Featured News
-

 89Malware
89MalwareRevealed: How a “malicious charger” infects iPhone with spyware in under a minute
Borrowing an iPhone charger - or using one in a public place - might be more risky than you think. Researchers from...
-

 88Password
88PasswordPets’ names and partners’ names remain top password choices, says Google
One in six adults use the name of a pet as the basis of their password, and two-thirds use their partner's name,...
-

 97Malware
97MalwareNew ransomware uses webcam and Homeland Security threat to scare victims
A new ransomware infection scares its victims by invoking the name of the Department of Homeland Security, and the National Cyber Security...
-

 297Cyber Events
297Cyber EventsSnowden leaves airport after getting 1 year asylum in Russia
NSA‘s whistleblower Edward Snowden has left the airport after receiving 1 year asylum in Russia from the government. RT reports that Snowden’s representative Anatoly Kucherena...
-

 188Surveillance
188SurveillanceIsraeli company ‘Verint’ to win Indian mass cyber surveillance contract
An Israeli based internet surveillance company ‘Verint Systems‘ is all set to win a contract from Department of Telecommunications, government of India to assist...
-

 294Cyber Crime
294Cyber CrimeBradley Manning faces 136-year jail sentence for leaking secret files to Wikileaks
A Us solider by the name of Bradley Manning who is known to have handed over thousands of confidential government documents to...
-
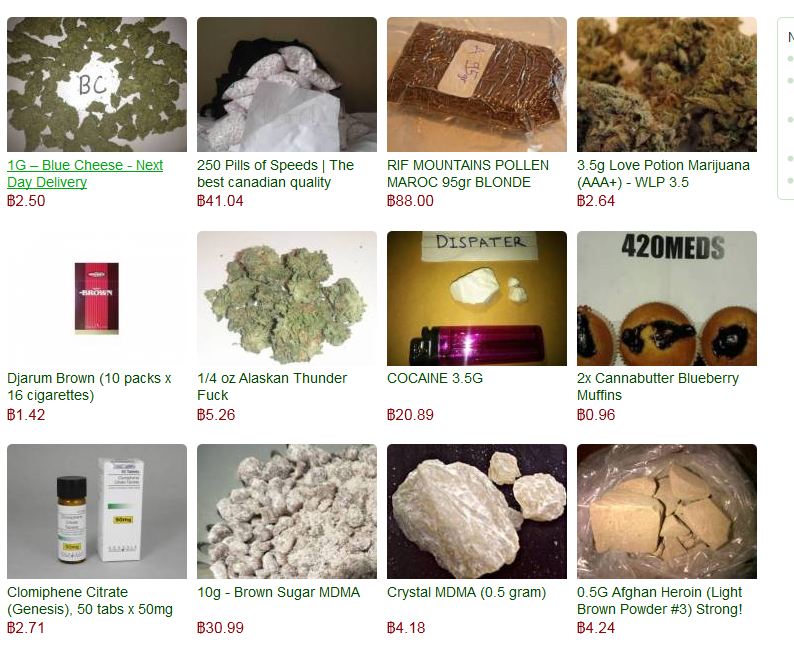
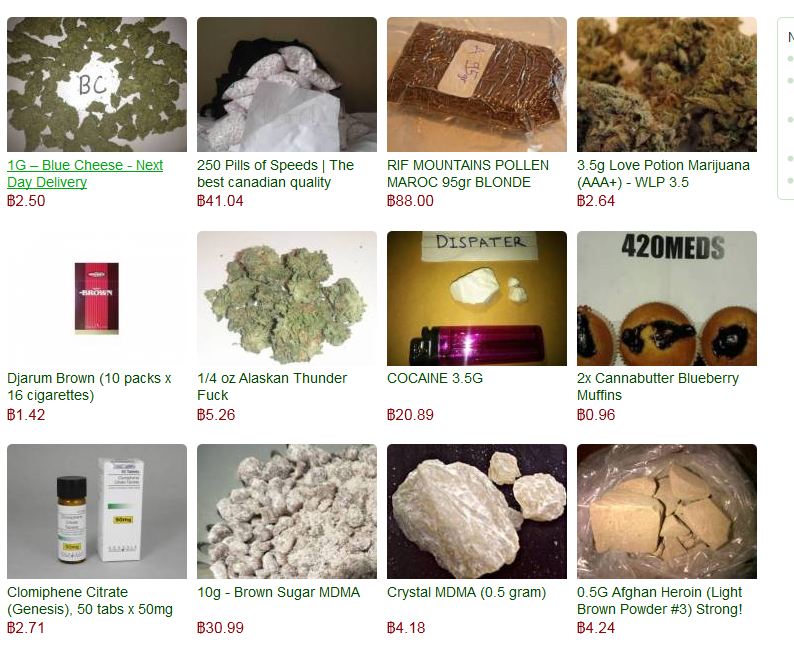 84Cyber Crime
84Cyber CrimeHackers “frame” security blogger with Silk Road heroin delivery
Members of a Russian cybercrime forum attempted to frame respected security blogger Brian Krebs by mailing 13 bags of heroin to his...
-

 257News
257News#OpIzzah & #OpIsrael: Login Details of 33,895 Israelis Leaked by Phr0zenMyst
A hacker going with the handle of @Phr0zenM on Twitter has claimed to leak 33,895 login details of Israeli citizens after breaching several...
-

 308News
308NewsCyber War: McDonalds Indonesia and 914 Websites Hacked by BD Grey Hat Hackers
Cyber war between Bangladeshi and Indonesian hackers is at peak where hackers from both sides are attacking each other’s cyber space, this...
-
 394Cyber Crime
394Cyber CrimeThomson Reuters is latest victim of high‑profile Twitter hacks
A Twitter account used by international news agency Thomson Reuters was compromised this week, by hackers affiliated to the Syrian Electronic Army.
-

 301News
301NewsThomson Reuters Official Twitter Account Hacked by Syrian Electronic Army
The hackers from Syrian Electronic Army have hacked the official Twitter account of New York based multinational media and information firm Thomson Reuters Corporation. After...
-

 383Malware
383MalwareVersatile and infectious: Win64/Expiro is a cross‑platform file infector
Recently, our anti-virus laboratory discovered an interesting new modification of a file virus known as Expiro which targets 64-bit files for infection....
-

 208Surveillance
208SurveillanceTurkey frees bird accused of spying for Israel
X-ray result of bird detained for spying Last week Turkish authorities had captured a bird suspecting it was spying for Israel, but later...
-

 144How To
144How ToSafe Summer PC Usage – beat the heat and stay secure with your laptop, tablet or smartphone
Beat the heat, find somewhere cool to compute! But first check our tips on how to more safely navigate the mall, lobby,...
-

 68Cyber Crime
68Cyber CrimeReal damage of cybercrime may be counted in job losses, not dollars, says CSIS report
Earlier estimates of “trillion-dollar” damage to the world economy may have overstated the financial impact of cybercrime, according to a report by...
-

 208News
208NewsOfficial Twitter account of UAE’s Foreign Minister Hacked and Restored
Just few moments ago the official Twitter account of United Arab Emirates (UAE)’s Foreign Minister Sheikh Abdullah bin Zayed Al Nahyan was hacked...
-

 317News
317NewsVenezuela Military Domains Hacked by Dr.SHA6H and Colombian Hacker
In two different cyber attacks three official sub-domains of Venezuelan military server (mil.ve) were hacked and defaced by hackers going with the...
-

 297News
297News430 Websites Hacked by Turk Hack Team
A hacker going with the handle of Black-Spy from Turk Hack Team has hacked and defaced 430 websites from different countries around the world....
-
 245News
245NewsViber’s Apple App store hacked, description changed by Syrian Electronic Army
Last week I reported that the famous and widely used Viber messenger was hacked by some Syrian Electronic Army and they also...
-
 193Geek
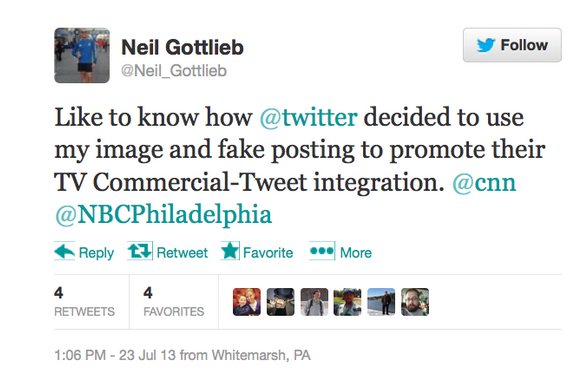
193GeekTwitter Caught Hijacking This Guy’s Account To Make Fake Tweets Promoting Its New TV Product
Twitter authorities have been caught doing something unexpected when a Twitter user going with the handle of @Neil_Gottlieb came to know about misuse...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




