Featured News
-

 201News
201NewsU.S. Senator asks if FBI can get iPhone 5S fingerprint data via Patriot Act
Since Senator. Al- Franken has become of part of the United States Senate, he has been the Chairman of Senate Judiciary Subcommittee...
-
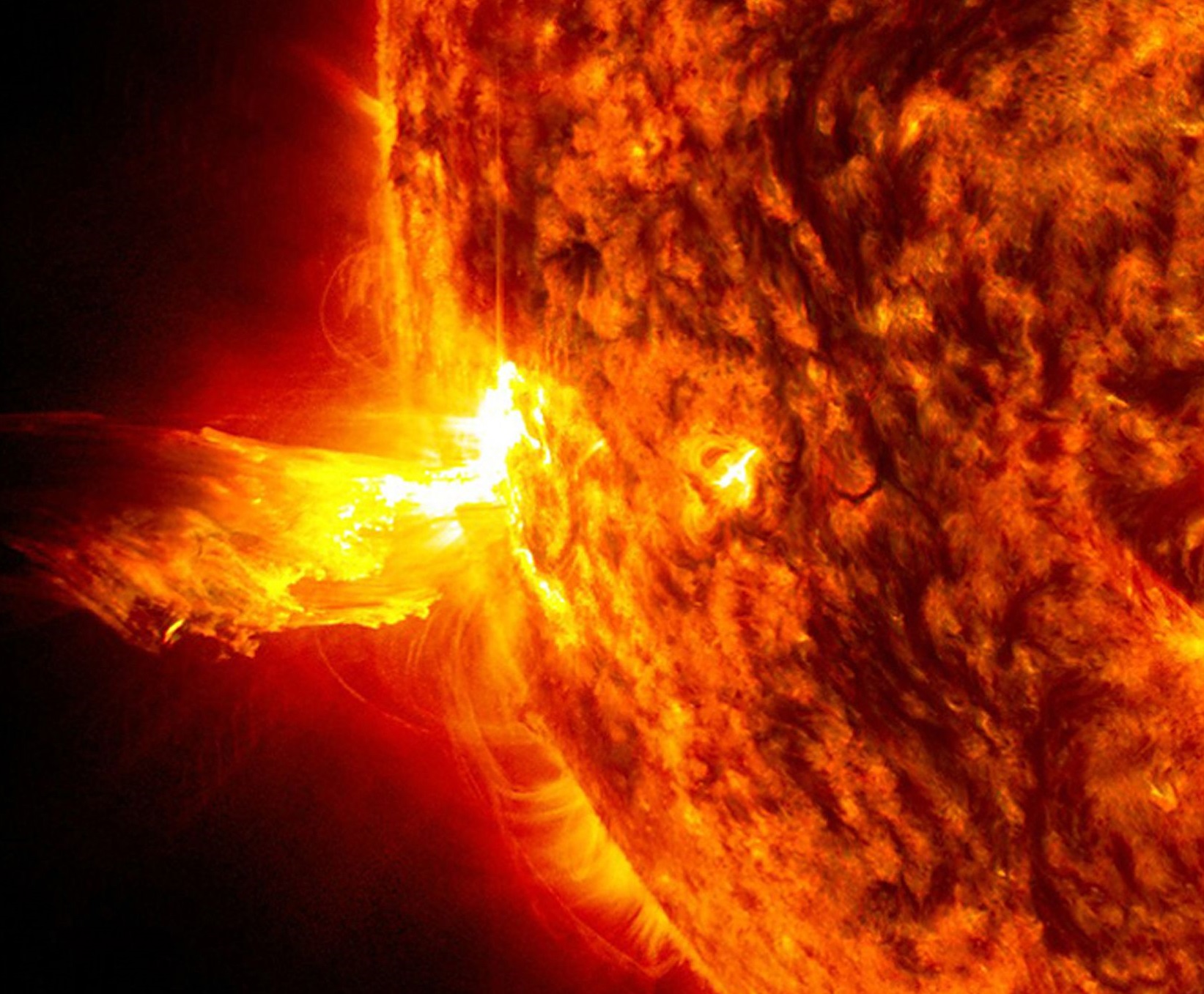
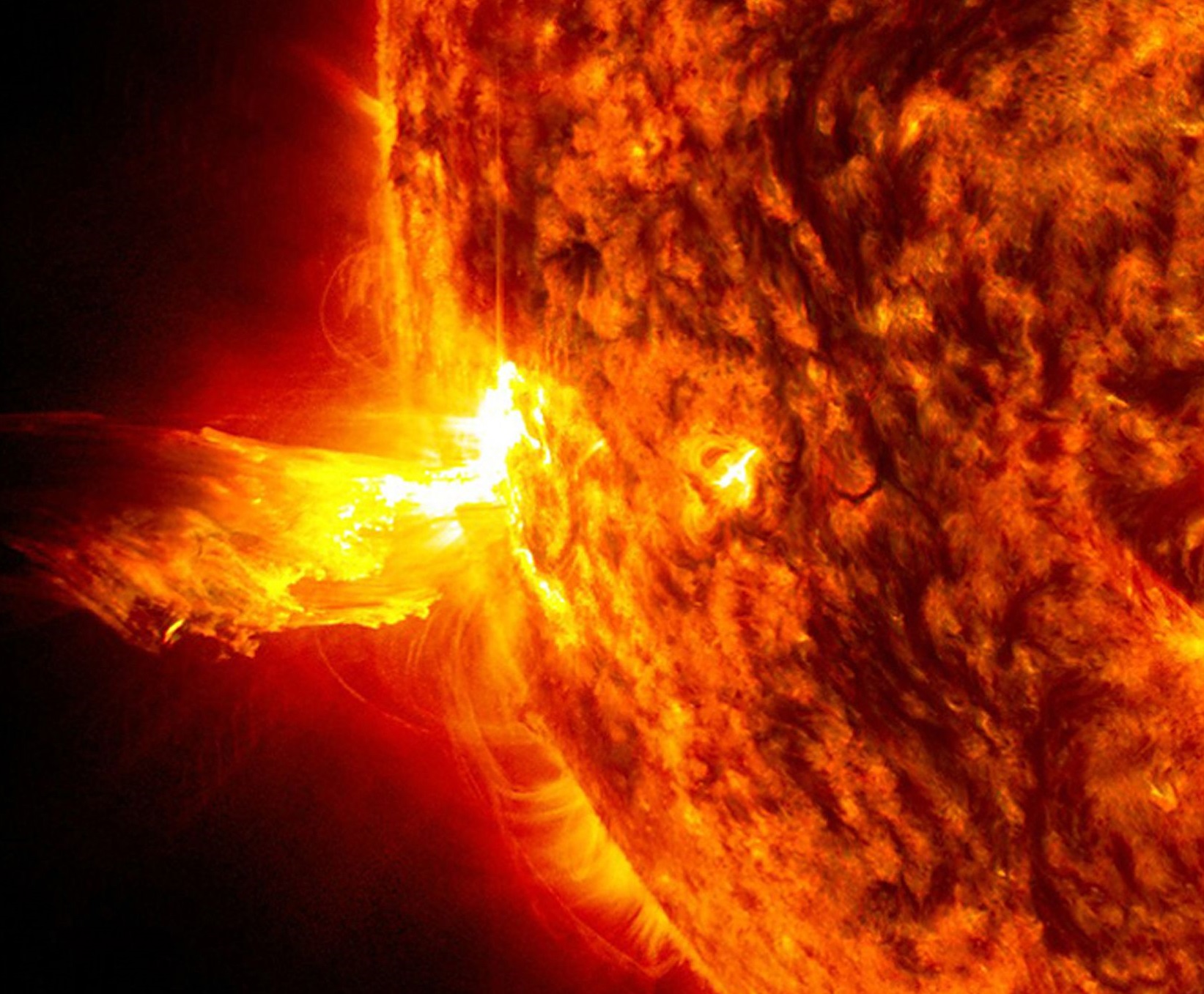 187Malware
187MalwareWin32/Napolar – A new bot on the block
There is a new bot on the block. ESET identifies it as Win32/Napolar while its author calls it solarbot. This piece of...
-

 88Cyber Crime
88Cyber Crime“I was invited to their friend’s wedding!” Recycled Yahoo! IDs leak VERY private information
Yahoo! recently began recycling “inactive” user accounts, in an effort to woo new customers - but some customers who have acquired these...
-

 177Geek
177GeekFake ‘Waterproof iPhone’ ad tricks users into iOS7 Update and Destroy their smartphones
Yesterday I updated you with NYPD’s activity where it was found running a campaign, asking users to upgrade their iPhone and iPads to...
-
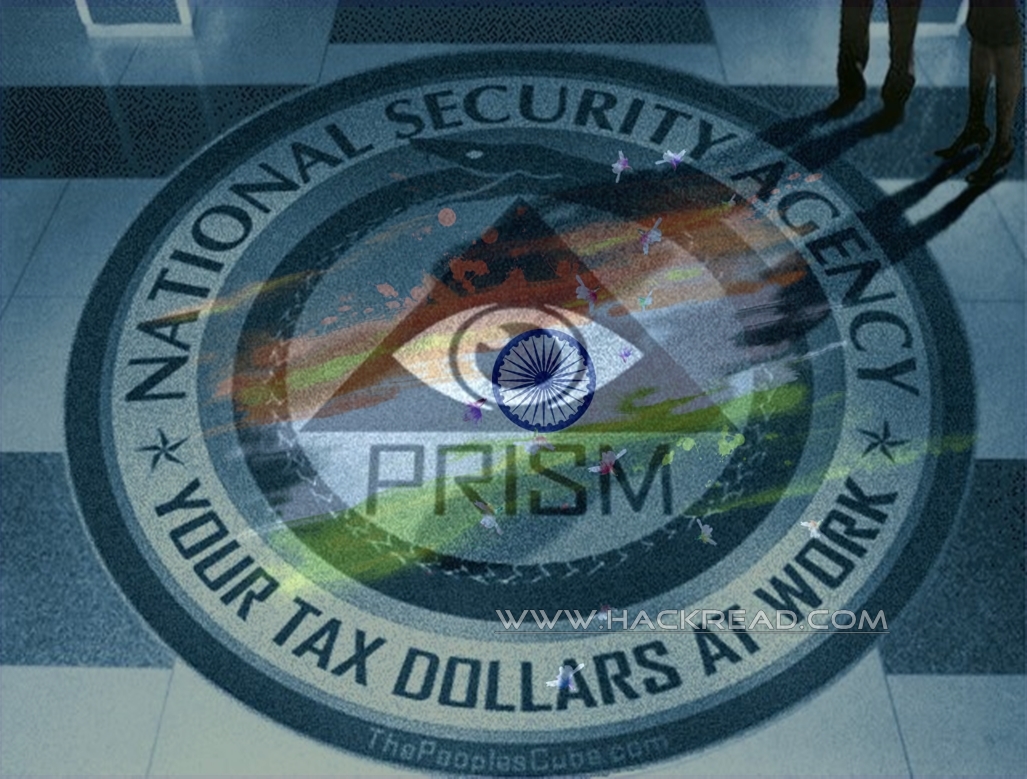
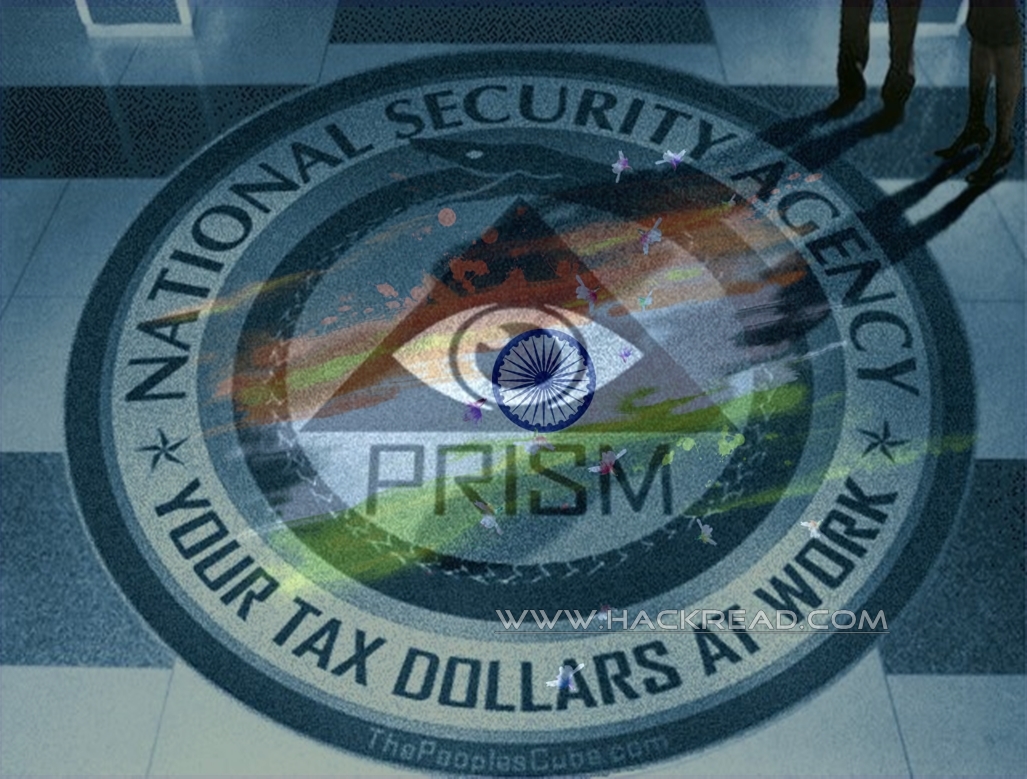 129Surveillance
129SurveillanceIndia Massively Spied By NSA, collected Highly Confidential Internet and Telephonic Data
Among the list of those countries which are considered a top target by the NSA‘s surveillance program, India has been up there...
-

 432How To
432How ToBYO‑Doh! How not to be the “bring your own disaster” guy
Many workplaces allow wokers to bring their own smartphones, tablets and PCs to work - a practise described as "Bring Your Own...
-

 88Password
88PasswordKeep your Droid on a leash: Google lets users change passwords remotely
Android users will now be able to remotely add a password to a lost device, even if it's locked, or already being...
-

 90Malware
90MalwareKnown unknowns – detecting rootkits under OS X
We think that there could be rootkits targeting the OS X platform, but we have very limited visibility into that threat right...
-

 429Password
429Password“Do not keep sensitive data on iPhone,” group warns after latex‑fingerprint hack
Germany's Chaos Computer Club released a video showing how a "fake fingerprint" made from latex could be used to fool the sensor,...
-

 405Geek
405GeekWhy NYPD is asking Users to Update iPads and iPhones to iOS 7?
The New York Police Department has issued a statement in which users have been asked to update their iPad and iPhone devices...
-

 232News
232NewsPalestine Ministry of Justice Website Hacked and Defaced by Jordanian Hacker
A Jordanian hacker going with the handle of Evil-Jo has hacked and defaced the official website of Palestine Ministry of Justice yesterday...
-

 307News
307NewsiPhone 5S Fingerprint Sensor Hacked! Hacker May Get $16K after Verification
One lucky hammer group had already nailed the fingerprint sensor of iPhone 5S. The phone will finally hit the sales floor on...
-

 179News
179NewsPakistani Hackers Defaces Google, Google Images and Google Translator Domain for Burundi
A Pakistani hacktivist group going with the handle of Team Madleets have hacked and defaced five (5) official Google domains designated for Republic of...
-

 95Cyber Crime
95Cyber CrimeGrand Theft Android: Gamers warned to avoid fake “iFruit” GTA app
Android gamers have been warned to be wary of Grand Theft Auto V’s official “partner” app – Grand Theft Auto iFruit –...
-

 247News
247NewsCyber War Continues as Indian Hacker Hacks Bangladeshi Prime Minister Office Website
Famous Indian hacker going with the handle of Yamraaj has hacked and defaced one of the official website of Bangladeshi Prime Minister...
-

 249News
249NewsAnonGhost Hacks and Defaces 75 Israeli Websites
The online hacktavist AnonGhost has hacked and defaced 75 Israeli websites from 15th to 19th September. AnonGhost left a deface page along...
-

 126Cyber Crime
126Cyber CrimeCybercriminals trying new tactics, security body warns – and attacks could have “large impact”
Cybercriminals are switching tactics, a leading security body has warned - and the combination of anonymisation technologies, mobile devices, and social media...
-
 127Malware
127MalwareCan’t keep a bad man down: “Shylock” Trojan returns to attack U.S. banks
A stealthy banking Trojan known as Caphaw or Shylock has resurfaced - and is attacking customers of 24 American banks. It's armed...
-

 214Privacy
214PrivacyHIPAA 9/23 compliance deadline looms as breaches continue
This is a quick reminder that the September 23 deadline for compliance with the new HIPAA regulations is rapidly approaching. Organizations that...
-
 205News
205NewsMaDleets TeaM defaces official Pakistani Military and Bar Council Websites
Pakistani hacktavists from MaDleets TeaM have defaced the official websites of Pakistan Military Engineer Services (mes.gov.pk), Pakistan Bar Council (pakistanbarcouncil.org) and Secretariat...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




