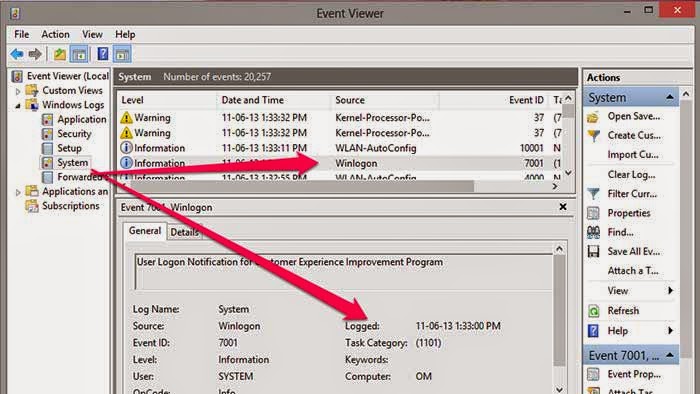
200How ToFind Out If Any One Opens Your Computer Without Your Permission
How to Know Who Logged into your computer and when? In Windows, there is one in-built too will records all events in...
-

 167How To
167How ToProtect your Eyes By Automatically Adjusting Computer Screen Brightness Based On Time of the Day
Today Most of the youngsters using their computers at night very long time than daytime. Staring at your computer screen for the...
-

 73Cyber Crime
73Cyber CrimeiCloud users in China under attack. But who could be after their passwords?
Make sure you are running a half-decent browser, don't ignore browser security warnings, and enable two-factor authentication. That appears to be the...
-

 98Cyber Crime
98Cyber CrimeUK takes aim at serious hacking offenses with planned life sentences
Law makers in Britain are discussing a dramatic increase in sentencing for serious hacking offences, according to The Register. Currently in discussion...
-

 137Password
137PasswordGoogle now offers USB key authentication
Google has added an extra layer of security to its browser, by introducing USB authentication to Chrome, the company has announced in...
-
 262Malware
262MalwareBotnet malware: What it is and how to fight it
Malware or malicious computer code has been around in some form or other for over 40 years, but the use of malware...
-
 347Android Hacking
347Android HackingHow to Hack an android phone
In this tutorial i will show you a guide on how to hack someones android phone. First you will need to root...
-

 119Malware
119MalwareMyths about malware: an exploit is the same as malware
In this post we want to share with you a question that arose from the first post in this series: whether exploits...
-

 91Malware
91MalwareStaples the latest to be hit by credit card breach?
Stationary and office supply store Staples is the latest company to be dealing with a credit and debit card breach, according to...
-
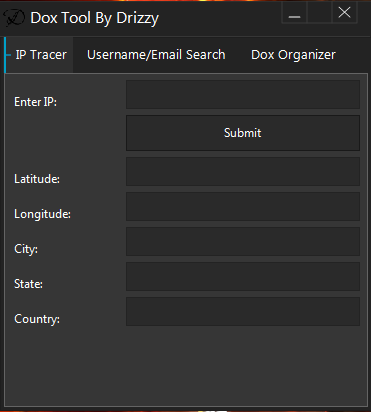
 267Information Gathering
267Information GatheringHow to Dox/Trace like a pro.
Firstly what is doxing? Doxing is a technique used to track, trace, and collect information on individuals or organizations online anonymously. So...
-

 167Password
167PasswordFacebook scans ‘paste sites’ for leaked usernames and passwords
Facebook has a system in place to scan public 'paste' sites for email address and password combinations to stay one step ahead...
-

 197Banking
197BankingObama signs federal credit cards security order
President Barack Obama has signed an executive order to increase security on federal credit cards, and has urged retailers and banks to...
-

 271Malware
271MalwareBotnets: remote controls for cybercriminals
As promised in our post about the European Cyber Security Month during October, we are publishing about Botnets and Exploits this week....
-

 253How To
253How ToHow To Shutdown A Computer With A Cell Phone.
Using this method, a user can shutdown, restart, hibernate, etc. his or her computer, just by sending an email from his or...
The Latest
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
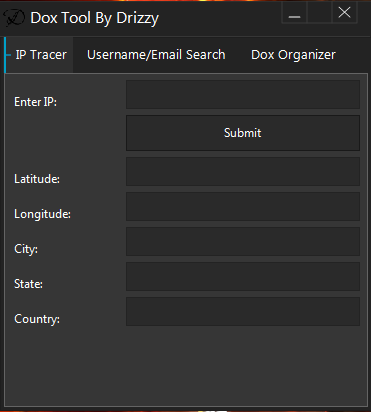
 Malware
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
 Malware
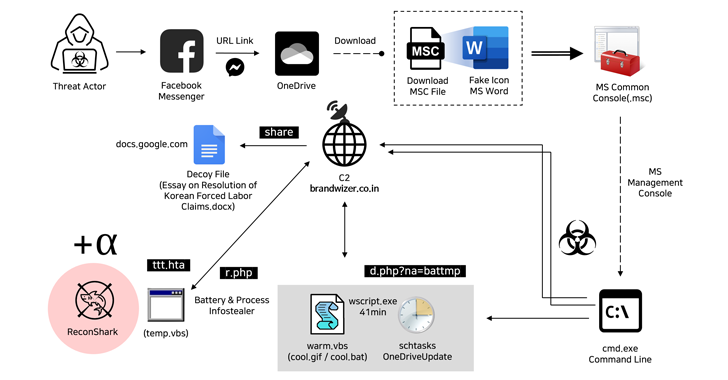
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Malware
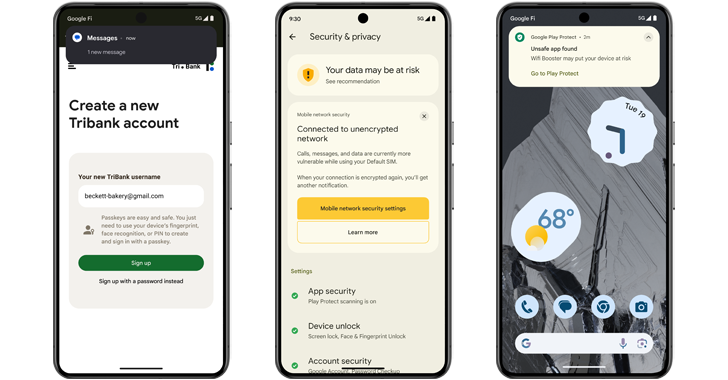
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions
-
 Vulnerabilities
Vulnerabilities(Cyber) Risk = Probability of Occurrence x Damage
-
 Malware
MalwareEbury Botnet Malware Compromises 400,000 Linux Servers Over Past 14 Years
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Vulnerabilities
VulnerabilitiesVMware Patches Severe Security Flaws in Workstation and Fusion Products
-
 Vulnerabilities
VulnerabilitiesNew Chrome Zero-Day Vulnerability CVE-2024-4761 Under Active Exploitation




