Search results for "surveillance"
-

 230Geek
230GeekFBI’s Surveillance Van Sold on eBay for US $18,700
Who doesn’t want to buy a fully equipped FBI surveillance van having facilities like video and audio recording equipment and even a...
-

 264Data Security
264Data SecurityVariant of Surveillance Malware Fruitfly Targeting Mac Users
In January this year, a dangerous surveillance malware was found targeting Mac and Linux devices – The malware was discovered by Thomas...
-

 316Malware
316MalwareVault 7 Leaks : CIA Owned PoC Malware Development Surveillance Projects “UCL Under Raytheon” Leaked – WikiLeaks
WikiLeaks Revealed CIA Surveillance Projects Documents “UMBRAGE Component Library(UCL)” from CIA contractor Raytheon Blackbird Technologies which contains five secret Malware Development Related...
-

 285GPS & Radio
285GPS & RadioCameradar – An RTSP Surveillance Camera Access Multitool
Cameradar hacks its way into RTSP CCTV cameras Cameradar allows you to: Detect open RTSP hosts on any accessible target Get their...
-

 137Privacy
137PrivacySurveillance, cybersecurity, and the future of privacy in The Circle
If surveillance, cybersecurity, and privacy are things you think about a lot, you should find The Circle interesting viewing.
-
 300Incidents
300IncidentsNSA announces it will stop surveillance activities on emails, texts and other internet communications
NSA announces a change in its surveillance activities, it will no longer spy on citizens’ emails, texts, and other Internet communications. It is...
-

 237Vulnerabilities
237VulnerabilitiesCallisto APT Group exploited Hacking Team surveillance tools to hack Government targets
The Callisto APT Group borrowed the source code leaked by hackers that broke into Hacking Team network. According to F-Secure Labs, The Callisto APT...
-

 111Vulnerabilities
111VulnerabilitiesSpies do spying, part 97: Shock horror as CIA turn phones, TVs, computers into surveillance bugs
Nothing to fear, citizens. Keep consuming. Keep smiling. WikiLeaks has dumped online what appears to be a trove of CIA documents outlining...
-

 272News
272NewsAnonymous Shut Down Thai Sites Against Internet Censorship, Surveillance Law
The government of Thailand has been under the hammer of internet activist groups since the parliament approved an amendment to the 2007...
-

 113Data Security
113Data SecurityBackdoor Found in 80 Sony Surveillance Camera Models
Sony has released firmware updates that remove a remotely exploitable backdoor account from 80 models of IP and security cameras. Because attackers...
-

 318News
318News$55 surveillance camera hacked by Mirai botnet within 98 seconds
The Internet of Things has become more of a joke lately because of the never ending styles of exploitation that these poor...
-

 246Data Security
246Data SecurityMass Surveillance of Cell Phone Data by AT&T Service Provider
AT&T has been data-mining and willingly sharing user phone data, through its “Hemisphere” Project, which is essentially a mass surveillance program. The...
-

 312Hacked
312HackedEndace: This Unknown Company Powers Massive Surveillance Around The World
Short Bytes: The government security agencies try to intercept information about people on the internet. The agency takes the help of companies...
-
 191Hacked
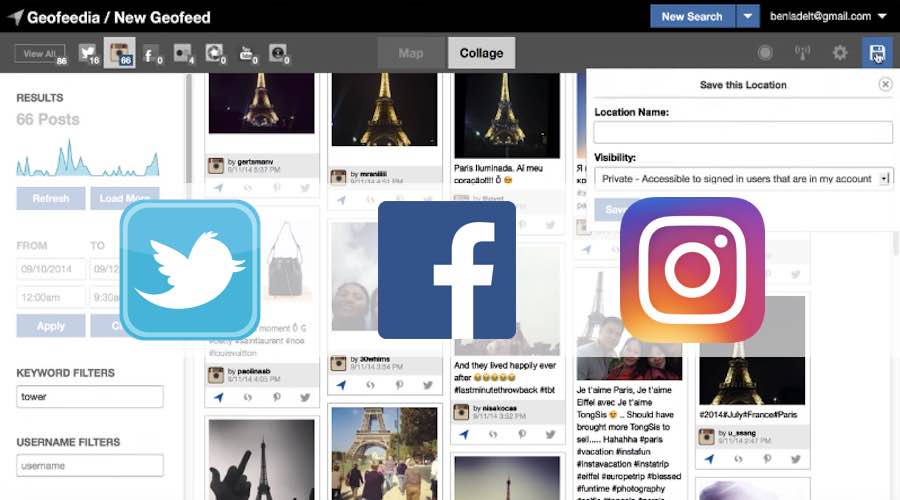
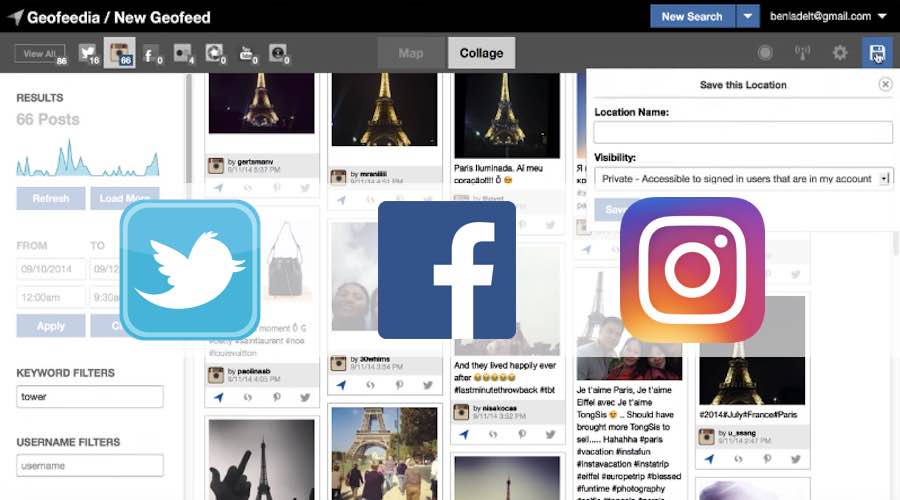
191HackedExposed: Facebook, Twitter, And Instagram Sent User Data To Surveillance Company
Short Bytes: The ACLU of California has released some records that show Twitter, Facebook, and Instagram shared the user data with a...
-

 82Data Security
82Data SecurityBuilding a new Tor that can resist next-generation state surveillance
Tor is an imperfect privacy platform. Ars meets the researchers trying to replace it. Since Edward Snowden stepped into the limelight from a hotel room...
-

 82Malware
82MalwareMalware found in surveillance cameras sold through Amazon
Security researcher finds malicious code embedded within cameras offered for sale on Amazon. Last week, independent security researcher Mike Olsen discovered that CCTV...
-

 83Data Security
83Data SecurityTorMail hack, FBI surgical operation, or dragnet surveillance?
In 2013 the FBI agents seized TorMail, now new information are emerging on the operations. Someone believes it was a surgical ops...
-

 337News
337NewsTech Giants in Battle Against UK Government Over Surveillance Program
Privacy protection or criminal activity prevention? UK Government faces battle against tech companies on a hot matter UK Government drafted a plan...
-

 279Incidents
279IncidentsDHS: Drug Traffickers are hacking surveillance drones on the border
The U.S. Department of Homeland Security and local law enforcement confirmed that Drug Traffickers are hacking surveillance drones on the border. Small...
-

 299Geek
299GeekThese Anti-Surveillance Tools Will Protect Activists and Their Privacy
In a world where government surveillance is a big thing there is a need for tools countering the whole idea of keeping...
-

 172Data Security
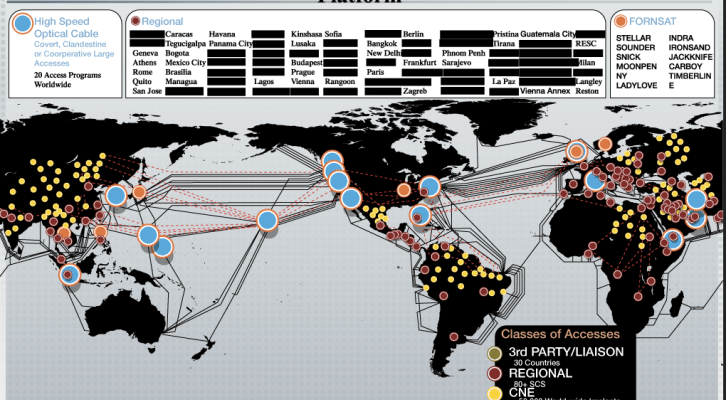
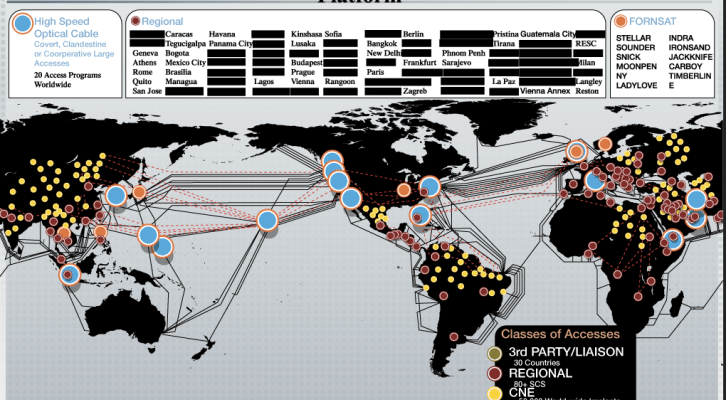
172Data SecurityDocuments demonstrate NSA continued mass surveillance
Newly disclosed documents show that the NSA had found a way to continue spying on American citizens’ email traffic from overseas. The...






