Featured News
-

 210News
210News75 Chinese Government Websites Hacked by SultanHaikal and M3QD4D
Two hackers from different hacking groups going with the handle of SultanHaikal and M3QD4D have hacked and defaced 71 websites owned by the government...
-

 203News
203NewsWebsites’ servers hacked to host child abuse images: BBC
The watch foundation of internet has made a statement that many online business networks have been hacked by different hackers and the...
-

 97Malware
97Malware“Worst of the worst” abuse images may be being used to spread Trojan, charity warns
Websites for businesses such as furniture stores have been hacked to host child pornography images - and the likely motivation is to...
-

 171Android
171AndroidParanoid Android user? Maybe this “security pouch” will help
The waterproof metal-fabric pocket ensures users cannot be tracked or contacted - offering a level of privacy that DIY alternatives such as...
-

 409Malware
409MalwareIdentity‑exposing malware on Tor “could be work of FBI”
A malware outbreak which reveals the IP addresses of computer users has struck sites on the anonymous Tor network, including some said...
-
 280Cyber Crime
280Cyber CrimeAnonymous Web-host shut down, owner arrested; Tor users compromised by Javascript exploit
FreedomWeb is a renowned Irish concern which provides web hosting services for the purpose of Tor hidden services which reached via the...
-
 98Malware
98MalwareMy Back Pages* – Virus Bulletin papers and articles
I recently completed my 14th Virus Bulletin conference paper, co-written with Intego’s Lysa Myers, on “Mac hacking: the way to better testing?”...
-

 254News
254NewsThailand’s Police Nursing College Website Hacked, Login Details Leaked by Pak Cyber Eaglez
A Pakistani hacker going with the handle of Sizzling Soul from Pak Cyber Eaglez has hacked in to the official website of Thai Police...
-
 151News
151NewsIndira Gandhi International Airport, Indian Customs Website Hacked by Pakistani Hacker
A Pakistani hacker going with the handle of Hasnain Haxor has hacked and defaced the official website of Indian Customs at Indira Gandhi...
-

 189How To
189How ToBulletproof Inbox: Tips for staying safe (and sane) on email
Many of us have got wiser to email spams and scams - but cybercriminals are in the perfect position to “fine tune”...
-

 383Cyber Crime
383Cyber CrimeJava adverts can be used to create million‑strong botnets for just $500
Fake adverts could be used to “remote control” internet browsers on a massive scale - allowing for cheap DDoS attacks, where millions...
-
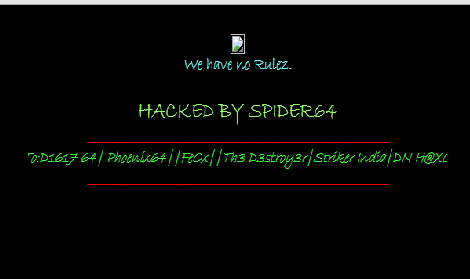
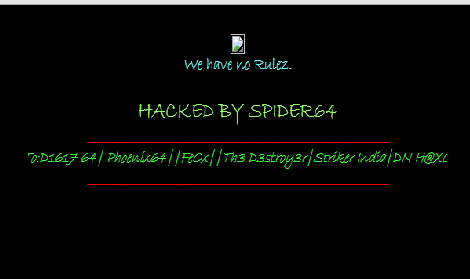 213News
213NewsWebsite of High Commission of India in Islamabad Hacked and Defaced by Spider64
An Indian hacker going with the handle of Spider64 has hacked and defaced the official websites of Indian High Commission in Pakistan....
-
 276News
276NewsWebsites of United Nations Development Programme and UN Volunteers Philippines Hacked by Over-X
The well known Algerian hacker going with the handle of Over-X is back, this time by hacking and defacing 2 official websites...
-

 237News
237NewsOfficial Websites of Automobile Giants Fiat and Dodge Australia Hacked by Dr.SHA6H
A well known hacker going with the handle of Dr.SHA6H has hacked and defaced 3 official websites of automobile and motor companies including...
-
 181Surveillance
181SurveillanceXKeyscore: NSA tool which tracks and stores everything a user does on the internet
Meet XKeyscore a tool used by NSA which can track and store everything a user does through the internet — XKeyscore allows the...
-

 89Malware
89MalwareRevealed: How a “malicious charger” infects iPhone with spyware in under a minute
Borrowing an iPhone charger - or using one in a public place - might be more risky than you think. Researchers from...
-

 88Password
88PasswordPets’ names and partners’ names remain top password choices, says Google
One in six adults use the name of a pet as the basis of their password, and two-thirds use their partner's name,...
-

 96Malware
96MalwareNew ransomware uses webcam and Homeland Security threat to scare victims
A new ransomware infection scares its victims by invoking the name of the Department of Homeland Security, and the National Cyber Security...
-

 297Cyber Events
297Cyber EventsSnowden leaves airport after getting 1 year asylum in Russia
NSA‘s whistleblower Edward Snowden has left the airport after receiving 1 year asylum in Russia from the government. RT reports that Snowden’s representative Anatoly Kucherena...
-

 188Surveillance
188SurveillanceIsraeli company ‘Verint’ to win Indian mass cyber surveillance contract
An Israeli based internet surveillance company ‘Verint Systems‘ is all set to win a contract from Department of Telecommunications, government of India to assist...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




