Featured News
-

 5.0KVulnerabilities
5.0KVulnerabilitiesSpectralBlur: New macOS Backdoor Threat from North Korean Hackers
Cybersecurity researchers have discovered a new Apple macOS backdoor called SpectralBlur that overlaps with a known malware family that has been attributed...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesExposed Secrets are Everywhere. Here’s How to Tackle Them
Picture this: you stumble upon a concealed secret within your company’s source code. Instantly, a wave of panic hits as you grasp...
-

 1.9KMalware
1.9KMalwareOrange Spain Faces BGP Traffic Hijack After RIPE Account Hacked by Malware
Mobile network operator Orange Spain suffered an internet outage for several hours on January 3 after a threat actor used administrator credentials...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesAlert: Ivanti Releases Patch for Critical Vulnerability in Endpoint Manager Solution
Ivanti has released security updates to address a critical flaw impacting its Endpoint Manager (EPM) solution that, if successfully exploited, could result...
-

 450Data Breach
450Data BreachRussian Hackers Had Covert Access to Ukraine’s Telecom Giant for Months
Ukrainian cybersecurity authorities have disclosed that the Russian state-sponsored threat actor known as Sandworm was inside telecom operator Kyivstar’s systems at least...
-

 201Malware
201MalwareNew Bandook RAT Variant Resurfaces, Targeting Windows Machines
A new variant of a remote access trojan called Bandook has been observed being propagated via phishing attacks with an aim to...
-

 1.3KMalware
1.3KMalwareBeware: 3 Malicious PyPI Packages Found Targeting Linux with Crypto Miners
Three new malicious packages have been discovered in the Python Package Index (PyPI) open-source repository with capabilities to deploy a cryptocurrency miner...
-
 1.5KMalware
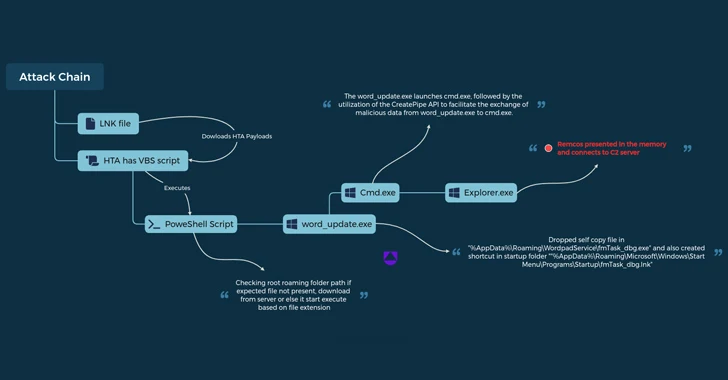
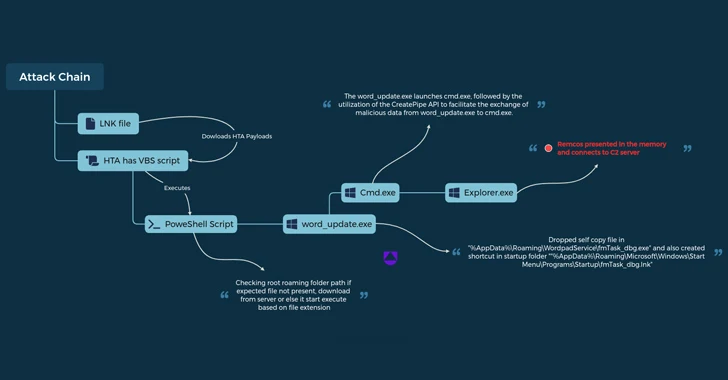
1.5KMalwareUAC-0050 Group Using New Phishing Tactics to Distribute Remcos RAT
The threat actor known as UAC-0050 is leveraging phishing attacks to distribute Remcos RAT using new strategies to evade detection from security...
-

 1.9KVulnerabilities
1.9KVulnerabilitiesMalware Using Google MultiLogin Exploit to Maintain Access Despite Password Reset
Information stealing malware are actively taking advantage of an undocumented Google OAuth endpoint named MultiLogin to hijack user sessions and allow continuous...
-
 2.8KVulnerabilities
2.8KVulnerabilitiesNew Variant of DLL Search Order Hijacking Bypasses Windows 10 and 11 Protections
Security researchers have detailed a new variant of a dynamic link library (DLL) search order hijacking technique that could be used by...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesNew Terrapin Flaw Could Let Attackers Downgrade SSH Protocol Security
Security researchers from Ruhr University Bochum have discovered a vulnerability in the Secure Shell (SSH) cryptographic network protocol that could allow an...
-
 4.8KMalware
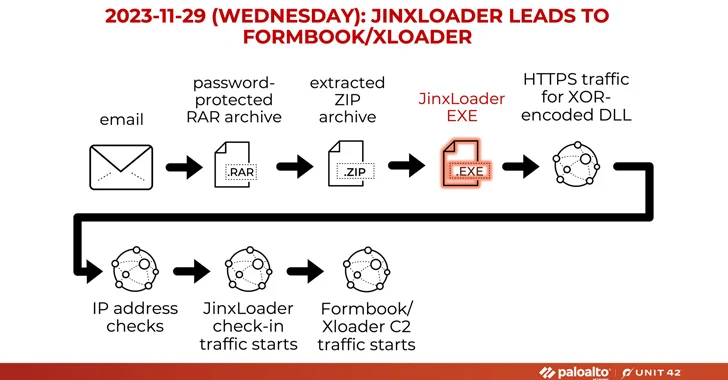
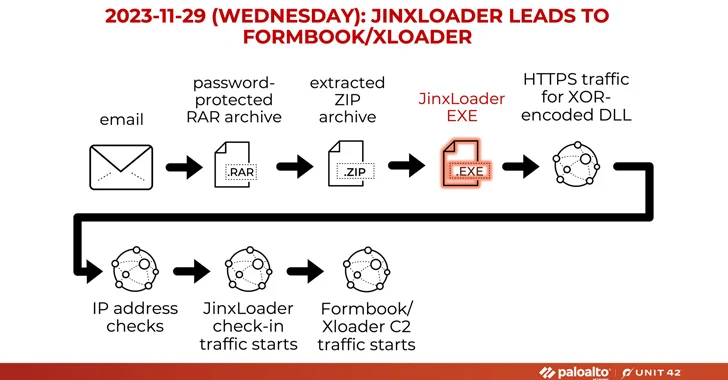
4.8KMalwareNew JinxLoader Targeting Users with Formbook and XLoader Malware
A new Go-based malware loader called JinxLoader is being used by threat actors to deliver next-stage payloads such as Formbook and its...
-

 3.2KCyber Attack
3.2KCyber AttackAlbanian Parliament and One Albania Telecom Hit by Cyber Attacks
The Assembly of the Republic of Albania and telecom company One Albania have been targeted by cyber attacks, the country’s National Authority...
-
 2.0KMalware
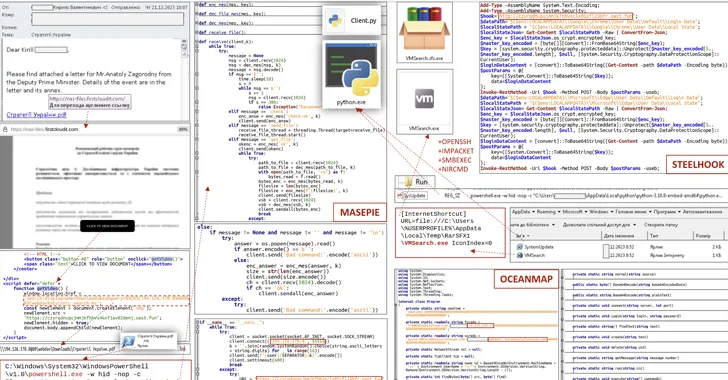
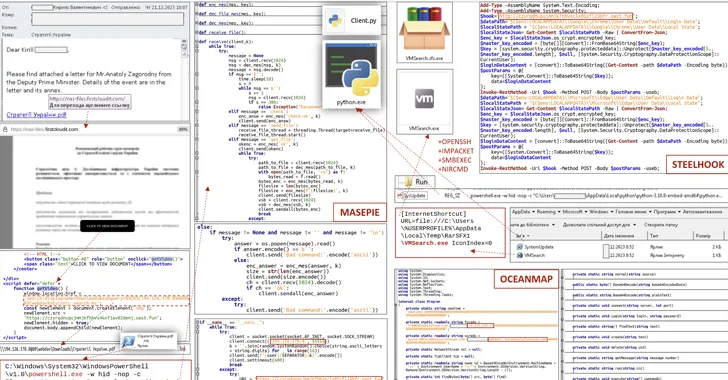
2.0KMalwareCERT-UA Uncovers New Malware Wave Distributing OCEANMAP, MASEPIE, STEELHOOK
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of a new phishing campaign orchestrated by the Russia-linked APT28 group to...
-

 1.1KMalware
1.1KMalwareKimsuky Hackers Deploying AppleSeed, Meterpreter, and TinyNuke in Latest Attacks
Nation-state actors affiliated to North Korea have been observed using spear-phishing attacks to deliver an assortment of backdoors and tools such as...
-
 4.3KMalware
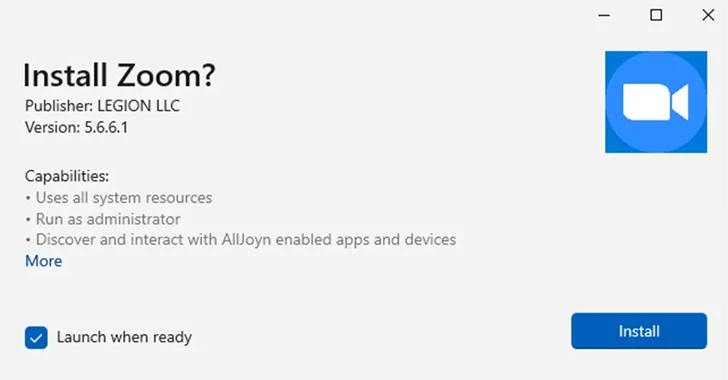
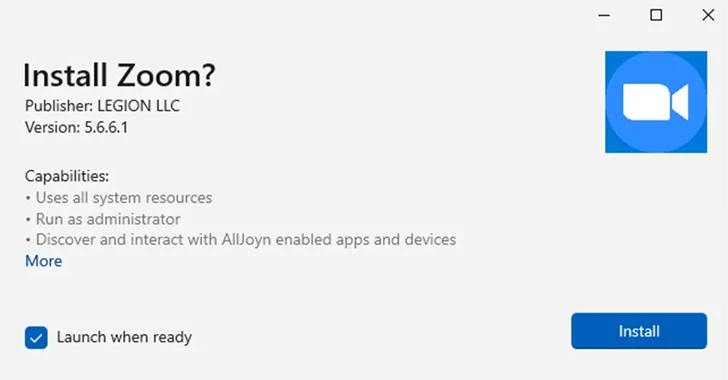
4.3KMalwareMicrosoft Disables MSIX App Installer Protocol Widely Used in Malware Attacks
Microsoft on Thursday said it’s once again disabling the ms-appinstaller protocol handler by default following its abuse by multiple threat actors to...
-

 2.1KData Security
2.1KData SecurityHow to hack Google Kubernetes Engine (GKE)? Securing against GKE threats
A recent investigation by Unit 42 of Palo Alto Networks has uncovered a dual privilege escalation chain in Google Kubernetes Engine (GKE)....
-

 3.2KVulnerabilities
3.2KVulnerabilitiesGoogle Cloud Resolves Privilege Escalation Flaw Impacting Kubernetes Service
Google Cloud has addressed a medium-severity security flaw in its platform that could be abused by an attacker who already has access...
-

 5.2KVulnerabilities
5.2KVulnerabilitiesCritical Zero-Day in Apache OfBiz ERP System Exposes Businesses to Attack
A new zero-day security flaw has been discovered in Apache OfBiz, an open-source Enterprise Resource Planning (ERP) system that could be exploited...
-

 3.9KVulnerabilities
3.9KVulnerabilitiesChinese Hackers Exploited New Zero-Day in Barracuda’s ESG Appliances
Barracuda has revealed that Chinese threat actors exploited a new zero-day in its Email Security Gateway (ESG) appliances to deploy backdoors on...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




