Featured News
-
 100Password
100PasswordFacial recognition system “reads” blood vessels for unbreakable security
A new biometrics system could “read” blood vessels under the skin using thermal imaging cameras - a system which its inventors claim...
-

 294News
294NewsLulzSecPeru defaces, leaks data of Peru’s government portals for using NSA’s backed hosting service
LulzSecPeru known as one of the most skilled online hackavists are back, this time by the hackers have hacked and defaced the...
-

 227News
227NewsOfficial Sony Electronics Italy Website Breached, 40k accounts leaked by Turkish Ajan Hackers
The well known Turkish hackers from Turkish Ajan hacking group have hacked into the official website of Sony Electronics (web.sony.it) designated for...
-

 290Surveillance
290SurveillanceMicrosoft allowed NSA to Spy on Skype and Outlook
Microsoft has collaborated extensively with the intelligence services of the United States to allow users’ communications details. The company even helped the...
-

 381Cyber Crime
381Cyber CrimeCyber threats are now the third‑biggest worry for CEOs, Lloyds survey reveals
Cyber risk has shot up in importance for company CEOs and senior executives, according to an Ipsos survey for Lloyds Risk Index...
-

 397Cyber Crime
397Cyber CrimeOld‑school security? Kremlin orders $15,000‑worth of electric typewriters
A Kremlin security agency has ordered $15,000 of electric typewriters - sparking international gossip about a return to “old school” security measures.
-

 292Surveillance
292SurveillanceRussia uses typewriters to prevent Spying by US
The Russian newspaper “Izvestia” reported on Thursday that the Federal Protective Service of the country bought 20 typewriters to prevent sensitive information...
-
 91News
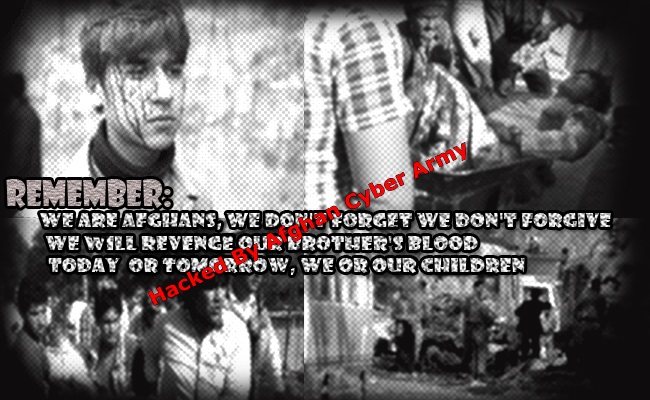
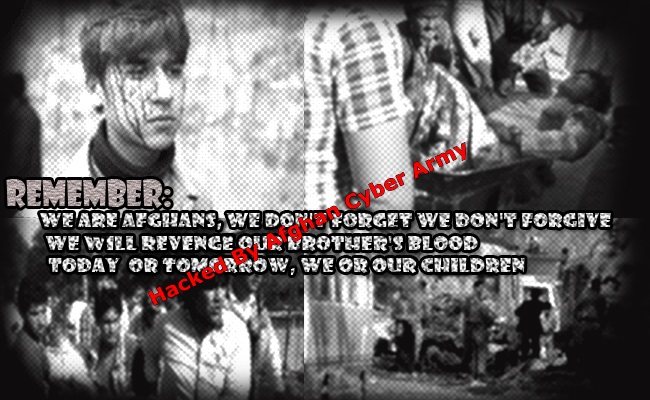
91News6 Pakistani Ministry Websites Hacked by Afghan Cyber Army
A group of hackers claiming to have roots in Afghanistan going with the handle of Afghan Cyber Army has hacked and defaced six...
-

 412Cyber Crime
412Cyber Crime“Cyber‑mercenaries” pose serious new threat, British government warns
Governments around the world are recruiting “cyber-mercenaries” - groups of skilled cyber professionals who target institutions such as banks and energy companies,...
-

 96Malware
96Malware“Bug bounties” are cheap way to keep companies secure, Berkeley study finds
“Bug bounties” paid out for finding and reporting bugs and vulnerabilities are a cheap and effective way for companies to bolster their...
-

 83Malware
83MalwareU.S. Government destroys $170,000 of PCS in malware scare – even mice and keyboards
A U.S. Government department threw away IT components including printers, computer mice and keyboards in an effort to root out a “sophisticated”...
-

 108Scams
108ScamsThe London Scam and the Londonderry Air
My colleagues at ESET Ireland, report that an all-too-familiar scam is currently hitting Irish mailboxes. I’ve talked about it at some length...
-

 102Android
102AndroidDarkleech and the Android Master Key: making a hash of it
I made a comment recently that was subsequently quoted in a recent ESET blog – Android “master key” leaves 900 million devices...
-

 395Cyber Crime
395Cyber CrimeCyber‑threat to London 2012 Olympic opening ceremony revealed
The threat of cyber attack loomed over the opening ceremony for the London Olympics last year, officials have revealed.
-

 413Cyber Crime
413Cyber CrimeNintendo site breached after month‑long brute force assault
A sustained brute force cyber attack battered Nintendo’s defences for a month this summer - and allowed cybercriminals access to private data...
-
 4.3KNews
4.3KNews8 Egyptian Ministry Websites Hacked by Anonymous Jordan, asks Anti-Morsi Protesters Few Questions
An Anonymous hacker going with the handle of Anonymous Jordan has hacked and defaced eight (8) Egyptian Ministry websites against the taking down...
-

 81Cyber Crime
81Cyber CrimeInvestment firm Morningstar admits client credit card numbers leaked in breach
Investment research firm Morningstar says that personal information including credit card numbers for clients, email addresses and passwords may have been compromised...
-

 203News
203NewsAnonymous Group Targets Hawthorne Police Department For Brutally Shooting Dog
The online hackavist from Anonymous group has targeted the Hawthorne Police department in response to police shooting a man’s rottweiler dog. As reported by...
-

 199Data Security
199Data SecurityVulnerabilities in Android will allow NSA to strengthen its grip on users
Just a few days after the reports on vulnerability in the android devices, more shocking news are disclosed. Now, it is believed...
-

 316Cyber Crime
316Cyber CrimeBeware of New Ransomware Scams Targeting Android Devices!
Android phones have now become a source of income for the cyber criminals. The cyber criminals have began a new type of...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




