Featured News
-

 118Cyber Crime
118Cyber Crime“Hacking” cars on the road wirelessly is easy, claims expert
It is perfectly possible to “hack” a car while it is driving on the road, seize control, and force the vehicle into...
-

 252News
252NewsExclusive: Linkin Park official Facebook Page Hacked! Spammed with adverts
In an exclusive report, we are updating that the official verified Facebook fan page of famous rock band Linkin Park (LP) with...
-
 212News
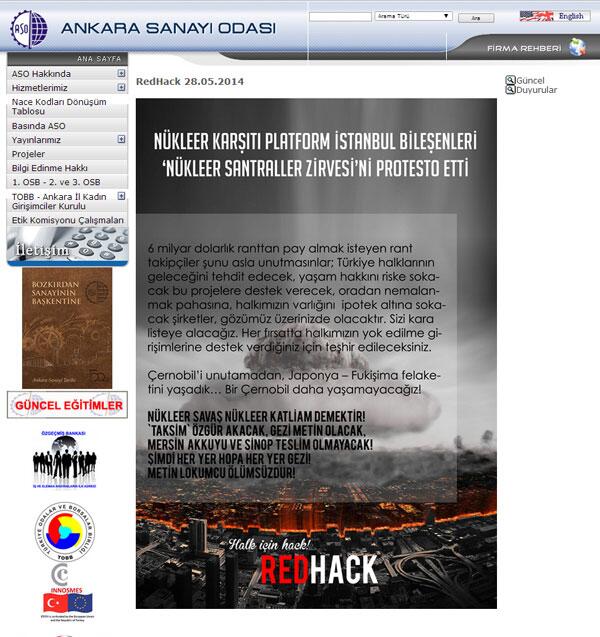
212NewsRedHack hacks Ankara Chamber of Industry website against Nuclear Summit
The famous Turkish Anonymous hacktivist group RedHack has hacked and defaced the official website of Ankara Chamber of Industry ASO, Turkey website (www.aso.org.tr). According...
-

 308Surveillance
308SurveillanceNSA is saving your facial web images, millions on daily basis: Snowden
The National Security Agency (NSA) collects millions of facial images transmitted through the Internet and uses them for various facial recognition programs,...
-

 300Android
300AndroidAndroid to power Space Station’s “Star Wars” floating robot
No one is too surprised to meet robots on the International Space Station - its Robonaut has posed for dozens of photos...
-

 402Cyber Crime
402Cyber CrimeWatch Dogs: How realistic is PS4 city‑hack thriller?
In Ubisoft's Watch Dogs, a man out for vengeance chooses an odd weapon - a smartphone. Loaded with deadly apps, he blows...
-

 432Scams
432ScamsiPhone and Apple ransom incidents? Don’t delay locking down your i‑stuff
Some users of Apple iPhones, iPads and Macs have been getting strange wake up calls and unsettling messages demanding a ransom for...
-
 373Password
373PasswordThousands of ex‑workers in IT “still have password” for old jobs
Ex-employees often still have full access to the network of their previous employer, leaving the company open to “revenge attacks” - or...
-

 75Cyber Crime
75Cyber CrimeSpotify breached – but just one mystery user is hacked
Music streaming service Spotify has urged its Android users to upgrade to a new version of the app after “unauthorized access to...
-

 380Malware
380MalwareWatch Dogs pirates hit by scurvy Bitcoin‑mining malware
Pirates who have downloaded one of the most popular torrent files of this week's big game release Watch Dogs - ironically, themed...
-

 265Android
265AndroidAndroid “eye spyware” takes photos without users knowing
Android users beware: a loophole in the mobile OS allows apps to take pictures without users knowing and upload them to the...
-

 167How To
167How ToRouter attacks: Five simple tips to lock criminals out
Cybercriminals always look for the weakest link when planning their attacks – and failings in home routers can allow another "way in"....
-

 104Password
104PasswordPassword inventor says his creation is now “a nightmare”
Fernando Corbato, the MIT computer scientist widely credited with inventing the computer password, says that he and his colleagues could not foresee...
-

 104Cyber Crime
104Cyber CrimeActivision Blizzard attacks hidden market in game “cheats”
Activision Blizzard - makers of game hits such as Call of Duty and World of Warcraft - have taken “aggressive” legal moves...
-

 242Cyber Crime
242Cyber CrimeeBay breach news: Posted data dump not valid, password reset issues
As the 145 million people affected by the security breach at online giant eBay get used to the idea that their personal...
-
 423Opinion
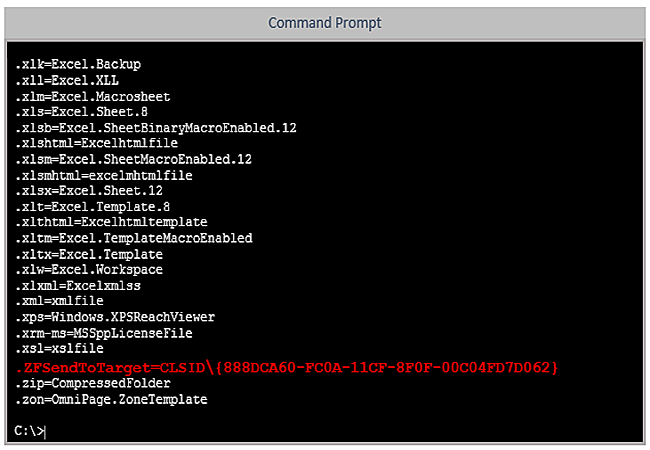
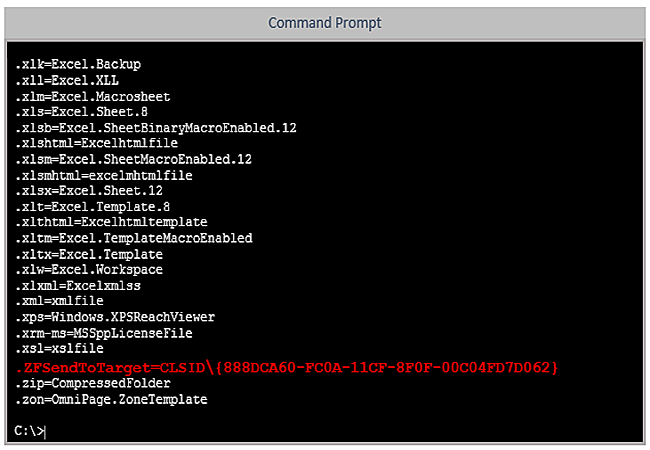
423OpinionSupport Scam Using (MS‑)DOS* Attack
The never-ending Windows support scam often misrepresents obsolete MS-DOS utilities. But three simple rules will bypass most of that social engineering.
-

 203How To
203How ToHow to retrieve your BitLocker Recovery key ?
if you are not using MBAM and don’t have access to your Active Directory and want to recover your BitLocker key for...
-

 215News
215NewseBay Hacked; 128 Million Users Asked to Change Passwords
eBay Inc. (Nasdaq: EBAY) has confirmed yesterday on its blog that it experienced one of the biggest criminal cyberattacks ever and has...
-

 183Cyber Crime
183Cyber CrimeNuclear aircraft carrier hacker pleads guilty
The leader of a gang who attacked 24 websites in search of personally identifiable information – from the unlikely confines of an...
-

 90Privacy
90PrivacyeBay customers urged to change their passwords after breach
eBay customers should change passwords following this latest high profile breach. The Internet giant says the hack exposed names, addresses, phone numbers,...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




