Featured News
-
 375Password
375PasswordThousands of ex‑workers in IT “still have password” for old jobs
Ex-employees often still have full access to the network of their previous employer, leaving the company open to “revenge attacks” - or...
-

 77Cyber Crime
77Cyber CrimeSpotify breached – but just one mystery user is hacked
Music streaming service Spotify has urged its Android users to upgrade to a new version of the app after “unauthorized access to...
-

 385Malware
385MalwareWatch Dogs pirates hit by scurvy Bitcoin‑mining malware
Pirates who have downloaded one of the most popular torrent files of this week's big game release Watch Dogs - ironically, themed...
-

 270Android
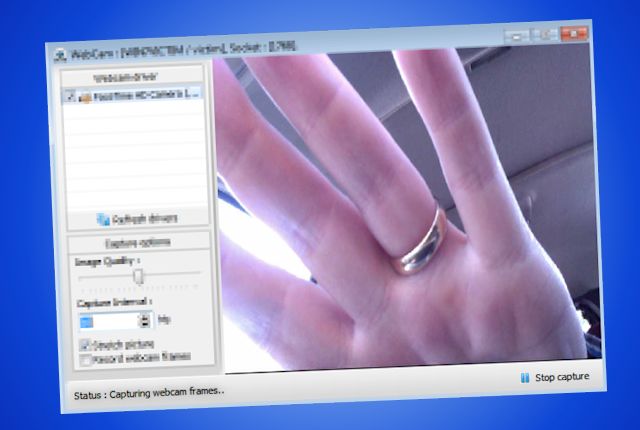
270AndroidAndroid “eye spyware” takes photos without users knowing
Android users beware: a loophole in the mobile OS allows apps to take pictures without users knowing and upload them to the...
-

 172How To
172How ToRouter attacks: Five simple tips to lock criminals out
Cybercriminals always look for the weakest link when planning their attacks – and failings in home routers can allow another "way in"....
-

 107Password
107PasswordPassword inventor says his creation is now “a nightmare”
Fernando Corbato, the MIT computer scientist widely credited with inventing the computer password, says that he and his colleagues could not foresee...
-

 116Cyber Crime
116Cyber CrimeActivision Blizzard attacks hidden market in game “cheats”
Activision Blizzard - makers of game hits such as Call of Duty and World of Warcraft - have taken “aggressive” legal moves...
-

 246Cyber Crime
246Cyber CrimeeBay breach news: Posted data dump not valid, password reset issues
As the 145 million people affected by the security breach at online giant eBay get used to the idea that their personal...
-
 427Opinion
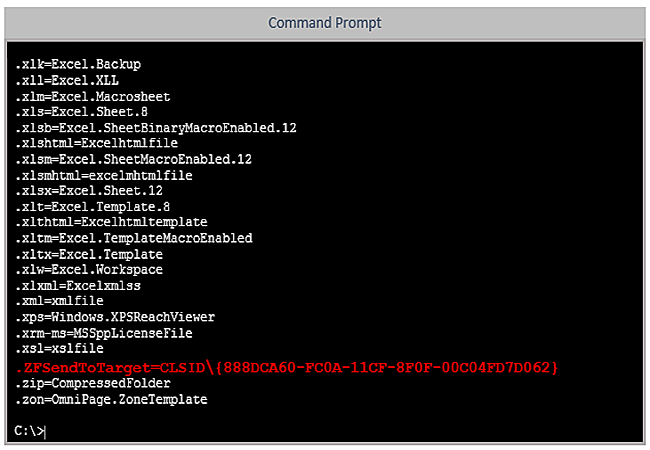
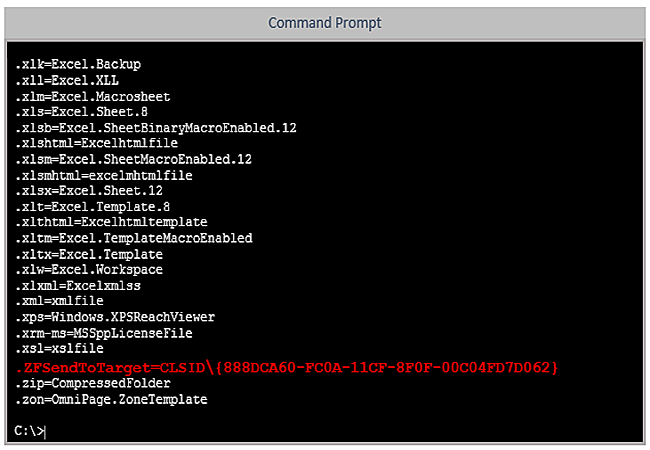
427OpinionSupport Scam Using (MS‑)DOS* Attack
The never-ending Windows support scam often misrepresents obsolete MS-DOS utilities. But three simple rules will bypass most of that social engineering.
-

 207How To
207How ToHow to retrieve your BitLocker Recovery key ?
if you are not using MBAM and don’t have access to your Active Directory and want to recover your BitLocker key for...
-

 220News
220NewseBay Hacked; 128 Million Users Asked to Change Passwords
eBay Inc. (Nasdaq: EBAY) has confirmed yesterday on its blog that it experienced one of the biggest criminal cyberattacks ever and has...
-

 187Cyber Crime
187Cyber CrimeNuclear aircraft carrier hacker pleads guilty
The leader of a gang who attacked 24 websites in search of personally identifiable information – from the unlikely confines of an...
-

 91Privacy
91PrivacyeBay customers urged to change their passwords after breach
eBay customers should change passwords following this latest high profile breach. The Internet giant says the hack exposed names, addresses, phone numbers,...
-

 422Privacy
422PrivacyRubber “anti‑ID” mask foils spy‑cams by turning us all into clones
A Chicago artist has created a cheap, effective way for the public to fight back against the growing profusion of security cameras...
-
 122Cyber Crime
122Cyber CrimeBehind Blackshades: a closer look at the latest FBI cyber crime arrests
Blackshades is a RAT and the FBI has just arrested a lot of people involved in its use and distribution. But what's...
-

 403Password
403PasswordSamsung raises Apple an eyeball with ultra‑secure iris‑scan smartphones
High-end Samsung phones could soon ship with a biometric scanner which puts fingerprint-swipe buttons (as seen in both Samsung and Apple’s flagship...
-

 219Malware
219MalwareMiniduke still duking it out
At the end of April Microsoft announced that a vulnerability in Word was actively being exploited. New variants of MiniDuke display interesting...
-

 181News
181News‘NSA-Proof’ Email Service ‘ProtonMail’ by Harvard and MIT Students becomes massive success
Necessity is the mother of invention, the old adage has proved its worth again when a group of Harvard and MIT students...
-

 128Scams
128ScamsTechnology giants join forces to battle tech support phone scams
Google, Facebook, Twitter and AOL have joined forces to stamp out fake tech support services where customers are fooled into calling bogus...
-
 204News
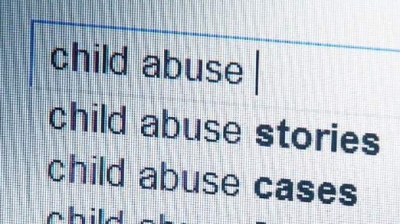
204NewsDelete our filthy searches: Paedophiles and politicians ask Google to remove their search results
Google is back in the news for all the wrong reasons! According to reports from BBC, a European Court of Justice ruled...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




