Featured News
-

 175Android
175AndroidParanoid Android user? Maybe this “security pouch” will help
The waterproof metal-fabric pocket ensures users cannot be tracked or contacted - offering a level of privacy that DIY alternatives such as...
-

 412Malware
412MalwareIdentity‑exposing malware on Tor “could be work of FBI”
A malware outbreak which reveals the IP addresses of computer users has struck sites on the anonymous Tor network, including some said...
-
 284Cyber Crime
284Cyber CrimeAnonymous Web-host shut down, owner arrested; Tor users compromised by Javascript exploit
FreedomWeb is a renowned Irish concern which provides web hosting services for the purpose of Tor hidden services which reached via the...
-
 102Malware
102MalwareMy Back Pages* – Virus Bulletin papers and articles
I recently completed my 14th Virus Bulletin conference paper, co-written with Intego’s Lysa Myers, on “Mac hacking: the way to better testing?”...
-

 259News
259NewsThailand’s Police Nursing College Website Hacked, Login Details Leaked by Pak Cyber Eaglez
A Pakistani hacker going with the handle of Sizzling Soul from Pak Cyber Eaglez has hacked in to the official website of Thai Police...
-
 157News
157NewsIndira Gandhi International Airport, Indian Customs Website Hacked by Pakistani Hacker
A Pakistani hacker going with the handle of Hasnain Haxor has hacked and defaced the official website of Indian Customs at Indira Gandhi...
-

 192How To
192How ToBulletproof Inbox: Tips for staying safe (and sane) on email
Many of us have got wiser to email spams and scams - but cybercriminals are in the perfect position to “fine tune”...
-

 387Cyber Crime
387Cyber CrimeJava adverts can be used to create million‑strong botnets for just $500
Fake adverts could be used to “remote control” internet browsers on a massive scale - allowing for cheap DDoS attacks, where millions...
-
 218News
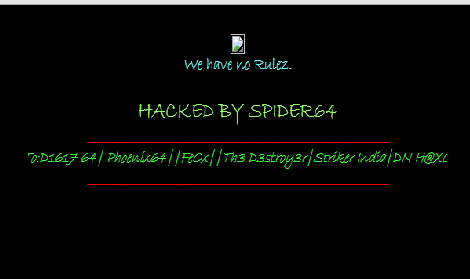
218NewsWebsite of High Commission of India in Islamabad Hacked and Defaced by Spider64
An Indian hacker going with the handle of Spider64 has hacked and defaced the official websites of Indian High Commission in Pakistan....
-
 280News
280NewsWebsites of United Nations Development Programme and UN Volunteers Philippines Hacked by Over-X
The well known Algerian hacker going with the handle of Over-X is back, this time by hacking and defacing 2 official websites...
-

 242News
242NewsOfficial Websites of Automobile Giants Fiat and Dodge Australia Hacked by Dr.SHA6H
A well known hacker going with the handle of Dr.SHA6H has hacked and defaced 3 official websites of automobile and motor companies including...
-
 185Surveillance
185SurveillanceXKeyscore: NSA tool which tracks and stores everything a user does on the internet
Meet XKeyscore a tool used by NSA which can track and store everything a user does through the internet — XKeyscore allows the...
-

 92Malware
92MalwareRevealed: How a “malicious charger” infects iPhone with spyware in under a minute
Borrowing an iPhone charger - or using one in a public place - might be more risky than you think. Researchers from...
-

 93Password
93PasswordPets’ names and partners’ names remain top password choices, says Google
One in six adults use the name of a pet as the basis of their password, and two-thirds use their partner's name,...
-

 100Malware
100MalwareNew ransomware uses webcam and Homeland Security threat to scare victims
A new ransomware infection scares its victims by invoking the name of the Department of Homeland Security, and the National Cyber Security...
-

 301Cyber Events
301Cyber EventsSnowden leaves airport after getting 1 year asylum in Russia
NSA‘s whistleblower Edward Snowden has left the airport after receiving 1 year asylum in Russia from the government. RT reports that Snowden’s representative Anatoly Kucherena...
-

 191Surveillance
191SurveillanceIsraeli company ‘Verint’ to win Indian mass cyber surveillance contract
An Israeli based internet surveillance company ‘Verint Systems‘ is all set to win a contract from Department of Telecommunications, government of India to assist...
-

 299Cyber Crime
299Cyber CrimeBradley Manning faces 136-year jail sentence for leaking secret files to Wikileaks
A Us solider by the name of Bradley Manning who is known to have handed over thousands of confidential government documents to...
-
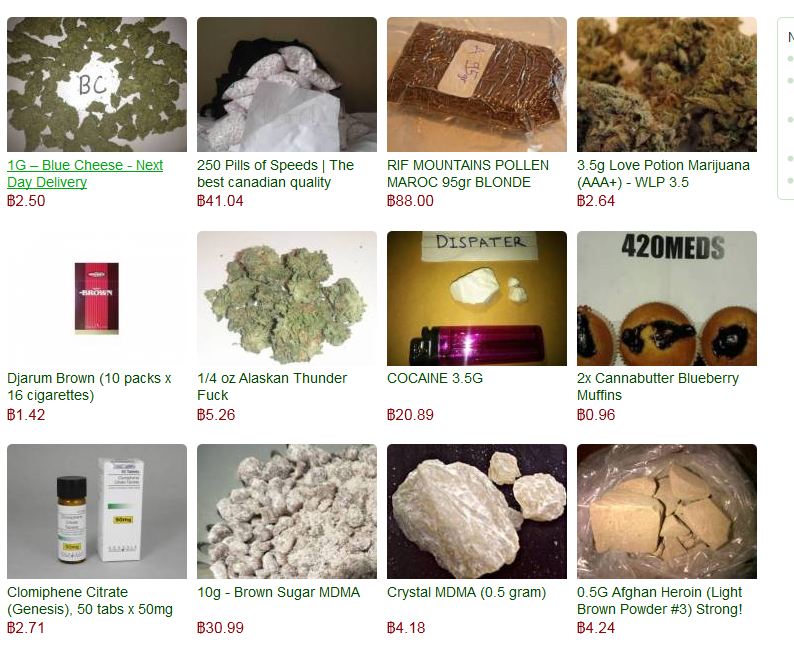
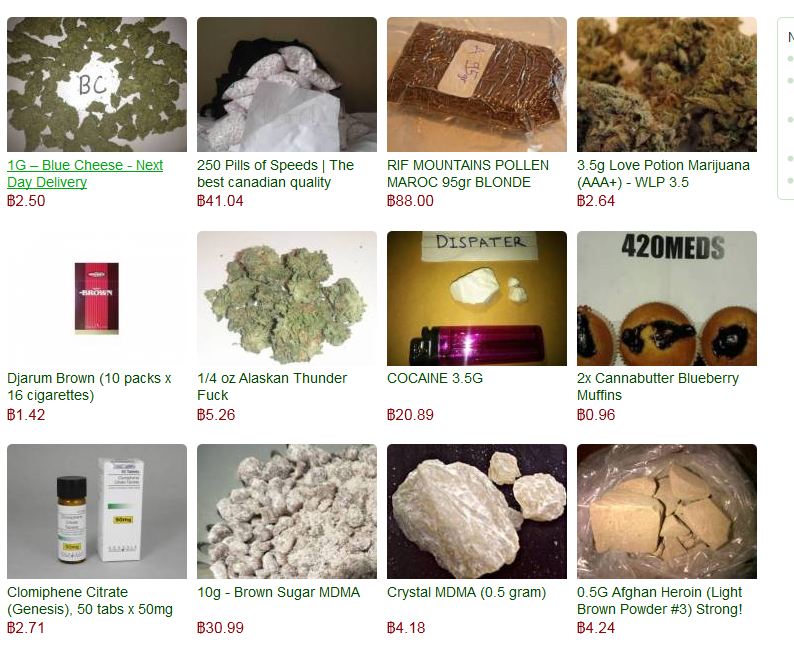 87Cyber Crime
87Cyber CrimeHackers “frame” security blogger with Silk Road heroin delivery
Members of a Russian cybercrime forum attempted to frame respected security blogger Brian Krebs by mailing 13 bags of heroin to his...
-

 262News
262News#OpIzzah & #OpIsrael: Login Details of 33,895 Israelis Leaked by Phr0zenMyst
A hacker going with the handle of @Phr0zenM on Twitter has claimed to leak 33,895 login details of Israeli citizens after breaching several...
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan




