Featured News
-

 231Cyber Events
231Cyber EventsBrazil is spying on social media accounts of protesters, hoping to protect World Cup
According to the officials, the security forces of Brazil are constantly using secret agents and thoroughly supervising the social media in order...
-

 219News
219NewsLulzSec Peru hacks Twitter account of Venezuela’s Ruling Party against Twitter Cencorship
World renowned hacktivists from LulzSec Peru have hacked a verified Twitter account of United Socialist Party of Venezuela (PSUV). After taking over the Twitter account, the hacktivists...
-

 285News
285NewsRedHack Leaks Contact Details of US Embassy staff in Turkey
Turkish based RedHack hacktivist claims to leak personal information and contact details of US embassy’ staff in Turkey. The dumped data shows...
-

 282News
282NewsSyrian Electronic Army hacks Forbes Website and Twitter account for spreading hate against Syria
The hardcore supporters of Syrian President Bashar-Al-Assad from Syrian Electronic Army have hacked the American business magazine Forbes. As a result of hack, a...
-
 77Cyber Crime
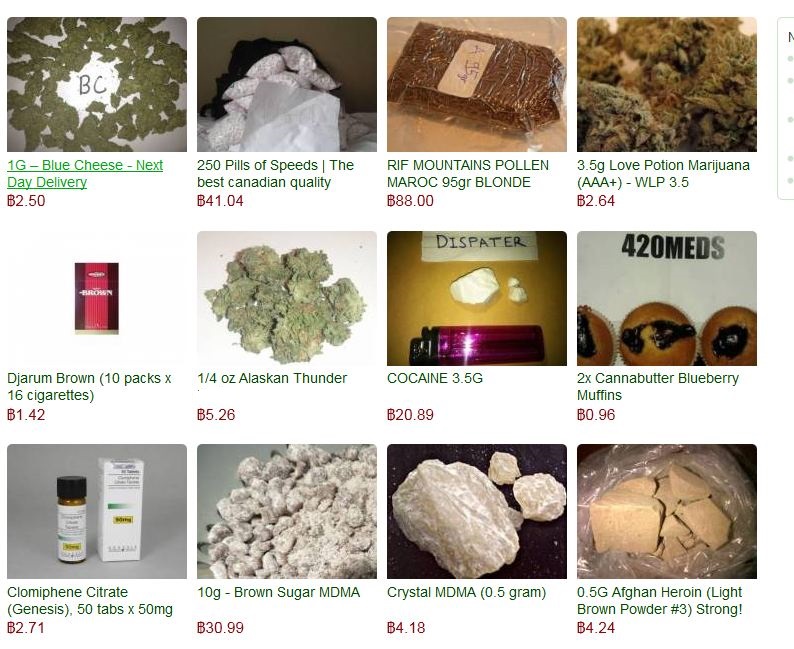
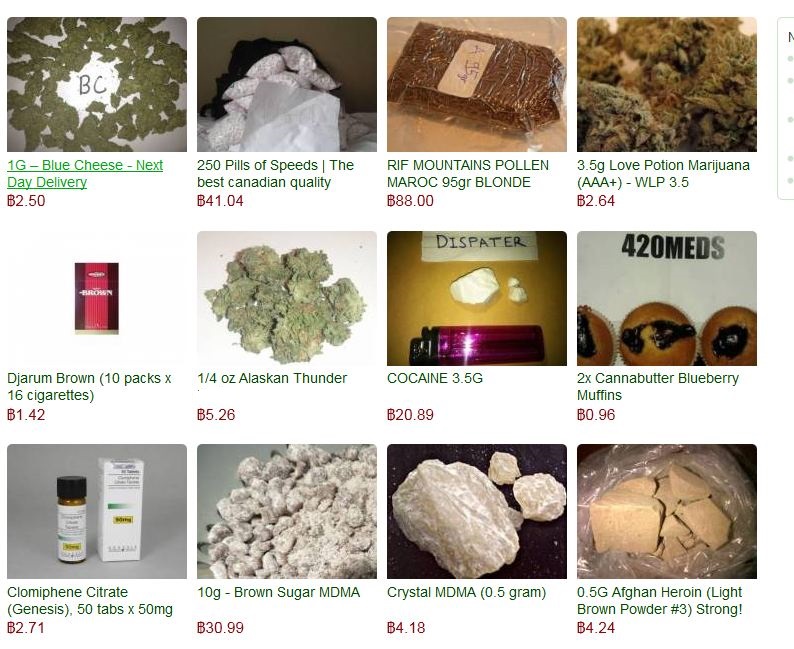
77Cyber CrimeSilk Road 2.0 drug market hit, millions stolen from bitcoin reserve
A large scale cyber-theft has drained the relaunched ‘online drug bazaar’ Silk Road 2.0 of nearly all of its Bitcoin reserves -...
-
 296News
296NewsAnonymous Ukraine Claims to hack and leak secret email conversations of Vitali Klitschko’s UDAR party
Activists in Ukraine are fighting a battle on ground, while hacktavists are putting their share online. The Anonymous Ukraine, in an email...
-

 384Password
384PasswordTwo‑thirds of couples ‘share passwords to online accounts’, Pew research finds
Couples who have been in a long-term relationship indulge in risky online behaviour, such as sharing passwords for online accounts, with two-thirds...
-
 183Cyber Crime
183Cyber CrimeThe 400Gbps largest DDoS attack has hit Europe using NTP Amplification
For temporary abandoning the services of the host that is connected to some internet, the most widely used and favorite method that...
-
 93Cyber Crime
93Cyber CrimeKaspersky Uncovers sophisticated Spying operation ‘The Mask’ targeted diplomats, govts for 7 years
Kaspersky Lab, the Moscow-based computer security software firm, has unearthed a cyber-spying campaign apparently started by a Spanish-speaking country. The campaign targeted...
-

 105Malware
105MalwareCritical IE and other flaws discovered. Patch your systems now, says Microsoft
If your system administrator looks a little frazzled this week, be nice to him or her and don't grumble too much about...
-

 99Cyber Crime
99Cyber CrimePersonal email and cloud storage pose ‘biggest threat’ to corporate data, report claims
Nearly two-thirds of employees - 63% - use personal email to transfer work files, potentially leaving workplaces exposed to hacks against their...
-

 81Cyber Crime
81Cyber CrimeWorldwide cost of identity theft could be $5 billion per year, Microsoft survey finds
A Microsoft survey of 10,000 consumers found that the worldwide annual cost of identity theft and phishing could be as high as...
-

 370Cyber Crime
370Cyber CrimeHalf of children left exposed to online threats as parents fail to use built‑in controls
Less than half of parents use parental controls on internet-enabled devices bought for their children - leaving millions of youngsters potentially exposed...
-

 345Windows
345WindowsWindows exploitation in 2013
The year 2013 was notable for the appearance of 0-day vulnerabilities that were primarily used in targeted attacks. In this case, criminal...
-
 211Cyber Events
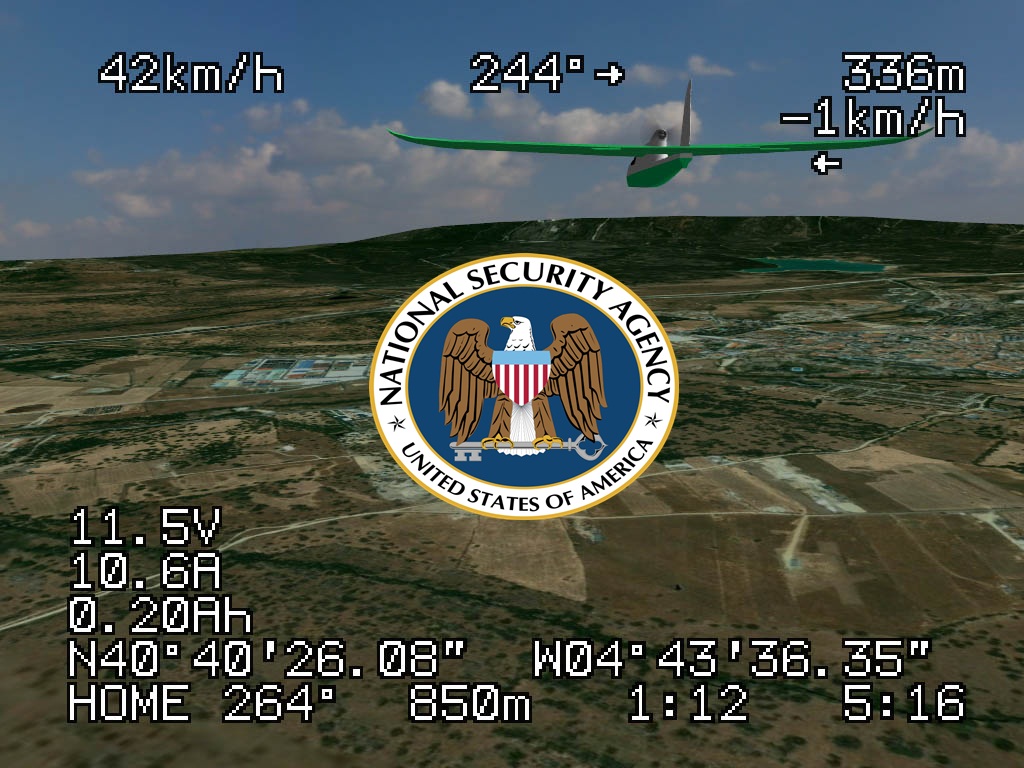
211Cyber EventsAnonymous Whistleblower reveals U.S. uses unreliable NSA cell phone location data to drone civilians.
USA identifies its drone targets based on NSA metadata, a flawed tactic, according to reports published in the Intercept. A former NSA...
-

 388Malware
388MalwareCorkow – the lesser‑known Bitcoin‑curious cousin of the Russian banking Trojan family
A little-known banking trojan, developed in Russia, has managed to infect thousands of victims' computers without the knowledge of their owners. Graham...
-

 562How To
562How ToTwo‑factor authentication: What is it – and why do I need it?
Over the past two years, many online services have started to offer ‘two-factor authentication’ - an extra security measure which often requires...
-

 465Password
465PasswordMicrosoft boosts security for Office 365 users with two‑factor logins
Microsoft’s online Office 365 service has added a new layer of protection to users of the online document-editing service, with two-factor authentication...
-

 205Data Security
205Data SecurityVulnerability that lets hackers hack Snapchat and disable your iPhone
Snapchat app vulnerability is highlighted again, and this time the hackers can temporarily freeze your iPhone and force restart, according to media...
-
 77Cyber Crime
77Cyber CrimePhishy business: Surge in tax scams as emails rise by nearly 50% in one year
Fraudulent emails offering refunds of overpaid tax have surged by nearly 50% in the past year, according to a report by Accountancy...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




