Featured News
-

 1.3KMalware
1.3KMalwareUkraine War Themed Files Become the Lure of Choice for a Wide Range of Hackers
A growing number of threat actors are using the ongoing Russo-Ukrainian war as a lure in various phishing and malware campaigns, even...
-

 3.8KLeaks
3.8KLeaksA Step-By-Step Guide on How To Remove Ransomware?
Prevention is always recommended when it comes to ransomware infections. Nevertheless, there are numerous ways to recover lost data whenever a device...
-

 3.9KMalware
3.9KMalwareAvosLocker ransomware can disable any defense solution using a legitimate Avast Anti-Rootkit driver
A report by Trend Micro details the detection of various samples of the AvosLocker ransomware capable of using legitimate files to disable...
-
 3.9KVulnerabilities
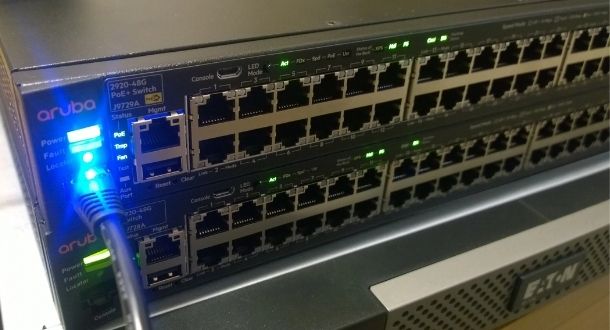
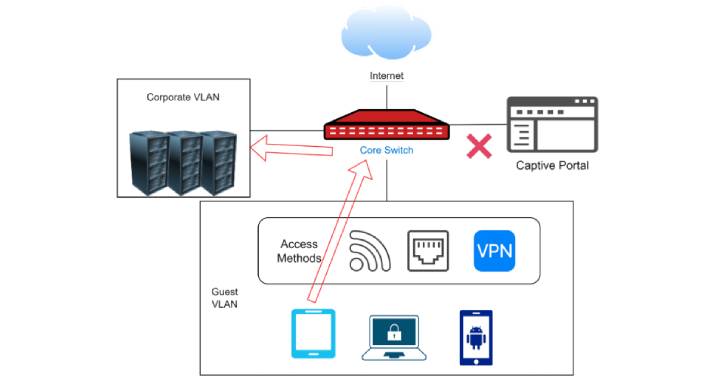
3.9KVulnerabilitiesThousands of airports, hospitals and hotels affected by critical vulnerabilities in Aruba and Avaya switches
Five critical remote code execution (RCE) vulnerabilities have been confirmed to be found in millions of Aruba and Avaya devices whose exploitation...
-

 5.1KData Security
5.1KData SecurityHow Narcotics and Economic Crime Investigations (NECI) Task Force arrested multiple dark web drug vendors?
The Narcotics and Economic Crimes Investigations (NECI) Task Force, a specialized unit of California police, has expanded its list of names of...
-
 1.2KVulnerabilities
1.2KVulnerabilitiesCritical TLStorm 2.0 Bugs Affect Widely-Used Aruba and Avaya Network Switches
Cybersecurity researchers have detailed as many as five severe security flaws in the implementation of TLS protocol in several models of Aruba...
-

 1.6KMalware
1.6KMalwareExperts Analyze Conti and Hive Ransomware Gangs’ Chats With Their Victims
An analysis of four months of chat logs spanning more than 40 conversations between the operators of Conti and Hive ransomware and...
-
 1.3KMalware
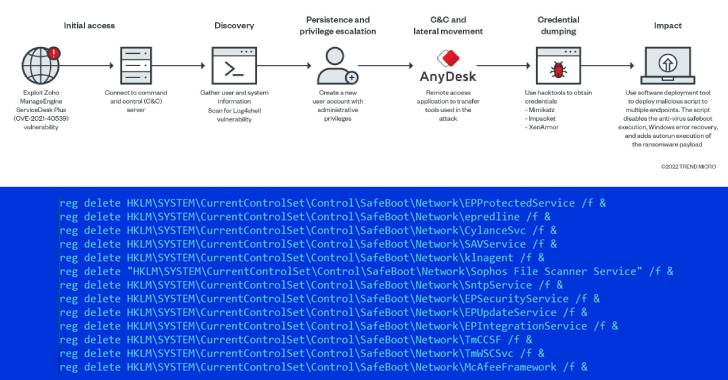
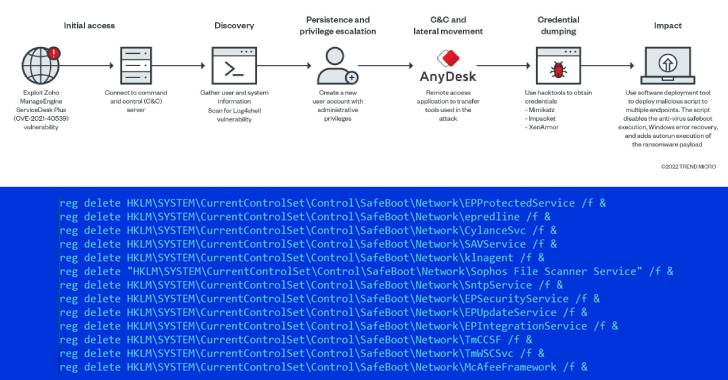
1.3KMalwareAvosLocker Ransomware Variant Using New Trick to Disable Antivirus Protection
Cybersecurity researchers have disclosed a new variant of the AvosLocker ransomware that disables antivirus solutions to evade detection after breaching target networks...
-
 1.4KMalware
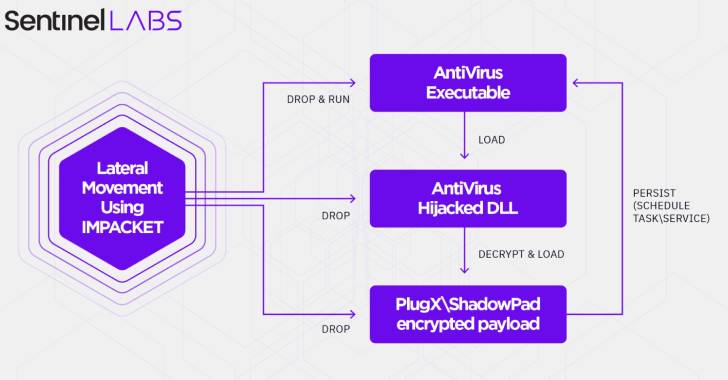
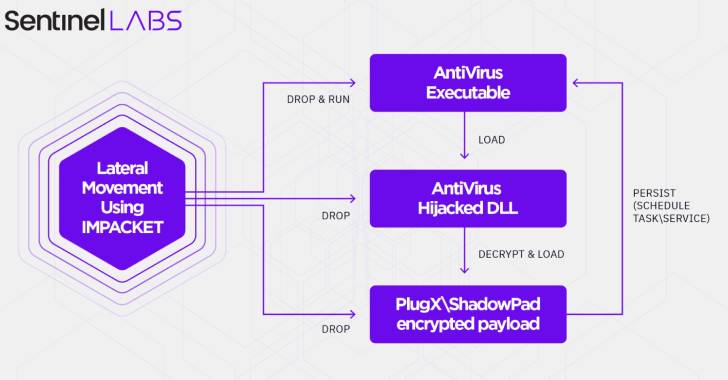
1.4KMalwareChinese Hackers Caught Exploiting Popular Antivirus Products to Target Telecom Sector
A Chinese-aligned cyberespionage group has been observed striking the telecommunication sector in Central Asia with versions of malware such as ShadowPad and...
-
 3.3KMalware
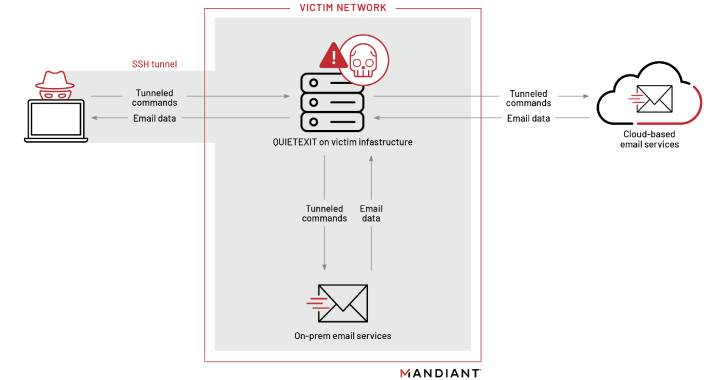
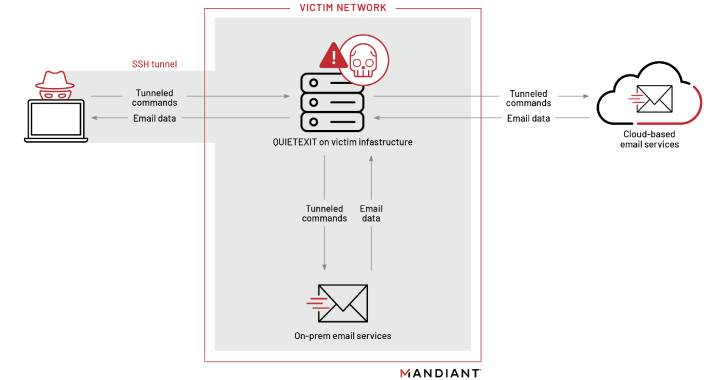
3.3KMalwareNew Hacker Group Pursuing Corporate Employees Focused on Mergers and Acquisitions
A newly discovered suspected espionage threat actor has been targeting employees focusing on mergers and acquisitions as well as large corporate transactions...
-

 983Incidents
983IncidentsYou can earn 1.5 million dollar by finding vulnerabilities in Android 13 Beta
Google has decided to temporarily increase payments in its vulnerability bounty program for those researchers who submit reports of flaws in Android...
-

 5.0KData Security
5.0KData SecurityHow a techie guy scammed the US Department of Defense and stole $23 million using a simple phishing email
The U.S. Department of Justice (DOJ) announced that Sercan Oyuntur, a 40-year-old Californian citizen, was convicted of six counts related to a...
-

 2.2KCyber Attack
2.2KCyber AttackChinese “Override Panda” Hackers Resurface With New Espionage Attacks
A Chinese state-sponsored espionage group known as Override Panda has resurfaced in recent weeks with a new phishing attack with the goal...
-

 4.5KVulnerabilities
4.5KVulnerabilitiesWhich Hole to Plug First? Solving Chronic Vulnerability Patching Overload
According to folklore, witches were able to sail in a sieve, a strainer with holes in the bottom. Unfortunately, witches don’t work...
-
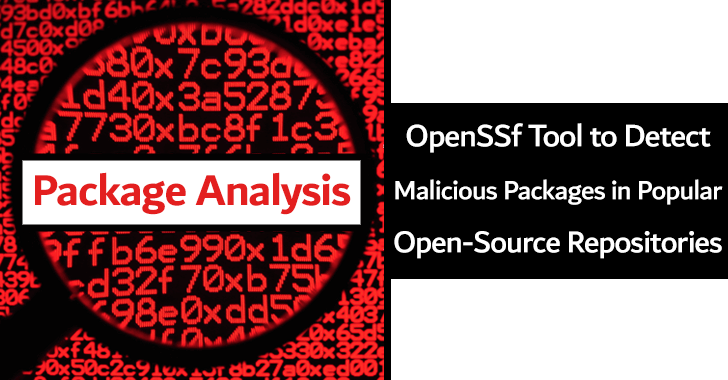
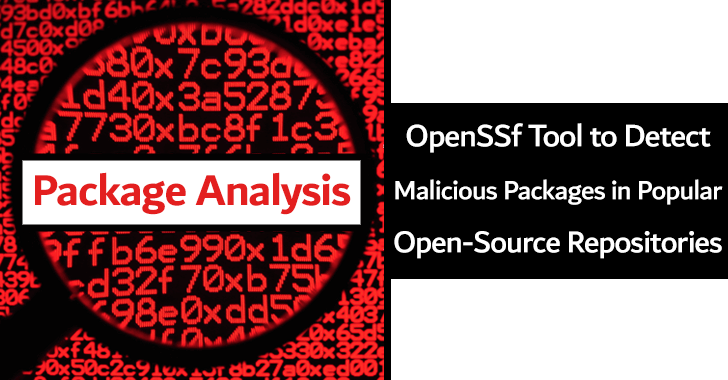 4.7KMalware
4.7KMalwarePackage Analysis – OpenSSf Tool to Detect Malicious Packages in Popular Open-Source Repositories
A prototype version of the Package Analysis tool has been recently released by the Open Source Security Foundation (OpenSSF), and it is...
-

 2.2KCyber Attack
2.2KCyber AttackRussian Hackers Targeting Diplomatic Entities in Europe, Americas, and Asia
A Russian state-sponsored threat actor has been observed targeting diplomatic and government entities as part of a series of phishing campaigns commencing...
-
 3.1KVulnerabilities
3.1KVulnerabilitiesCVE-2022-0543: Vulnerability in Redis with 10/10 CVSS score. Thousands of Linux servers affected
A couple of months ago Ubuntu and Debian officials published security advisories related to CVE-2022-0543, a vulnerability derived from a bug in...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesZero-day vulnerabilities in Netatalk affect NAS products from Synology, QNAP and Western Digital. Protect your storage solutions before they’re encrypted with ransomware
Several manufacturers of network-attached storage (NAS) solutions have alerted their customers to the detection of critical vulnerabilities in Netatalk. The exploitation of...
-

 2.6KCyber Attack
2.6KCyber AttackMicrosoft Documents Over 200 Cyberattacks by Russia Against Ukraine
At least six different Russia-aligned actors launched no less than 237 cyberattacks against Ukraine from February 23 to April 8, including 38...
-

 2.3KData Breach
2.3KData BreachIndian Govt Orders Organizations to Report Security Breaches Within 6 Hours to CERT-In
India’s computer and emergency response team, CERT-In, on Thursday published new guidelines that require service providers, intermediaries, data centers, and government entities...
The Latest
-
 Malware
MalwareNorth Korean Hackers Target Brazilian Fintech with Sophisticated Phishing Tactics
-
 Vulnerabilities
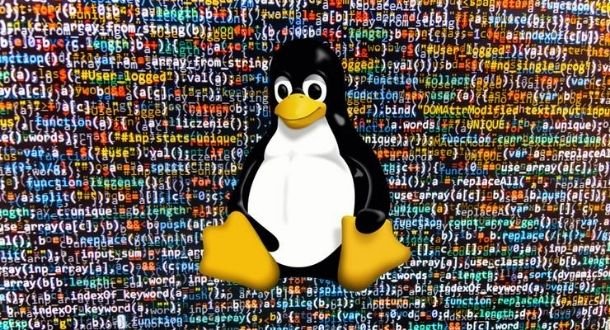
VulnerabilitiesNew Attack Technique ‘Sleepy Pickle’ Targets Machine Learning Models
-
 Malware
MalwareArid Viper Launches Mobile Espionage Campaign with AridSpy Malware
-
 Malware
MalwarePakistan-linked Malware Campaign Evolves to Target Windows, Android, and macOS
-
 Vulnerabilities
VulnerabilitiesGoogle Warns of Pixel Firmware Security Flaw Exploited as Zero-Day
-
 Malware
MalwareNew Cross-Platform Malware ‘Noodle RAT’ Targets Windows and Linux Systems
-
 Malware
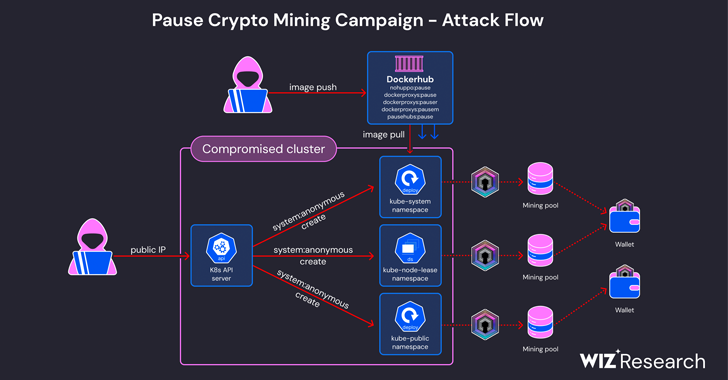
MalwareCryptojacking Campaign Targets Misconfigured Kubernetes Clusters
-
 Malware
MalwareBlack Basta Ransomware May Have Exploited MS Windows Zero-Day Flaw
-
 Malware
MalwareNew Phishing Campaign Deploys WARMCOOKIE Backdoor Targeting Job Seekers
-
 Malware
MalwareChina-Backed Hackers Exploit Fortinet Flaw, Infecting 20,000 Systems Globally
-
 Vulnerabilities
VulnerabilitiesMicrosoft Issues Patches for 51 Flaws, Including Critical MSMQ Vulnerability
-
 Malware
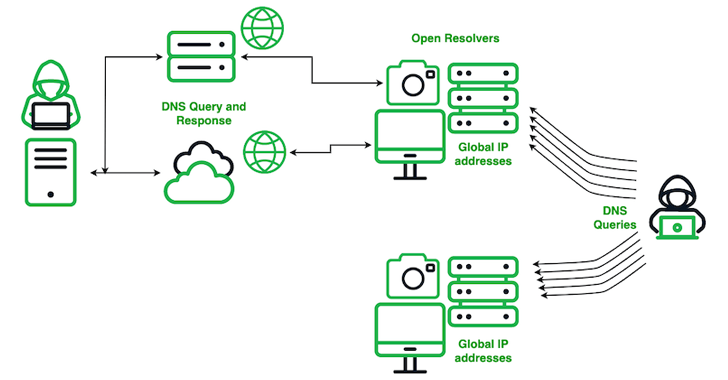
MalwareChinese Actor SecShow Conducts Massive DNS Probing on Global Scale
-
 Malware
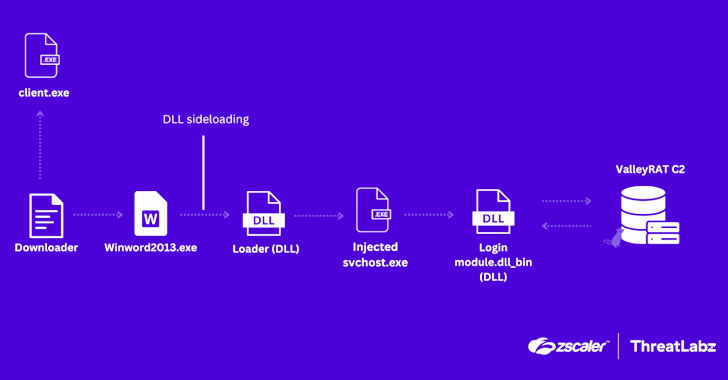
MalwareChina-Linked ValleyRAT Malware Resurfaces with Advanced Data Theft Tactics
-
 Malware
MalwareSnowflake Breach Exposes 165 Customers’ Data in Ongoing Extortion Campaign
-
 Malware
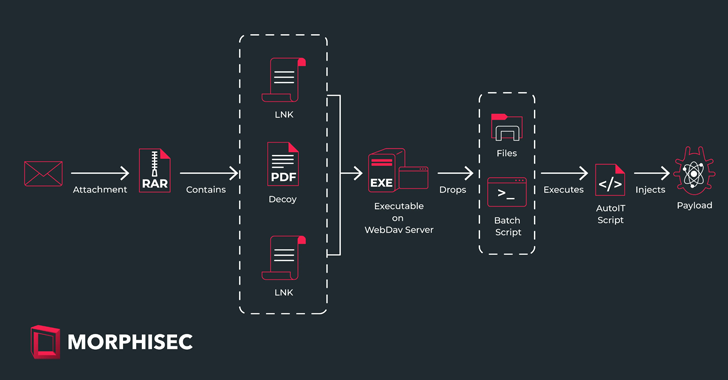
MalwareSticky Werewolf Expands Cyber Attack Targets in Russia and Belarus
-
 Vulnerabilities
VulnerabilitiesNew PHP Vulnerability Exposes Windows Servers to Remote Code Execution
-
 Malware
MalwareMicrosoft Revamps Controversial AI-Powered Recall Feature Amid Privacy Concerns
-
 Cyber Attack
Cyber AttackUltimate Cyber Hygiene Guide: Learn How to Simplify Your Security Efforts
-
 Malware
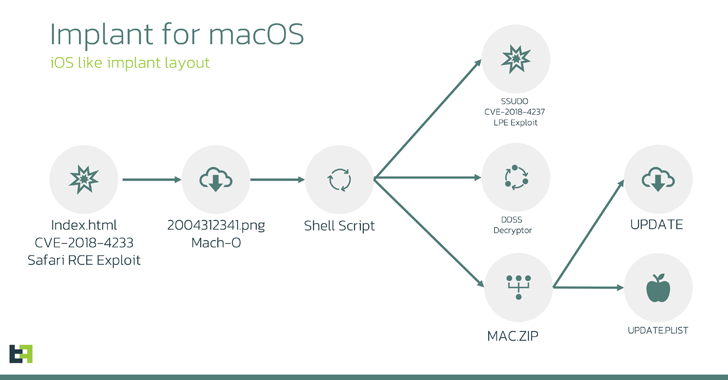
MalwareLightSpy Spyware’s macOS Variant Found with Advanced Surveillance Capabilities
-
 Data Breach
Data BreachFBI Distributes 7,000 LockBit Ransomware Decryption Keys to Help Victims




