Featured News
-

 433Scams
433ScamsThe Fresh Prince of Bel‑Where? – Academic Publishing Scams
[A shorter version of this article was originally published – without illustrations – on the Anti-Phishing Working Group’s eCrime blog.] Phishing attacks...
-

 106Malware
106MalwareKnow who your Friends are: Staying safe on social sites
Making a mistake on Facebook or other social sites can cost a great deal - either in terms of accidental “oversharing", or...
-

 282News
282NewsSnowden and Assange Targeted by Pro-US Hacker “The Jester”
A self-proclaimed patriot and shadowy hacker has recently launched several cyber-attacks against Ecuador and has also made the statement that such attacks will...
-
 245News
245NewsBangladeshi Department of Immigration & Passports Website Hacked by Group Hp-Hack
The official website of Bangladeshi Department of Immigration & Passports (http://www.dip.gov.bd) was hacked and defaced by the group of Saudi hackers getting famous with...
-

 80Cyber Crime
80Cyber CrimeGaming giant Ubisoft falls victim to breach – user emails and passwords at risk
Game publisher Ubisoft has fallen victim to a website hack, which exposed data including email addresses, user names and encrypted passwords.
-

 123Scams
123ScamsPhishing “test” finds half of employees will take bait, says Atlantic Media CTO
Atlantic Media CTO Tom Cochran emailed employees a fake phishing email supposedly from “Google Apps”, and found that 58% clicked the link.
-

 266News
266NewsUS Air Force Culture & Language Center Hacked, Highly Sensitive Personal Details Leaked by Turkish Ajan
The official website of US Air Force Culture & Language Center () has been hacked, as a result highly sensitive personal details of...
-
 251News
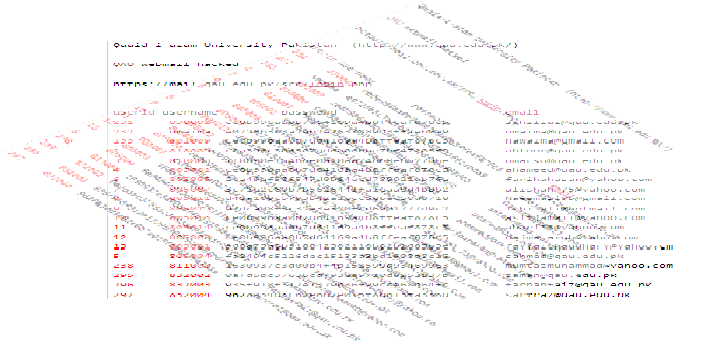
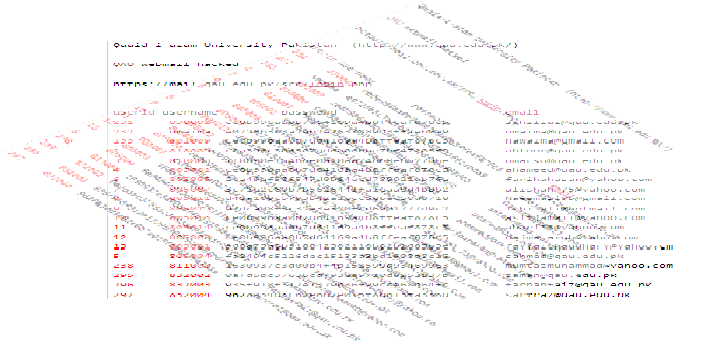
251NewsQuaid-e-Azam University Pakistan Hacked, Login Info leaked by Indian Hacker
An Indian hacker going with the handle of Assassin has hacked into the email system of Pakistan’s Quaid-e-Azam University ), as a result...
-

 186Cyber Events
186Cyber EventsIndia, Brazil and France Rejects Snowden’s Asylum Request
Thing are getting worse for Snowden as Brazil and India have refused asylum request from former NSA’s whistle blower Edward Snowden’s today. The officials...
-

 107Malware
107MalwareThe Home Campaign: overstaying its welcome
The Home Campaign is a malware campaign that uses a modified variant of Darkleech to direct visitors to the Blackhole exploit kit....
-
 87Cyber Crime
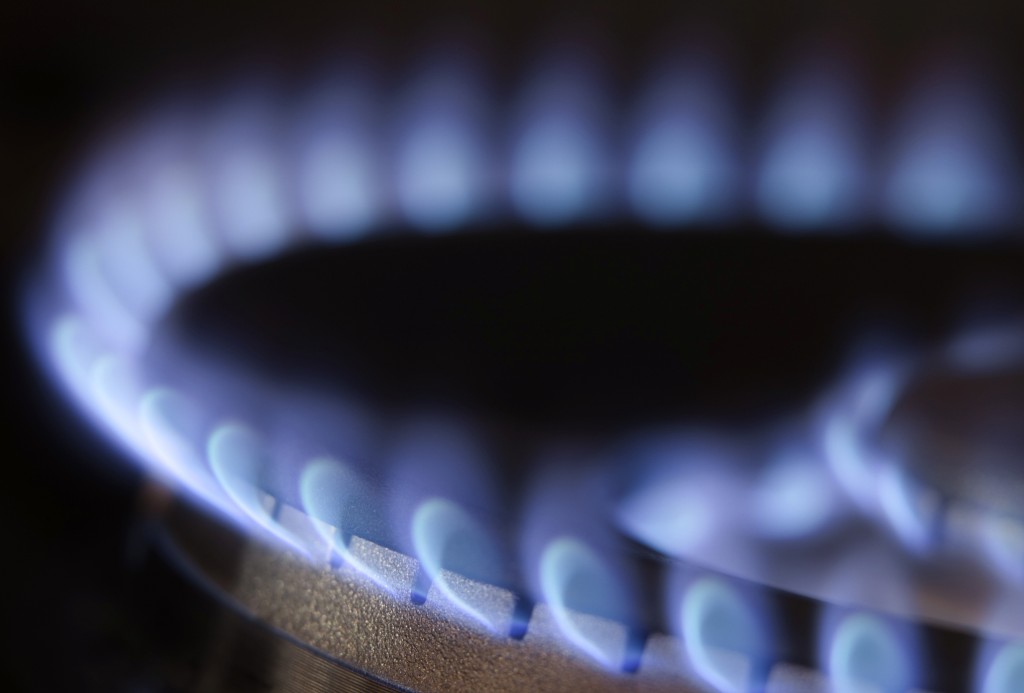
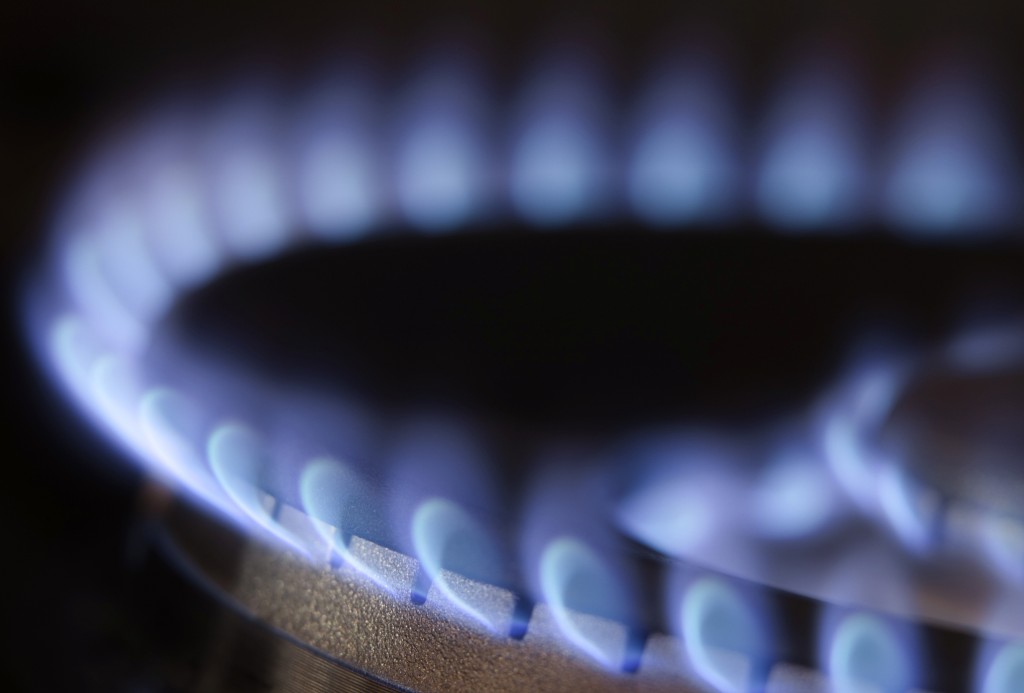
87Cyber CrimeNatural gas plants in U.S. face wave of brute force cyber attacks
Cybercriminals have targeted U.S. energy companies with a wave of brute force cyber attacks, according to the Industrial Control Systems Emergency Response...
-

 270Surveillance
270SurveillanceNew Statement from Edward Snowden in Moscow
The NSA whistle blower Edward Snowden who is in Moscow these days has made a new statement which has been published by Wikileaks. ...
-

 297News
297NewsHere is the List of 19 Countries Where Edward Snowden Has Requested Asylum
The anti-secrecy non-profit organisation Wikileaks which publishes secret information, news leaks, and classified media from anonymous sources has published an application request that...
-

 287News
287NewsTurkish Finance Ministry Office Hacked , 2006-2010 Incoming & Outgoing Data Leaked by Anonymous
A supporter of Anonymous hacker going with the Twitter handle of @RunaGalande has claimed to hack and breach the official website of Turkish Finance Ministry...
-

 273Cyber Crime
273Cyber CrimeFacebook abuse tops cyber crime chart in Indian Punjab
In the state of Punjab, India, 170 cyber-crime complaints have been made in total and the state has topped the chart of...
-

 242Data Security
242Data SecuritySecure Phone App Library Highly Vulnerable
People who are using a different telephone apps on their cell phones need to be cautious, as a researcher has indicated vulnerabilities...
-

 394Cyber Crime
394Cyber CrimeMore malware targeting crypto‑currencies: Litecoin stealing Trojan found
Bitcoin is not the only crypto-currency targeted by malware now that a Trojan designed to steal Litecoins has been discovered. In this...
-

 78Cyber Crime
78Cyber CrimeBusiness secrets being stolen on “industrial scale” says UK spy agency chief
Every month, around 70 sophisticated cyber espionage campaigns target government or industry networks, Sir Iain Lobban, head of Britain's GCHQ spy agency...
-

 176News
176NewsS.Korean Presidential Website Hacked, Personal info of 100,000 People Leaked
The officials at South Korean Presidential office have said that official website of S.Korean President (english.president.go.kr) was hacked on Monday last week, as...
-

 116Scams
116ScamsInstagram hit by fruity spam attack
Instagram users were bombarded with pictures of fruit over the weekend in a spam attack that swept the photo-sharing network.
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan




