Featured News
-

 1.9KMalware
1.9KMalwareCloudzy Elevates Cybersecurity: Integrating Insights from Recorded Future to Revolutionize Cloud Security
Cloudzy, a prominent cloud infrastructure provider, proudly announces a significant enhancement in its cybersecurity landscape. This breakthrough has been achieved through a...
-

 418Malware
418MalwareINTERPOL Arrests 31 in Global Operation, Identifies 1,900+ Ransomware-Linked IPs
An INTERPOL-led collaborative operation targeting phishing, banking malware, and ransomware attacks has led to the identification of 1,300 suspicious IP addresses and...
-

 2.5KData Breach
2.5KData BreachCloudflare Breach: Nation-State Hackers Access Source Code and Internal Docs
Cloudflare has revealed that it was the target of a likely nation-state attack in which the threat actor leveraged stolen credentials to...
-
 3.2KData Security
3.2KData SecurityHacking Debian, Ubuntu, Redhat& Fedora servers using a single vulnerability in 2024
The recent discovery of a significant flaw in the GNU C Library (glibc), a fundamental component of major Linux distributions, has raised...
-

 2.9KVulnerabilities
2.9KVulnerabilitiesFritzFrog Returns with Log4Shell and PwnKit, Spreading Malware Inside Your Network
The threat actor behind a peer-to-peer (P2P) botnet known as FritzFrog has made a return with a new variant that leverages the...
-

 190Cyber Attack
190Cyber AttackU.S. Feds Shut Down China-Linked “KV-Botnet” Targeting SOHO Routers
The U.S. government on Wednesday said it took steps to neutralize a botnet comprising hundreds of U.S.-based small office and home office...
-

 3.6KMalware
3.6KMalwareHeadCrab 2.0 Goes Fileless, Targeting Redis Servers for Crypto Mining
Cybersecurity researchers have detailed an updated version of the malware HeadCrab that’s known to target Redis database servers across the world since...
-
 2.0KMalware
2.0KMalwareWarning: New Malware Emerges in Attacks Exploiting Ivanti VPN Vulnerabilities
Google-owned Mandiant said it identified new malware employed by a China-nexus espionage threat actor known as UNC5221 and other threat groups during...
-
 1.1KVulnerabilities
1.1KVulnerabilitiesCISA Warns of Active Exploitation Apple iOS and macOS Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added a high-severity flaw impacting iOS, iPadOS, macOS, tvOS, and watchOS to...
-

 942Vulnerabilities
942VulnerabilitiesAlert: Ivanti Discloses 2 New Zero-Day Flaws, One Under Active Exploitation
Ivanti is alerting of two new high-severity flaws in its Connect Secure and Policy Secure products, one of which is said to...
-
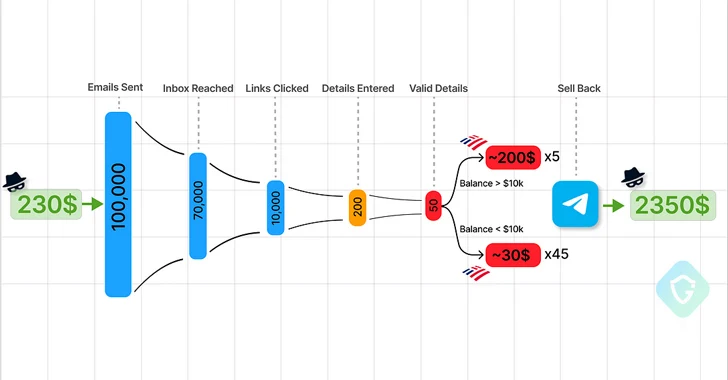
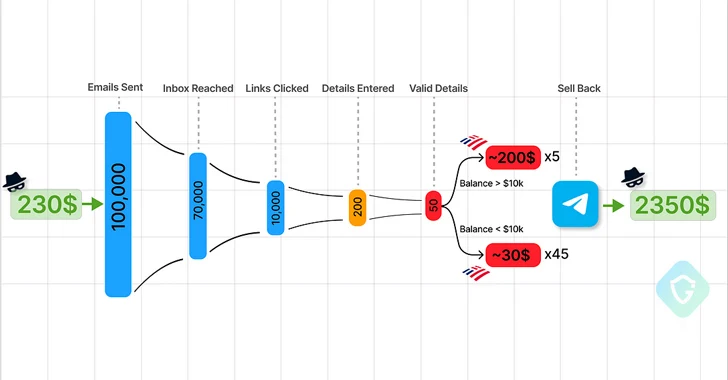 3.7KMalware
3.7KMalwareTelegram Marketplaces Fuel Phishing Attacks with Easy-to-Use Kits and Malware
Cybersecurity researchers are calling attention to the “democratization” of the phishing ecosystem owing to the emergence of Telegram as an epicenter for...
-

 2.4KData Breach
2.4KData BreachThe SEC Won’t Let CISOs Be: Understanding New SaaS Cybersecurity Rules
The SEC isn’t giving SaaS a free pass. Applicable public companies, known as “registrants,” are now subject to cyber incident disclosure and...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesHackers Exploiting Ivanti VPN Flaws to Deploy KrustyLoader Malware
A pair of recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) virtual private network (VPN) devices have been exploited to deliver...
-

 4.4KMalware
4.4KMalwareBrazilian Feds Dismantle Grandoreiro Banking Trojan, Arresting Top Operatives
A Brazilian law enforcement operation has led to the arrest of several Brazilian operators in charge of the Grandoreiro malware. The Federal...
-

 3.9KVulnerabilities
3.9KVulnerabilitiesURGENT: Upgrade GitLab – Critical Workspace Creation Flaw Allows File Overwrite
GitLab once again released fixes to address a critical security flaw in its Community Edition (CE) and Enterprise Edition (EE) that could...
-
 590Malware
590MalwareChina-Linked Hackers Target Myanmar’s Top Ministries with Backdoor Blitz
The China-based threat actor known as Mustang Panda is suspected to have targeted Myanmar’s Ministry of Defence and Foreign Affairs as part...
-

 549Data Breach
549Data BreachTop Security Posture Vulnerabilities Revealed
Each New Year introduces a new set of challenges and opportunities for strengthening our cybersecurity posture. It’s the nature of the field...
-

 3.3KMalware
3.3KMalwareNew ZLoader Malware Variant Surfaces with 64-bit Windows Compatibility
Threat hunters have identified a new campaign that delivers the ZLoader malware, resurfacing nearly two years after the botnet’s infrastructure was dismantled...
-
 830Vulnerabilities
830VulnerabilitiesJuniper Networks Releases Urgent Junos OS Updates for High-Severity Flaws
Juniper Networks has released out-of-band updates to address high-severity flaws in SRX Series and EX Series that could be exploited by a...
-

 689Data Security
689Data SecurityExploit code: How the New Jenkins Vulnerability Could Compromise Your Data
Recent news about a critical vulnerability in Jenkins, identified as CVE-2024-23897, has raised significant concerns in the cybersecurity community. This vulnerability has...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




