Featured News
-
 267News
267NewsInternet Minefield: NBC Reporter was immediately hacked in Sochi! Your Phone & Laptop will be hacked as well.
Devices brought to Sochi get apparently hacked within few moments of being connected to a Wi-Fi network, according to NBC Nightly News’...
-

 392Cyber Crime
392Cyber CrimeCellphone‑sized $20 gadget can remote‑control car electronics, researchers claim
A tiny, cheap gadget which can ‘hack’ into the network of modern cars to receive radio commands ranging from controlling steering and...
-

 121Scams
121Scams419 Scams: Let The Seller Beware
419s are a well-known scam type, but some scams are more obvious than others. And sometimes it's the seller who's cheated not...
-

 368Password
368PasswordTarget attackers ‘broke in using log‑in from air‑con contractor’
Attackers involved in the Target breach, which led to the theft of 40 million debit and credit card details late last year,...
-

 222Cyber Crime
222Cyber CrimeScared of Anonymous? British Spies DDOS-ed Anonymous Websites: Snowden
The latest in the series of Snowden revelations include attacks of British spies on hacktivists of Anonymous and LulzSec. According to NBC...
-

 191Cyber Crime
191Cyber CrimeIsraeli pilots punished for storing sensitive data on smartphones: Reuters
JERUSALEM: Two Israeli combat pilots were jailed for five days and 12 others were disciplined for storing operational maps on their smartphones,...
-

 416Malware
416MalwareZombie detector: Half‑century‑old tool may help sniff out botnets, researchers claim
A statistical tool first used in 1966 and currently used in speech and gesture recognition may hold a key to sniffing out...
-

 80Cyber Crime
80Cyber CrimeWeak passwords and ancient software left U.S. Government data vulnerable, DHS report finds
Weak passwords and rarely updated software are a recurring theme behind the 48,000 cyber incidents reported to the Department of Homeland Security...
-

 86Password
86PasswordGovernment committee to set facial recognition guidelines
A Department of Commerce committee will meet for the first time this Thursday to begin discussions on a standard of guidelines for...
-

 130Android
130AndroidBrowser security gets a boost with updates to Chrome and Firefox for Android
It is now possible to enable HTTPS secure browsing on every website using Firefox for Android, the Electronic Frontier Foundation has announced.
-

 220Cyber Events
220Cyber EventsPirate Party members nominate Snowden and Manning for Nobel Peace Prize
Pirate party members from Iceland and Sweden have nominated Edward Snowden and Chelsea Manning for Noble prize award. Such a recognition for...
-
 273News
273NewsRedHack hacks ISP TTNET, Vodafone and Turkcell, leaks data of Govt Officials against death of a Gezi protester
RedHack, Turkish hacktivists, breached into the databases of Turkey-based ISP TTNET, and mobile operators, Vodafone and TurkCell, to protest against the death...
-
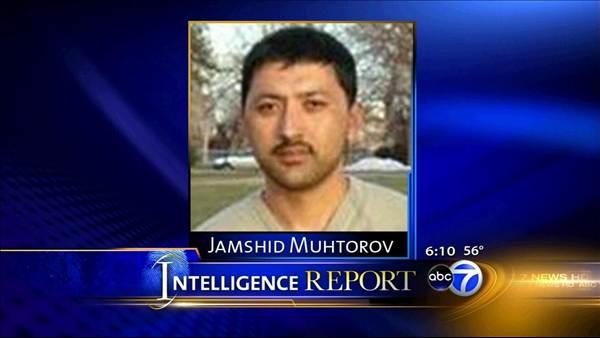
 222Surveillance
222SurveillanceNSA Surveillance Program Challenged by a Terror Suspect in U.S
A terror suspect has challenged the constitutionality of the NSA’s surveillance program alleging that the federal government has gone too far on...
-

 81Cyber Crime
81Cyber CrimeCalifornia students expelled for using a keylogger to hack teachers’ computers
Eleven high school students have been expelled after being caught bugging their teachers’ computers with a key logger device to change their...
-

 78Cyber Crime
78Cyber CrimeHotel franchise hit by credit card hack
White Lodging, a hotel management firm that works under brands including Hilton and Marriott, has suffered a credit card hack revealing customers'...
-
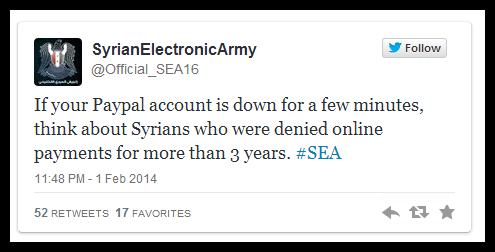
 300News
300NewsEbay and Paypal hacked by Syrian Electronic Army for not providing services in Syria
The pro-Bashar Al Assad hacking group Syrian Electronic Army has hacked into the domain registry of world renowned online shopping and money transaction...
-

 204News
204News30 Ukrainian government and media websites defaced by neo-fascist Svoboda party
Hacktivists from Ukrainian neo-fascist ‘Svoboda’ party hacked and defaced more than 30 Ukrainian government and media websites. Hackers have left a deface...
-
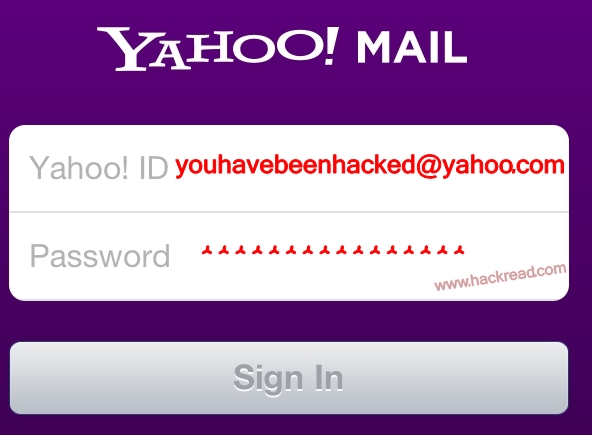
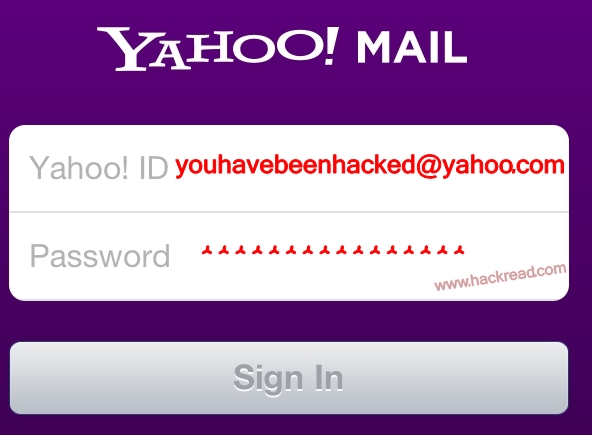 252News
252NewsYahoo! Mail hacked, passwords and user information stolen
Yahoo has been hacked again. On Thursday Yahoo announced that usernames and passwords of its email users have been stolen by unknown hackers. The...
-

 88Password
88PasswordYahoo Mail falls victim to password hack
Yahoo has announced that its email system has recently been subject to a “coordinated effort to gain unauthorized access”.
-

 102Password
102Password‘Honey Encryption’ foils hackers with false positive data
The key to beating hackers might not just lie in stronger security measures and ‘unbreakable’ passwords. Now, it seems like an element...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




