Featured News
-

 2.2KLeaks
2.2KLeaksHow To Access Your Photos On iCloud
iCloud can be an easy and secure way to back up photos and videos, but accessing those files across devices may prove...
-

 3.3KLeaks
3.3KLeaksHow to See Who Blocked You on Facebook
If you suspect someone has blocked you on Facebook, various methods exist to investigate their actions. One option would be searching for...
-
 1.2KLeaks
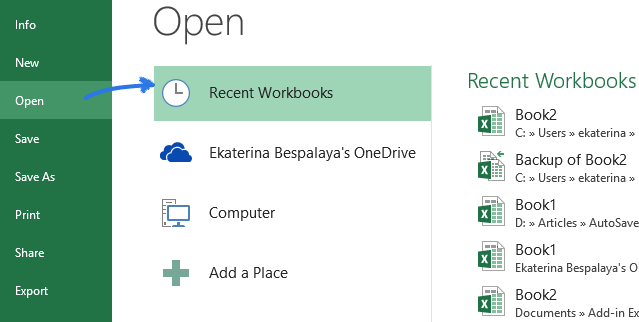
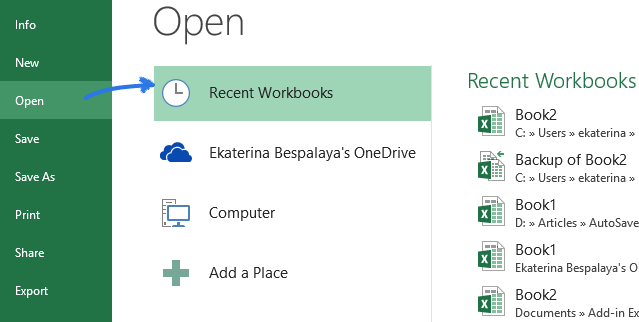
1.2KLeaksHow to Recover an Unsaved Excel File
If your Excel file was left unsaved by accident, don’t fret – Microsoft understands mistakes happen and provides built-in functionality to help...
-

 818Vulnerabilities
818VulnerabilitiesNew PoC Exploit for Apache OfBiz Vulnerability Poses Risk to ERP Systems
Cybersecurity researchers have developed a proof-of-concept (PoC) code that exploits a recently disclosed critical flaw in the Apache OfBiz open-source Enterprise Resource...
-
 533Malware
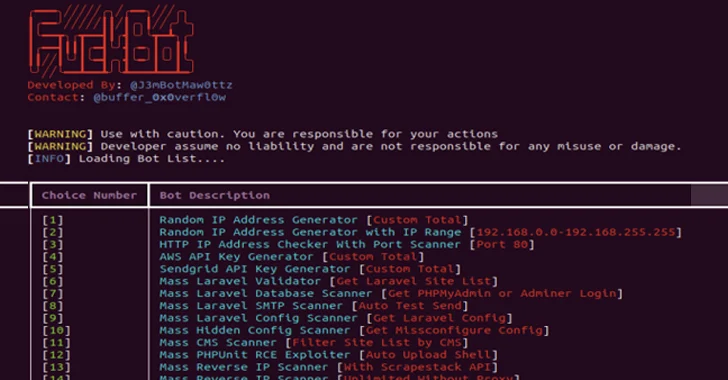
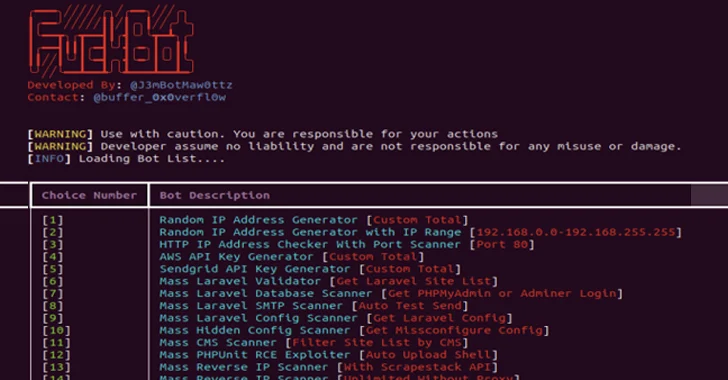
533MalwareNew Python-based FBot Hacking Toolkit Aims at Cloud and SaaS Platforms
A new Python-based hacking tool called FBot has been uncovered targeting web servers, cloud services, content management systems (CMS), and SaaS platforms...
-

 2.4KData Breach
2.4KData BreachThere is a Ransomware Armageddon Coming for Us All
Generative AI will enable anyone to launch sophisticated phishing attacks that only Next-generation MFA devices can stop The least surprising headline from...
-
 4.1KMalware
4.1KMalwareAtomic Stealer Gets an Upgrade – Targeting Mac Users with Encrypted Payload
Cybersecurity researchers have identified an updated version of a macOS information stealer called Atomic (or AMOS), indicating that the threat actors behind...
-
 230Vulnerabilities
230VulnerabilitiesCisco Fixes High-Risk Vulnerability Impacting Unity Connection Software
Cisco has released software updates to address a critical security flaw impacting Unity Connection that could permit an adversary to execute arbitrary...
-

 1.1KMalware
1.1KMalwareInside the Scam: How Ransomware Gangs Fool You with Data Deletion Lies!
Recently, there has been an emergence of a new scam targeting victims of ransomware attacks. This scam involves individuals or groups posing...
-

 2.3KMalware
2.3KMalwareNoaBot: Latest Mirai-Based Botnet Targeting SSH Servers for Crypto Mining
A new Mirai-based botnet called NoaBot is being used by threat actors as part of a crypto mining campaign since the beginning...
-

 1.3KData Breach
1.3KData BreachGetting off the Attack Surface Hamster Wheel: Identity Can Help
IT professionals have developed a sophisticated understanding of the enterprise attack surface – what it is, how to quantify it and how...
-
 3.9KMalware
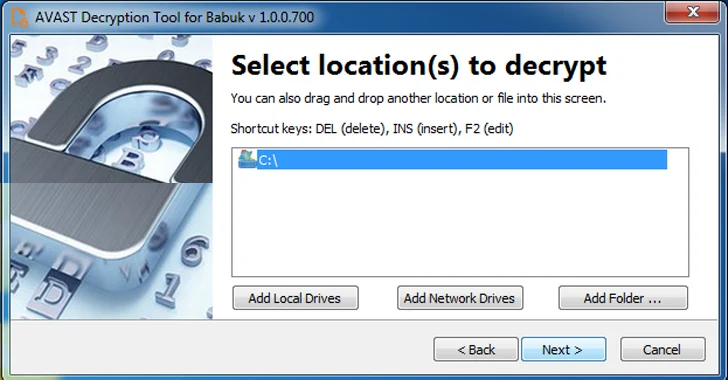
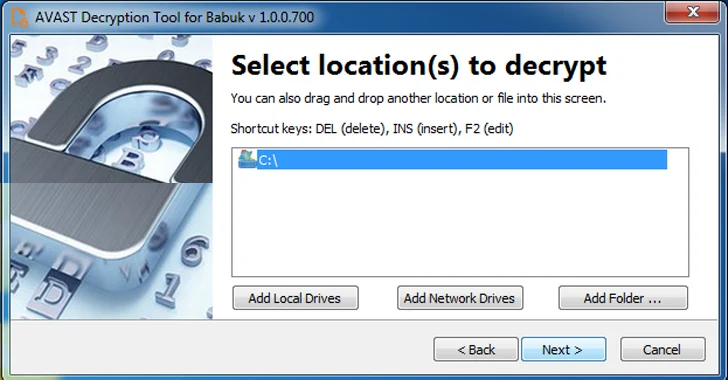
3.9KMalwareFree Decryptor Released for Black Basta and Babuk’s Tortilla Ransomware Victims
A decryptor for the Tortilla variant of the Babuk ransomware has been released by Cisco Talos, allowing victims targeted by the malware...
-

 2.7KVulnerabilities
2.7KVulnerabilitiesMicrosoft’s January 2024 Windows Update Patches 48 New Vulnerabilities
Microsoft has addressed a total of 48 security flaws spanning its software as part of its Patch Tuesday updates for January 2024....
-
 2.3KVulnerabilities
2.3KVulnerabilitiesCISA Flags 6 Vulnerabilities – Apple, Apache, Adobe, D-Link, Joomla Under Attack
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added six security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence...
-
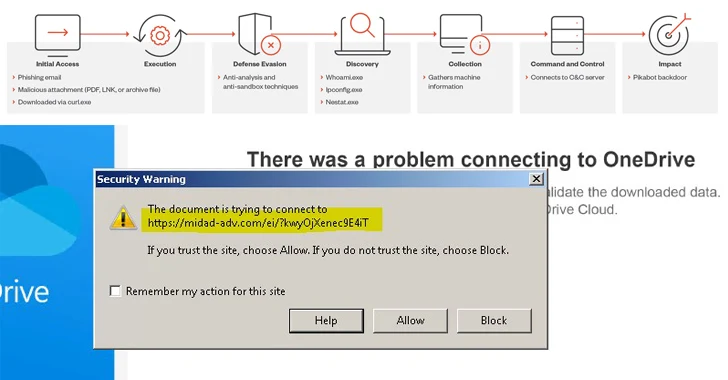
 2.0KMalware
2.0KMalwareAlert: Water Curupira Hackers Actively Distributing PikaBot Loader Malware
A threat actor called Water Curupira has been observed actively distributing the PikaBot loader malware as part of spam campaigns in 2023....
-
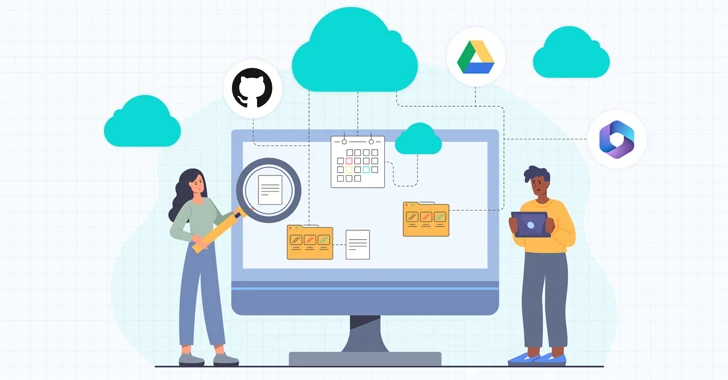
 2.8KVulnerabilities
2.8KVulnerabilitiesWhy Public Links Expose Your SaaS Attack Surface
Collaboration is a powerful selling point for SaaS applications. Microsoft, Github, Miro, and others promote the collaborative nature of their software applications...
-
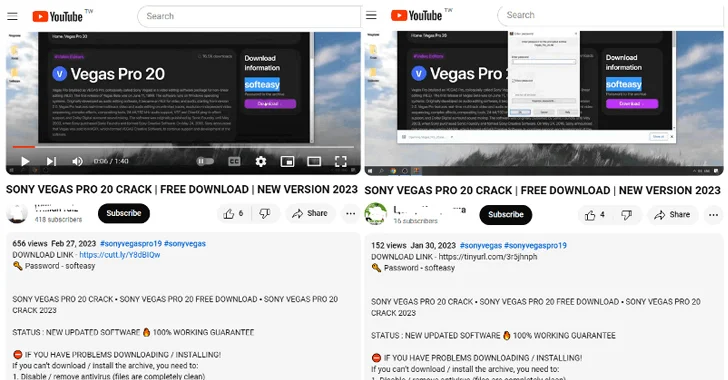
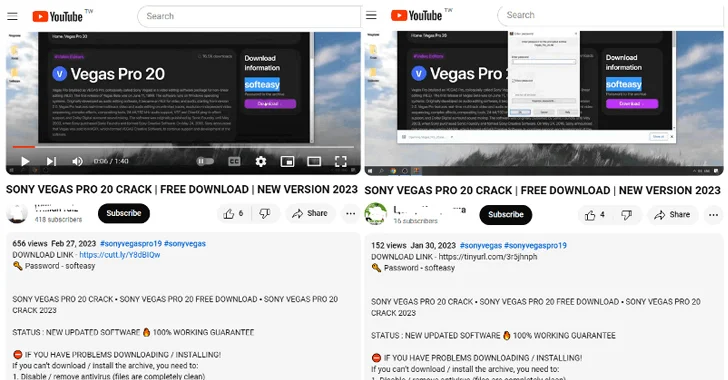 2.8KMalware
2.8KMalwareBeware! YouTube Videos Promoting Cracked Software Distribute Lumma Stealer
Threat actors are resorting to YouTube videos featuring content related to cracked software in order to entice users into downloading an information...
-
 496Tutorials
496Tutorials11 ways of hacking into ChatGpt like Generative AI systems
In the rapidly evolving landscape of artificial intelligence, generative AI systems have become a cornerstone of innovation, driving advancements in fields ranging...
-

 2.8KMalware
2.8KMalwareSyrian Hackers Distributing Stealthy C#-Based Silver RAT to Cybercriminals
Threat actors operating under the name Anonymous Arabic have released a remote access trojan (RAT) called Silver RAT that’s equipped to bypass...
-
 1.2KData Breach
1.2KData BreachUnifying Security Tech Beyond the Stack: Integrating SecOps with Managed Risk and Strategy
Cybersecurity is an infinite journey in a digital landscape that never ceases to change. According to Ponemon Institute1, “only 59% of organizations...
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan




