Featured News
-
 257News
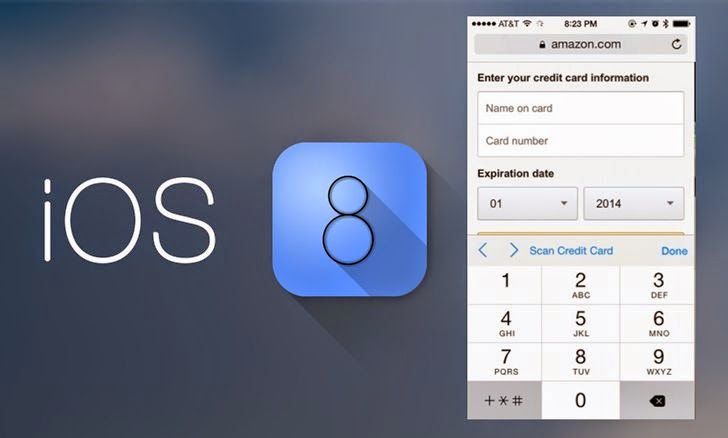
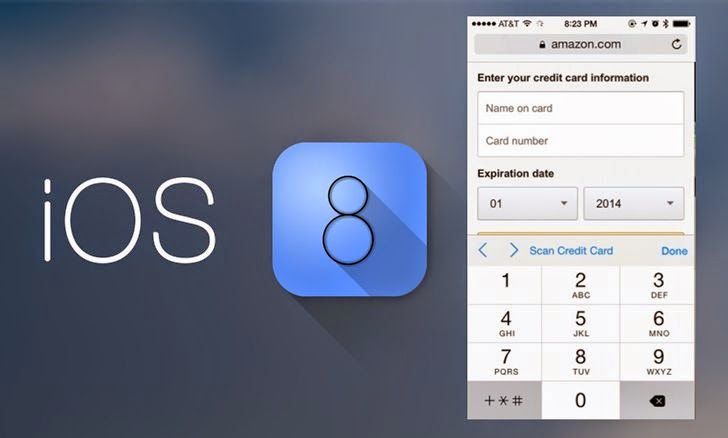
257NewsiOS 8 Safari Browser on iPhone and iPad Can Read Your Credit Card Details
Your iPad or iPhone’s camera has become immensely powerful after the emergence of iOS 8 Safari’s new version. Its most astounding feature...
-

 93Malware
93MalwareRansomware 101: FAQ for computer users and smartphone owners
Do you know what ransomware is? Do you know a filecoder from a lockscreen? Read our FAQ to become more clued-up about...
-
 85Password
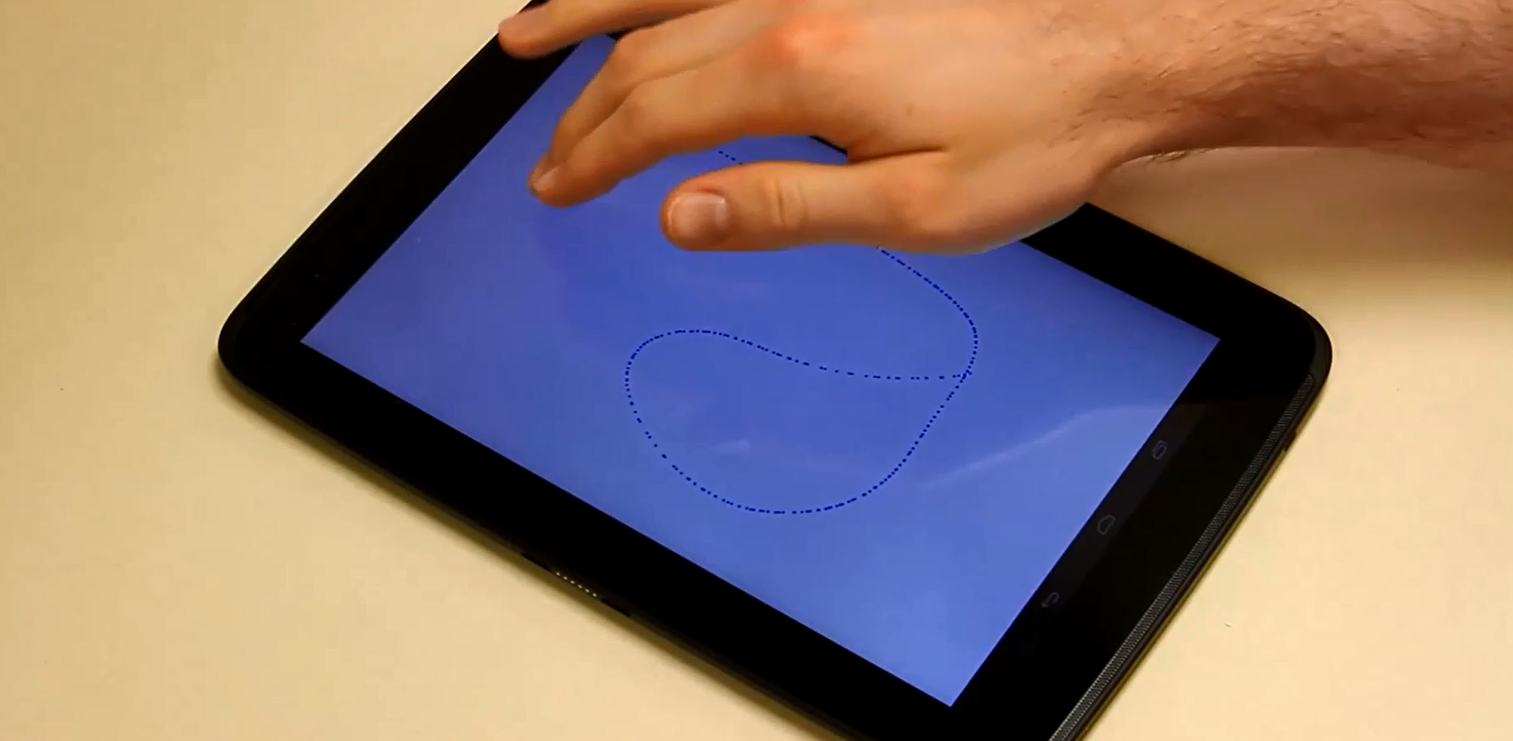
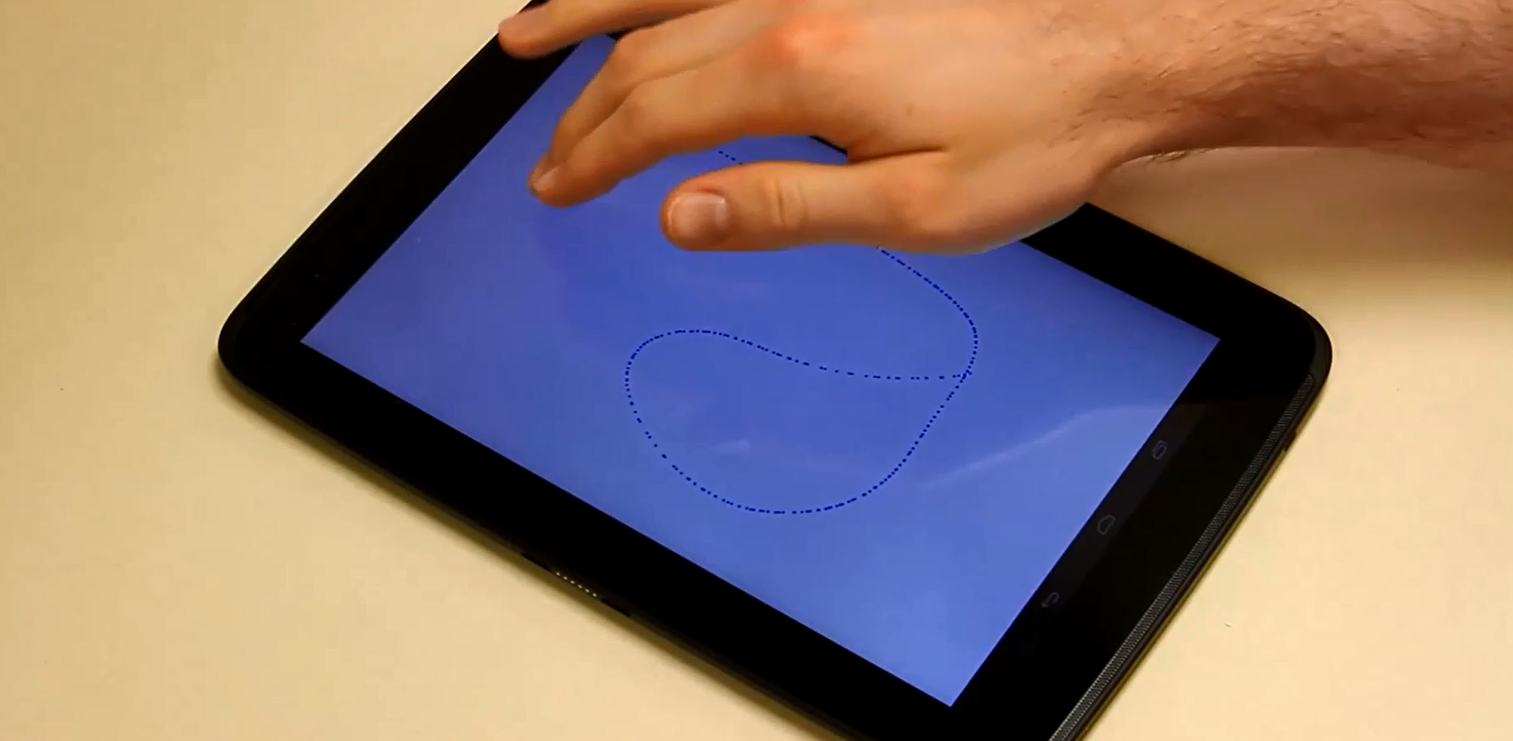
85PasswordDrawing “signature” on screen could replace passwords, study finds
Even smartphone and tablet users who choose a four-digit PIN to protect their device are vulnerable to “shoulder surfers” glimpsing the code...
-

 101How To
101How ToAndroid malware: how to keep your device safe from filecoders (and everything else)
When ESET researchers analyzed the first Android ransomware controlled via Tor, it showed how quickly Android malware is evolving to match its...
-

 176Privacy
176PrivacyNSA faces fresh revelations as Snowden anniversary arrives
On the one year anniversary of Edward Snowden's public revelations of mass surveillance conducted by the U.S. National Security Agency we look...
-
 203Cyber Crime
203Cyber CrimeDARPA to hold $2m Grand Challenge for “fully automated” cyber defense systems
The hi-tech research wing of the US military DARPA (Defence Advanced Research Projects Agency) is to offer a $2 million prize offered...
-

 119Privacy
119PrivacyEngland footballers have their passport details leaked on Twitter
In an embarrassing breach of security, the passport numbers of members of the England Football squad have been accidentally tweeted out by...
-
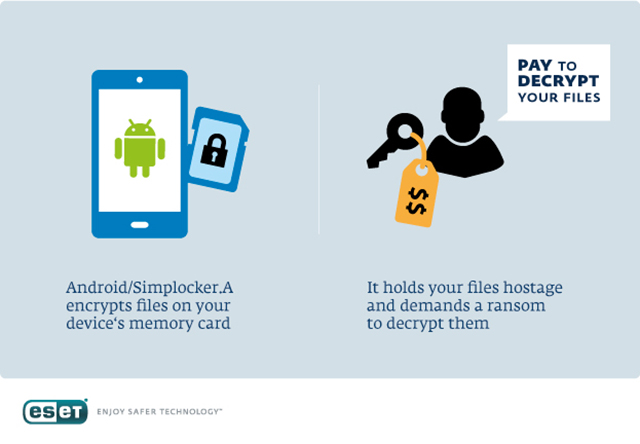
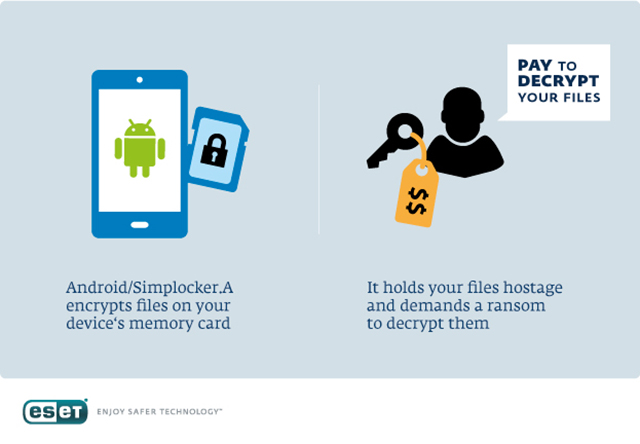 417Malware
417MalwareESET Analyzes Simplocker – First Android File‑Encrypting, TOR‑enabled Ransomware
Last weekend saw the (somewhat anticipated) discovery of an interesting mobile trojan – the first spotting of a file-encrypting ransomware for Android...
-

 89Malware
89MalwareWindows XP users slow to upgrade despite risks
Users of Windows XP are not upgrading to safer versions of the operating system after the April 8 deadline when Microsoft stopped...
-

 144Scams
144ScamsPhishers turn to Dropbox links as fresh bait for victims
Convincing-looking emails where the victim is directed to click on a Dropbox link to download a supposedly unpaid invoice (and other classic...
-

 309Data Security
309Data SecurityHeartbleed now reforms into “Cupid” attack targeting Wi-Fi networks and Android
If you thought that Heartbleed is out of date now, and the whole cyber world is secure, then you have to change...
-

 210Cyber Crime
210Cyber CrimeGameOver Zeus and Cryptolocker: Law enforcement hits gang responsible
FBI names as "Most Wanted" the leader of cyber criminal gang based in Russia and Ukraine responsible for both GameOver Zeus and...
-
 214Surveillance
214SurveillanceScarface Writer Oliver Stone to Make Film on Snowden’s Whistleblowing
Oliver Stone is known for depicting famous [rather infamous] real life stories on screen. And the list of his highly successful real-life...
-

 116Cyber Crime
116Cyber Crime“Hacking” cars on the road wirelessly is easy, claims expert
It is perfectly possible to “hack” a car while it is driving on the road, seize control, and force the vehicle into...
-

 251News
251NewsExclusive: Linkin Park official Facebook Page Hacked! Spammed with adverts
In an exclusive report, we are updating that the official verified Facebook fan page of famous rock band Linkin Park (LP) with...
-
 212News
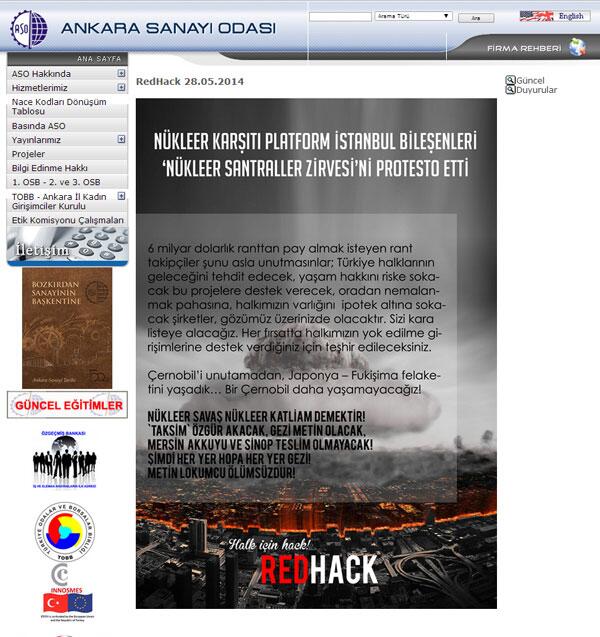
212NewsRedHack hacks Ankara Chamber of Industry website against Nuclear Summit
The famous Turkish Anonymous hacktivist group RedHack has hacked and defaced the official website of Ankara Chamber of Industry ASO, Turkey website (www.aso.org.tr). According...
-

 307Surveillance
307SurveillanceNSA is saving your facial web images, millions on daily basis: Snowden
The National Security Agency (NSA) collects millions of facial images transmitted through the Internet and uses them for various facial recognition programs,...
-

 300Android
300AndroidAndroid to power Space Station’s “Star Wars” floating robot
No one is too surprised to meet robots on the International Space Station - its Robonaut has posed for dozens of photos...
-

 402Cyber Crime
402Cyber CrimeWatch Dogs: How realistic is PS4 city‑hack thriller?
In Ubisoft's Watch Dogs, a man out for vengeance chooses an odd weapon - a smartphone. Loaded with deadly apps, he blows...
-

 431Scams
431ScamsiPhone and Apple ransom incidents? Don’t delay locking down your i‑stuff
Some users of Apple iPhones, iPads and Macs have been getting strange wake up calls and unsettling messages demanding a ransom for...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




