Featured News
-

 214News
214NewseBay Hacked; 128 Million Users Asked to Change Passwords
eBay Inc. (Nasdaq: EBAY) has confirmed yesterday on its blog that it experienced one of the biggest criminal cyberattacks ever and has...
-

 182Cyber Crime
182Cyber CrimeNuclear aircraft carrier hacker pleads guilty
The leader of a gang who attacked 24 websites in search of personally identifiable information – from the unlikely confines of an...
-

 89Privacy
89PrivacyeBay customers urged to change their passwords after breach
eBay customers should change passwords following this latest high profile breach. The Internet giant says the hack exposed names, addresses, phone numbers,...
-

 417Privacy
417PrivacyRubber “anti‑ID” mask foils spy‑cams by turning us all into clones
A Chicago artist has created a cheap, effective way for the public to fight back against the growing profusion of security cameras...
-
 116Cyber Crime
116Cyber CrimeBehind Blackshades: a closer look at the latest FBI cyber crime arrests
Blackshades is a RAT and the FBI has just arrested a lot of people involved in its use and distribution. But what's...
-

 398Password
398PasswordSamsung raises Apple an eyeball with ultra‑secure iris‑scan smartphones
High-end Samsung phones could soon ship with a biometric scanner which puts fingerprint-swipe buttons (as seen in both Samsung and Apple’s flagship...
-

 212Malware
212MalwareMiniduke still duking it out
At the end of April Microsoft announced that a vulnerability in Word was actively being exploited. New variants of MiniDuke display interesting...
-

 178News
178News‘NSA-Proof’ Email Service ‘ProtonMail’ by Harvard and MIT Students becomes massive success
Necessity is the mother of invention, the old adage has proved its worth again when a group of Harvard and MIT students...
-

 124Scams
124ScamsTechnology giants join forces to battle tech support phone scams
Google, Facebook, Twitter and AOL have joined forces to stamp out fake tech support services where customers are fooled into calling bogus...
-
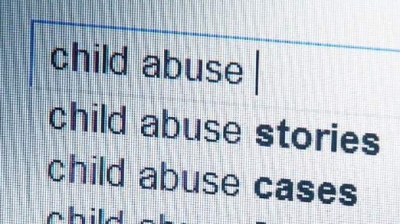
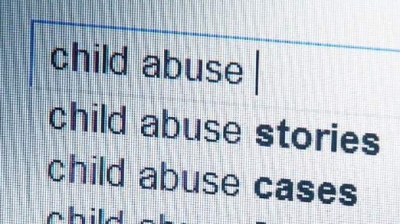 200News
200NewsDelete our filthy searches: Paedophiles and politicians ask Google to remove their search results
Google is back in the news for all the wrong reasons! According to reports from BBC, a European Court of Justice ruled...
-

 77Cyber Crime
77Cyber CrimeThink cybercriminals are “evil geniuses”? Wrong – and these idiots show why
Many cybercriminals are not exactly Bond villain material - in fact, some are criminals with a level of weapons-grade stupidity that Bond...
-

 87Malware
87MalwareMalicious advertising is growing threat, warns Senate report
Technology giants with large ad networks need to do more to protect consumers from hackers infiltrating their advertising networks to deliver malicious...
-

 106How To
106How ToXbox Kinect Hack Allows For Virtual Reality
It’s one thing to bring your mind into virtual reality. Get some snazzy VR goggles in front of your eyes, bump the...
-

 77Cyber Crime
77Cyber CrimeFBI plans worldwide crackdown on cybercrime
The FBI is gearing up for a major crackdown on cybercrime, and says that arrests of major criminals will follow in weeks....
-

 85Privacy
85PrivacyFormer Royal reporter: “I hacked Kate Middleton’s phone 155 times”
So-called phone hacking makes the headlines again, as new revelations are made. Have you properly secured your mobile phone voicemail?
-
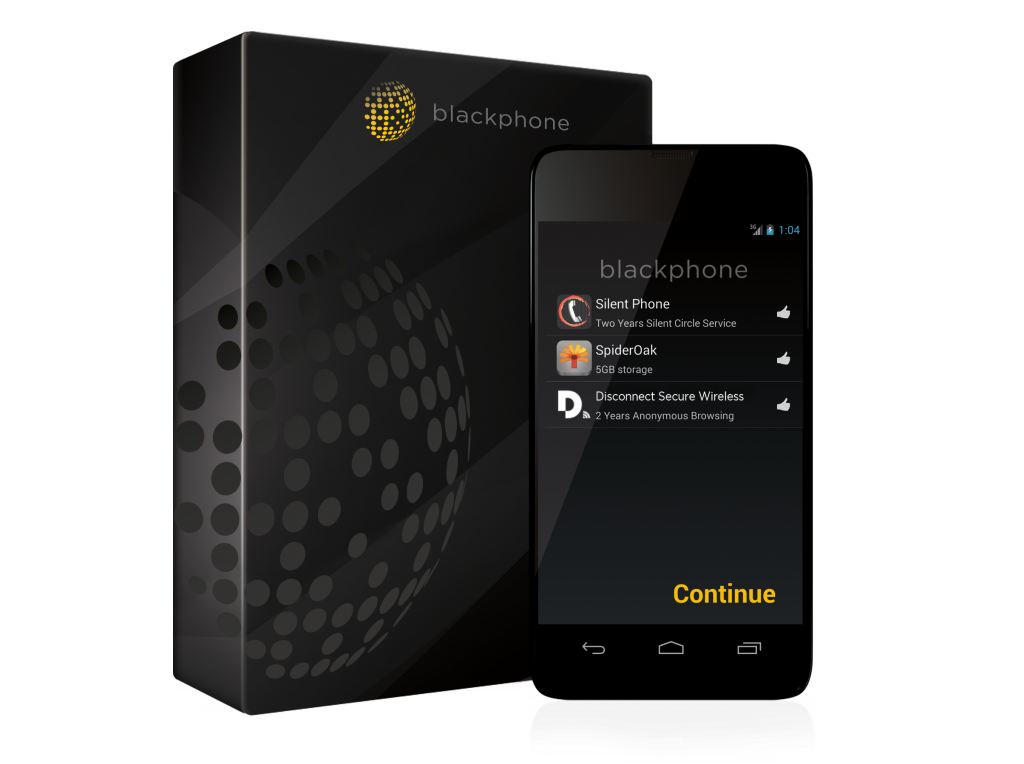
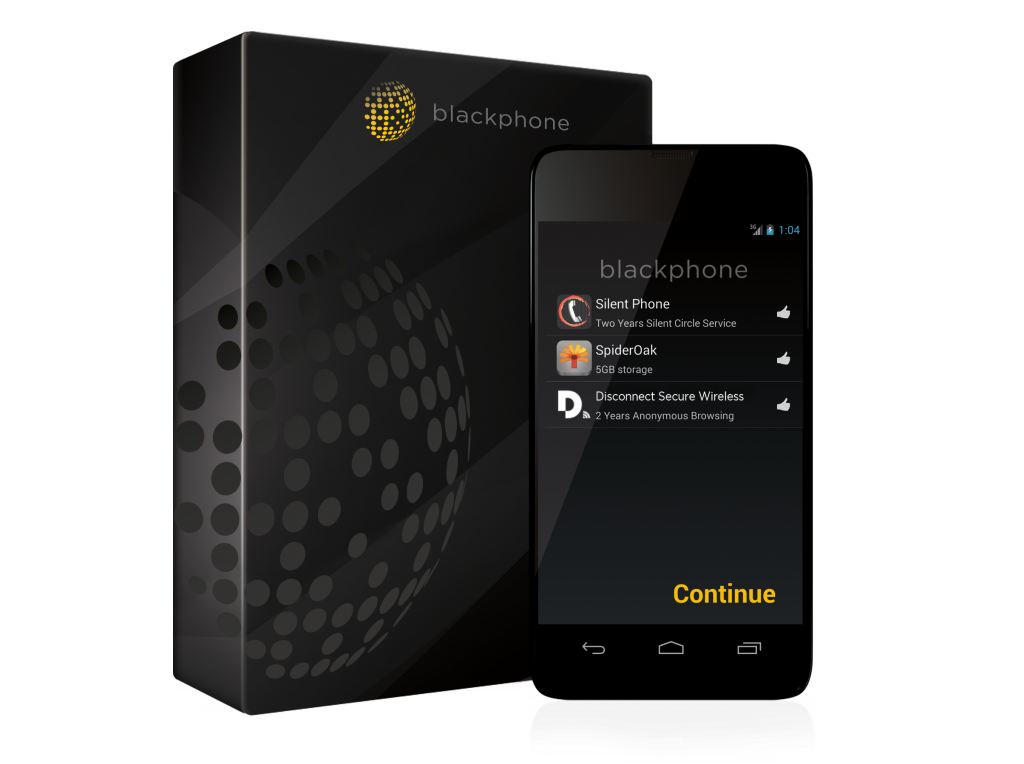 178Privacy
178PrivacyInterview: Phil Zimmermann – why Fortune 100 companies are buying Blackphone
Phil Zimmermann invented the most widely used system of email encryption in the world - and says that Fortune 100 companies are...
-
 74Cyber Crime
74Cyber CrimeDogecoin vault vanishes after attack – and “mysterious withdrawals”
The popular online wallet site Dogevault is offline after attackers destroyed data on the site. The impact on user funds is unknown...
-

 211How To
211How ToHack Androids lock screen with an Arduino
You can also find the code for this project below: /* Brute forcing Android 4 Digit PIN's To run the whole range...
-

 158Privacy
158PrivacySnapchat “lied to users” about privacy of vanishing photos
The photo-sharing app Snapchat, popular with youngsters for its photos which would exist briefly then “disappear forever” has admitted that the photos...
-
 86Malware
86MalwareRansomware on Android: Keep calm but get protected
There has been a lot of talk in the news lately of a new ransomware for Android. While this does sound dire,...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




