Featured News
-

 71Cyber Crime
71Cyber Crime‘Sextortion’ blackmail attacks on the rise, Police warn
‘Sextortion’ attacks where cybercriminals blackmail victims with the threat of exposing explicit photographs or messages are increasingly common, according to a report...
-

 76Cyber Crime
76Cyber CrimeInsider threat – should you worry about the ‘enemy within’?
Disgruntled employees and other malicious insiders could be one of the most serious security threats companies face - but the importance of...
-

 220Scams
220ScamsFacebook scams target grieving families of Flight MH17
Callous cybercriminals have used the Malaysia Airlines Flight MH17 tragedy as a lure for Facebook scams - creating fake profiles for victims...
-

 224Cyber Events
224Cyber EventsAnonymous asks Elite hackers to join them in a massive cyber attack on Israel
The online hacktivist Anonymous has a message for Israeli government in which the group has asked elite hackers from around the world...
-

 290News
290NewsPalestinians and Israelis take battle to social networks
Now, the battle waged by both sides also extends to social networks. Israelis and Palestinians are increasingly using sophisticated methods in an attempt...
-

 340Data Security
340Data SecurityDangerous Malware steals credit card information from Android devices
Security experts at Dr. Web have warned Android users to be careful with a new Trojan that is stealing credit card details while...
-

 377Password
377PasswordWi‑Fi security alert on Chromecast as ‘Rickmote’ hijacks nearby boxes
A security researcher has built a remote control which hijacks any nearby Chromecast highlighting a Wi-Fi security issue, which allows an attacker...
-
 109Privacy
109PrivacyPrivacy concerns over Police ‘instant ID’ camera trial
New facial recognition technology which can instantly identify people from any digital image in seconds is being trialled in the UK for...
-

 317News
317NewsIsrael’s Channel 10 TV Station Hacked by Hamas
Hackers from Hamas military wing in Palestine hacked the satellite communication of the Channel 10 TV station in Israel on Monday for a few...
-

 104Cyber Crime
104Cyber CrimeHacked Japanese porn sites spread banking malware attack
Thinking of spending some time perusing Japanese porn websites before you do your online banking? Security researchers at ESET have analysed an...
-

 179Cyber Crime
179Cyber CrimeWin32/Aibatook: Banking Trojan Spreading Through Japanese Adult Websites
Win32/Aibatook targets Japanese bank customers with an unusual Internet Explorer monitoring technique. We believe the malware has been in development for months...
-

 102Privacy
102PrivacyArtist mails NSA ‘uncrackable’ mixtape
An artist has created what he claims to be an ‘uncrackable’ mixtape, using freely available encryption tools and housed on a home-made...
-
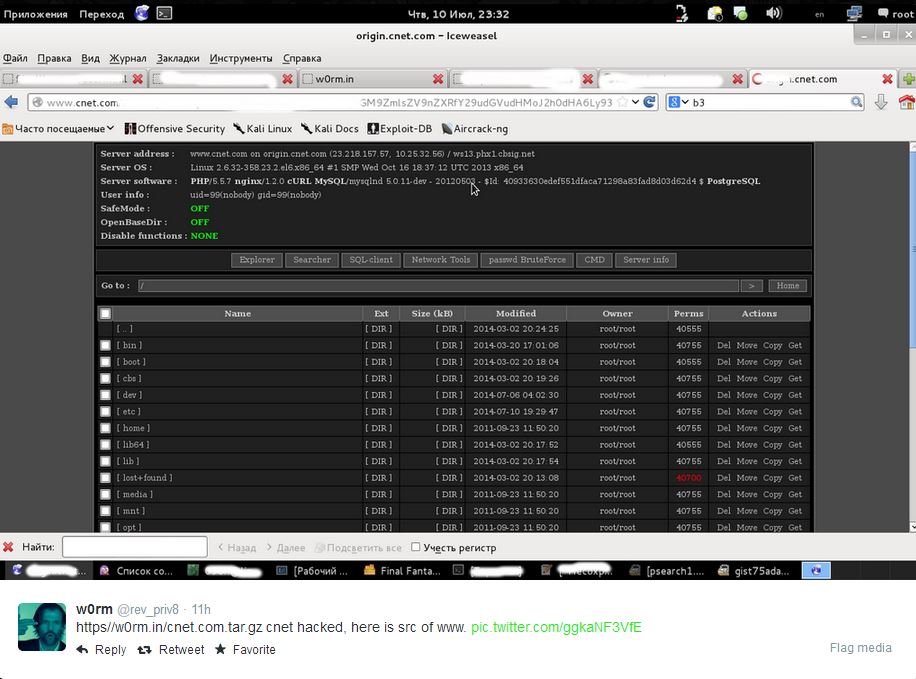
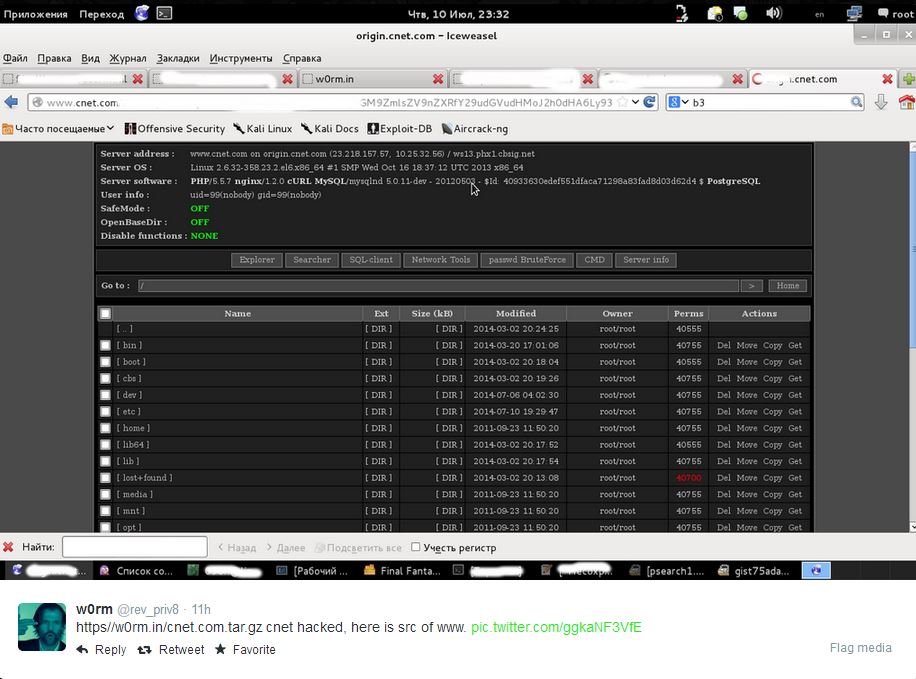 81Cyber Crime
81Cyber CrimeCNET ‘database leak’ – are your details safe?
Popular technology news and review website CNET faced the threat of having a million users' data exposed this week, with an unknown...
-
 146News
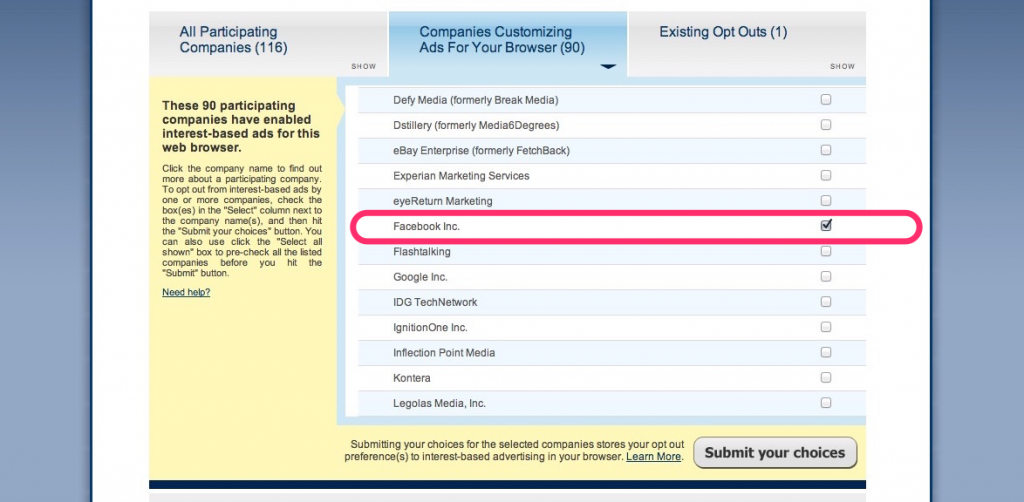
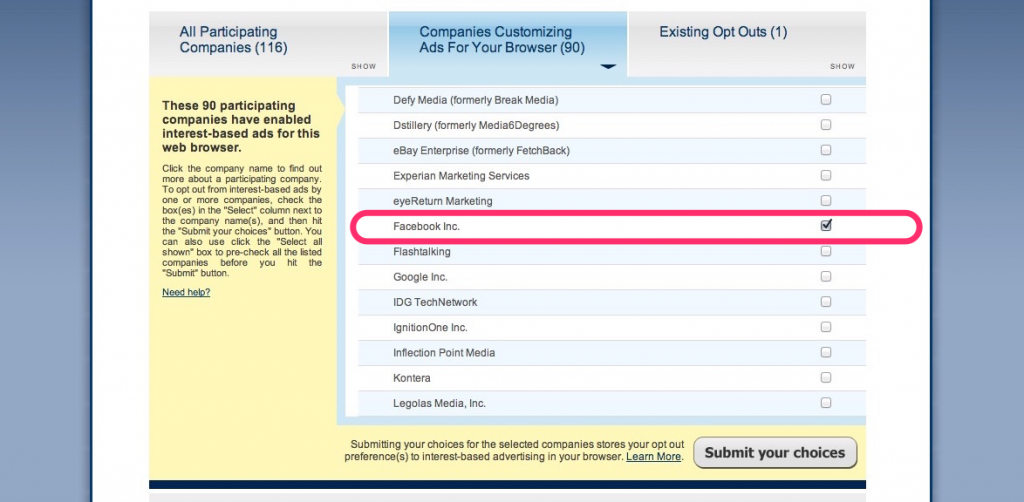
146NewsThis is How You Stop Facebook From Using Your Browsing History
A couple of weeks ago, the social media giant Facebook announced that in order to serve us with targeted ads – it will starting...
-

 73Cyber Crime
73Cyber CrimeData breaches in New York have tripled
Data breaches have hit a record high in the state of New York, tripling since 2006, according to records released by the...
-

 63Cyber Crime
63Cyber CrimeGoogle Chrome security warnings – now in plain English
“Phishing attack ahead” is similar to the stark, clear warnings delivered by road signs - and web users will soon benefit from...
-

 69Cyber Crime
69Cyber CrimeKeylogger malware in hotel business centers – should you worry?
Guests who used business centers in American hotels may be at risk from gangs installing keylogger malware on the computers to steal...
-

 185Password
185PasswordRetina scanner for Samsung Galaxy Note 4?
A Tweet from an official Samsung Galaxy Note 4 account has dropped a very unsubtle hint that its upcoming Galaxy Note 4...
-

 112Privacy
112PrivacyLastPass security holes found by researcher, says password management firm – but no need to panic
LastPass has gone public about a couple of security holes that were found in its popular online password management software. That's enough...
-
 224How To
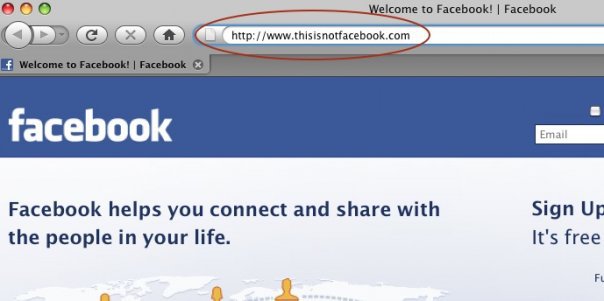
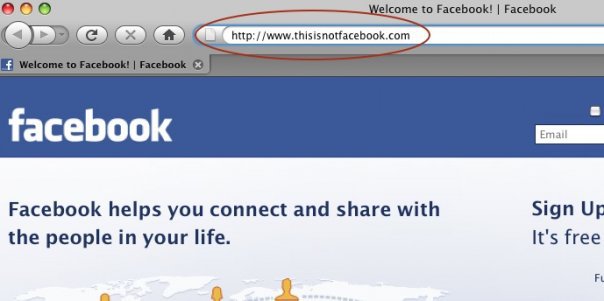
224How ToHow do Facebook accounts get hacked [Protect Yourself Against It]
Facebook phishing. Phishing is a way of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




