Search results for "surveillance"
-

 271News
271NewsChinese Surveillance Is Using AI To Target Minorities In The Country
China is known to have been working on its surveillance strategies for a while now, with AI playing a significant role in...
-

 398Data Security
398Data SecurityNasty Android & iOS malware found using govt surveillance tech
The latest findings of security researchers at security firm Lookout and privacy firm Security Without Borders are not only groundbreaking but concerning....
-
 253Malware
253Malware‘Exodus’ Surveillance Malware Found Targeting Apple iOS Users
Cybersecurity researchers have discovered an iOS version of the powerful mobile phone surveillance app that was initially targeting Android devices through apps...
-
 246Exploitation Tools
246Exploitation ToolsCameradar v2.1.0 – Hacks Its Way Into RTSP Videosurveillance Cameras
An RTSP stream access tool that comes with its library Cameradar allows you to Detect open RTSP hosts on any accessible target...
-
 301Surveillance
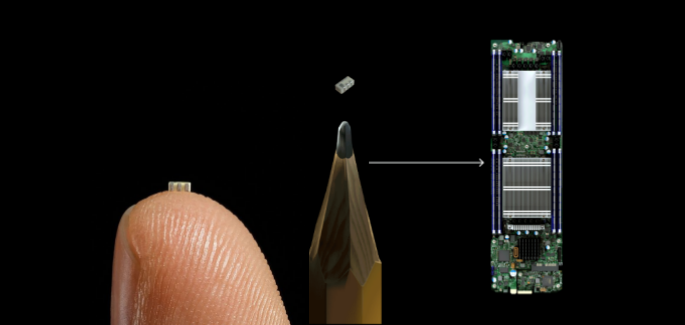
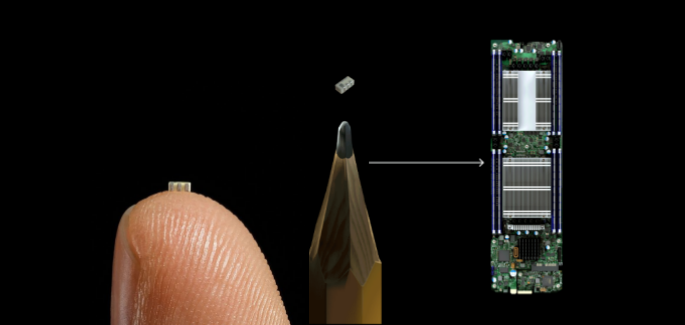
301SurveillanceChinese surveillance chips found in servers used by US technology giants: Report
This can be one of one of the largest corporate spying and hardware hacking campaigns ever launched by a nation-state. Bloomberg has...
-

 284Vulnerabilities
284VulnerabilitiesVulnerability affects Cisco Video Surveillance Manager
The company has patched a critical vulnerability in Cisco Video Surveillance Manager that could be exploited to gain root access Reports of...
-

 466Ransomware
466Ransomware28-year-old Romanian Woman Pleads Guilty for Hacking 126 Computers Associated With Surveillance Cameras
A Romanian Woman Eveline Cismaru. 28, pled guilty to federal charges for illegally gaining access to more than 126 computers that connected...
-
 271Mobile Security
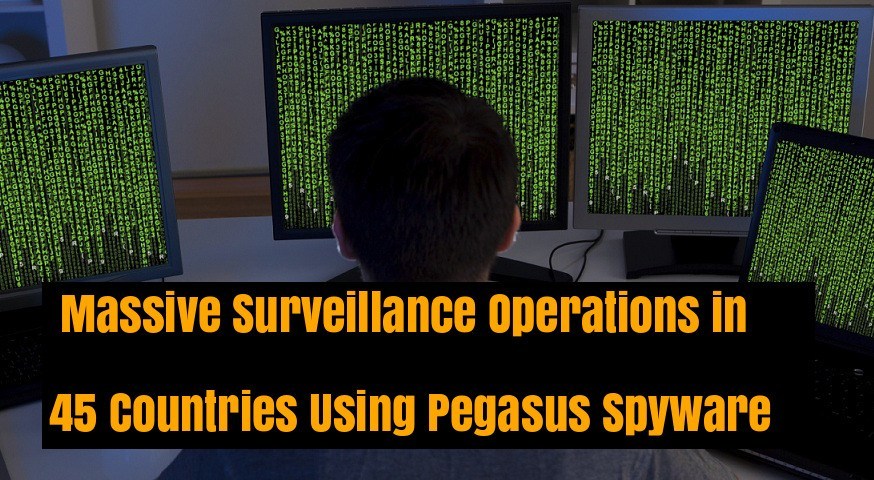
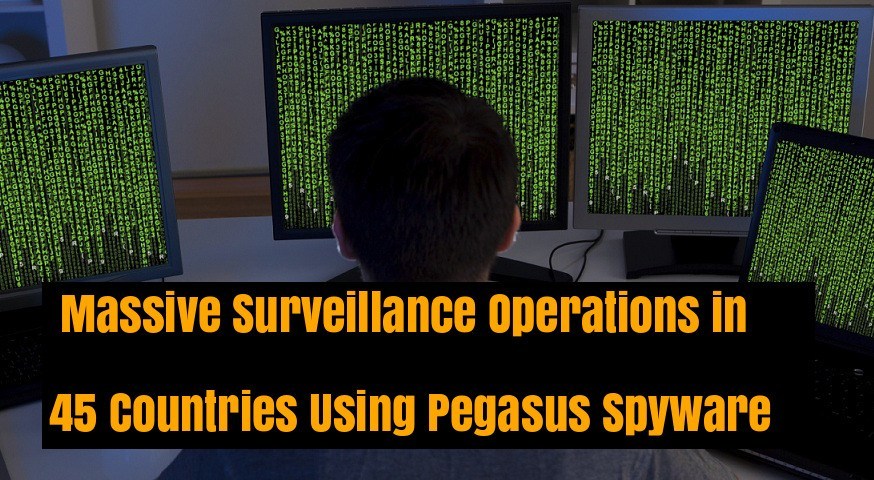
271Mobile SecurityHackers using Android & iOS Spyware “Pegasus” to Conducting Massive Surveillance Operations in 45 Countries
New research reveals that Israel based NSO Group using powerful mobile based Pegasus Spyware to conducting massive surveillance in 45 countries across...
-

 359Surveillance
359SurveillanceCell-Site surveillance devices (Stingray) could disrupt 911 emergency calls
Senator Ron Wyden of Oregon has made startling new revelations about CSS or cell-site stimulators. These cell surveillance devices, better known as...
-

 177News
177News4 Creative Ways to Secure Surveillance Cameras from known Vulnerability
Corporate systems are categorized into two: Internally developed Developed by a vendor Internally developed systems are the exact tailor fit solutions that...
-

 216Hacked
216HackedThis Tool Stops Your Data From Passing Through Surveillance-Happy Countries
Many of us already know that the internet traffic passes through different countries before reaching its destination. But did you know that...
-

 138Hackers Repository
138Hackers RepositoryWATCH: Phone Hackers – Britain’s Secret Surveillance (Vice)
Phone Hackers: Britain’s Secret Surveillance In this video Vice Media uncovers one of Britain’s secret surveillance devices the IMSI catcher. International Mobile...
-

 205Data Security
205Data SecuritySupreme Court dictates that Government will need a warrant for long-term surveillance using location data
Information security training specialists report a new ruling from The Supreme Court, establishing that, in most cases, the Government will need an...
-

 248Surveillance
248SurveillanceMan Sues Feds For Installing Surveillance Camera on his Property
A 74-year old rancher in Texas discovered a small portal surveillance camera installed on his property in the south of Encinal, Texas,...
-

 220Malware
220MalwareUS capital’s surveillance cam network allegedly hijacked by Romanian ransomware suspects
Charges filed against pair coincide with arrests abroad. Two of the five unnamed individuals cuffed this month in Romania on suspicion of spreading ransomware...
-

 352Data Breach
352Data BreachPentagon’s Data Leak Exposed 1.8 Billion of Social Media Surveillance Data
Pentagon Data Leak, other three Amazon Web Services S3 cloud storage buckets that contain social media surveillance data configured in the way...
-

 304Data Security
304Data SecurityTexas National Guard secretly installed spying devices on surveillance aircrafts
The Texas National Guard bought two DRT 1301C cell-site simulator devices for more than $373,000. The purpose of buying these devices was...
-

 274Articles
274ArticlesTexas is spying on Thousands of Phones using Surveillance Drones and Planes
Similar to questionable stingray devices, DRT’s operations nicknamed “dirt boxes” mimic cellphone pillars, relating to every smartphone within a specific area. Because...
-

 189Hack Tools
189Hack ToolsEggShell – iOS And macOS Surveillance Tool
EggShell is an iOS and macOS post exploitation surveillance pentest tool written in Python. This tool creates 1 line multi stage payloads...
-

 125Data Security
125Data SecuritySpeakers and Mics hacked to turn Music Into Surveillance Tool
University of Washington’s Paul G. Allen School of Computer Science & Engineering research team has concluded that it is possible to use...
-

 373Data Security
373Data SecurityAmazon Echo Can Be Hacked to act as a Surveillance device
Taking over an IoT (Internet of Things) device is nothing new for hackers, but since users have become increasingly dependent on smart devices,...






