Featured News
-

 193Cyber Crime
193Cyber CrimePSN hacked – Network back after cyber attack and bomb threat
Sony’s PlayStation Network was back online and the information of its 53 million users safe, despite a weekend-long cyber attack, and a...
-

 385Cyber Crime
385Cyber CrimeBitcoin wallet phishing scores unlikely hit with crypto‑curious
A new tactic where waves of Bitcoin wallet phishing emails are targeted at corporations has proved a success for the criminals behind...
-

 398How To
398How ToHow to Download Only Audio from a Youtube Video?
There would have been many times when you wanted to download just the audio of a YouTube video, but not finding any...
-

 94How To
94How ToHow to protect your identity at school
Young people are targeted for data theft at 35 times the rate of adults – they are considered an easy target for...
-

 392Cyber Crime
392Cyber CrimeWeek in security: Nuclear attack, scareware back and traffic‑light hack
This week saw two of the scariest targets for hacks ever - nuclear plants and city-wide traffic systems. Tthe traffic-light hack could...
-
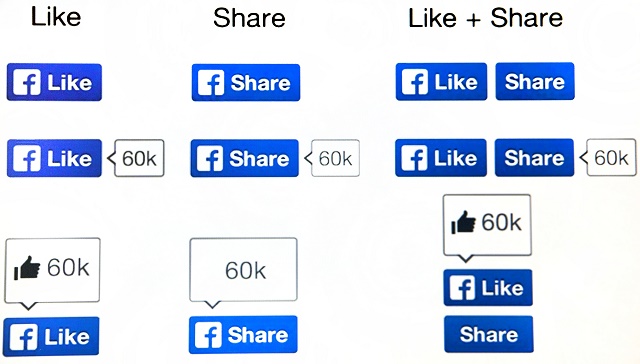
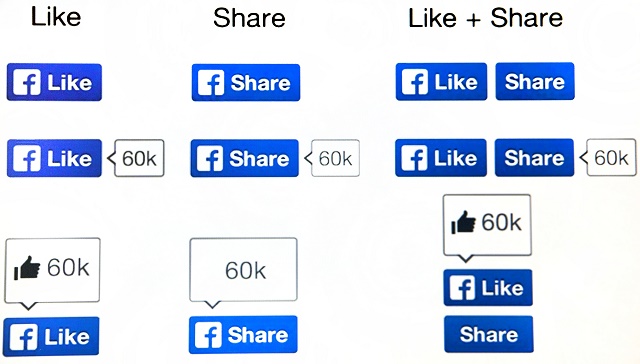 174How To
174How ToFacebook scams – the ‘classics’ and how to avoid them
But some things on Facebook haven’t changed - namely, the scams. It’s not that cybercriminals are unoriginal - it’s just that there...
-
News
Researchers show how to hack Gmail with 92% success rate
Security researchers from University of Michigan and the University of California Riverside Bourns College of Engineering have found out a security flaw...
-
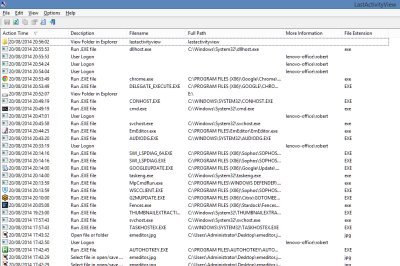
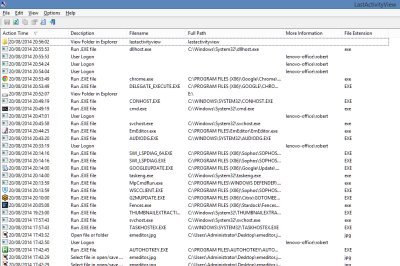 196How To
196How ToFree Software to Monitor Your PC’s Activity
If you ever get asked to fix the PC of a friend or colleague which has been having problems, the first thing...
-

 85Malware
85MalwareScareware: It’s back, and now it’s even scarier
‘Scareware’ - fake antivirus programs which attempt to fool the user into downloading malware, by warning him or her of a “threat”...
-

 74Cyber Crime
74Cyber CrimeFlight MH370 – did cyber attack steal its secret?
Classified documents relating to the missing Malaysian Airlines Flight MH370 were stolen using a carefully-crafted spear-phishing attack, targeting 30 government officials just...
-
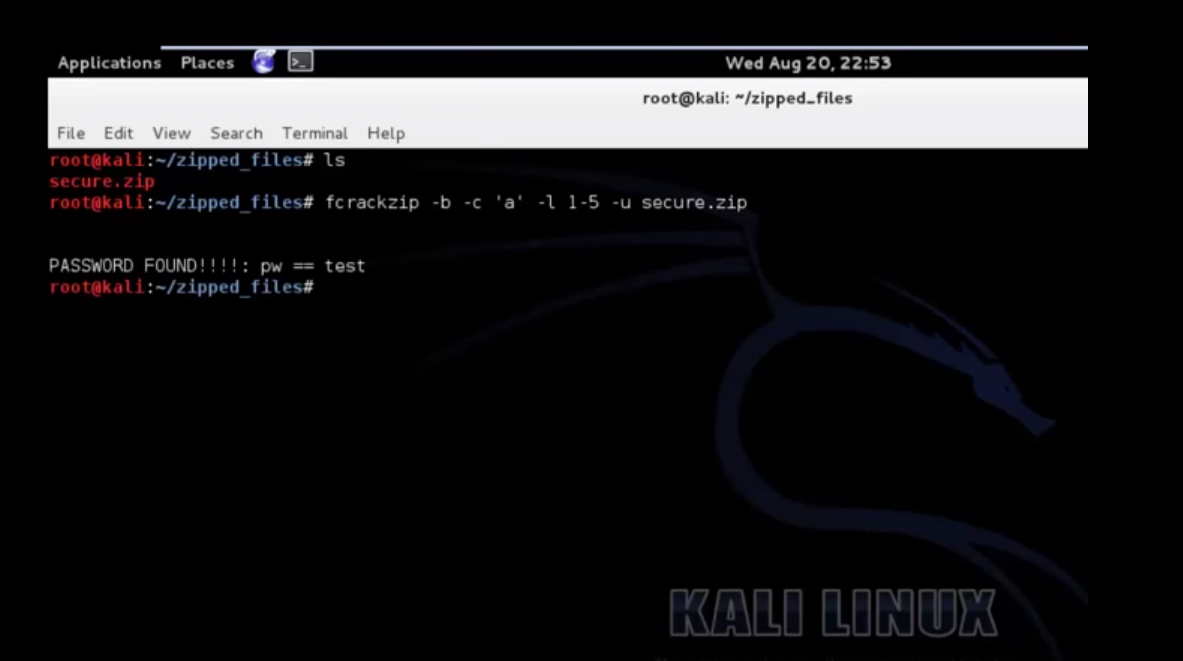
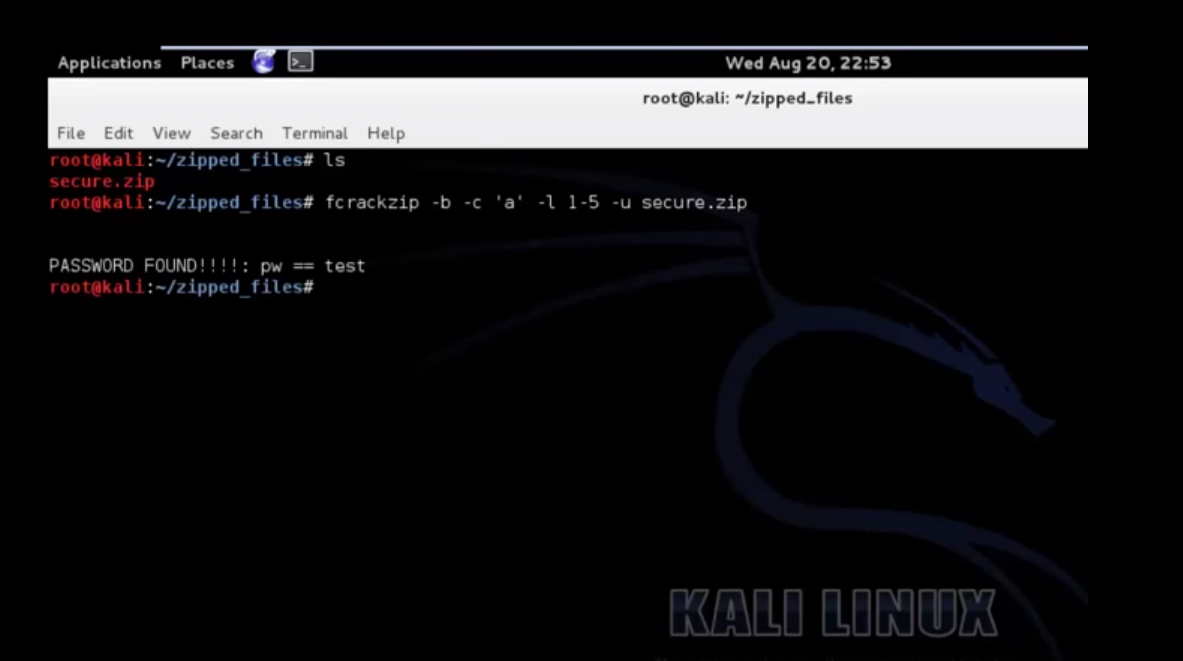 201How To
201How ToCrack A Password Protected Zip File Using Kali
Also Read: Download Kali 2.0 Now
-

 84Cyber Crime
84Cyber CrimeTraffic light – ‘easy’ to hack whole city’s systems
The most famous traffic light ‘hack’ in history is in the classic film, The Italian Job (1969), where the heist involves paralyzing...
-

 90Password
90PasswordPIN number: Police want codes on ALL devices
Police hope to work with leading mobile phone manufacturers such as Samsung to build in the requirement for a password or PIN...
-

 90Password
90PasswordBanking security – new apps ‘know’ your touch
Everyone hates passwords - even the guy who invented them - but some bank app users in the Nordic region are experiencing...
-

 236Lists
236ListsTop 5 Torrent sites of 2014
In the world of torrent downloading, you must understand one thing that there always will be more “Leechers” than “Seeders”. Telling about...
-

 93Malware
93MalwarePhishing emails: U.S. nuke authority hit three times
America’s Nuclear Regulatory Commission was successfully attacked three times within the past hree years, by unknown attackers, some foreign - and largely...
-

 160Privacy
160PrivacyTwitter hacked – Cricket legend ‘Beefy’ Botham exposed
One of England’s greatest-ever cricketers, Sir Ian Botham, appeared to have been the victim of a Twitter hack yesterday as an obscene...
-
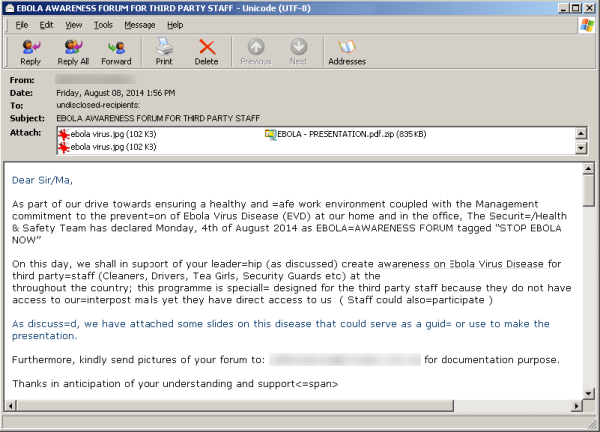
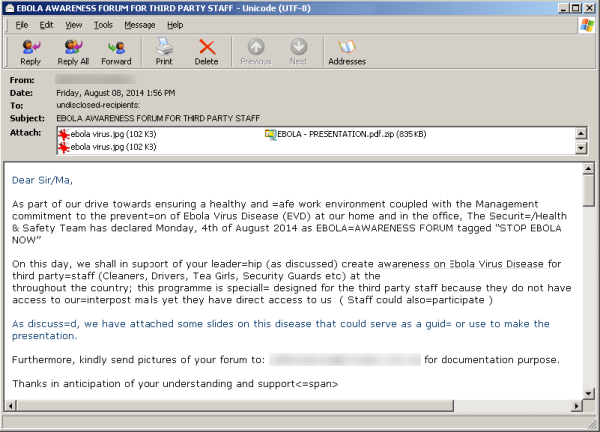 388News
388NewsHackers Sending Fake Ebola Virus reports in emails with Malware and Phishing Links
A new malicious campaign has been identified by security researchers spreading fake news about the Ebola virus, in order to redirect users...
-
 323Geek
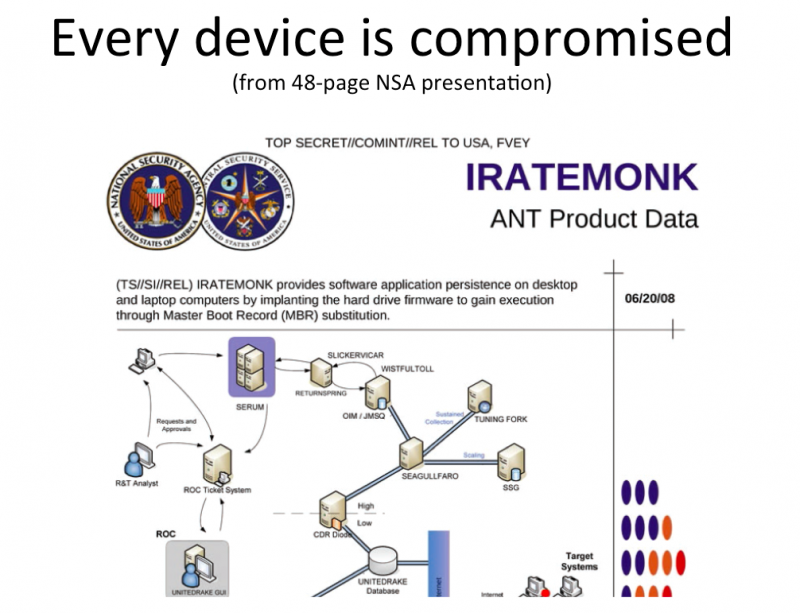
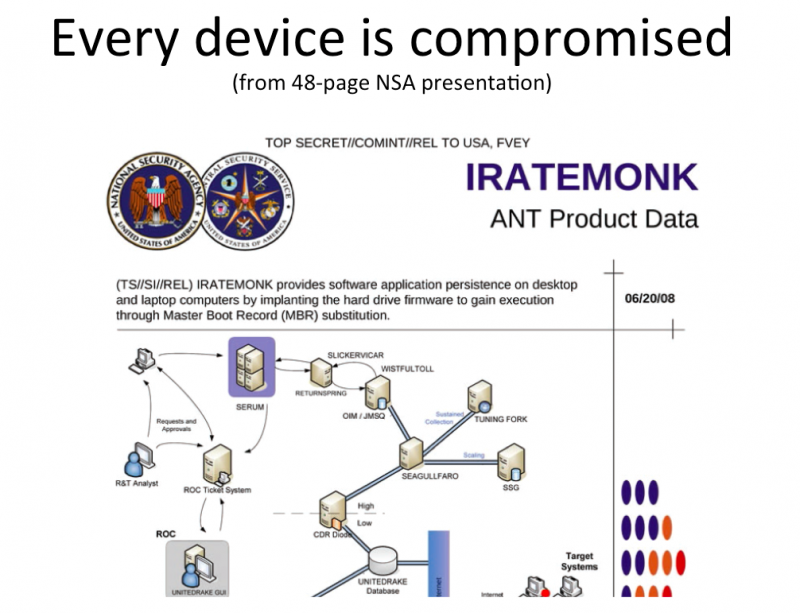
323GeekDon’t freak out about Facebook messenger app, NSA already has your chats
Privacy concerns over the Facebook Chat App is at an all time high. Increasingly more and more people are voicing their concern...
-

 189Privacy
189PrivacyPrivacy: Workers “would pay” to stop snoopers
Online privacy has gone from being a minority concern to something that worries the man in the street - after a study...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




