Featured News
-

 371Cyber Crime
371Cyber CrimeHalf of children left exposed to online threats as parents fail to use built‑in controls
Less than half of parents use parental controls on internet-enabled devices bought for their children - leaving millions of youngsters potentially exposed...
-

 346Windows
346WindowsWindows exploitation in 2013
The year 2013 was notable for the appearance of 0-day vulnerabilities that were primarily used in targeted attacks. In this case, criminal...
-
 211Cyber Events
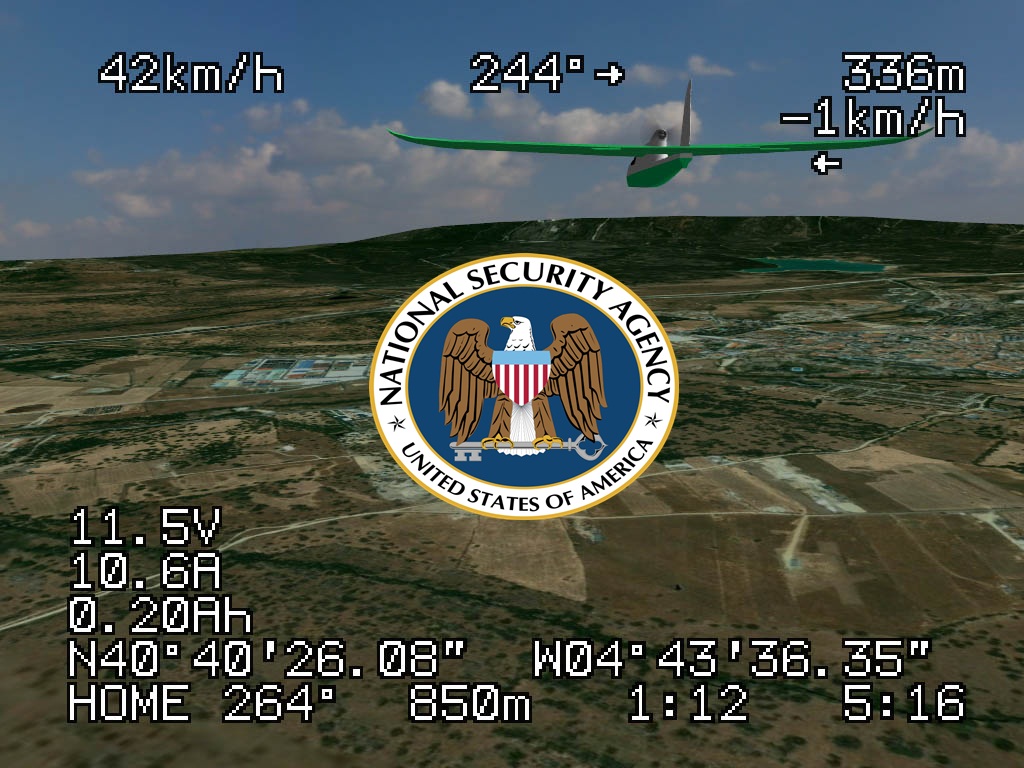
211Cyber EventsAnonymous Whistleblower reveals U.S. uses unreliable NSA cell phone location data to drone civilians.
USA identifies its drone targets based on NSA metadata, a flawed tactic, according to reports published in the Intercept. A former NSA...
-

 389Malware
389MalwareCorkow – the lesser‑known Bitcoin‑curious cousin of the Russian banking Trojan family
A little-known banking trojan, developed in Russia, has managed to infect thousands of victims' computers without the knowledge of their owners. Graham...
-

 563How To
563How ToTwo‑factor authentication: What is it – and why do I need it?
Over the past two years, many online services have started to offer ‘two-factor authentication’ - an extra security measure which often requires...
-

 466Password
466PasswordMicrosoft boosts security for Office 365 users with two‑factor logins
Microsoft’s online Office 365 service has added a new layer of protection to users of the online document-editing service, with two-factor authentication...
-

 205Data Security
205Data SecurityVulnerability that lets hackers hack Snapchat and disable your iPhone
Snapchat app vulnerability is highlighted again, and this time the hackers can temporarily freeze your iPhone and force restart, according to media...
-
 78Cyber Crime
78Cyber CrimePhishy business: Surge in tax scams as emails rise by nearly 50% in one year
Fraudulent emails offering refunds of overpaid tax have surged by nearly 50% in the past year, according to a report by Accountancy...
-

 184News
184NewsAnother target for Hackers: A small device that can hack a car! (Video Added)
This small sized device could hack a car, let’s see how the researchers demonstrate. Auto makers over the years have paid less...
-

 207Cyber Crime
207Cyber CrimeAmerican law firm admits entire server of legal files fell victim to Cryptolocker
A small American law firm has admitted that every document on a server at the North Carolina company has fallen prey to...
-

 83Cyber Crime
83Cyber CrimeFacebook’s ‘A Look Back’ video used as bait for malware, report claims
A fake version of Facebook’s 10th anniversary celebration video page, ‘A Look Back’ is spreading via the social network, with users directed...
-

 108Scams
108ScamsWangiri Telephone Fraud – One Ring to Scam Them All
Missed a phone call? The Better Business Bureau says answering international telephone fraud calls looking like US calls might cost you more...
-

 257News
257NewsDubai Police Official Twitter, LinkedIn and Pinterest accounts Hacked by Anonymous
An Anonymous hacker going with the handle of @TheHorsemenLulz has hacked 4 official Social Media accounts of UAE‘s Dubai Police. The hacked accounts include LinkedIn,...
-

 238Cyber Events
238Cyber EventsSnowden used a cheap software to gather secret NSA files
Edward Snowden, the American whistleblower, used a very simple ‘Web crawler’ to collect controversial NSA data, according to a senior intelligence official...
-

 173Data Security
173Data SecurityHow to Prevent Your Website from Authentication Hacking Attack? (In Depth Analysis)
Websites though being secured remains at a risk of getting attacked in one or the other way. Internet is coming up with...
-

 191News
191NewsThe President of Nepal has his official website hacked by Iranian hackers
An Iranian hacker going with the handle of Dr.3v1l has hacked and defaced the official website of President of Nepal. Screenshot of the...
-

 78Cyber Crime
78Cyber CrimeU.S. hotel firm ‘knew of credit card breach for two weeks’ before going public
Managers at White Lodging, a hotel management firm that works with various brands including Hilton, Marriott, Westin, Sheraton and Hyatt, may have...
-

 182Password
182PasswordSniffing body odor has ‘enormous potential’ for biometrics, researchers claim
Body odor could be used as a biometric identifier, with high rates of accuracy, due to chemical patterns in the smell that...
-

 220Cyber Events
220Cyber EventsRedHack Hactivists Join hands with activists for a protest against Internet Censorship Laws in Turkey
The Turkish parliament has accepted a highly controversial reversal to a cyber law, granting authorities full power to block certain websites in...
-

 239News
239NewsSyrian Electronic Army Targets Facebook, Google, Yahoo via MarkMonitor Hack
The hardcore supporter of Syrian President Bashar Al Assad and the online hacktavist Syrian Electronic Army has made an attempt to hack...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




