Featured News
-

 3.5KData Breach
3.5KData BreachHands-On Review: SASE-based XDR from Cato Networks
Companies are engaged in a seemingly endless cat-and-mouse game when it comes to cybersecurity and cyber threats. As organizations put up one...
-

 2.1KMalware
2.1KMalwarePegasus Spyware Targeted iPhones of Journalists and Activists in Jordan
The iPhones belonging to nearly three dozen journalists, activists, human rights lawyers, and civil society members in Jordan have been targeted with...
-

 1.5KMalware
1.5KMalwareNew Mispadu Banking Trojan Exploiting Windows SmartScreen Flaw
The threat actors behind the Mispadu banking Trojan have become the latest to exploit a now-patched Windows SmartScreen security bypass flaw to...
-
 5.2KCyber Attack
5.2KCyber AttackU.S. Sanctions 6 Iranian Officials for Critical Infrastructure Cyber Attacks
The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) announced sanctions against six officials associated with the Iranian intelligence agency for...
-

 2.5KCyber Attack
2.5KCyber AttackAnyDesk Hacked: Popular Remote Desktop Software Mandates Password Reset
Remote desktop software maker AnyDesk disclosed on Friday that it suffered a cyber attack that led to a compromise of its production...
-

 2.6KMalware
2.6KMalwareDirtyMoe Malware Infects 2,000+ Ukrainian Computers for DDoS and Cryptojacking
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned that more than 2,000 computers in the country have been infected by...
-

 2.4KData Breach
2.4KData BreachFormer CIA Engineer Sentenced to 40 Years for Leaking Classified Documents
A former software engineer with the U.S. Central Intelligence Agency (CIA) has been sentenced to 40 years in prison by the Southern...
-

 1.9KMalware
1.9KMalwareCloudzy Elevates Cybersecurity: Integrating Insights from Recorded Future to Revolutionize Cloud Security
Cloudzy, a prominent cloud infrastructure provider, proudly announces a significant enhancement in its cybersecurity landscape. This breakthrough has been achieved through a...
-

 419Malware
419MalwareINTERPOL Arrests 31 in Global Operation, Identifies 1,900+ Ransomware-Linked IPs
An INTERPOL-led collaborative operation targeting phishing, banking malware, and ransomware attacks has led to the identification of 1,300 suspicious IP addresses and...
-

 2.5KData Breach
2.5KData BreachCloudflare Breach: Nation-State Hackers Access Source Code and Internal Docs
Cloudflare has revealed that it was the target of a likely nation-state attack in which the threat actor leveraged stolen credentials to...
-
 3.2KData Security
3.2KData SecurityHacking Debian, Ubuntu, Redhat& Fedora servers using a single vulnerability in 2024
The recent discovery of a significant flaw in the GNU C Library (glibc), a fundamental component of major Linux distributions, has raised...
-

 2.9KVulnerabilities
2.9KVulnerabilitiesFritzFrog Returns with Log4Shell and PwnKit, Spreading Malware Inside Your Network
The threat actor behind a peer-to-peer (P2P) botnet known as FritzFrog has made a return with a new variant that leverages the...
-

 190Cyber Attack
190Cyber AttackU.S. Feds Shut Down China-Linked “KV-Botnet” Targeting SOHO Routers
The U.S. government on Wednesday said it took steps to neutralize a botnet comprising hundreds of U.S.-based small office and home office...
-

 3.6KMalware
3.6KMalwareHeadCrab 2.0 Goes Fileless, Targeting Redis Servers for Crypto Mining
Cybersecurity researchers have detailed an updated version of the malware HeadCrab that’s known to target Redis database servers across the world since...
-
 2.0KMalware
2.0KMalwareWarning: New Malware Emerges in Attacks Exploiting Ivanti VPN Vulnerabilities
Google-owned Mandiant said it identified new malware employed by a China-nexus espionage threat actor known as UNC5221 and other threat groups during...
-
 1.1KVulnerabilities
1.1KVulnerabilitiesCISA Warns of Active Exploitation Apple iOS and macOS Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added a high-severity flaw impacting iOS, iPadOS, macOS, tvOS, and watchOS to...
-

 943Vulnerabilities
943VulnerabilitiesAlert: Ivanti Discloses 2 New Zero-Day Flaws, One Under Active Exploitation
Ivanti is alerting of two new high-severity flaws in its Connect Secure and Policy Secure products, one of which is said to...
-
 3.7KMalware
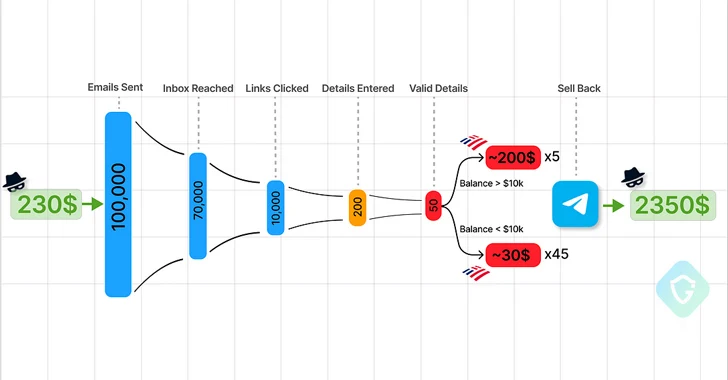
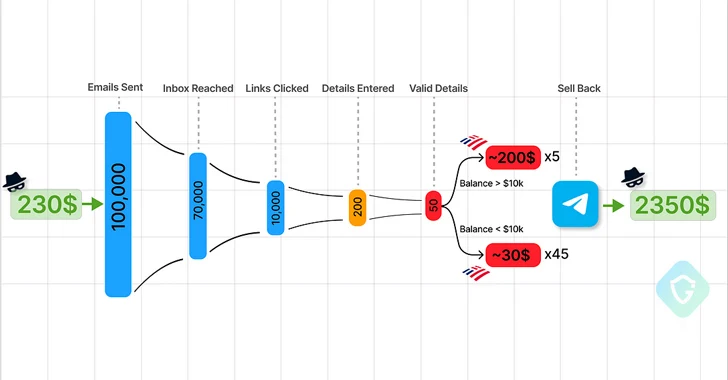
3.7KMalwareTelegram Marketplaces Fuel Phishing Attacks with Easy-to-Use Kits and Malware
Cybersecurity researchers are calling attention to the “democratization” of the phishing ecosystem owing to the emergence of Telegram as an epicenter for...
-

 2.4KData Breach
2.4KData BreachThe SEC Won’t Let CISOs Be: Understanding New SaaS Cybersecurity Rules
The SEC isn’t giving SaaS a free pass. Applicable public companies, known as “registrants,” are now subject to cyber incident disclosure and...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesHackers Exploiting Ivanti VPN Flaws to Deploy KrustyLoader Malware
A pair of recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) virtual private network (VPN) devices have been exploited to deliver...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




