Featured News
-

 195Surveillance
195SurveillanceNew Surveillance System Tracks Every Moving Object In An Entire City
An ultimate level of spy has been manufactured by the BAE systems as part of their contract with DAPRA (Defence Advanced Research Project Agency)....
-
 463Privacy
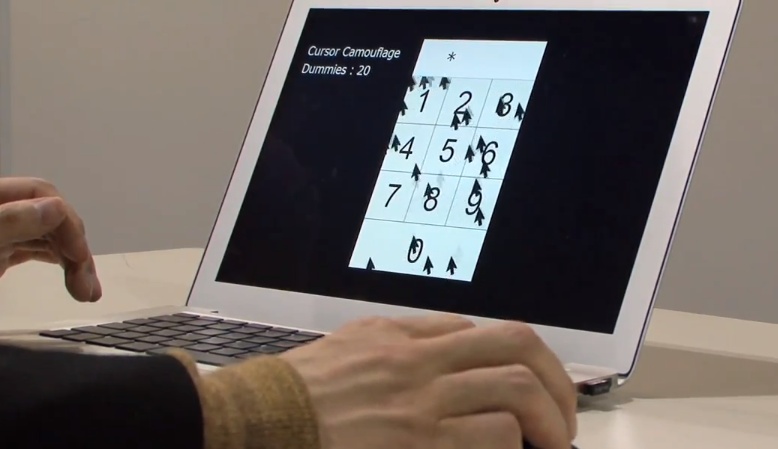
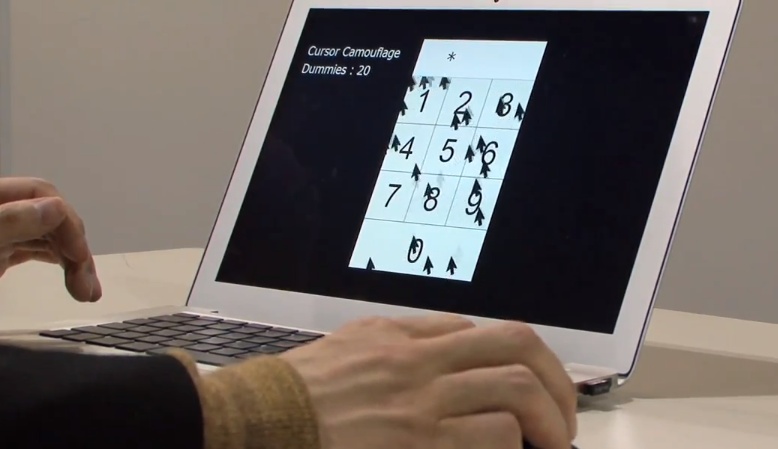
463PrivacyMulti‑cursor password system unveiled by Japanese researchers
A prototype multi-cursor system designed to improve the security of on screen password entry has been posted onto DigInfo, the Tokyo based...
-
 308News
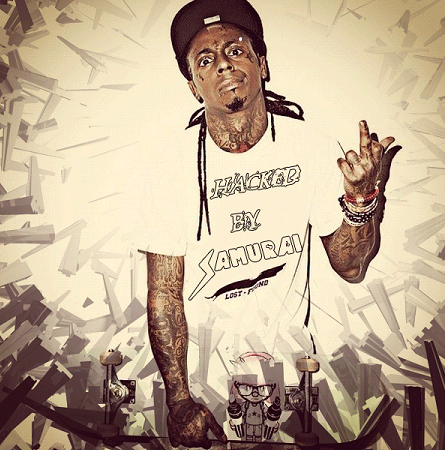
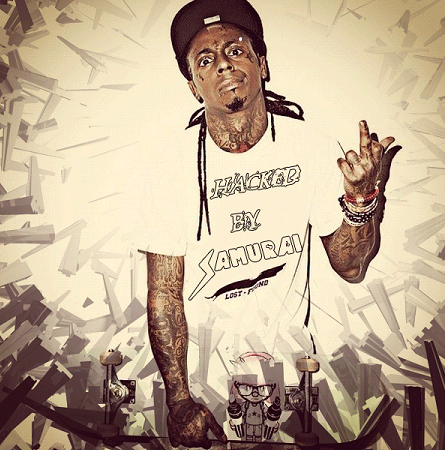
308NewsOfficial ACER Electronics Service Center Thailand Website Hacked by Samurai of TurkHackTeam
The official website of ACER electronic’s service center for Thailand has been hacked and partially defaced by Samurai of TurkHackTeam. The hacker contacted me today...
-

 190News
190News#OpIsrael: 25 Israeli Websites hacked and Defaced by Local Army Crew
A group of Malaysian hackers from Local Army Crew have collectively hacked and defaced 25 Israeli websites in support of Palestine. A...
-

 92Cyber Crime
92Cyber CrimeHeartless Mother Tries to Sell Her Kids on Facebook
A young heartless mum has been arrested for an attempt to sell her Children on Facebook to bail out her husband from...
-

 178Geek
178GeekHacked Russian Car that can be driven via #iPad [Video Included]
A group of Russian motorists from Tula Oblast have modified an old Opel Vectra into a remotely controlled automobile that can be driven through...
-

 197News
197NewsIndian Defence Organisation DRDO Servers Hacked, China among the Suspects
The official website of one of India’s most high profile defense organization, Defense Research and Development Organization (DRDO) (www.drdo.gov.in) was hacked and breached...
-
 111Scams
111ScamsPhishbait: not so much a Smile as a rictus
Below, you can see the textual part of a bank phishing email I received today (it also contained a Smile logo, which...
-
 212Data Security
212Data SecurityDownload now Kali Linux (BackTrack 6) [Download Link & Password in the article]
Earlier I wrote about BackTrack renaming itself as Kali Linux or BackTrack 6 will be available for download soon, today is the day...
-

 122Malware
122MalwareHow Theola malware uses a Chrome plugin for banking fraud
A deep dive into Win32/Theola, one of the most malicious components of the notorious bootkit family, Win32/Mebroot.FX. Theola uses malicious Chrome browser...
-

 191Data Security
191Data SecurityFacebook Black Malware Spreading Rapidly on Facebook
A new malware spreading rapidly on Facebook bluffing users into clicking an app link that supposedly allows Fake Facebook Black template replacing...
-

 197Data Security
197Data SecurityMircosoft to Fix Some Critical Vulnerabilities by Tuesday
Microsoft has found seven vulnerabilities in its programs and has deemed of them critical. The critical are so serious that officials have...
-
 211News
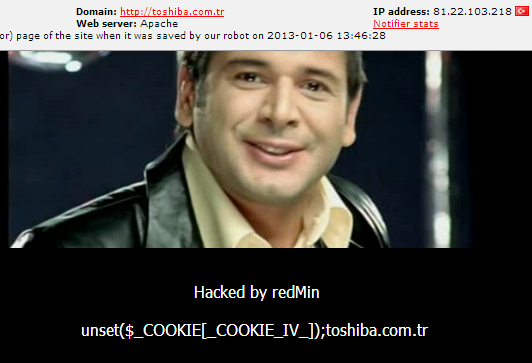
211NewsOfficial Toshiba Turkey Website Hacked & Defaced by redMin
A hacker going with the handle of redMin has hacked and defaced the official website of Toshiba Corporation a Japanese multinational engineering and electronics...
-

 182Cyber Events
182Cyber EventsUS warns, but, China agrees to talk on Cyber Security
An official at White House has warned China to take “serious steps” in tackling cyber-crimes originating from its cyber space, as it has...
-

 106Hacking
106HackingTop celebrities and government officials financial details leaked online
The Associated Press reports that celebrities, including ashton Kutcher and Kim Kardashian, along with top government officials have had private financial information...
-

 108Cyber Crime
108Cyber CrimeSingapore joins fight against digital crime with new Cyber Security Lab
Reports from Asia say that Singapore is to open a new Cyber Security Lab in a bid to combat criminal hacking by...
-

 102News
102NewsAnonymous Hackers Leak Financial Records of US Vice President Joe Biden, Jay-Z, Beyoncé other High Profile Figures
Anonymous Hackers have published personal financial records of some high profile celebrities, musicians and politician like US Vice President Joe Biden, Attorney General Eric...
-
 282News
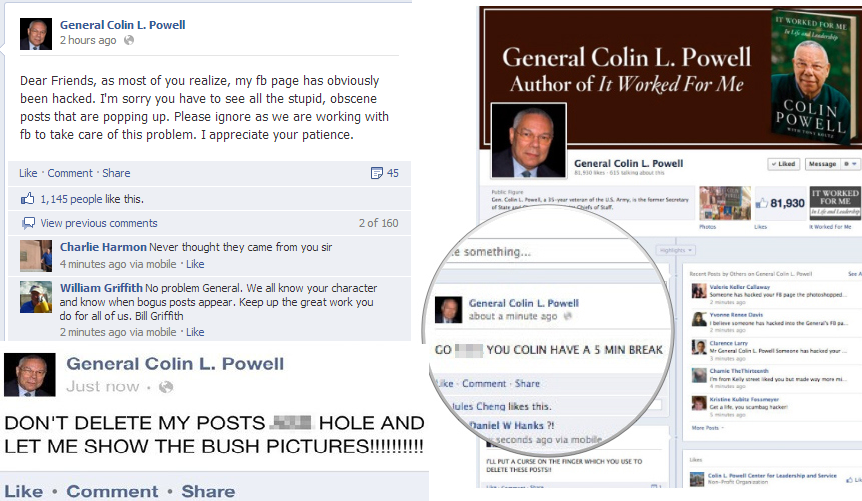
282NewsGen. Colin Powell’s Facebook Page Hacked by Guccifer, spammed with anti-Bush Status
The official Facebook page of former Secretary of State and a retired four-star general in the United States Army was hacked few hours ago, resulting...
-
 307News
307NewsSerbian Students Hack Billboard, Display Advert in PirateBay’s support [Video Included]
A group of Serbian students penetrated into the security of a billboard advertisement which stands tall at a crowded and much eminent location...
-
 137Mobile Security
137Mobile SecurityRogue developers hiding Android malware in apps on Google Play
Respected security blogger Brian Krebs reports that an “explosion in Android malware” is being fuelled by a growing market for hijacked of...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




