Search results for "Phishing "
-
 1.1KCyber Attack
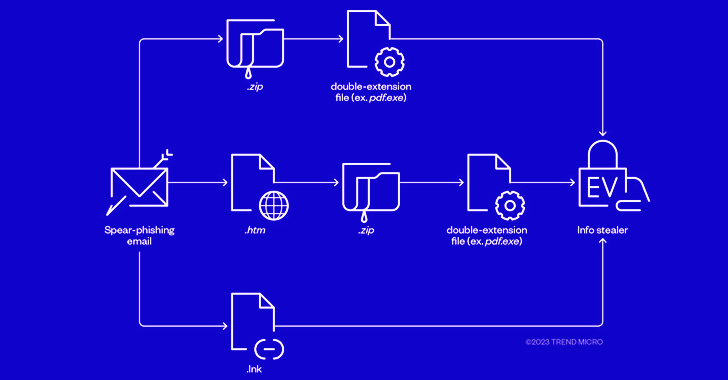
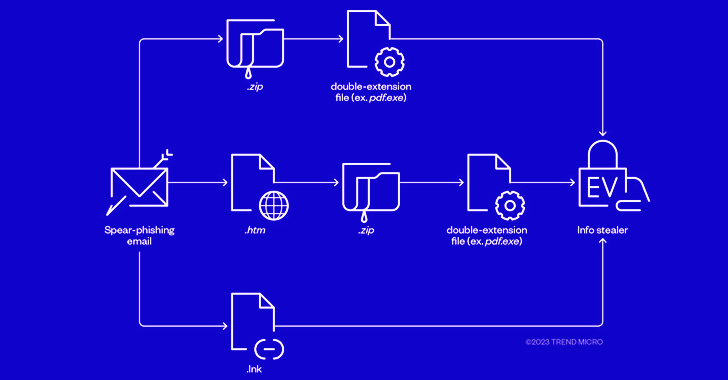
1.1KCyber AttackCybercriminals Combine Phishing and EV Certificates to Deliver Ransomware Payloads
The threat actors behind RedLine and Vidar information stealers have been observed pivoting to ransomware through phishing campaigns that spread initial payloads...
-
 5.1KMalware
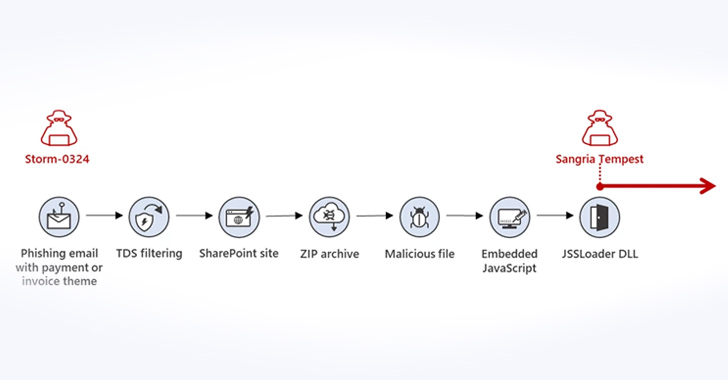
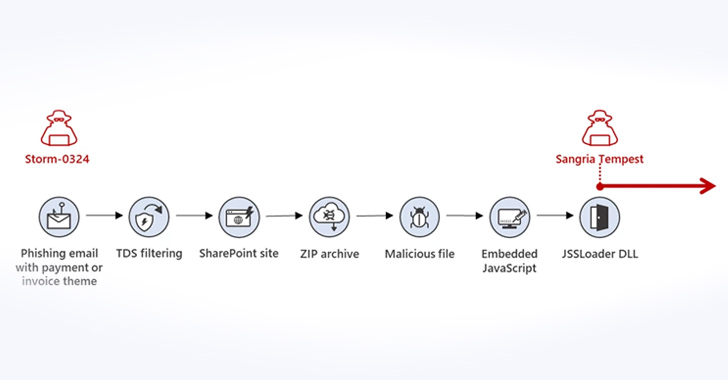
5.1KMalwareMicrosoft Warns of New Phishing Campaign Targeting Corporations via Teams Messages
Microsoft is warning of a new phishing campaign undertaken by an initial access broker that involves using Teams messages as lures to...
-
 3.3KMalware
3.3KMalwareSophisticated Phishing Campaign Deploying Agent Tesla, OriginBotnet, and RedLine Clipper
A sophisticated phishing campaign is using a Microsoft Word document lure to distribute a trifecta of threats, namely Agent Tesla, OriginBotnet, and...
-
 3.0KCyber Attack
3.0KCyber AttackAlert: Phishing Campaigns Deliver New SideTwist Backdoor and Agent Tesla Variant
The Iranian threat actor tracked as APT34 has been linked to a new phishing attack that leads to the deployment of a...
-
Malware
New SuperBear Trojan Emerges in Targeted Phishing Attack on South Korean Activists
A new phishing attack likely targeting civil society groups in South Korea has led to the discovery of a novel remote access...
-
 3.3KMalware
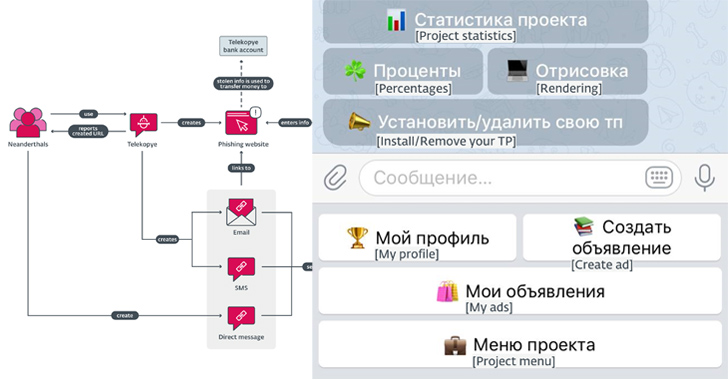
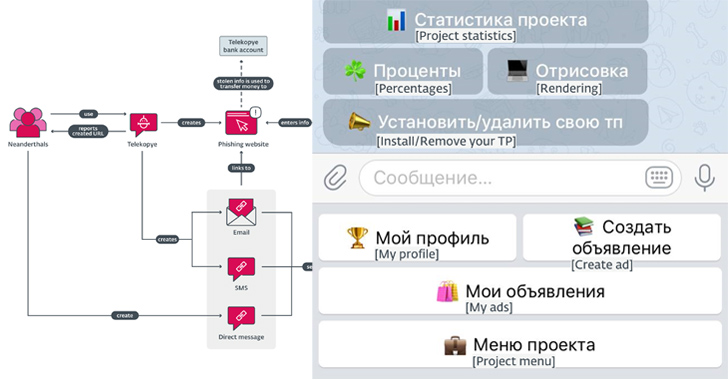
3.3KMalwareNew Telegram Bot “Telekopye” Powering Large-scale Phishing Scams from Russia
A new financially motivated operation is leveraging a malicious Telegram bot to help threat actors scam their victims. Dubbed Telekopye, a portmanteau...
-
 1.1KCyber Attack
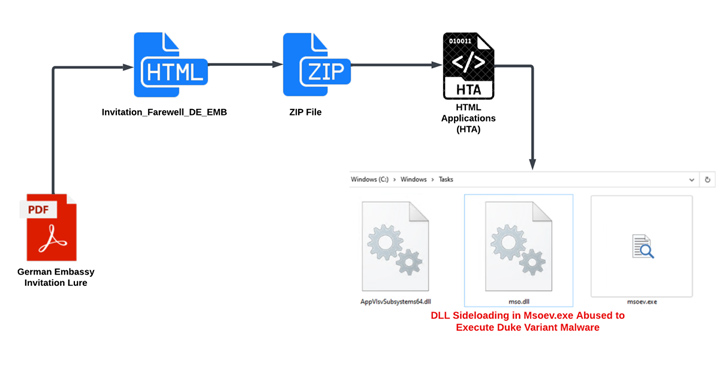
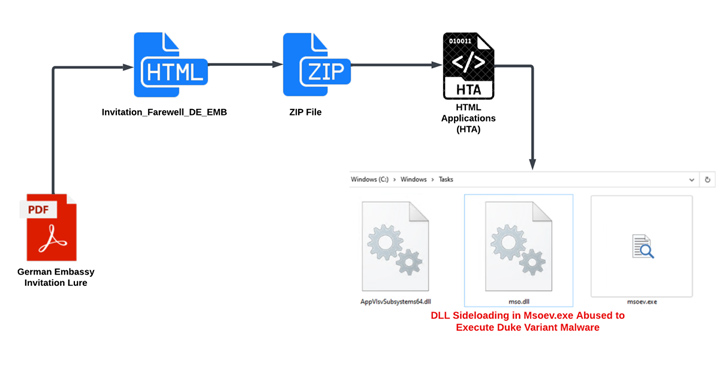
1.1KCyber AttackRussian Hackers Use Zulip Chat App for Covert C&C in Diplomatic Phishing Attacks
An ongoing campaign targeting ministries of foreign affairs of NATO-aligned countries points to the involvement of Russian threat actors. The phishing attacks...
-
 808Cyber Attack
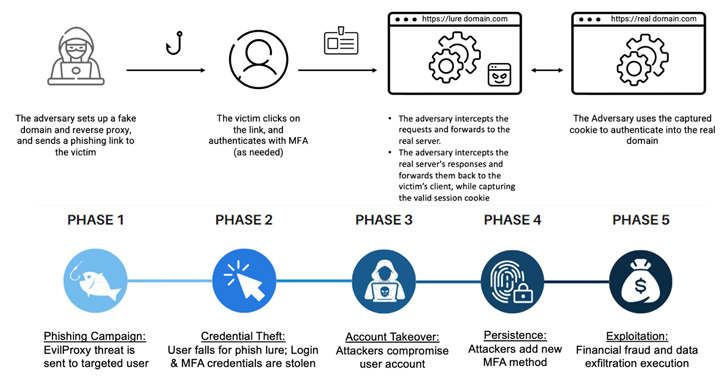
808Cyber AttackCybercriminals Increasingly Using EvilProxy Phishing Kit to Target Executives
Threat actors are increasingly using a phishing-as-a-service (PhaaS) toolkit dubbed EvilProxy to pull off account takeover attacks aimed at high-ranking executives at...
-

 1.8KIncidents
1.8KIncidentsHow $400 toolkit EvilProxy was used to send 120k phishing emails to hundreds of companies
Researchers have discovered that malicious actors have been utilizing the phishing toolkit EvilProxy to gain control of cloud-based Microsoft 365 accounts belonging...
-
 434Data Security
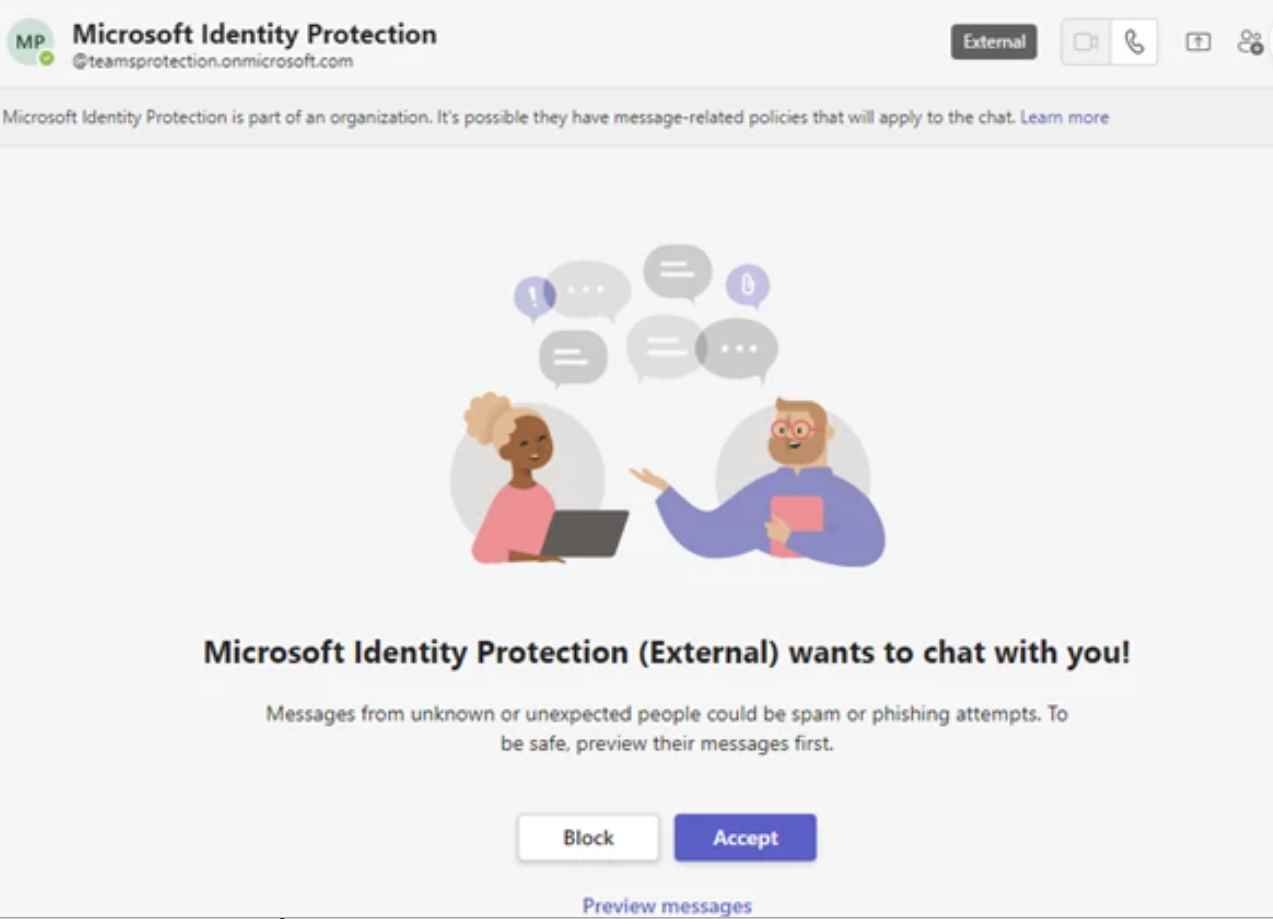
434Data SecurityPhishing attack over Microsoft Teams allows getting MFA from victim
Hackers working for the Russian government disguised as technical support personnel on Microsoft Teams in order to breach the security of hundreds...
-

 2.3KMalware
2.3KMalwareUsers of Facebook for Business are the Target of a New Phishing Attack
An unreported phishing campaign that disseminated a Python version of the NodeStealer has been found. NodeStealer gave threat actors the ability to steal...
-
 3.3KData Security
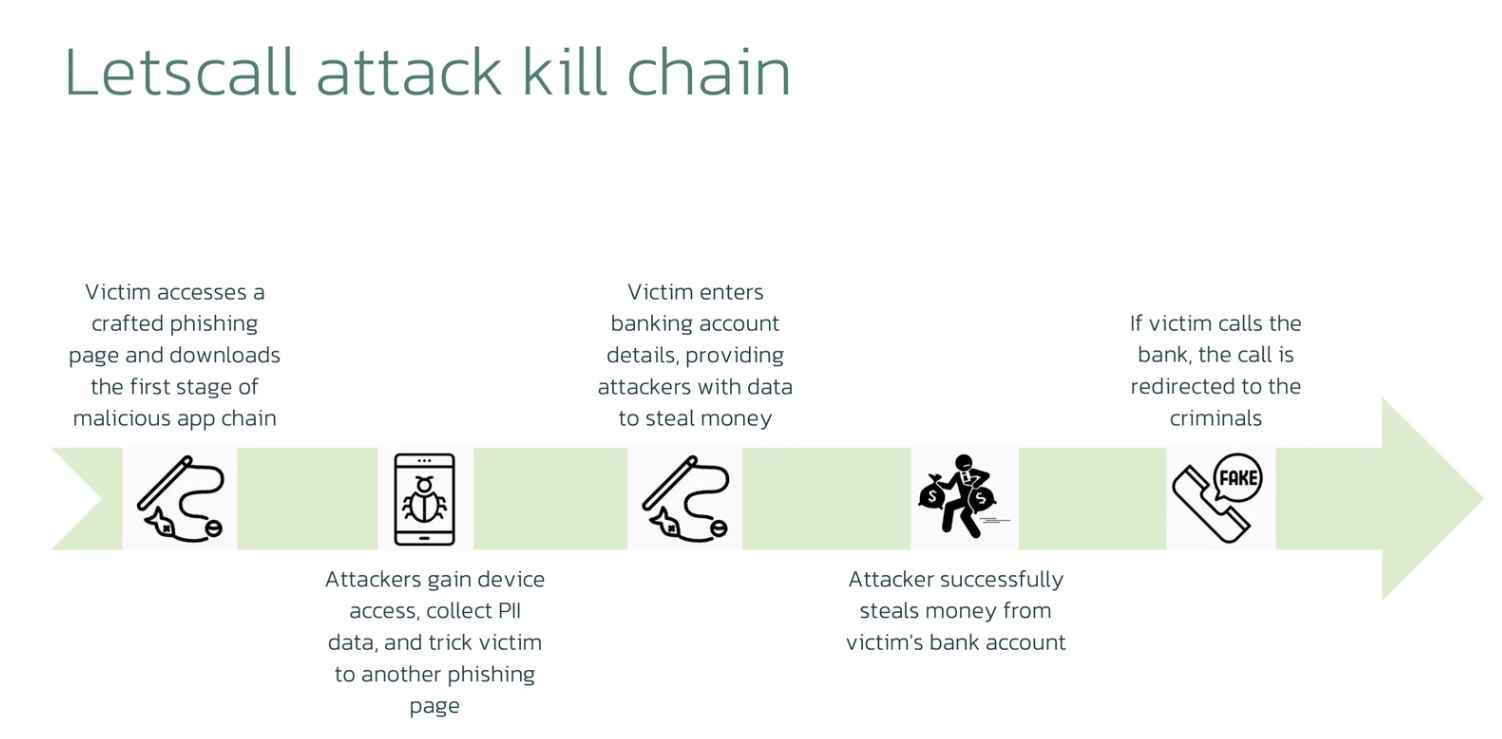
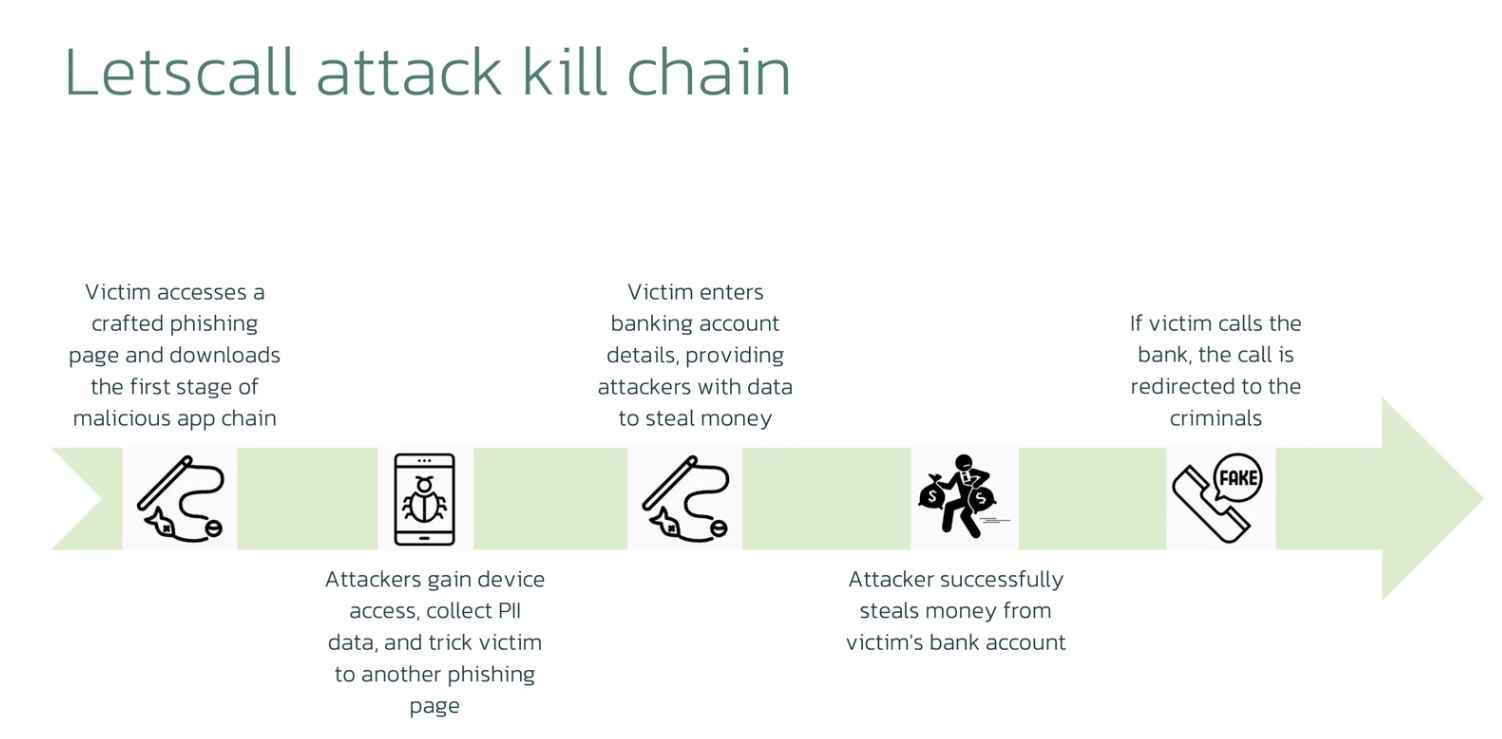
3.3KData SecurityVoIP phishing call to rob a bank. New Letscall attack technique
The cybersecurity researcher working for ThreatFabric made the discovery, and the company issued a warning, about a new and more sophisticated kind...
-

 4.6KMalware
4.6KMalwareCharming Kitten APT Group Uses Innovative Spear-phishing Methods
Charming Kitten APT Group Uses Innovative Spear-phishing Methods. Volexity researchers recently noticed that threat actors are actively intensifying their efforts to compromise...
-

 4.8KPhishing
4.8KPhishingMassive Phishing Campaign Uses 6,000 Sites to Mimic Popular Brands
Bolster’s threat research team recently discovered an extensive brand impersonation effort targeting over 100 well-known clothes, footwear, and apparel firms. The peak...
-

 2.4KData Security
2.4KData SecurityNew AiTM Phishing Attack Technique Makes It Easy to Hack Business Email Accounts
Experts from Microsoft Defender discovered a multi-stage adversary-in-the-middle (AiTM) phishing and business email compromise (BEC) attack that targeted firms that provide banking...
-

 615Data Security
615Data SecuritySend spoofed phishing emails to Gmail accounts
The most people use Gmail, which has a total user base of a staggering 1.5 billion people. This represents 18.75% of the...
-
 4.7KData Security
4.7KData SecurityNew phishing technique to allows hacking someone using .zip & .mov domains
When a victim visits a website ending in .ZIP, a recently developed phishing method known as “file archiver in the browser” may...
-

 4.7KPhishing
4.7KPhishingShut Down Phishing Attacks – Types, Methods, Detection, Prevention Checklist
In today’s interconnected world, where digital communication and transactions dominate, phishing attacks have become an ever-present threat. By masquerading as trustworthy entities,...
-

 3.7KPhishing
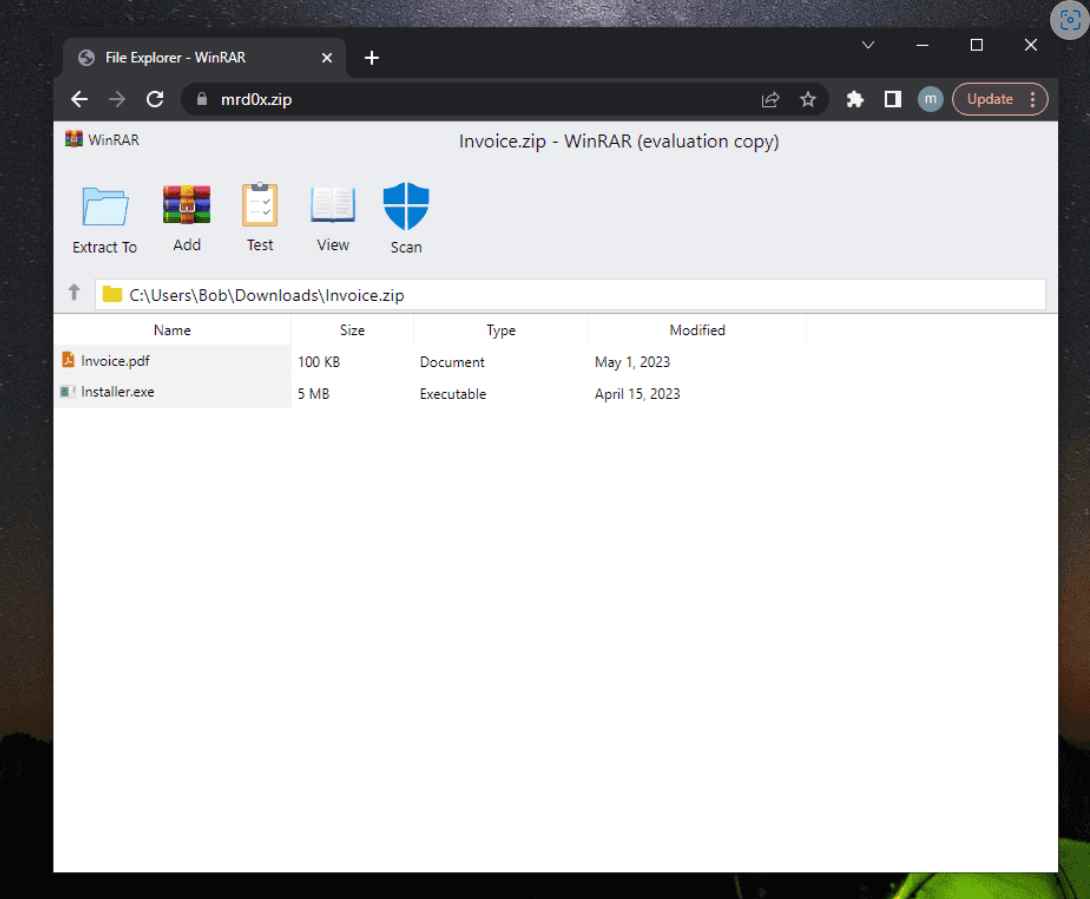
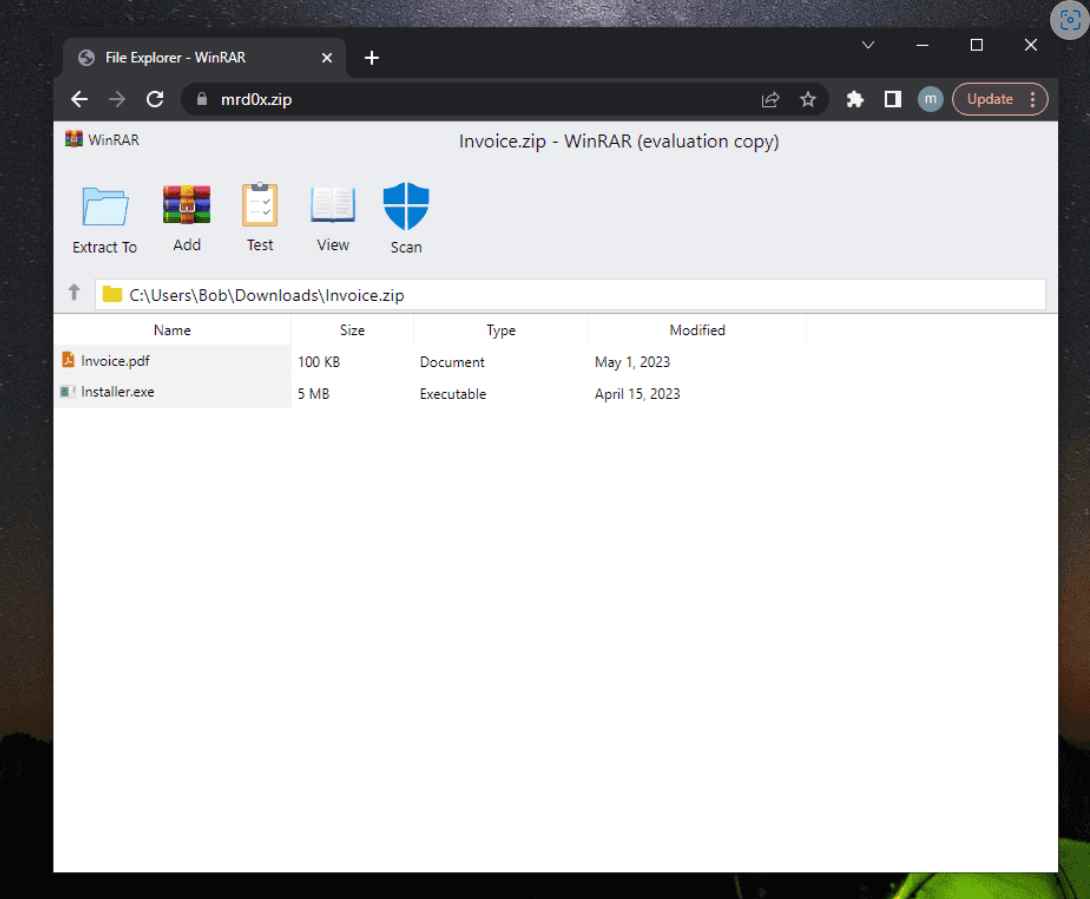
3.7KPhishingNew Phishing Attack Abuses .Zip Domain to Emulate Fake WinRAR Within the Browser
Google recently released new top-level domains (TLDs) like .dad, .phd, .mov, and .zip, raising concerns within the security community due to the...
-
 1.3KMalware
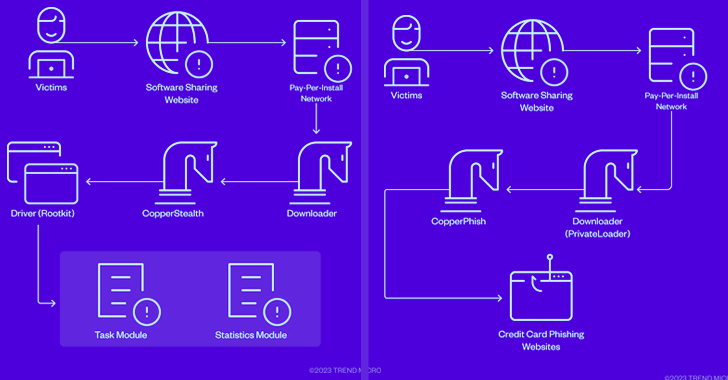
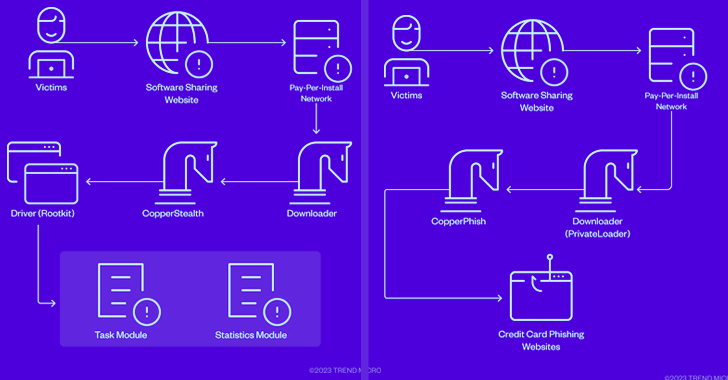
1.3KMalwareCopperStealer Malware Crew Resurfaces with New Rootkit and Phishing Kit Modules
The threat actors behind the CopperStealer malware resurfaced with two new campaigns in March and April 2023 that are designed to deliver...
-

 208Phishing
208PhishingNew Phishing Attacks Using ChatGPT to Develop Sophisticated Campaigns
Phishing has been one of the greatest threats to organizations, growing year after year. Phishing attacks have contributed to 90% of data...






