Featured News
-
 201How To
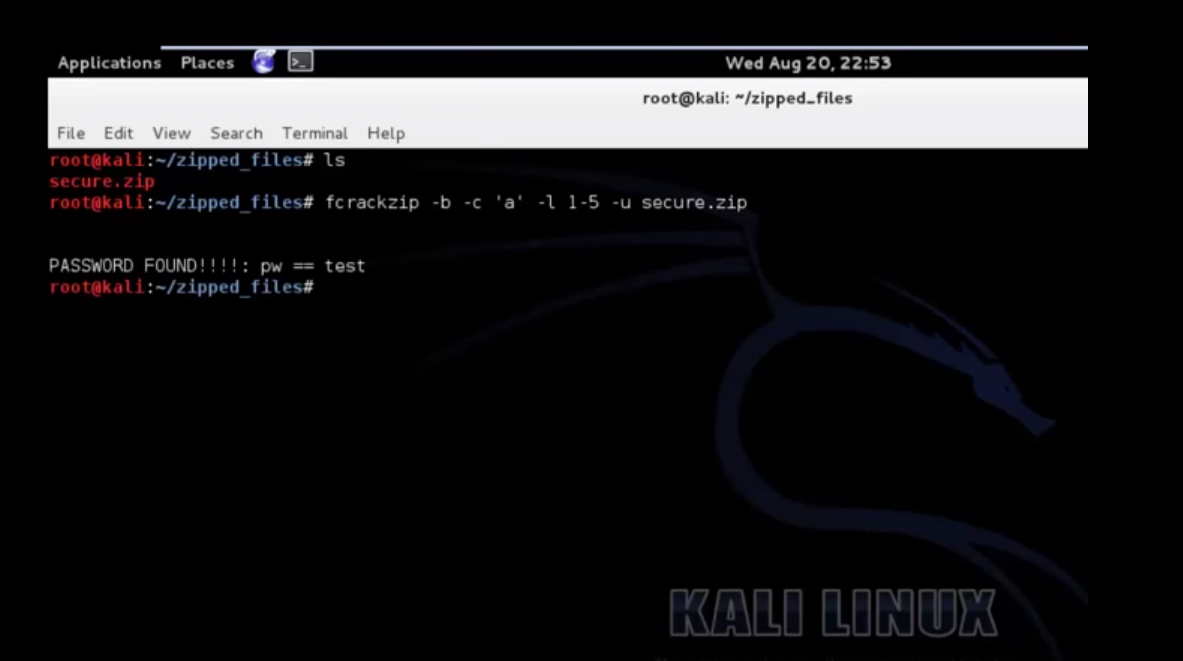
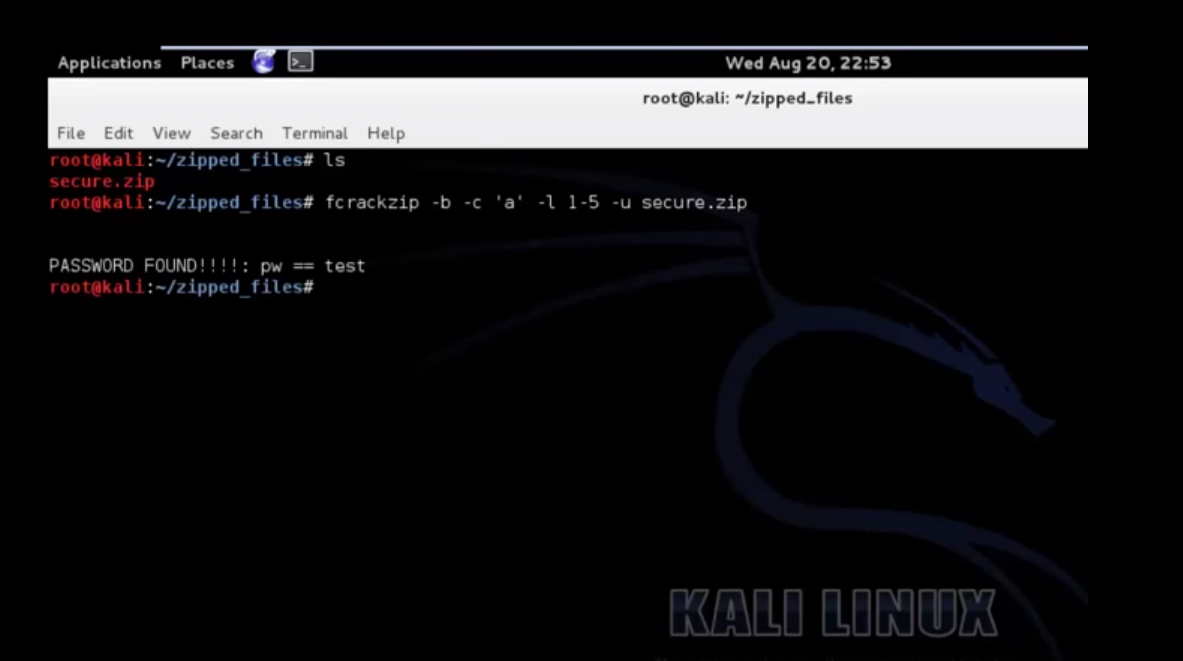
201How ToCrack A Password Protected Zip File Using Kali
Also Read: Download Kali 2.0 Now
-

 84Cyber Crime
84Cyber CrimeTraffic light – ‘easy’ to hack whole city’s systems
The most famous traffic light ‘hack’ in history is in the classic film, The Italian Job (1969), where the heist involves paralyzing...
-

 90Password
90PasswordPIN number: Police want codes on ALL devices
Police hope to work with leading mobile phone manufacturers such as Samsung to build in the requirement for a password or PIN...
-

 89Password
89PasswordBanking security – new apps ‘know’ your touch
Everyone hates passwords - even the guy who invented them - but some bank app users in the Nordic region are experiencing...
-

 235Lists
235ListsTop 5 Torrent sites of 2014
In the world of torrent downloading, you must understand one thing that there always will be more “Leechers” than “Seeders”. Telling about...
-

 93Malware
93MalwarePhishing emails: U.S. nuke authority hit three times
America’s Nuclear Regulatory Commission was successfully attacked three times within the past hree years, by unknown attackers, some foreign - and largely...
-

 160Privacy
160PrivacyTwitter hacked – Cricket legend ‘Beefy’ Botham exposed
One of England’s greatest-ever cricketers, Sir Ian Botham, appeared to have been the victim of a Twitter hack yesterday as an obscene...
-
 387News
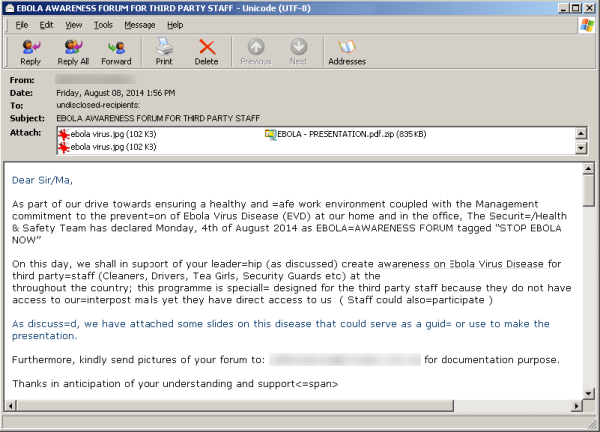
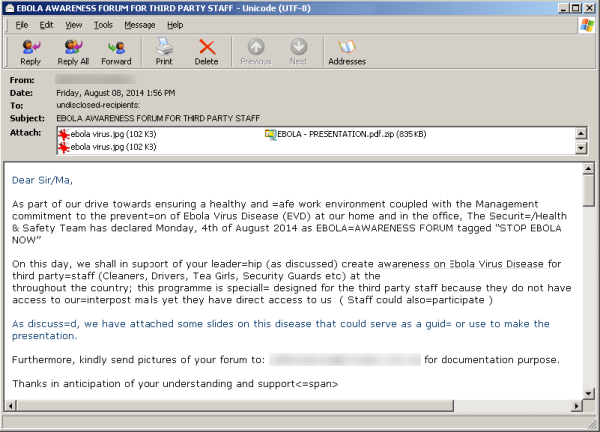
387NewsHackers Sending Fake Ebola Virus reports in emails with Malware and Phishing Links
A new malicious campaign has been identified by security researchers spreading fake news about the Ebola virus, in order to redirect users...
-
 323Geek
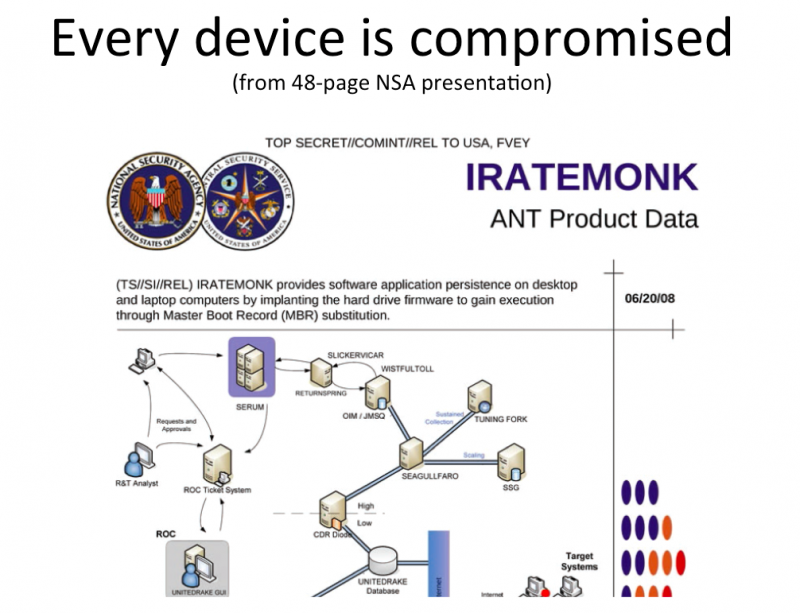
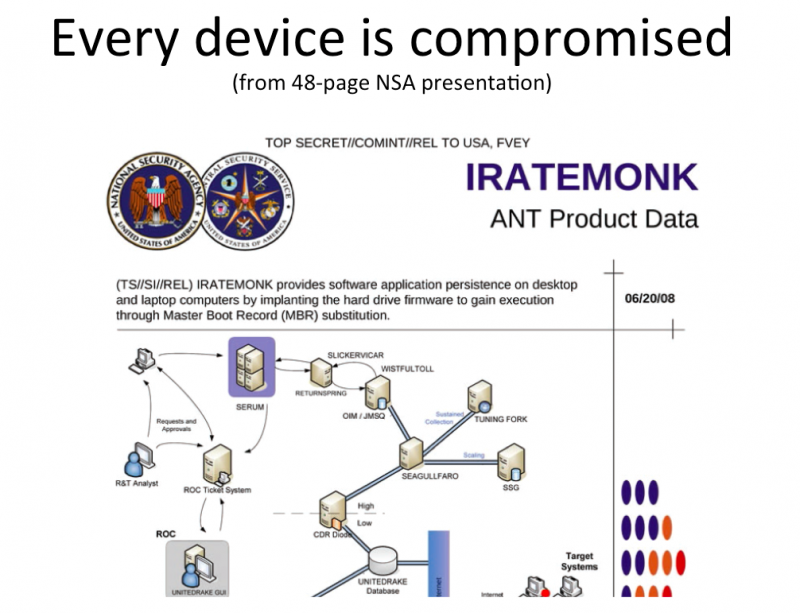
323GeekDon’t freak out about Facebook messenger app, NSA already has your chats
Privacy concerns over the Facebook Chat App is at an all time high. Increasingly more and more people are voicing their concern...
-

 188Privacy
188PrivacyPrivacy: Workers “would pay” to stop snoopers
Online privacy has gone from being a minority concern to something that worries the man in the street - after a study...
-

 81Cyber Crime
81Cyber CrimeGamescom: How gaming grew up into a target for crime
Video games have gone since the late 1970s and early 1980s from being a small offshoot of the "traditional" computing industry to...
-

 168Cyber Crime
168Cyber CrimeWeek in security: Blackphone unmasked, RATs vs Androids, and browsers kill cars
Blackphone, billed as a privacy tool to keep the puplic safe ruled the headlines when it was is hacked in five minutes,...
-

 283Scams
283ScamsRobin Williams’ last phone call? Sick Facebook video scam exploits celebrity suicide
Sick-hearted scammers have proven themselves to have no morals once again, exploiting the death of Robin Williams with their latest Facebook scam.
-

 74Cyber Crime
74Cyber CrimeRussian PM has his Twitter account hacked, announces “I resign”
There may be red faces in Red Square, after Russian prime minister Dmitry Medvedev had his Twitter account hacked.
-

 95Password
95Password‘Biometric’ earbuds invisibly prove it’s you, with no need for passwords
Biometrics are touted as a replacement for the passwords and PINs we all know and hate - and Intel’s new earbuds could...
-

 90Malware
90MalwareGamescom 2014: World of Malware?
The gaming industry keeps growing, and the crowds at Cologne's Gamescom 2014, show why big game titles are rapidly becoming a target...
-

 104Scams
104ScamsPhone scams: card fraud with that steak, Sir?
A new telephone scam in upscale restaurants in London, has “convincing” scammers calling restaurant staff and tricking them into believing there's a...
-

 138Hacking
138HackingWill web browsers turn cars lethal?
Two researchers have launched a petition to change how car companies and technology cmpanies work together - with a new villain: in-car...
-

 93Cyber Crime
93Cyber Crime2FA – are big banks failing America?
The Target breach caused real damage to millions of American card users - but big financial institutions are doing little to remedy...
-

 385Cyber Crime
385Cyber CrimeWɑit! Stοp! Is that ℓιηκ what it claims to be?
Can you tell the difference between exɑmple and example? Google adds non-Latin support to Gmail, and we explain why characters matter when...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




