Featured News
-

 269News
269NewsOfficial websites of Avira Anti-Virus Slovenia & United Nation Armenia hacked by Dr.SHA6H
A profile Syrian hacker going with the handle of Dr.SHA6H has hacked the official website of German based Avira antivirus software company designated...
-

 89Cyber Crime
89Cyber CrimePhishing warning after Vodafone hack leaks personal information for 2 million customers
A breach which has leaked personal data for two million Vodafone Germany customers has ben claimed to be the work of an...
-

 98Password
98PasswordThe end? “Passwords are done,” says Google security chief
“Passwords are done at Google,” said Heather Adkins, Google’s information security chief - and said that “the game is over” for start-ups...
-

 486How To
486How ToA scam‑spotters guide: Ten things your bank will NEVER do – but cybercriminals will
These days cybercriminals will use phone calls, SMS messages, emails, fake apps - and even couriers - in an effort to get...
-
 209Surveillance
209SurveillanceSnowden Leaks: Top-secret document shows NSA shares Personal Details of U.S citizens with Israel
The National Security Agency (NSA) shares first hand intelligence with Israel without omitting personal details of U.S citizens, shows top-secret document handing...
-

 192Data Security
192Data SecuritySMS Fake Installer tricking Android Users
Nathan Collier of Webroot ThreatVlog, talks about an old, but still active, SMS Fake Installer, a Russian based program used to trick...
-

 344Cyber Events
344Cyber EventsFearing Anonymous? Government bans use of Masks in Rio de Janeiro during protests
Members of the Rio de Janeiro state voted on Tuesday (September 10th) a bill that prohibits every kind of mask, especially Guy...
-

 311News
311News#OpIsraelReload: AnonGhost hacks 400 Israeli websites, claims to leak Credit Card details
The online hackavist going with the handle of AnonGhost along with TeamR00t have claimed to hack and deface around 400 Israeli websites...
-
 228News
228NewsWebsite of Passport & Visa Center, Indian Embassy in Bahrain Defaced by ZHC
The online hacktavist group Z Company Hacking Crew (ZHC) has hacked and defaced the official website of Octic International that act as...
-

 190How To
190How ToEncryption advice for companies in the wake of Snowden NSA revelations
What are the immediate practical implications of the Snowden-prompted revelation that the NSA has broken or circumvented a lot of commercially available...
-

 411Scams
411ScamsTwitter faces fruit invasion as weight‑loss spammers invade via Hootsuite
Twitter has been hit by a wave of spam promising “pure garcinia cambogia” - a vegetable extract used in weight loss supplements....
-
 250News
250NewsSyrian Electronic Army Hacks FOX TV Hootsuite social media account
The Syrian Electronic Army is back in news by hacking the official Hootsuite account of FOX TV, used to post online content...
-

 400Password
400PasswordApple’s fingerprint‑reading iPhone 5S – a new dawn for biometric security?
Apple introduced biometric security to iPhone for the first time with the launch of its new iPhone 5S, featuring what Apple describes...
-
 253Geek
253GeekMicrosoft takes over Nokia’s Cell Phone Business in $ 7 Billion: what will be the effect on Microsoft’s shares and revenues?
Microsoft Corporation has entered into a $7 Billion agreement with Nokia purchasing its cell phones and devices business. The deal which will...
-

 227News
227News627 websites hacked and defaced by Indonesian Hackers for #OpFreeSyria
Two Indonesian hackers going with the handle of SultanHaikal and Brian Kamikaze have hacked and defaced total 627 random websites under the...
-

 182How To
182How ToComment/No Comment: a word about blog comments
After taking quite a long break from comment moderation on the WeLiveSecurity blog, I’ve recently started receiving comment notifications and have therefore...
-

 180Cyber Crime
180Cyber CrimeInside a scam factory: Gray hat hacker offers peek at how Nigerian 419ers work
Keylogging tools to steal personal information from victims are available as a “service” from a site known as PrivateRecovery, which offers the...
-

 373Password
373Password“Silent” audio could be key to unlocking PCs, new password‑beating start‑up claims
Simply holding your phone a few inches from your PC to "hear" signals inaudible to humans will be enough to log in...
-
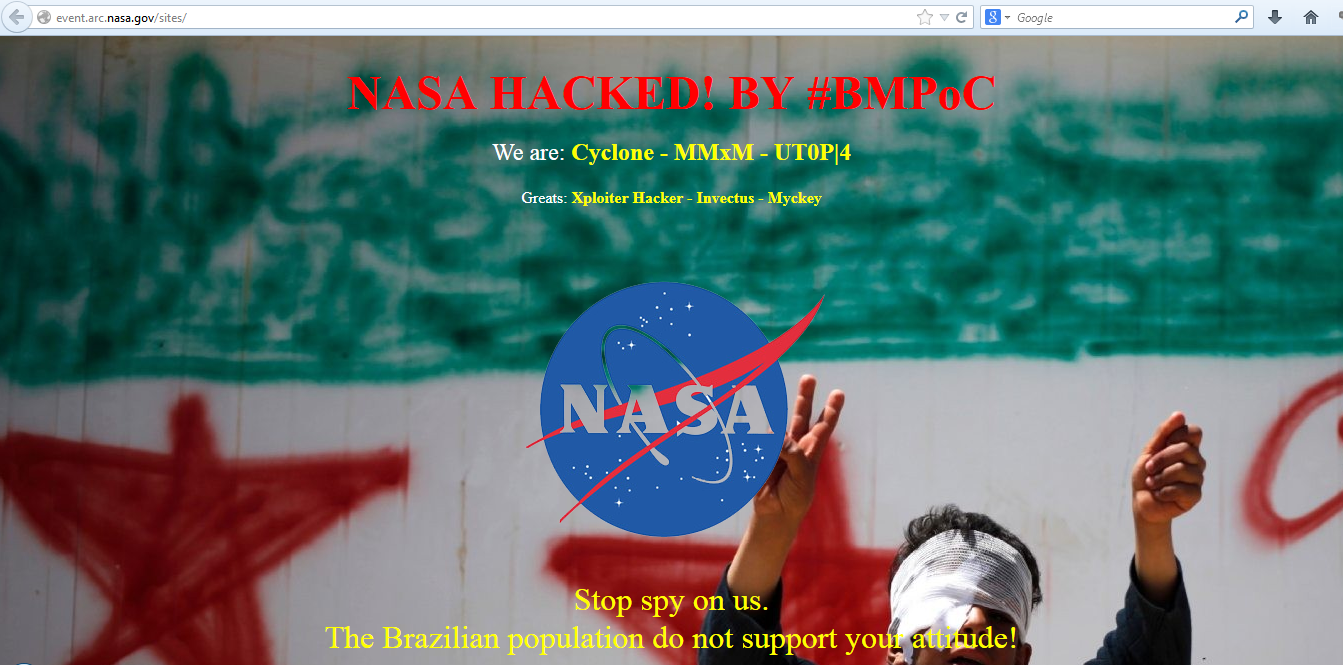
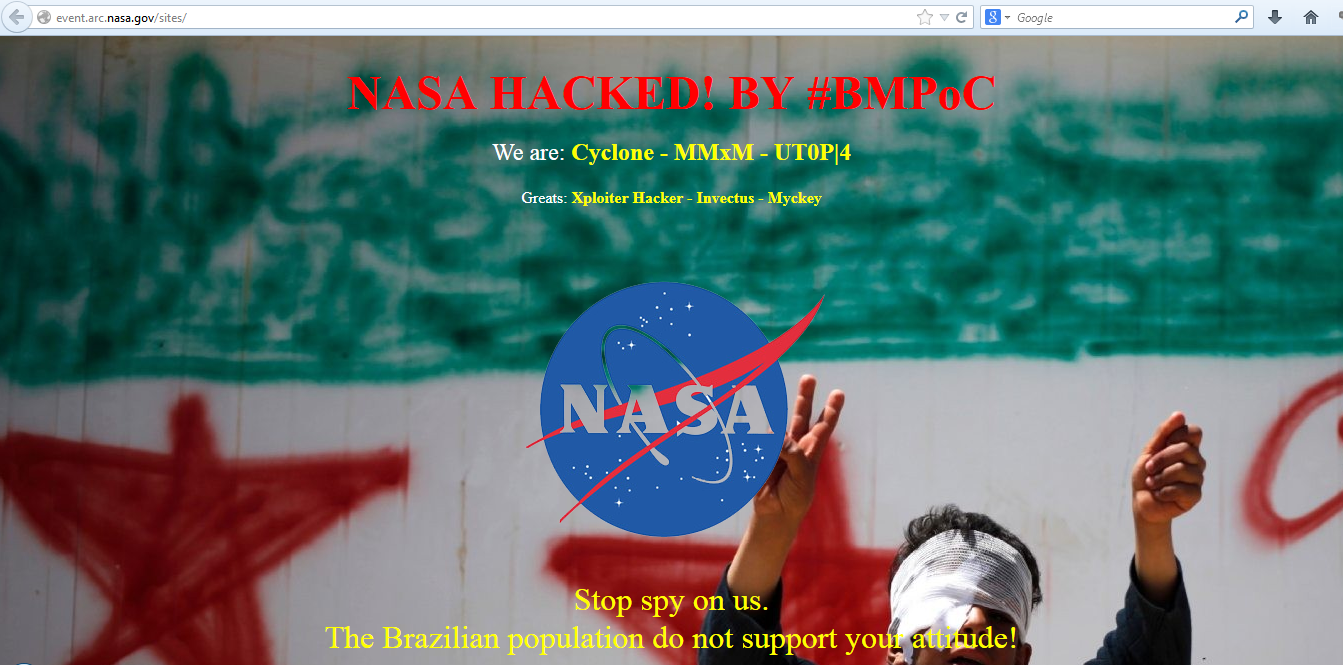 188News
188News14 official NASA domains hacked by BMPoC, left with messages against NSA
National Aeronautics and Space Administration (NASA) which is now more famous for its poor cyber security rather than any else is again under attack,...
-

 97Malware
97MalwareHesperbot – technical analysis: part 2/2
In this 3rd Hesperbot blog post we’ll look at the most intriguing part of the malware - the way it handles network...
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan




