Search results for "Malware"
-

 4.9KMalware
4.9KMalwareRaspberry Robin Malware Upgrades with Discord Spread and New Exploits
The operators of Raspberry Robin are now using two new one-day exploits to achieve local privilege escalation, even as the malware continues...
-

 2.8KMalware
2.8KMalwareMoqHao Android Malware Evolves with Auto-Execution Capability
Threat hunters have identified a new variant of Android malware called MoqHao that automatically executes on infected devices without requiring any user...
-
 1.9KMalware
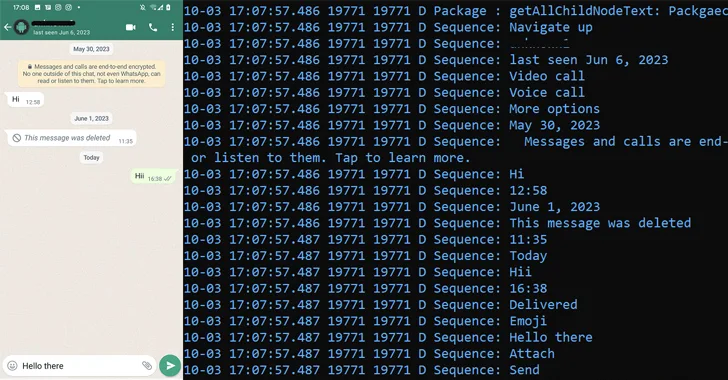
1.9KMalwarePatchwork Using Romance Scam Lures to Infect Android Devices with VajraSpy Malware
The threat actor known as Patchwork likely used romance scam lures to trap victims in Pakistan and India, and infect their Android...
-

 2.6KMalware
2.6KMalwareDirtyMoe Malware Infects 2,000+ Ukrainian Computers for DDoS and Cryptojacking
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned that more than 2,000 computers in the country have been infected by...
-

 2.9KVulnerabilities
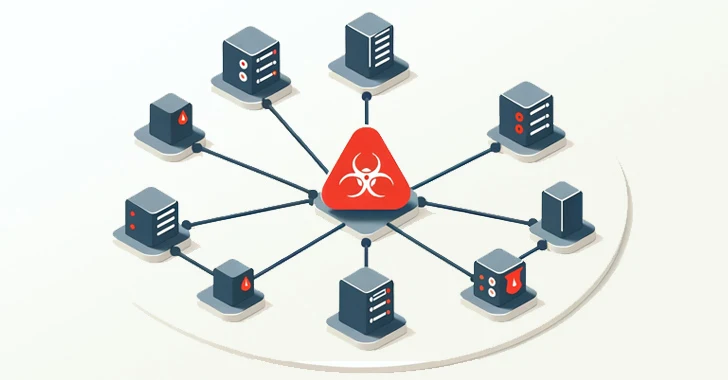
2.9KVulnerabilitiesFritzFrog Returns with Log4Shell and PwnKit, Spreading Malware Inside Your Network
The threat actor behind a peer-to-peer (P2P) botnet known as FritzFrog has made a return with a new variant that leverages the...
-
 2.0KMalware
2.0KMalwareWarning: New Malware Emerges in Attacks Exploiting Ivanti VPN Vulnerabilities
Google-owned Mandiant said it identified new malware employed by a China-nexus espionage threat actor known as UNC5221 and other threat groups during...
-
 3.7KMalware
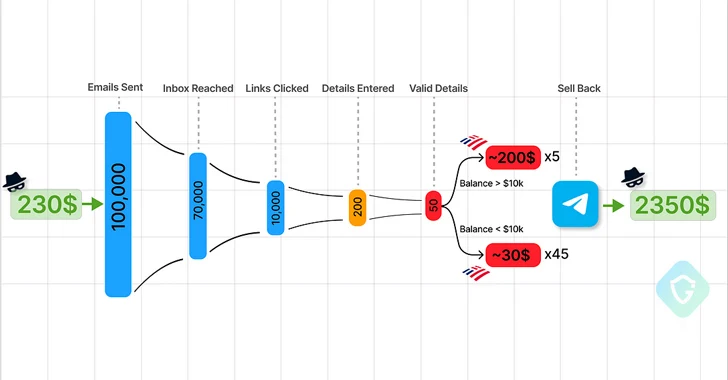
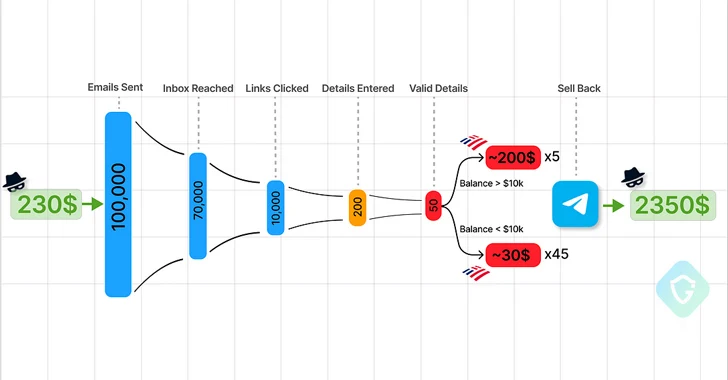
3.7KMalwareTelegram Marketplaces Fuel Phishing Attacks with Easy-to-Use Kits and Malware
Cybersecurity researchers are calling attention to the “democratization” of the phishing ecosystem owing to the emergence of Telegram as an epicenter for...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesHackers Exploiting Ivanti VPN Flaws to Deploy KrustyLoader Malware
A pair of recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) virtual private network (VPN) devices have been exploited to deliver...
-

 3.3KMalware
3.3KMalwareNew ZLoader Malware Variant Surfaces with 64-bit Windows Compatibility
Threat hunters have identified a new campaign that delivers the ZLoader malware, resurfacing nearly two years after the botnet’s infrastructure was dismantled...
-

 4.6KMalware
4.6KMalwareMalicious PyPI Packages Slip WhiteSnake InfoStealer Malware onto Windows Machines
Cybersecurity researchers have identified malicious packages on the open-source Python Package Index (PyPI) repository that deliver an information stealing malware called WhiteSnake...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesAllaKore RAT Malware Targeting Mexican Firms with Financial Fraud Tricks
Mexican financial institutions are under the radar of a new spear-phishing campaign that delivers a modified version of an open-source remote access...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesSystemBC Malware’s C2 Server Analysis Exposes Payload Delivery Tricks
Cybersecurity researchers have shed light on the command-and-control (C2) server workings of a known malware family called SystemBC. “SystemBC can be purchased...
-
 2.2KMalware
2.2KMalwareNew CherryLoader Malware Mimics CherryTree to Deploy PrivEsc Exploits
A new Go-based malware loader called CherryLoader has been discovered by threat hunters in the wild to deliver additional payloads onto compromised...
-
 4.3KMalware
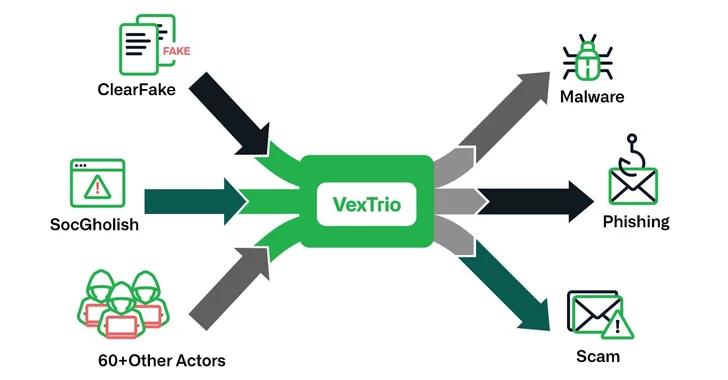
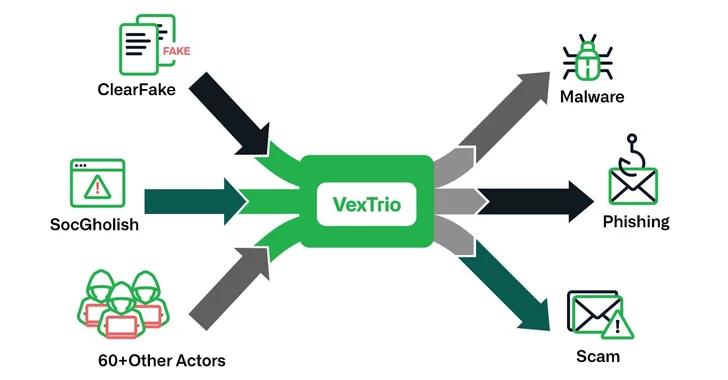
4.3KMalwareVexTrio: The Uber of Cybercrime – Brokering Malware for 60+ Affiliates
The threat actors behind ClearFake, SocGholish, and dozens of other actors have established partnerships with another entity known as VexTrio as part...
-
 3.5KMalware
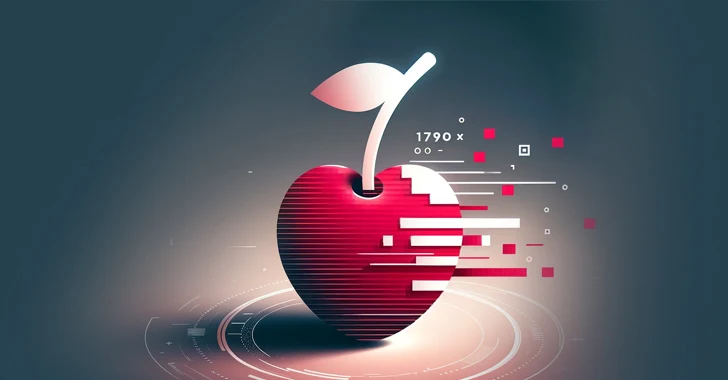
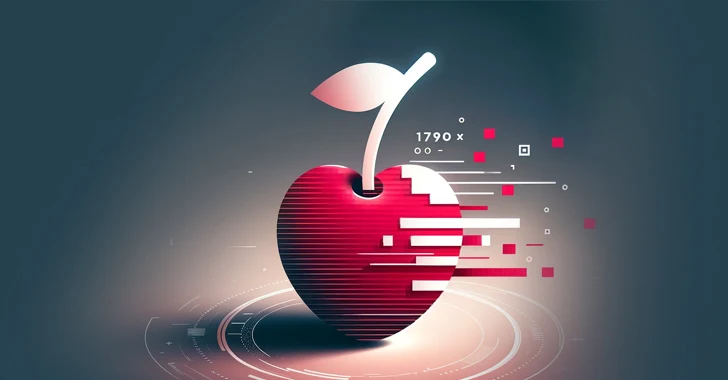
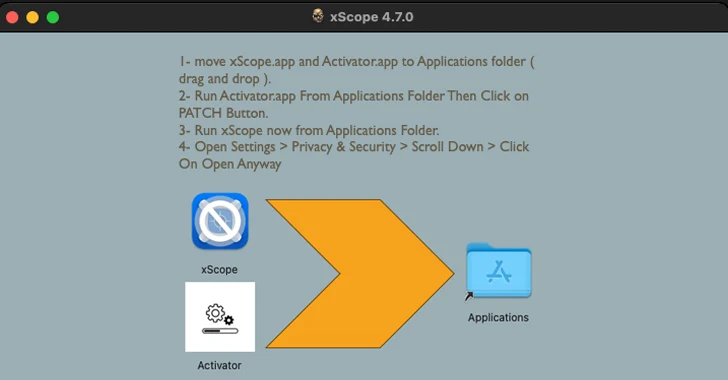
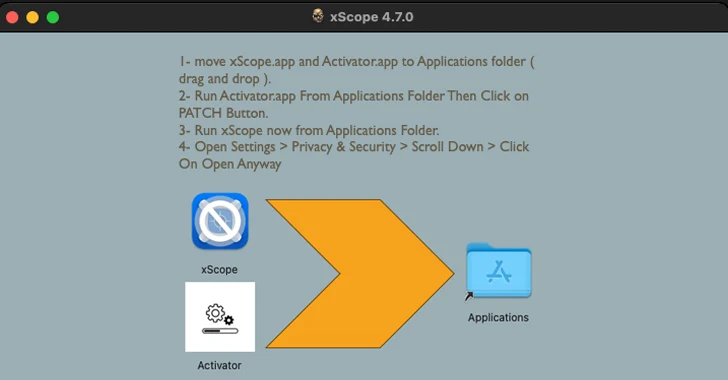
3.5KMalware“Activator” Alert: MacOS Malware Hides in Cracked Apps, Targeting Crypto Wallets
Cracked software have been observed infecting Apple macOS users with a previously undocumented stealer malware capable of harvesting system information and cryptocurrency...
-

 2.4KMalware
2.4KMalwareInvoice Phishing Alert: TA866 Deploys WasabiSeed & Screenshotter Malware
The threat actor tracked as TA866 has resurfaced after a nine-month hiatus with a new large-volume phishing campaign to deliver known malware...
-

 2.2KMalware
2.2KMalwareNew Docker Malware Steals CPU for Crypto & Drives Fake Website Traffic
Vulnerable Docker services are being targeted by a novel campaign in which the threat actors are deploying XMRig cryptocurrency miner as well...
-

 3.9KIncidents
3.9KIncidentsHow to exploit Windows Defender Antivirus to infect a device with malware
Trend Micro’s recent threat hunting efforts have uncovered active exploitation of CVE-2023-36025, a vulnerability in Microsoft Windows Defender SmartScreen, by a new...
-

 1.5KVulnerabilities
1.5KVulnerabilitiesNation-State Actors Weaponize Ivanti VPN Zero-Days, Deploying 5 Malware Families
As many as five different malware families were deployed by suspected nation-state actors as part of post-exploitation activities leveraging two zero-day vulnerabilities...
-
 2.0KMalware
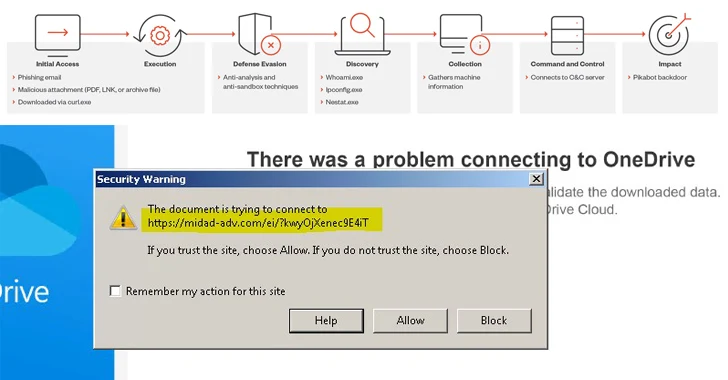
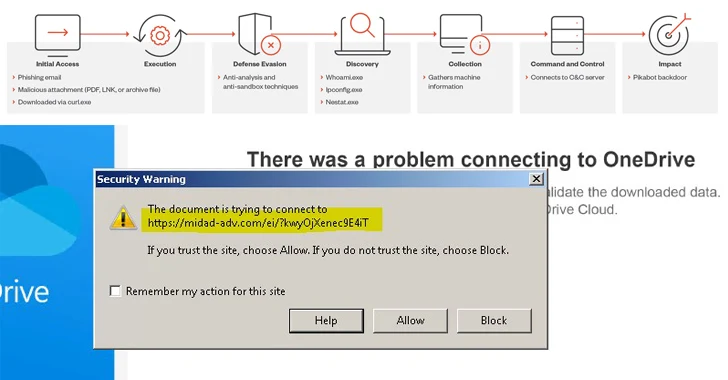
2.0KMalwareAlert: Water Curupira Hackers Actively Distributing PikaBot Loader Malware
A threat actor called Water Curupira has been observed actively distributing the PikaBot loader malware as part of spam campaigns in 2023....
-

 756Cyber Attack
756Cyber AttackPro-Iranian Hacker Group Targeting Albania with No-Justice Wiper Malware
The recent wave of cyber attacks targeting Albanian organizations involved the use of a wiper called No-Justice. The findings come from cybersecurity...






