Featured News
-

 163News
163NewsGoogle Image Search Hacked? Search results filled with Russian car crash images
Users witness looking at pictures of Russian car crash regardless of what they searched on Google Images. If someone searched for ‘cat’ the search result...
-

 69Cyber Crime
69Cyber CrimeOnline fraud – POS malware has now hit 1,000 U.S. firms
More than a thousand U.S. businesses have been affected by point-of-sale malware - malicious software written specifically for online fraud, to steal...
-

 86Cyber Crime
86Cyber CrimeGoogle Images hacked? Searches fill with morbid image
An image of a Russian car crash has piled up in Google Images - leading to speculation that the service has been...
-

 245Lists
245Lists2014 Emmy Award Winners : Breaking Bad Wins Big, Game of Thrones Scores Zero
2014 Emmy Awards were pretty much unsurprising and a lot of fan favorites won. NBC drama Breaking Bad won the Emmy Award for...
-

 198Cyber Crime
198Cyber CrimePSN hacked – Network back after cyber attack and bomb threat
Sony’s PlayStation Network was back online and the information of its 53 million users safe, despite a weekend-long cyber attack, and a...
-

 391Cyber Crime
391Cyber CrimeBitcoin wallet phishing scores unlikely hit with crypto‑curious
A new tactic where waves of Bitcoin wallet phishing emails are targeted at corporations has proved a success for the criminals behind...
-

 407How To
407How ToHow to Download Only Audio from a Youtube Video?
There would have been many times when you wanted to download just the audio of a YouTube video, but not finding any...
-

 100How To
100How ToHow to protect your identity at school
Young people are targeted for data theft at 35 times the rate of adults – they are considered an easy target for...
-

 399Cyber Crime
399Cyber CrimeWeek in security: Nuclear attack, scareware back and traffic‑light hack
This week saw two of the scariest targets for hacks ever - nuclear plants and city-wide traffic systems. Tthe traffic-light hack could...
-
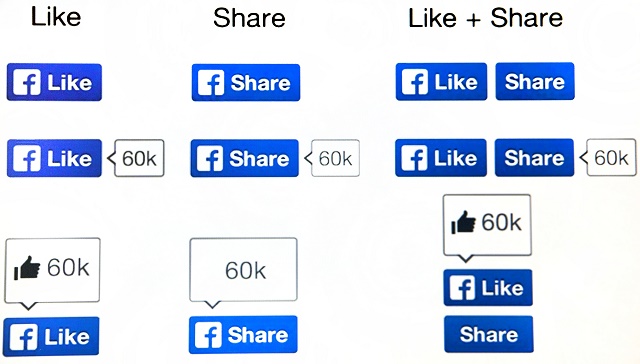
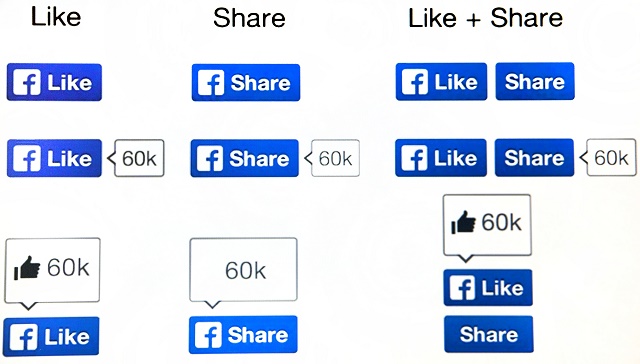 180How To
180How ToFacebook scams – the ‘classics’ and how to avoid them
But some things on Facebook haven’t changed - namely, the scams. It’s not that cybercriminals are unoriginal - it’s just that there...
-
News
Researchers show how to hack Gmail with 92% success rate
Security researchers from University of Michigan and the University of California Riverside Bourns College of Engineering have found out a security flaw...
-
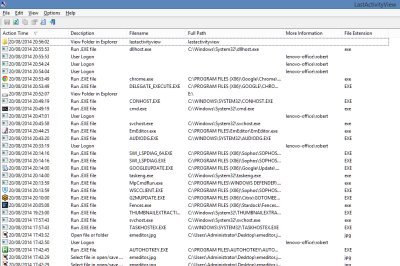
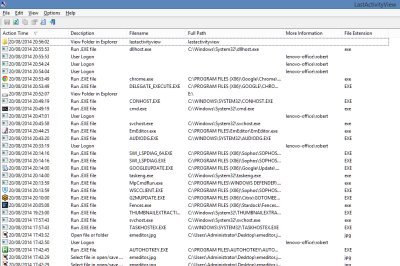 200How To
200How ToFree Software to Monitor Your PC’s Activity
If you ever get asked to fix the PC of a friend or colleague which has been having problems, the first thing...
-

 93Malware
93MalwareScareware: It’s back, and now it’s even scarier
‘Scareware’ - fake antivirus programs which attempt to fool the user into downloading malware, by warning him or her of a “threat”...
-

 79Cyber Crime
79Cyber CrimeFlight MH370 – did cyber attack steal its secret?
Classified documents relating to the missing Malaysian Airlines Flight MH370 were stolen using a carefully-crafted spear-phishing attack, targeting 30 government officials just...
-
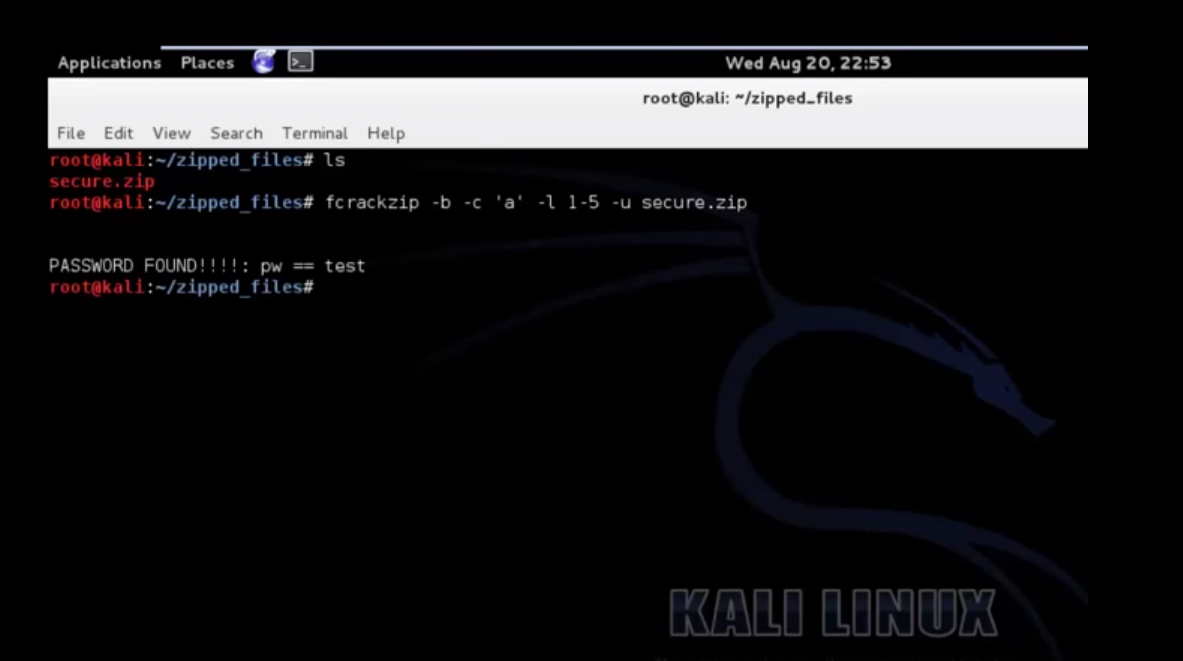
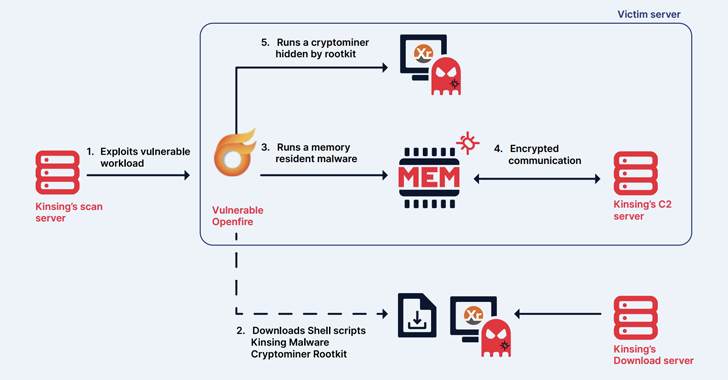
 209How To
209How ToCrack A Password Protected Zip File Using Kali
Also Read: Download Kali 2.0 Now
-

 93Cyber Crime
93Cyber CrimeTraffic light – ‘easy’ to hack whole city’s systems
The most famous traffic light ‘hack’ in history is in the classic film, The Italian Job (1969), where the heist involves paralyzing...
-

 99Password
99PasswordPIN number: Police want codes on ALL devices
Police hope to work with leading mobile phone manufacturers such as Samsung to build in the requirement for a password or PIN...
-

 96Password
96PasswordBanking security – new apps ‘know’ your touch
Everyone hates passwords - even the guy who invented them - but some bank app users in the Nordic region are experiencing...
-

 243Lists
243ListsTop 5 Torrent sites of 2014
In the world of torrent downloading, you must understand one thing that there always will be more “Leechers” than “Seeders”. Telling about...
-

 101Malware
101MalwarePhishing emails: U.S. nuke authority hit three times
America’s Nuclear Regulatory Commission was successfully attacked three times within the past hree years, by unknown attackers, some foreign - and largely...
The Latest
-
 Data Breach
Data BreachAre Your SaaS Backups as Secure as Your Production Data?
-
 Data Breach
Data BreachMS Exchange Server Flaws Exploited to Deploy Keylogger in Targeted Attacks
-
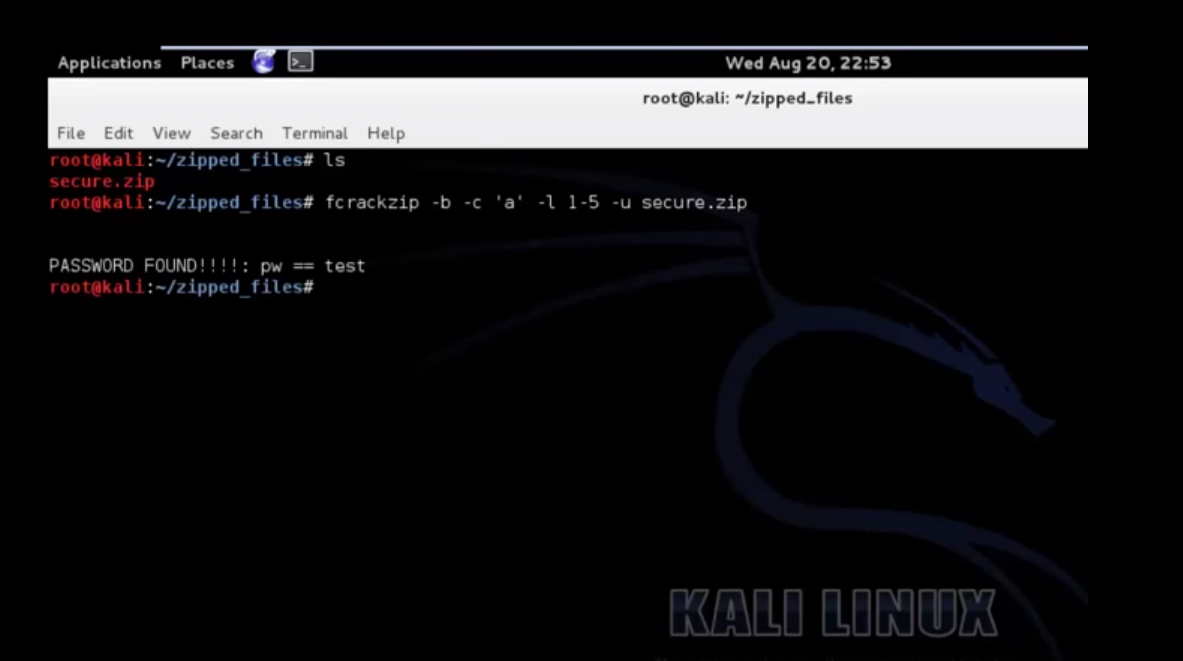
 Data Breach
Data BreachSolarMarker Malware Evolves to Resist Takedown Attempts with Multi-Tiered Infrastructure
-
 Cyber Attack
Cyber Attack“Linguistic Lumberjack” Vulnerability Discovered in Popular Logging Utility Fluent Bit
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
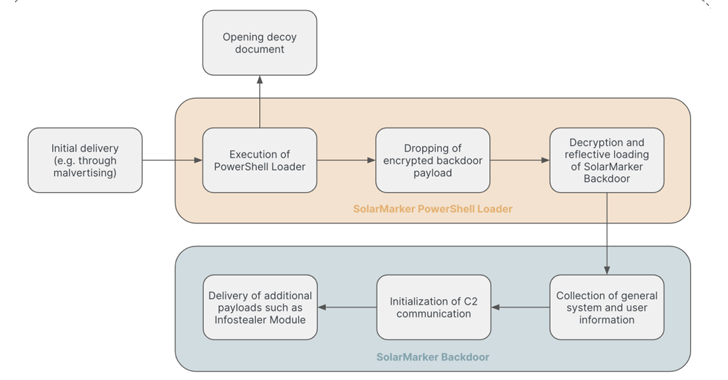
 Malware
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
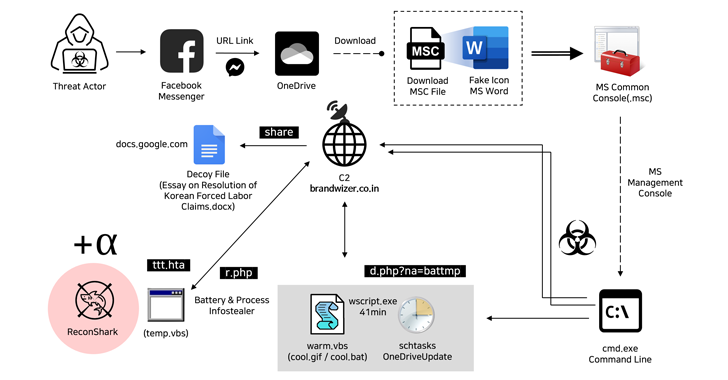 Malware
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
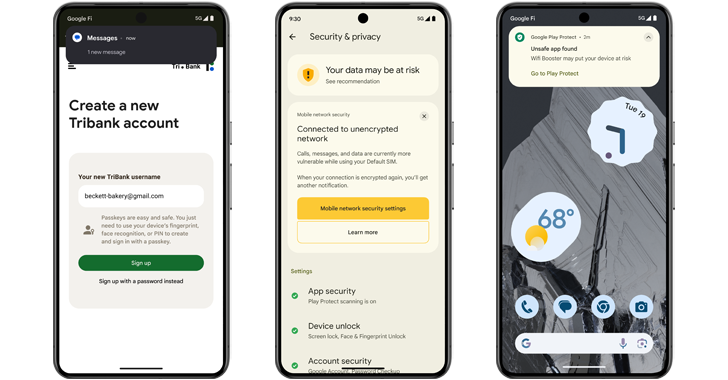 Malware
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions
-
 Vulnerabilities
Vulnerabilities(Cyber) Risk = Probability of Occurrence x Damage




