Featured News
-

 83Password
83PasswordBetter latte than never? Starbucks adds extra shot of security after app blunder
Starbucks has promised to update its mobile app - the most-used mobile payment app in America - after a security researcher found...
-

 280News
280NewsAVG in trouble: Gets 19 official domains hacked by Indonesian and Pakistani hackers
The internet security software company AVG is in trouble, this time the company has been attacked by hackers from Indonesia and Pakistan who have...
-

 115Malware
115MalwareFridge raiders: Will 2014 REALLY be the year your Smart Home gets hacked?
At CES 2014, the app was king - and more importantly, the appcessory - fridges, lights, appliances and gadgets built for app...
-
 77Cyber Crime
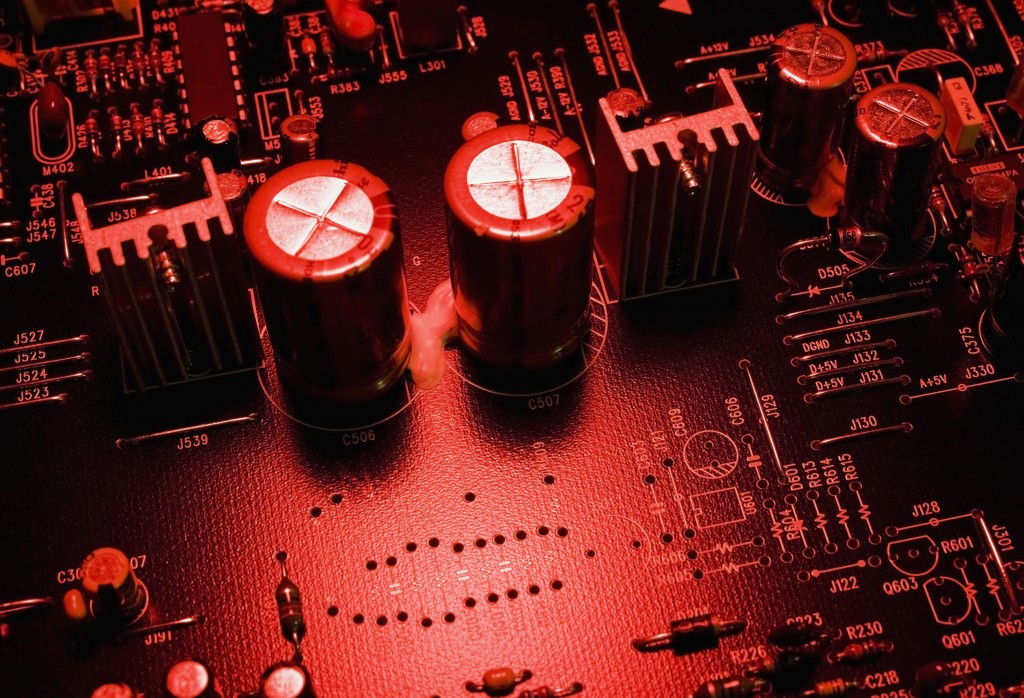
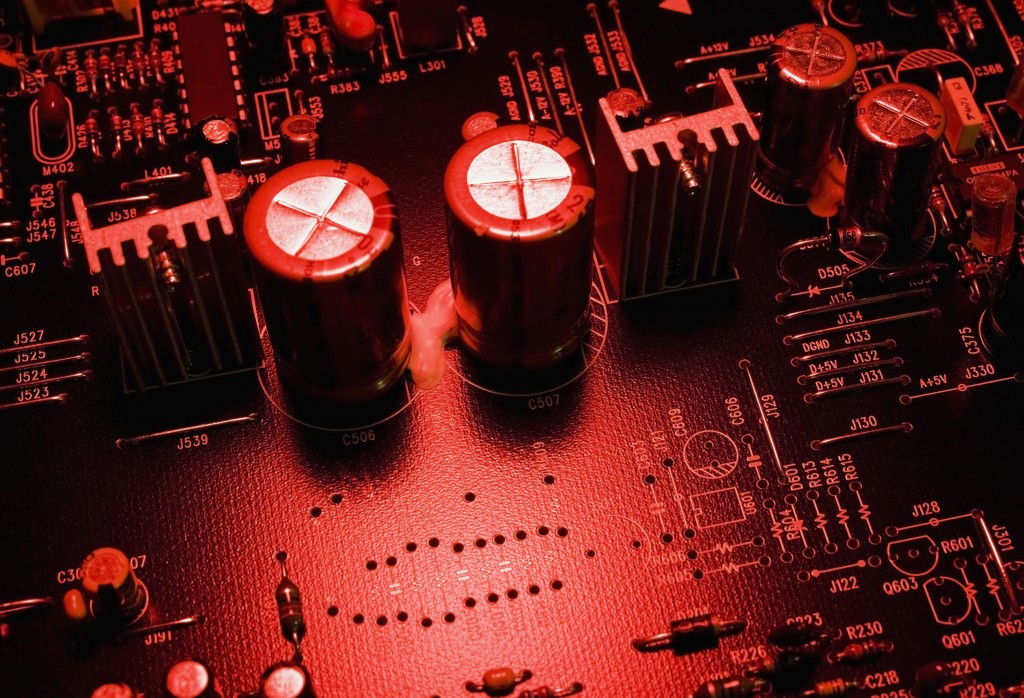
77Cyber CrimeSecret radio technology allowed NSA to spy on PCs disconnected from the Internet
A secret technology which relied on radio transmissions has allowed the National Security Agency to spy on computers disconnected from the internet...
-

 84Cyber Crime
84Cyber CrimeBorrowing tricks from cybercriminals can ‘scare’ web users into safe browsing, Cambridge researchers claim
Computer users often feel bombarded by warnings about malware - particularly in internet browsers, which often repeatedly warn about risky sites -...
-

 241News
241NewsSyrian Electronic Army’s official website hacked and defaced by Turkish Hackers
A group of Turkish hackers going with the handle of @Turkguvenligi on Twitter has hacked and defaced the official website (http://leaks.sea.sy/) of high...
-
 110Surveillance
110SurveillanceNSA Surveillance Fails to Prevent Terrorist Attacks: Report
The US government’s extensive dragnet across the country keeping track of almost everything that travels across the internet and following every single...
-

 67Cyber Crime
67Cyber CrimeMajor cyber attacks ‘can be predicted’ using computer model, researchers claim
Major international cyber attacks follow a pattern - and attacks such as Stuxnet, which targeted Iran's nuclear plant can be predicted by...
-

 60Cyber Crime
60Cyber CrimeMalware in Target’s registers harvested millions of card details for weeks, chain admits
Malicious software was installed in tills in Target stores across the U.S. and went undetected for weeks, the chain has admitted, harvesting...
-

 93How To
93How ToAttention Shoppers! Top tips for defending your accounts against card fraud
Read how to protect yourself if you've been shopping with credit or debit cards (and who hasn't?). As the scope of the...
-

 78Malware
78MalwareBoaxxe adware: ‘A good ad sells the product without drawing attention to itself’ – Pt 1
This is the first in a series of two blog posts on the malware family Win32/Boaxxe.BE whose end goal is to drive...
-
 230News
230NewsMIT Website Hacked by Anonymous to Mark First Death Anniversary of Aaron Swartz
Anonymous hacktivists hacked into the official website of Massachusetts Institute of Technology (MIT) on January 11, 2014 to mark first death anniversary of...
-

 73Cyber Crime
73Cyber CrimeLess than half of consumers take ANY steps to stay safe online, UK government survey finds
A survey of 22,762 consumers conducted by the British government found that less than half took the most basic steps to protect...
-

 79Cyber Crime
79Cyber CrimeLuxury store Neiman Marcus joins growing list of card theft targets
High-end retailer Neiman Marcus has admitted that thieves had accessed its systems and made unauthorized charges on customers’ credit cards over the...
-
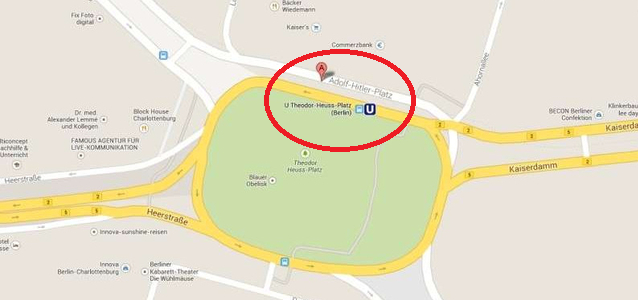
 305Cyber Events
305Cyber EventsGoogle Maps Mistakenly Labels Berlin Square as Hitler Square
Google has apologized for mistakenly listing the Berlin intersection as Adolf-Hitler-Platz, a mistake that was corrected only after a few days. The...
-
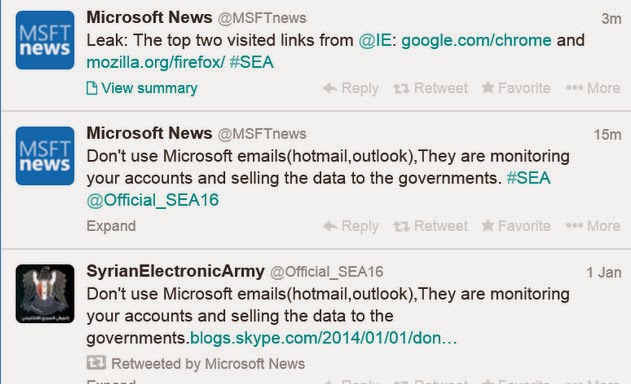
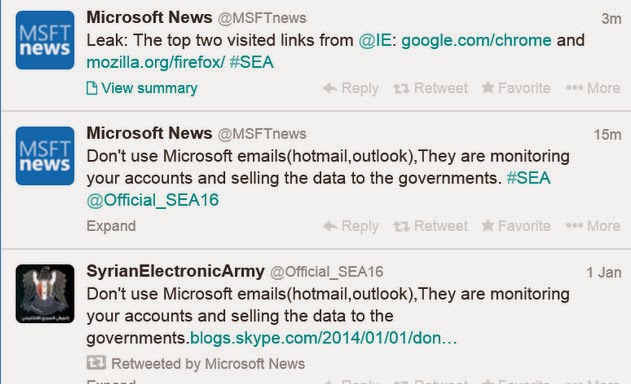 243News
243NewsThe Official Microsoft Blog and Twitter account Hacked by Syrian Electronic Army
The Pro – Assad hackers from Syrian Electronic Army have hacked the official blog and verified Twitter account of Microsoft. A bad...
-

 247Cyber Crime
247Cyber CrimeRacism at It’s Peak: ‘Blacks for sale in $0.42’ online ad sparks outrage in Brazil
Brazil: An online advert on South America’s largest online shopping website (MercadoLivre.com) has put humanity to shame offering “blacks for sale for...
-

 204Surveillance
204SurveillanceEuropean Parliament invites Snowden to testify against NSA’s Surveillance
A European Parliament committee has approved inviting the ex-NSA contractor, Edward Snowden, to testify for US snooping on the EU leaders through...
-

 117How To
117How ToTarget breach expands: what does this mean?
Target's 2013 data breach is expanding in scope and scale, requiring additional vigilance on the part of shoppers to protect their accounts...
-

 443Cyber Crime
443Cyber CrimeTarget announces scale of credit‑card leak was even bigger: 70 million victims or more
Retailer Target has announced that the breach affecting the company was even bigger than thought - and 70 million credit card details...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




