Featured News
-

 180Cyber Crime
180Cyber CrimeWin32/Aibatook: Banking Trojan Spreading Through Japanese Adult Websites
Win32/Aibatook targets Japanese bank customers with an unusual Internet Explorer monitoring technique. We believe the malware has been in development for months...
-

 103Privacy
103PrivacyArtist mails NSA ‘uncrackable’ mixtape
An artist has created what he claims to be an ‘uncrackable’ mixtape, using freely available encryption tools and housed on a home-made...
-
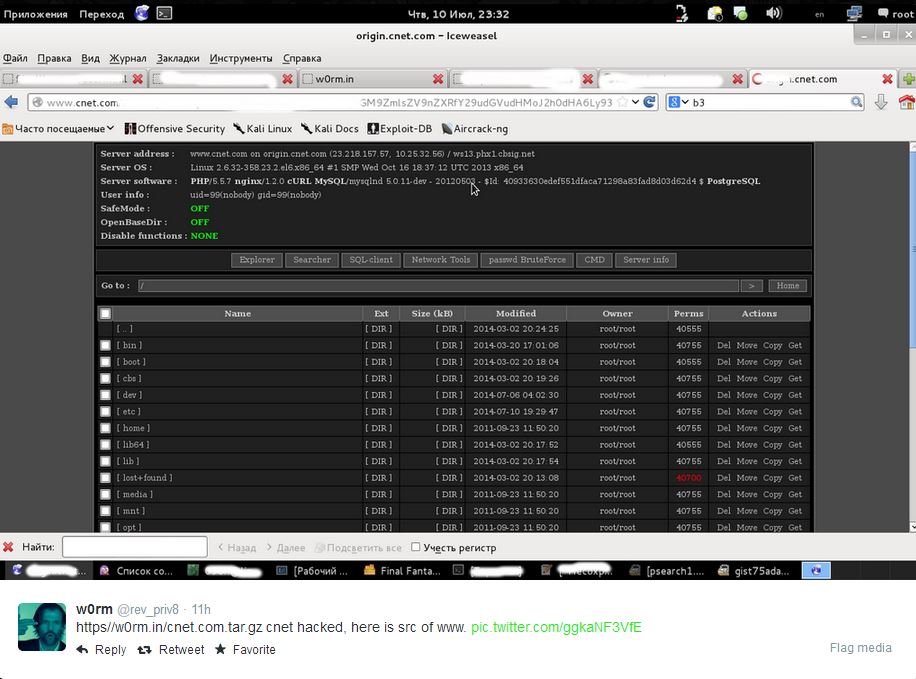
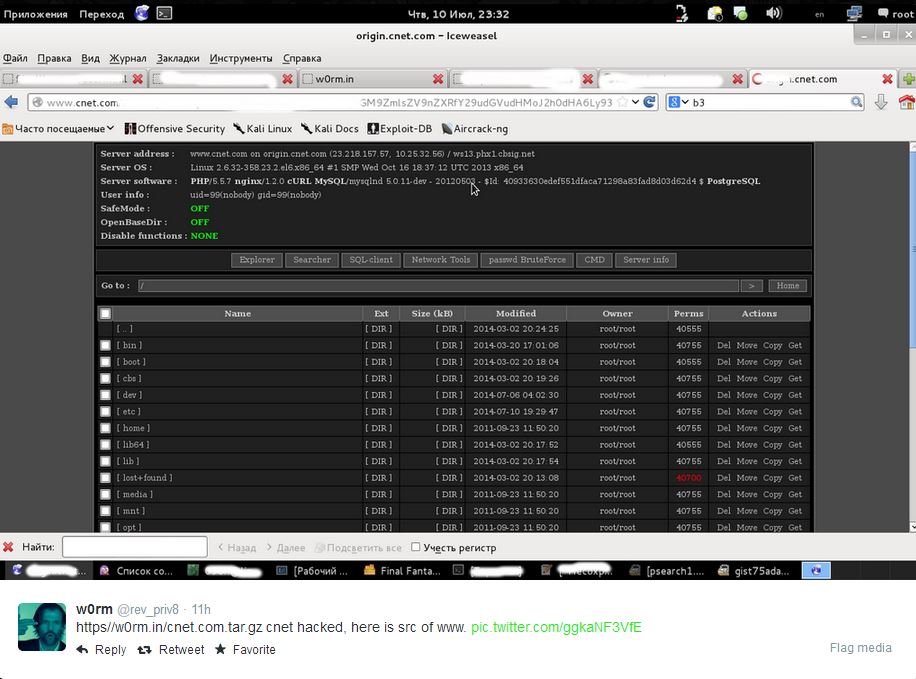 82Cyber Crime
82Cyber CrimeCNET ‘database leak’ – are your details safe?
Popular technology news and review website CNET faced the threat of having a million users' data exposed this week, with an unknown...
-
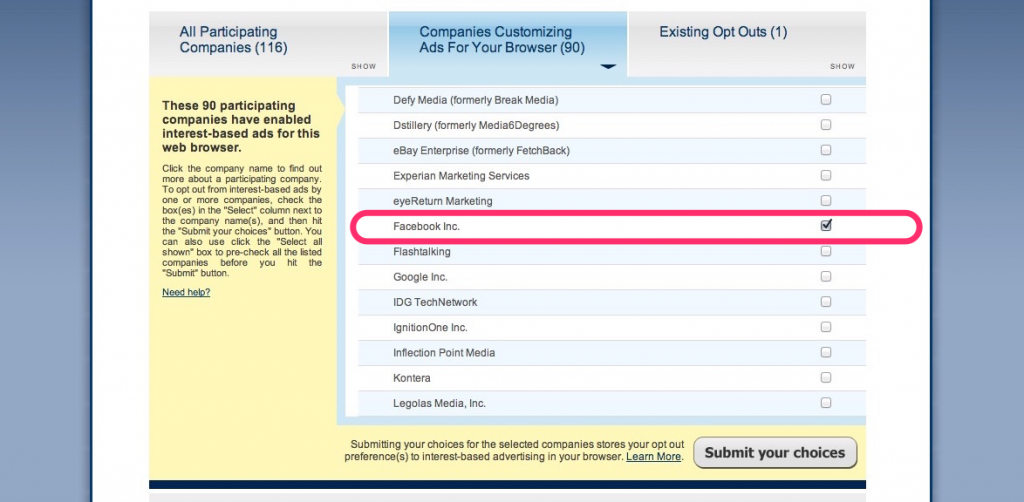
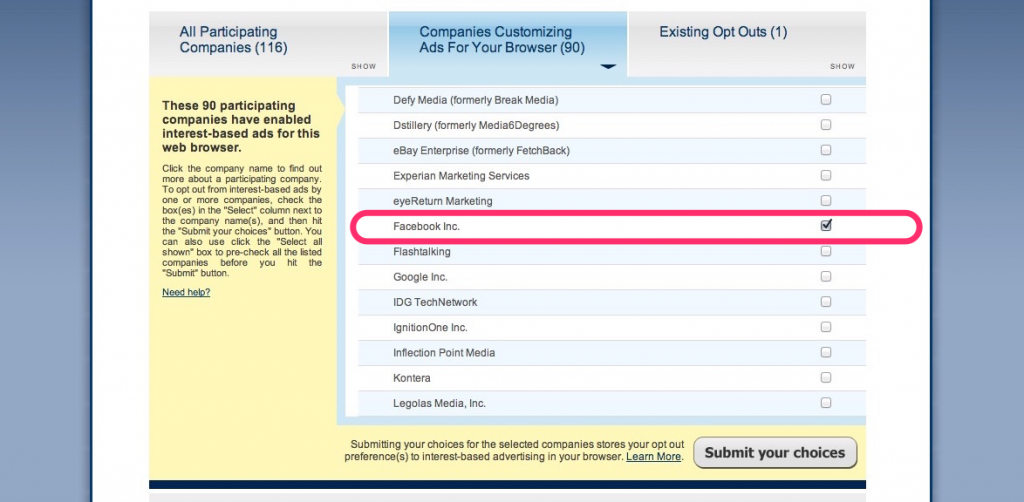 147News
147NewsThis is How You Stop Facebook From Using Your Browsing History
A couple of weeks ago, the social media giant Facebook announced that in order to serve us with targeted ads – it will starting...
-

 74Cyber Crime
74Cyber CrimeData breaches in New York have tripled
Data breaches have hit a record high in the state of New York, tripling since 2006, according to records released by the...
-

 64Cyber Crime
64Cyber CrimeGoogle Chrome security warnings – now in plain English
“Phishing attack ahead” is similar to the stark, clear warnings delivered by road signs - and web users will soon benefit from...
-

 70Cyber Crime
70Cyber CrimeKeylogger malware in hotel business centers – should you worry?
Guests who used business centers in American hotels may be at risk from gangs installing keylogger malware on the computers to steal...
-

 186Password
186PasswordRetina scanner for Samsung Galaxy Note 4?
A Tweet from an official Samsung Galaxy Note 4 account has dropped a very unsubtle hint that its upcoming Galaxy Note 4...
-

 113Privacy
113PrivacyLastPass security holes found by researcher, says password management firm – but no need to panic
LastPass has gone public about a couple of security holes that were found in its popular online password management software. That's enough...
-
 225How To
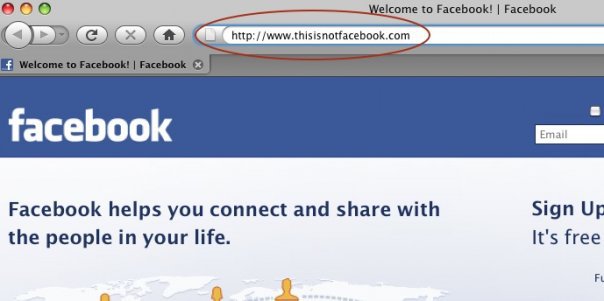
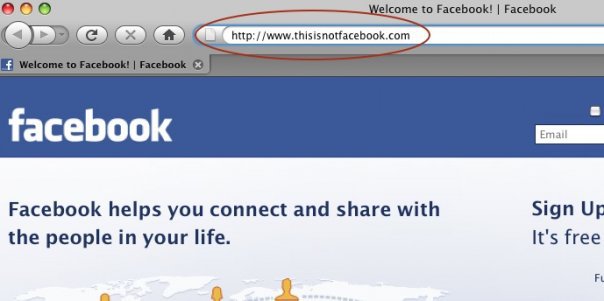
225How ToHow do Facebook accounts get hacked [Protect Yourself Against It]
Facebook phishing. Phishing is a way of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as...
-

 78Cyber Crime
78Cyber CrimeBanking malware Shylock’s servers knocked out by law enforcement
A notorious strain of banking malware, known as Caphaw - or Shylock, due to snippets of Shakespeare’s Merchant of Venice embedded in...
-

 126Privacy
126PrivacyGoogle Drive privacy warning – could yours have leaked data?
Files sent as a link from Google Drive could have shared more than their senders intended, Google admitted this week - in...
-

 2.3KCyber Events
2.3KCyber EventsNorway�s financial sector under massive cyber attack, Anonymous claims �responsibility�
Norway�s�top financial institutions came under massive cyber attacks on Tuesday.Anonymous Norway appears to be behind this attack. The attack�on Norway�s�top financial institutions/banks,...
-

 90Malware
90MalwareCopyright emails ‘poisoned with Trojan’
Emails warning internet users that they have violated copyright and owe companies such as Sony and Paramount a cash settlement have been...
-

 89Cyber Crime
89Cyber CrimeNigerian scams expand to Malaysia – fraud doubles
Nigeria’s notorious fraud industry has expanded overseas - with Nigerian conmen entering Malaysia on student visas to perpetrate fraud using the country’s...
-

 136Privacy
136PrivacyHow to remove your house from Google Street View
How are YOU supposed to remove your house from Google Street View if you don't like the idea that Google drove one...
-

 497Cyber Crime
497Cyber CrimeNew ‘slimline’ ATM skimmers are near‑invisible
New ‘slimline’ ATM skimmers are proving far harder to spot - with some of the hi-tech models remaining in place for up...
-

 157Geek
157GeekAmazon Fire Phone: An Amazing Smartphone (Specifications)
Amazon�s new smartphone launch is all set to fire up the smartphone market and is likely to give a hard time to...
-

 113Privacy
113PrivacyCould latest NSA revelations further impact online behavior, denting the economy?
Internet surveillance by America's National Security Agency (NSA) has been further exposed by two new developments: the analysis of leaked NSA surveillance...
-

 181How To
181How ToFacebook settings – five steps for better privacy and security
Facebook has faced repeated controversy over privacy, with features such as Graph Search revealing information which users might have forgotten they ever...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




