Featured News
-

 122How To
122How ToNational Health IT Week – tips for starting Risk Assessment
This week is National Health IT Week, and you may be wondering – what is the best way to observe this occasion?...
-

 94Privacy
94PrivacyRight to be forgotten – why do Americans want it?
A poll has found that more than half (61%) of Americans want a ‘right to be forgotten’ from search engines such as...
-

 80Cyber Crime
80Cyber CrimeWeek in security: Free iPhone scams target eager fans
This week offered a lesson in how cybercriminals follow the news, and time their attacks to dupe the unwary - with several...
-

 78Cyber Crime
78Cyber CrimeScottish independence poll – warning over phishing scams
This Thursday, September 18, is the biggest day in Scottish political history, as the country votes on whether it should become independent...
-

 111Password
111PasswordeBay scam: site ‘slow to react’ after iPhone phishing attack
The dangers of clicking on links in eBay scam postings were highlighted after a fake posting advertising iPhones linked to a phishing...
-

 155Privacy
155PrivacyHow to change Safari’s default search engine in iOS 8 for greater privacy
With iOS 8, you can - for the first time - switch your Safari browser's search engine to alternatives such as DuckDuckGo....
-
Scams
Free iPhone 6 Facebook scam does the rounds, right on time
Facebook scams tend to crop up in the run-up to a big Apple launch with around the same regularity as big Apple...
-

 81Cyber Crime
81Cyber CrimeGTA V hacks warning as gamers ‘lose millions’ in online games
Gamers have reported losing millions of dollars to hackers running customised 'Grand Theft Auto V' software which allows them to steal weapons,...
-

 280Small business
280Small businessIs your business prepared to continue? Watch now and get started with BCM
Planning your 2015 budget? Forecasting 2015 sales? Don't forget a plan to survive "adverse events" from hurricanes to viruses, virtual and medical....
-
 109Password
109PasswordPrinter security: Canon offers ‘fix’ after researcher plays Doom
Printer giant Canon is to provide a security fix “as quickly as is feasible” after a researcher exploited vulnerabilities in one of...
-

 111Password
111PasswordFree ebooks warning: Pirates ‘can hack into Amazon accounts’
Pirates beware: free ebooks available online can be used to hack into Amazon accounts via the retail giant's ‘Manage Your Kindle’ page,...
-

 346Surveillance
346SurveillanceAnti-surveillance mask enables you to pass as someone else
If you are not comfortable with the surveillance cameras, an identity replacement technology that is basically a Surveillance identity prosthetic provides you...
-
 111Malware
111MalwareBeware overdue invoice malware attack, wrapped in an .ARJ file!
Online criminals are spamming out messages claiming that invoices are overdue. But attached to the emails are .ARJ files containing a malicious...
-

 325How To
325How ToHow to Install Gnome Desktop Environment in Ubuntu 14.04 LTS?
Gnome is one of the most popular and most used desktop environment for Linux systems . It is a desktop environment which...
-

 78Cyber Crime
78Cyber CrimePhishing email: UK hit with three times as many ‘bad’ links as U.S.
British internet users opening a spam email are three times more likely to be facing a malicious URL than users in the...
-

 69Cyber Crime
69Cyber CrimeWeek in security: Home Depot speaks, Gmail and Android ‘leak’
This week, American chain Home Depot admitted its systems had been breached, Gmail users got a fright, and a series of videos...
-

 276Lists
276ListsConnect Your Phone and Computer with These Free Apps and Enhance Your Productivity
You can make your phone even more productive if you can connect them with your computer. Connecting them isn’t just about using...
-
 92Privacy
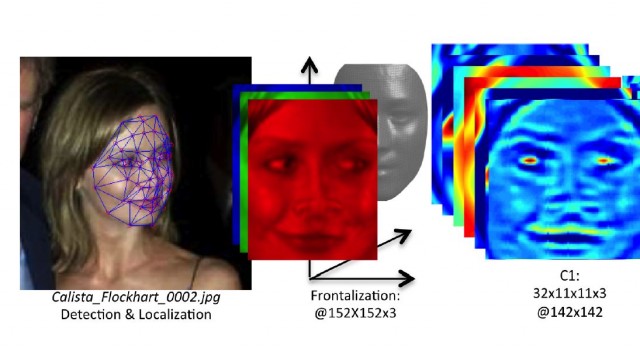
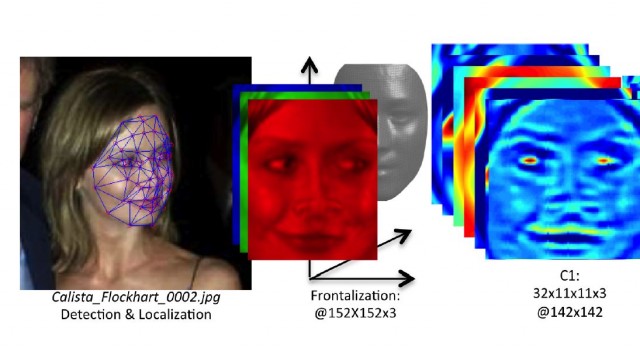
92PrivacyFacebook tag – fears over “Faceprints” after genetic match
A young man who got an email from Facebook ‘identifying’ him via Facebook tag in a series of photographs which turned out...
-

 83Cyber Crime
83Cyber CrimeSalesforce software – millions of users at risk of Dyre malware
A strain of malware which previously targeted banks has turned its attention to users of the popular Customer Relationship Management (CRM) software...
-

 73Cyber Crime
73Cyber CrimeFive million Gmail credentials posted online
Some five million people who used their Gmail address as a user name had their passwords published by someone who apparently thinks...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




