Featured News
-

 193News
193NewsHacking of US Navy Computers by Iranian Hackers will Test new NSA Commander Rogers
In 2012, we reported that US NAVY faces 110,000 cyber attacks every hour. Now a report has gone viral that Iran’s penetration into...
-

 315News
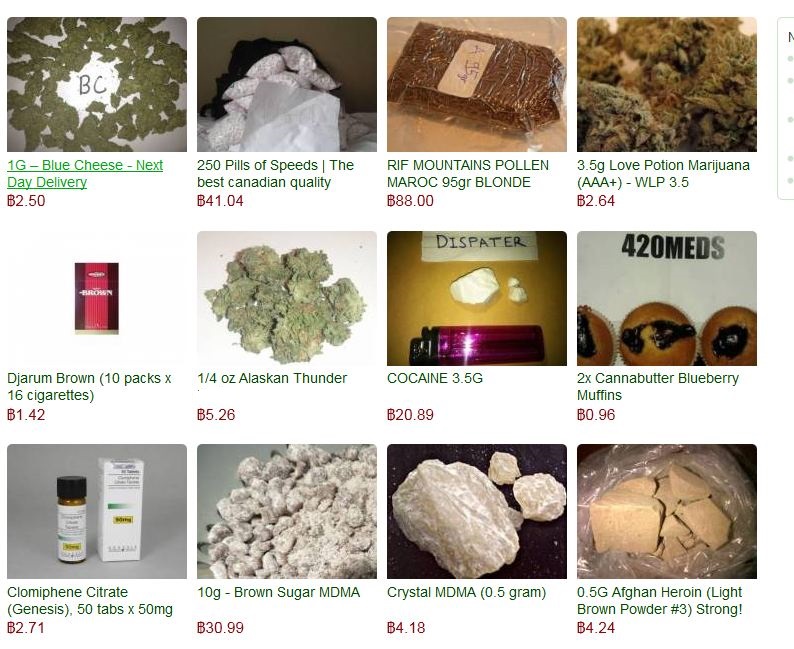
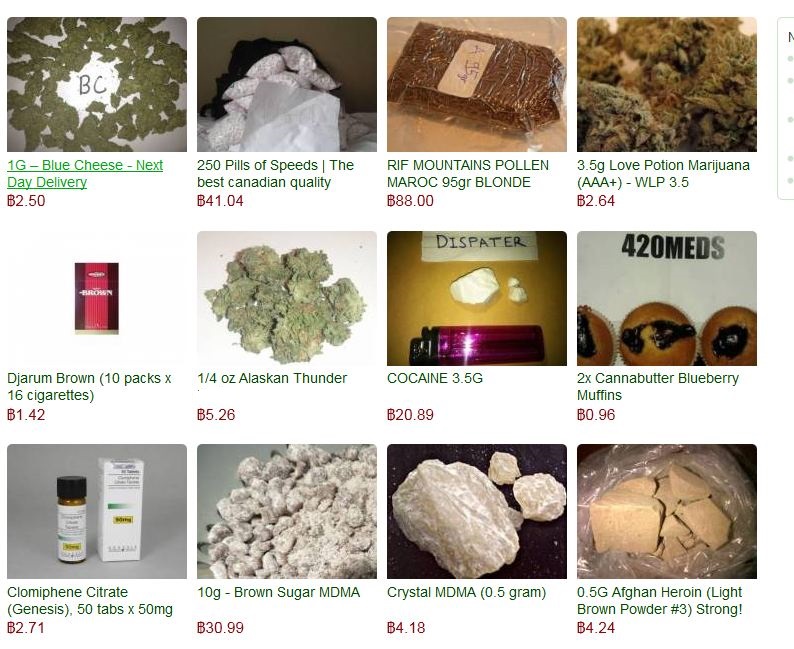
315NewsSilk Road 2.0 Hacked: $2.5 million in Bitcoins Stolen! Administrator makes an emotional appeal
An emotional appeal posted on the dark market’s official forum clearly stated that “We have been hacked” and nearly $2.4 to $2.7...
-
 451Password
451PasswordGoogle buys firm with password‑busting “silent sound” authentication system
Google has bought a company offering a new form of two-factor authentication - using “silent” sounds played via PC and smartphone speakers...
-
 272Scams
272ScamsTax Scams, Malware, Phishing and a 419
A roundup of scam information, including a tax scams article, email with a link to malware, a phish, and the worlds laziest...
-

 291Mac
291MacNew to Mac? Four security tips you need to know
Mac OS X is a slick, easy-to-use operating system with an impressive record on security – and basic malware detection built in...
-
 95Malware
95MalwareMysterious ‘Moon’ worm spreads into many Linksys routers – and hunts new victims
Malware dubbed ‘Moon’ due to images found within the malware has spread rapidly through many models of Linksys routers - even ones...
-

 84Password
84PasswordThe password is ‘burger joint’; places could be key to secure passwords
Could places, not phrases, be the basis of secure passwords. UAE researchers have created a system for creating complex passwords using facts...
-

 83Password
83PasswordKickstarter hacked. Users told to change passwords
Security expert Graham Cluley takes a look at the Kickstarter hack, and discovers there's more to think about than just changing your...
-
 215Cyber Events
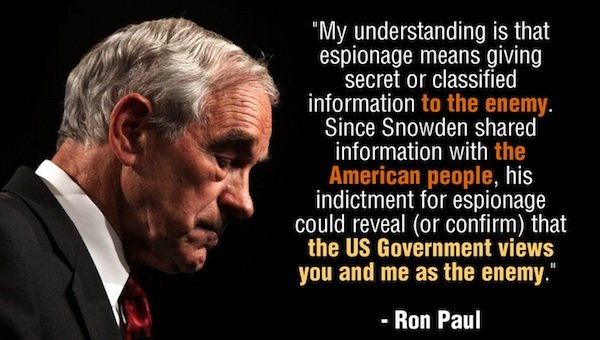
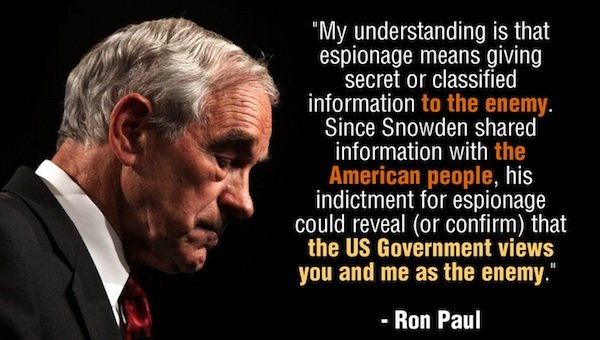
215Cyber EventsRon Paul Launches Clemency Petition for Snowden!
Ron Paul, a former Texas congressman, has launched a petition seeking clemency for Edward Snowden, the whistleblower who leaked data about the NSA surveillance...
-
 181Geek
181GeekEgyptian hacker removes Mark Zuckerberg’s Facebook Timeline Photo
An Egyptian hacker removed Mark Zuckerberg’s Facebook timeline cover photo from his account using a private exploit, according to a latest hacker...
-

 230Cyber Events
230Cyber EventsBrazil is spying on social media accounts of protesters, hoping to protect World Cup
According to the officials, the security forces of Brazil are constantly using secret agents and thoroughly supervising the social media in order...
-

 216News
216NewsLulzSec Peru hacks Twitter account of Venezuela’s Ruling Party against Twitter Cencorship
World renowned hacktivists from LulzSec Peru have hacked a verified Twitter account of United Socialist Party of Venezuela (PSUV). After taking over the Twitter account, the hacktivists...
-

 283News
283NewsRedHack Leaks Contact Details of US Embassy staff in Turkey
Turkish based RedHack hacktivist claims to leak personal information and contact details of US embassy’ staff in Turkey. The dumped data shows...
-

 282News
282NewsSyrian Electronic Army hacks Forbes Website and Twitter account for spreading hate against Syria
The hardcore supporters of Syrian President Bashar-Al-Assad from Syrian Electronic Army have hacked the American business magazine Forbes. As a result of hack, a...
-
 77Cyber Crime
77Cyber CrimeSilk Road 2.0 drug market hit, millions stolen from bitcoin reserve
A large scale cyber-theft has drained the relaunched ‘online drug bazaar’ Silk Road 2.0 of nearly all of its Bitcoin reserves -...
-
 294News
294NewsAnonymous Ukraine Claims to hack and leak secret email conversations of Vitali Klitschko’s UDAR party
Activists in Ukraine are fighting a battle on ground, while hacktavists are putting their share online. The Anonymous Ukraine, in an email...
-

 383Password
383PasswordTwo‑thirds of couples ‘share passwords to online accounts’, Pew research finds
Couples who have been in a long-term relationship indulge in risky online behaviour, such as sharing passwords for online accounts, with two-thirds...
-
 182Cyber Crime
182Cyber CrimeThe 400Gbps largest DDoS attack has hit Europe using NTP Amplification
For temporary abandoning the services of the host that is connected to some internet, the most widely used and favorite method that...
-
 92Cyber Crime
92Cyber CrimeKaspersky Uncovers sophisticated Spying operation ‘The Mask’ targeted diplomats, govts for 7 years
Kaspersky Lab, the Moscow-based computer security software firm, has unearthed a cyber-spying campaign apparently started by a Spanish-speaking country. The campaign targeted...
-

 104Malware
104MalwareCritical IE and other flaws discovered. Patch your systems now, says Microsoft
If your system administrator looks a little frazzled this week, be nice to him or her and don't grumble too much about...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




