Featured News
-
 4.2KVulnerabilities
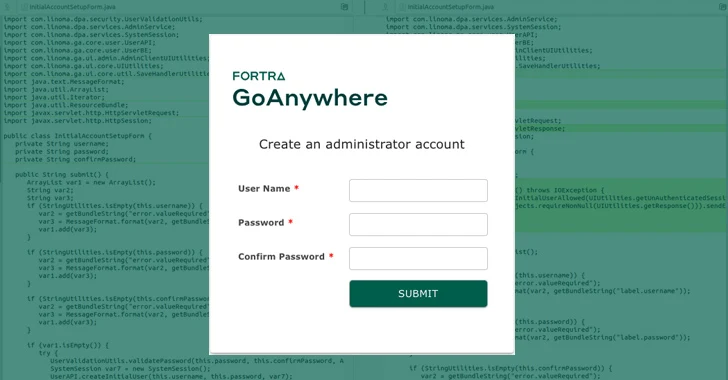
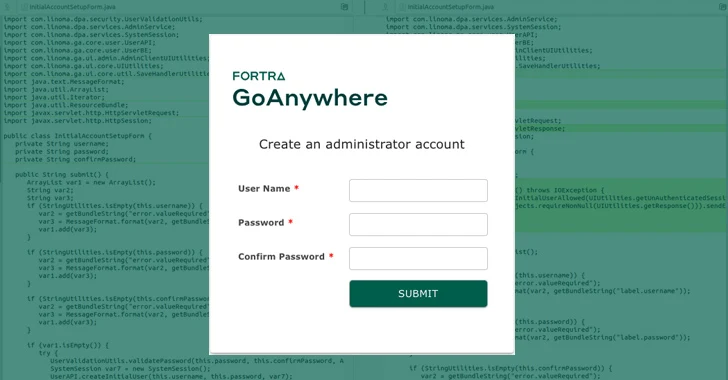
4.2KVulnerabilitiesPatch Your GoAnywhere MFT Immediately – Critical Flaw Lets Anyone Be Admin
A critical security flaw has been disclosed in Fortra’s GoAnywhere Managed File Transfer (MFT) software that could be abused to create a...
-
 4.3KMalware
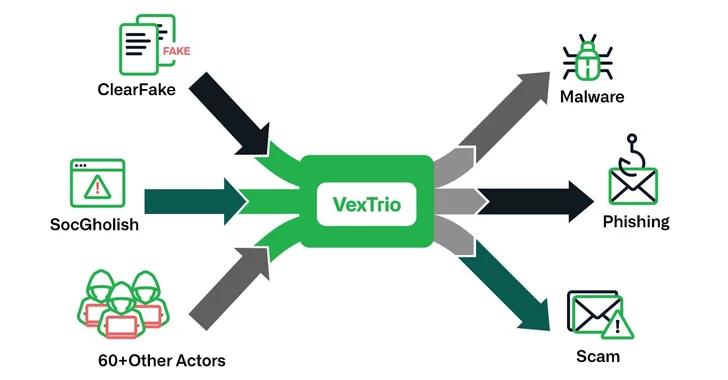
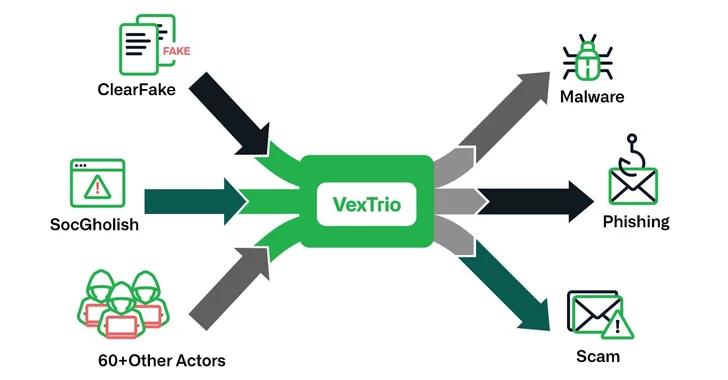
4.3KMalwareVexTrio: The Uber of Cybercrime – Brokering Malware for 60+ Affiliates
The threat actors behind ClearFake, SocGholish, and dozens of other actors have established partnerships with another entity known as VexTrio as part...
-
 3.5KMalware
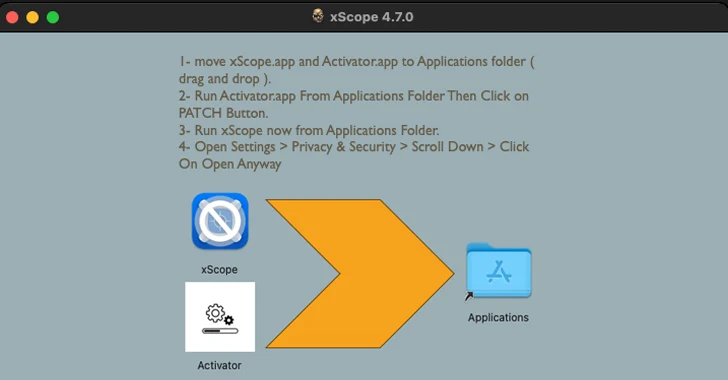
3.5KMalware“Activator” Alert: MacOS Malware Hides in Cracked Apps, Targeting Crypto Wallets
Cracked software have been observed infecting Apple macOS users with a previously undocumented stealer malware capable of harvesting system information and cryptocurrency...
-

 2.0KData Breach
2.0KData BreachBreachForums Founder Sentenced to 20 Years of Supervised Release, No Jail Time
Conor Brian Fitzpatrick has been sentenced to time served and 20 years of supervised release for his role as the creator and...
-

 1.8KVulnerabilities
1.8KVulnerabilities~40,000 Attacks in 3 Days: Critical Confluence RCE Under Active Exploitation
Malicious actors have begun to actively exploit a recently disclosed critical security flaw impacting Atlassian Confluence Data Center and Confluence Server, within...
-
 3.6KData Security
3.6KData SecurityHow to steal Windows password via Outlook email exploiting vulnerabilities in Windows Performance Analyzer (WPA) and File Explorer
Varonis Threat Labs has uncovered a significant vulnerability in Microsoft Outlook (CVE-2023-35636) that allows attackers to access NTLM v2 hashed passwords. This...
-

 886Malware
886MalwareNorth Korean Hackers Weaponize Research Lures to Deliver RokRAT Backdoor
Media organizations and high-profile experts in North Korean affairs have been at the receiving end of a new campaign orchestrated by a...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesMavenGate Attack Could Let Hackers Hijack Java and Android via Abandoned Libraries
Several public and popular libraries abandoned but still used in Java and Android applications have been found susceptible to a new software...
-

 1.6KMalware
1.6KMalwareNS-STEALER Uses Discord Bots to Exfiltrate Your Secrets from Popular Browsers
Cybersecurity researchers have discovered a new Java-based “sophisticated” information stealer that uses a Discord bot to exfiltrate sensitive data from compromised hosts....
-

 525Vulnerabilities
525Vulnerabilities52% of Serious Vulnerabilities We Find are Related to Windows 10
We analyzed 2,5 million vulnerabilities we discovered in our customer’s assets. This is what we found. Digging into the data The dataset...
-

 777Malware
777MalwareApache ActiveMQ Flaw Exploited in New Godzilla Web Shell Attacks
Cybersecurity researchers are warning of a “notable increase” in threat actor activity actively exploiting a now-patched flaw in Apache ActiveMQ to deliver...
-
 1.6KCyber Attack
1.6KCyber AttackCISA Issues Emergency Directive to Federal Agencies on Ivanti Zero-Day Exploits
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday issued an emergency directive urging Federal Civilian Executive Branch (FCEB) agencies to...
-

 2.4KMalware
2.4KMalwareInvoice Phishing Alert: TA866 Deploys WasabiSeed & Screenshotter Malware
The threat actor tracked as TA866 has resurfaced after a nine-month hiatus with a new large-volume phishing campaign to deliver known malware...
-

 4.2KMalware
4.2KMalwareExperts Warn of macOS Backdoor Hidden in Pirated Versions of Popular Software
Pirated applications targeting Apple macOS users have been observed containing a backdoor capable of granting attackers remote control to infected machines. “These...
-

 2.2KMalware
2.2KMalwareNew Docker Malware Steals CPU for Crypto & Drives Fake Website Traffic
Vulnerable Docker services are being targeted by a novel campaign in which the threat actors are deploying XMRig cryptocurrency miner as well...
-

 491Data Breach
491Data BreachMFA Spamming and Fatigue: When Security Measures Go Wrong
In today’s digital landscape, traditional password-only authentication systems have proven to be vulnerable to a wide range of cyberattacks. To safeguard critical...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesPixieFail UEFI Flaws Expose Millions of Computers to RCE, DoS, and Data Theft
Multiple security vulnerabilities have been disclosed in the TCP/IP network protocol stack of an open-source reference implementation of the Unified Extensible Firmware...
-
 3.5KMalware
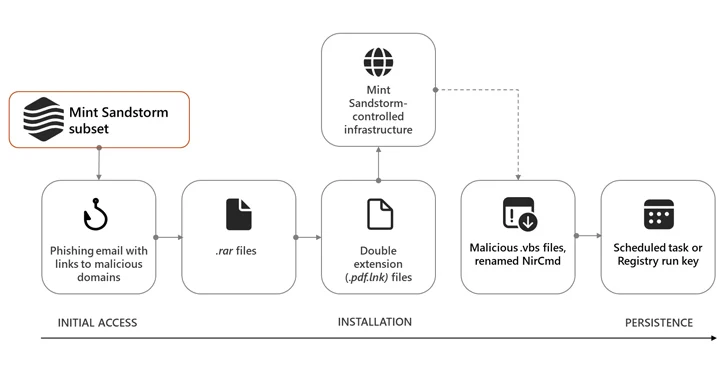
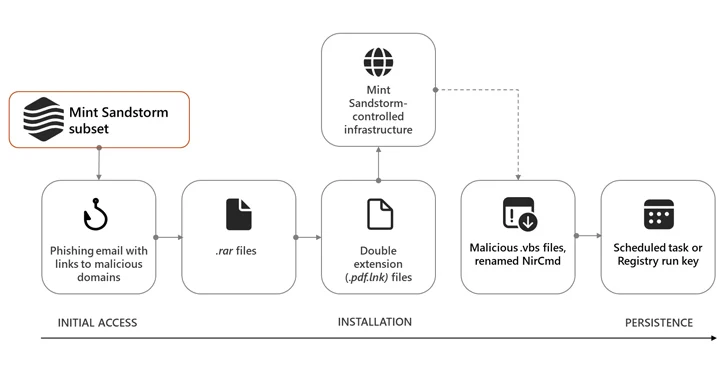
3.5KMalwareIranian Hackers Masquerade as Journalists to Spy on Israel-Hamas War Experts
High-profile individuals working on Middle Eastern affairs at universities and research organizations in Belgium, France, Gaza, Israel, the U.K., and the U.S....
-

 4.1KMalware
4.1KMalwareFeds Warn of AndroxGh0st Botnet Targeting AWS, Azure, and Office 365 Credentials
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) warned that threat actors deploying the AndroxGh0st...
-
 1.4KVulnerabilities
1.4KVulnerabilitiesGoogle Chrome Browser Zero-Day Vulnerability Exploited in Wild – Emergency Patch!
Google Chrome has released its stable channel update version 20.0.6099.234 for Mac, 120.0.6099.224 for Linux, and 120.0.6099.224/225 for Windows. However, Google stated...
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan




