Featured News
-

 76Cyber Crime
76Cyber CrimeHacking predictions gone wild from the ‘internet of things’
A new, terrifying weapon is in the hands of hackers - the ability to stop a toilet flush working. We look at...
-

 99Password
99PasswordGoogle Chromebook passwords could soon just be the wave of an Android
Google’s popular Chromebook laptops could soon do away with passwords entirely with a new system where simply bringing a phone near the...
-

 197Cyber Crime
197Cyber CrimeCanadian teenager is first to be arrrested for Heartbleed bug attack
A 19-year-old teenager in London, Ontario, Canada has become the first criminal to be arrested for exploiting the ‘Heartbleed’ bug to steal...
-

 89Cyber Crime
89Cyber CrimeLaCie breach leaks passwords and emails – for a whole YEAR
Hard drive specialist LaCie has admitted a data breach that exposed customer emails and passwords - and the attack went undetected for...
-

 331Surveillance
331SurveillanceGoogle admits it’s reading your emails, tells court Gmail users should not expect privacy
Google’s latest update on Monday only highlights how apathetic they are to the privacy of their users and consider every bit of...
-

 87Cyber Crime
87Cyber CrimeSamsung Galaxy S5 is vulnerable to crude “fake fingerprint” hack
A crude fake fingerprint molded using wood glue, and based on a photo taken by a smartphone was enough to fool the...
-

 207Malware
207Malware‘Heartbleed thingumajig’ man suffers heartbleed hackers revenge
Man challenges hackers to break into accounts after complaining Heartbleed was “overhyped” – and has online life destroyed in minutes.
-

 91Malware
91MalwareFacebook Webinject Leads to iBanking Mobile Bot
iBanking is a malicious Android application that when installed on a mobile phone is able to spy on its user’s communications. This...
-

 419Opinion
419OpinionXP‑diency: beyond the end of the line
Can't yet upgrade from XP? Recommendations are being made by Gartner and others for staying (relatively) safe.
-

 177Cyber Crime
177Cyber CrimeHeartbleed claims British mums and Canadian tax payers as victims
The critical security vulnerability in OpenSSL known commonly as “Heartbleed” continues to raise alarms, with websites now warning that hackers have breached...
-
 129How To
129How ToTaxing Times: Dealing with tax identity fraud in America
Filing your taxes on April 15? What if someone has already filed “your” income tax return? Sadly, this can happen, and it...
-
 186Cyber Crime
186Cyber CrimeHeartbleed bug: worse than feared and could affect “billions”
The full scope of the Heartbleed bug came to light in a series of reports by researchers and white-hat hackers, with some...
-

 178Malware
178MalwareInterview: Windigo victim speaks out on the ‘stealth’ malware that attacked his global company
Francois Gagnon is a Canadian business owner who was targeted because his company had lots of servers, and many customers - victims...
-
 274Geek
274GeekThe Major Cyber Events You Might Have Missed
The most happening events in cyber world that makes every web savvy thrilled and compel to think ahead of cyber crime are...
-

 287Privacy
287Privacy“I am responsible”: Heartbleed developer breaks silence
The source of the bug, which has affected at least 500,000 sites and millions of users, was a small programming error made...
-

 482Privacy
482PrivacyPrivacy, Social Media, and the Younger Generation
When parents post photographs and information about their children to social media, what are the privacy implications for those children when they're...
-

 255Android
255AndroidAndroid malware? Google will be watching your every move
Google is to boost security on its Android devices, by continuously checking apps to see that they haven’t mutated into malicious Android...
-

 128Malware
128MalwareWindigo not Windigone: Linux/Ebury updated
There have been some interesting new developments since we published our report on Operation Windigo. In this blog post you will read...
-
 325Data Security
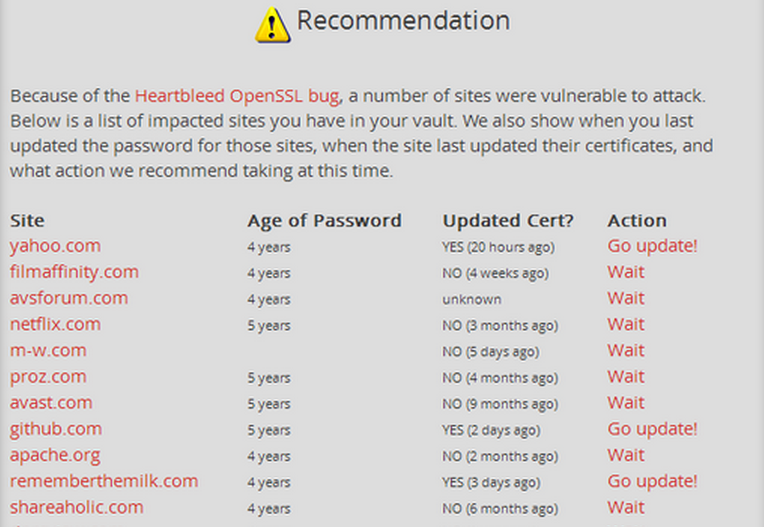
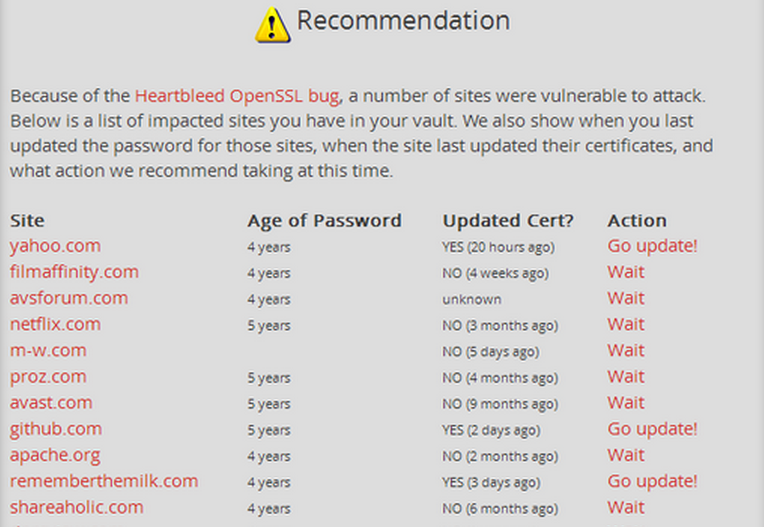
325Data SecurityUse LastPass checker to find sites vulnerable to ‘Heartbleed’ and if you’ve to change your password
The password manager, LastPass, allows you to check if the saved sites are affected by the bug through its ‘LastPass Heratbleed Checker. LastPass’s Security...
-

 201Data Security
201Data SecurityYour email Password, Credit Card at Risk—Web Encryption Compromised by ‘Heart Bleed’ Bug
The new bug allows attackers to gain sensitive information protected by the SSL/TLS encryption. A new exploit in the open SSL, the...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




