Featured News
-

 227How To
227How ToTurn Your Desktop into a Touch Screen!!!
Wonder, if you can change your desktop screen into a touch screen with minimal investment? Well, it is possible. Your desktop screen...
-

 439How To
439How ToHow to Undo Sent Emails from Gmail Tutorial
Do you find yourself in trouble when you send a mail to a wrong recipient and believe the user might use the...
-

 345Data Security
345Data SecurityFacebook Graph Search is the best tool for phishing attacks
Facebook shocked the world by unveiling its new Graph Search. Where users are waiting to test the new search features, the hackers are anxiously waiting to...
-

 199News
199NewsNew Phishing Attacks on MSN/Hotmail Users with Same Old Way
Its a new year, people with new ideas, new plans regarding all phases of life but there are some people or rather...
-

 249News
249News200 Indian Websites Hacked by Pakistani Hackers
Two Pakistani hackers going with the handles of Um3r-H & Mr Max have hacked and defaced 200 Indian websites a while ago. The...
-

 123News
123News47 Greek Government Websites Defaced by !nf3rN.4lL
One of the most famous and dangerous hacker going with the handle of !nf3rN.4lL has hacked and defaced 47 Greek government owned websites today. ...
-

 295News
295NewsChinese Embassy Information Site Hacked and Defaced by Nesta
A hacker going with the handle of Nesta from Indonesia has hacked and defaced the Chinese embassy and visa information site (chinese-embassy.com). ...
-

 259Geek
259GeekRun Android Applications on PC via Android SDK Manager
Do you wish to run Android application or games but don’t have a Smartphone to do it? Well, we would in this...
-

 295News
295NewsProximus Security Website Hacked, 20,000 Emails & Passwords Leaked
@JokerCracker keeping up with his work has now hacked into the website of Proximus Security, a security products & Service providing company and left with...
-
 283News
283NewsGovernment of Philippines & 115 other sites hacked by AnonGhost
The well know hacker AnonGhost has hacked and defaced the official website of Philippine’s Lanuza municipality (lanuza.gov.ph) and 115 other websites from different...
-
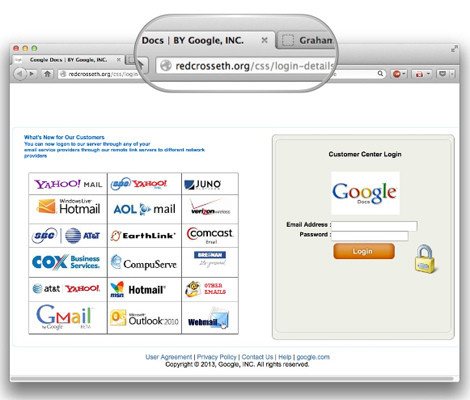
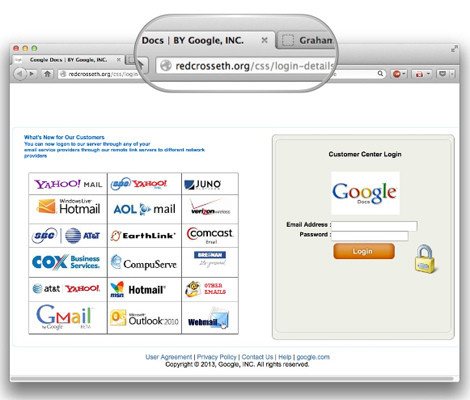 291News
291NewsPhishing Attempts to Hack Google Passwords via Hacked Red Cross website
The official website of Red Cross Ethiopia has been compromised and currently under hackers who have been trying phishing attacks on user...
-
 213News
213News#Op_Egypt: Ministry of Information & Cabinet of Ministers Websites Taken Down by Anonymous
Just when things were looking down, the hackavist group Anonymous hit back the Egyptian government by taking down three of its high profile websites....
-

 265News
265News87 Canadian Websites Hacked by @rooterror
A hacker going with the Twitter handle @rooterror has hacked and defaced 87 Canadian based websites. The hack was announced by @rooterror himself on...
-

 239News
239NewsSony Music Mexico Website Hacked & Defaced by DiE_AucH
The official website of Sony Music for Mexico (sonymusic.com.mx) has been hacked and defaced by a hacker going with the handle of DiE_AucH, along...
-
 137News
137NewsNepal’s Ministry of Health, Education & Poverty Alleviation Defaced by The Crows Crew
A hacking group The Crows Crew from Indonesia has hacked and defaced 3 official websites of Nepal’s Ministry of Health, Ministry of Education...
-

 339Data Security
339Data SecurityVulnerability of Oil and Gas Infrastructure Drives Security Investments
Gas and oil markets are one of the most profitable markets in the world. The projection in future for these markets looks...
-

 169How To
169How To5 physical security tips for protecting your digital devices
As we read earlier this week, the chances that one or more of your digital devices may get stolen are uncomfortably high....
-

 281Geek
281GeekGoogle Denies Killing Donkey! Image Included
Reports on social media suggest that Google Street View car ran over a donkey due to which it died on the spot, but...
-
 188Cyber Crime
188Cyber CrimeBotnet Threat: Over a Million Chinese Smartphones Infected with Trojan Horse Malware
In a shocking news reported by Chinese media, the security researchers have reveled that there are more than a million smartphones in...
-

 377Geek
377GeekMark Zuckerberg Presents Facebook Search Engine aka Graph Search
Facebook has announced its very own search engine in an event organized by the Facebook officials to announce its new fascinating product....
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




