Featured News
-

 101Kids Online
101Kids OnlineHow do you know if your child’s ID has been stolen?
When it comes to identity theft, the most successful attack is on the person least likely to be aware of activity being...
-

 128Privacy
128PrivacyCybercrime evolves as criminal gangs join forces with spies – report
Hackers targeting sensitive information or stealing from retailers work at such speed that customers often notice data breaches first - and for...
-
 106Malware
106MalwareFake Facebook app attack can lead to your Android being spied upon, and your bank account being hacked
Hackers are using a notorious banking Trojan horse to display a bogus message from Facebook, in an aggressive attempt to infect Android...
-
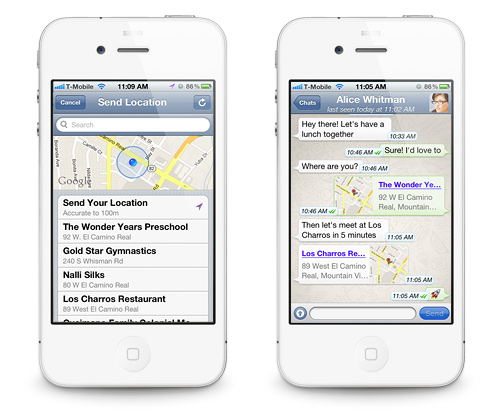
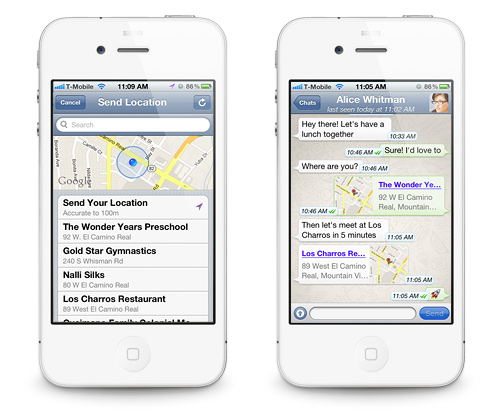 179Data Security
179Data SecurityWhatsApp Flaw leaves User Location Vulnerable to Hackers and Spies.
Researchers warn that the highly popular mobile application WhatsApp cannot be trusted blindly. WhatsApp has been one of the most popular mobile...
-

 150Surveillance
150SurveillanceNo Room for Privacy: Facebook Launches Friend-Spying Feature ‘Nearby Friends’
A new feature introduced by Facebook to allow meeting the Facebook friends in real time when they are actually close by has...
-

 246News
246NewsOfficial website of Bangalore City Police hacked by Pakistani hacker
A Pakistani hacker going with the handle of H4x0r10ux m1nd has hacked and defaced the official website of Bangalore City Police India, yesterday....
-

 229How To
229How ToHow to run Kali on your Android device
This tutorial mainly created for Linux fans. Follow the given steps below to install Kali Linux on your Android phone. Step 1:...
-

 74Cyber Crime
74Cyber CrimeHacking predictions gone wild from the ‘internet of things’
A new, terrifying weapon is in the hands of hackers - the ability to stop a toilet flush working. We look at...
-

 96Password
96PasswordGoogle Chromebook passwords could soon just be the wave of an Android
Google’s popular Chromebook laptops could soon do away with passwords entirely with a new system where simply bringing a phone near the...
-

 194Cyber Crime
194Cyber CrimeCanadian teenager is first to be arrrested for Heartbleed bug attack
A 19-year-old teenager in London, Ontario, Canada has become the first criminal to be arrested for exploiting the ‘Heartbleed’ bug to steal...
-

 85Cyber Crime
85Cyber CrimeLaCie breach leaks passwords and emails – for a whole YEAR
Hard drive specialist LaCie has admitted a data breach that exposed customer emails and passwords - and the attack went undetected for...
-

 328Surveillance
328SurveillanceGoogle admits it’s reading your emails, tells court Gmail users should not expect privacy
Google’s latest update on Monday only highlights how apathetic they are to the privacy of their users and consider every bit of...
-

 84Cyber Crime
84Cyber CrimeSamsung Galaxy S5 is vulnerable to crude “fake fingerprint” hack
A crude fake fingerprint molded using wood glue, and based on a photo taken by a smartphone was enough to fool the...
-

 204Malware
204Malware‘Heartbleed thingumajig’ man suffers heartbleed hackers revenge
Man challenges hackers to break into accounts after complaining Heartbleed was “overhyped” – and has online life destroyed in minutes.
-

 90Malware
90MalwareFacebook Webinject Leads to iBanking Mobile Bot
iBanking is a malicious Android application that when installed on a mobile phone is able to spy on its user’s communications. This...
-

 416Opinion
416OpinionXP‑diency: beyond the end of the line
Can't yet upgrade from XP? Recommendations are being made by Gartner and others for staying (relatively) safe.
-

 174Cyber Crime
174Cyber CrimeHeartbleed claims British mums and Canadian tax payers as victims
The critical security vulnerability in OpenSSL known commonly as “Heartbleed” continues to raise alarms, with websites now warning that hackers have breached...
-
 126How To
126How ToTaxing Times: Dealing with tax identity fraud in America
Filing your taxes on April 15? What if someone has already filed “your” income tax return? Sadly, this can happen, and it...
-
 183Cyber Crime
183Cyber CrimeHeartbleed bug: worse than feared and could affect “billions”
The full scope of the Heartbleed bug came to light in a series of reports by researchers and white-hat hackers, with some...
-

 175Malware
175MalwareInterview: Windigo victim speaks out on the ‘stealth’ malware that attacked his global company
Francois Gagnon is a Canadian business owner who was targeted because his company had lots of servers, and many customers - victims...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




