Search results for "extension "
-

 537Vulnerabilities
537VulnerabilitiesRemote code execution vulnerability in Cisco WebEx browser extensions
Ethical hacking training specialists from the International Institute of Cyber Security have reported the discovery of a new vulnerability in the Cisco...
-

 275News
275NewsThis Open Source Extension Displays Hidden Google Search Results
Google receives tonnes of requests from copyright holders daily for removing infringing content. The company then analyzes the received requests and removes the content that violates copyright claims....
-
 358News
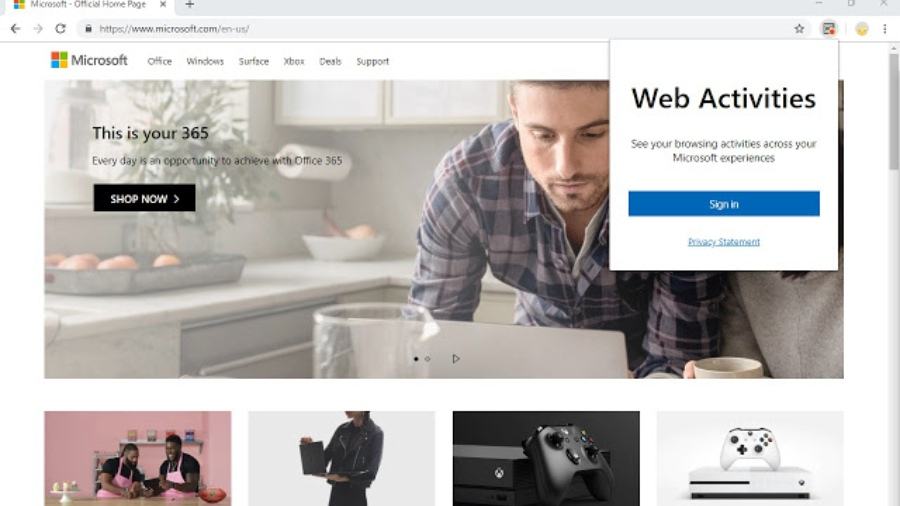
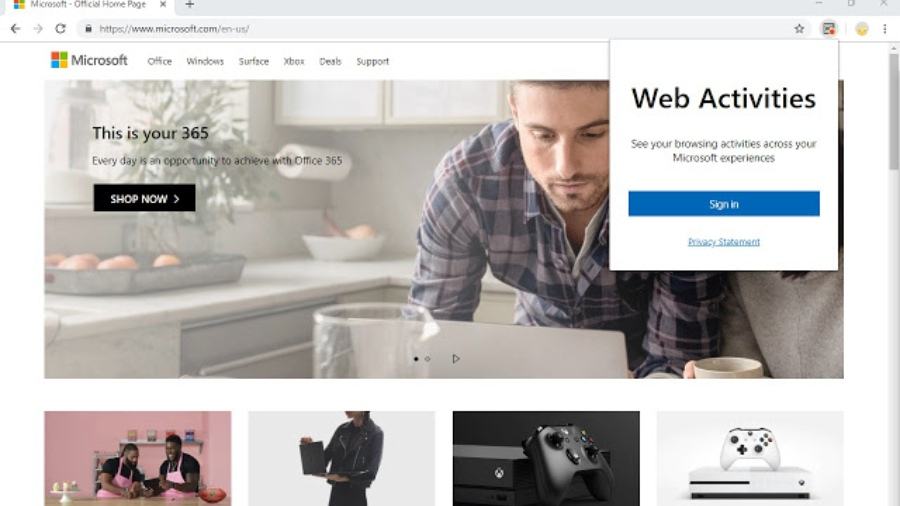
358NewsMicrosoft Launches Windows 10 Timeline Extension For Google Chrome
Windows 10 Timeline, which allows users to track documents and web pages that they have accessed in past, is now available as...
-

 287Password
287PasswordGoogle rolls out Chrome extension to warn you about compromised logins
The new tool aims to help in an age when billions of login credentials are floating around the internet
-

 221News
221NewsFirefox Finally Disables Extensions In Private Mode By Default
Firefox is known for its resolve to offer a Google Chrome alternative that offers reliable privacy solutions as compared to the data-hungry...
-

 467Malware
467MalwareChrome Extension That Steals Credit Cards Numbers Detected On Web Store
A chrome extension that still available on Chrome Web Store steals the payment card information from website forms visited by the users....
-

 298News
298NewsChrome Extension that Steals Credit Card Data Detected
Security researchers have found a Google Chrome extension which steals payment card information and which is still available on Chrome Web Store....
-
 240Data Security
240Data SecurityStart hacking with browser extension
Pentester always uses various tools to gather information of the target. And it is most crucial part before creating any further scenarios....
-
 236News
236NewsHacking Group Uses Chrome Extension, Targets Academic Sector
A hacking group, suspected to be from North Korea, uses a Google Chrome extension to target victims in the academic sector. ZDNet...
-

 241Hacked
241HackedGoogle Chrome Clean Tool Will Remove “Force-Installed Extensions” As Well
Many of you may not know that Google Chrome has its own cleanup tool for finding and removing malware. The tool is...
-
 263Exploitation Tools
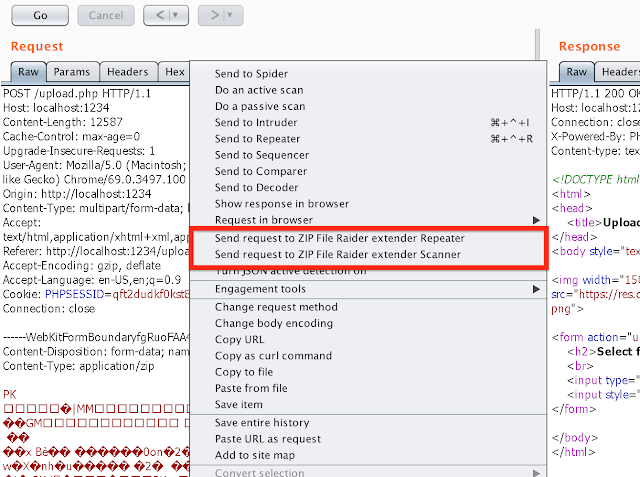
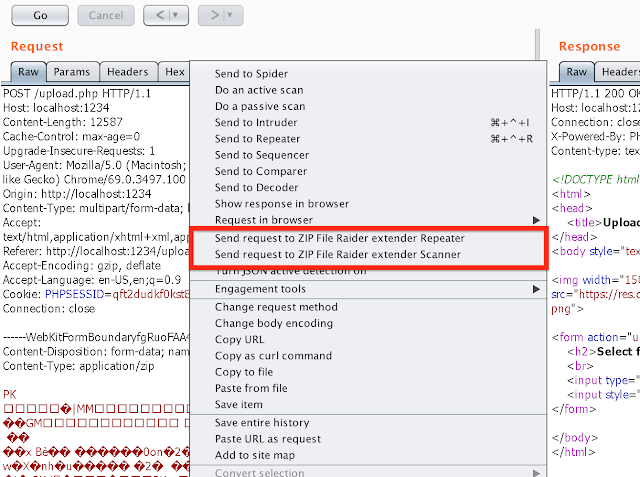
263Exploitation ToolsZIP File Raider – Burp Extension For ZIP File Payload Testing
ZIP File Raider is a Burp Suite extension for attacking web application with ZIP file upload functionality. You can easily inject Burp...
-

 613Lists
613Lists5 Best Chrome Extensions For Reading News In 2019
The internet is the major source of news for many of us, and we spend a lot of time reading articles to...
-

 358Lists
358Lists5 Best Chrome Extensions For Productivity That You Should Use In 2019
Google is the most popular browser around and supports a vast number of extensions as well. Since there are a lot of...
-
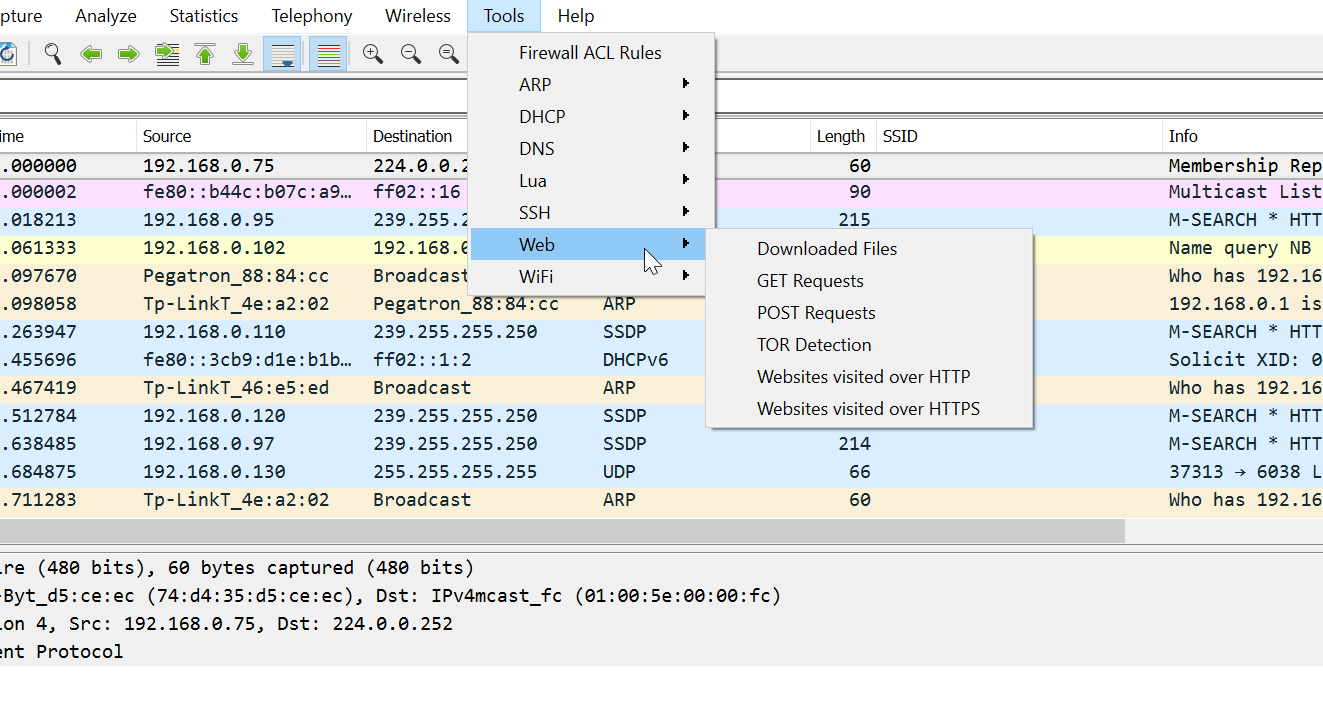
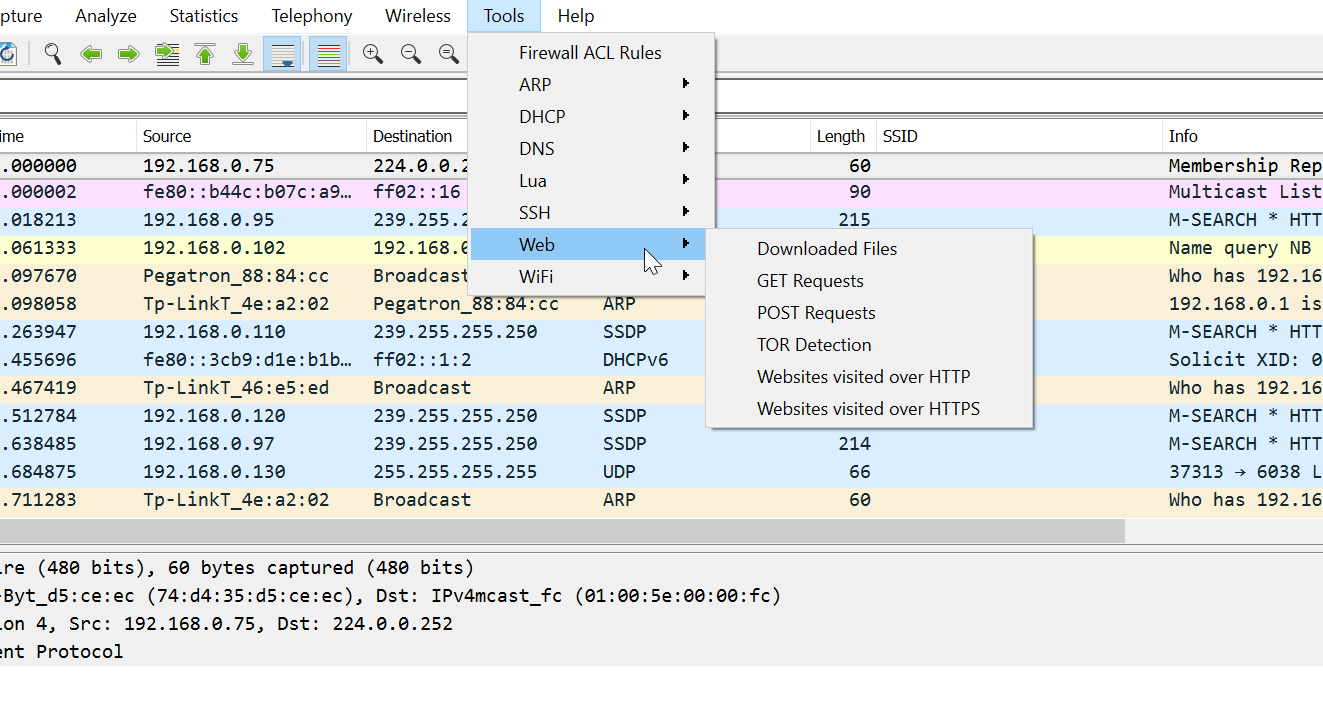 221Packet Manipulation
221Packet ManipulationPA Toolkit – Wireshark Extensions for Penetration Testers
PA Toolkit is a collection of traffic analysis plugins to extend the functionality of Wireshark from a micro-analysis tool and protocol dissector...
-
 255Ransomware
255RansomwareNew Version of GandCrab Ransomware Appends 5 Character Extension To Encrypted Files
A new version of GandCrab Ransomware released, as like the previous version it was not distributed through exploit kits. The distribution method...
-
 221Malware
221MalwareNew PyLocky Ransomware Attack on Various Organization that Encrypt More than 100 File Extensions
Newly spreading PyLocky Ransomware widely targeting and attack various organization by evading the security solutions using its sophisticated attack functionality and its...
-

 314Data Security
314Data SecurityMEGA Chrome extension was hijacked to steal personal information
If you use this extension for the Chrome browser, it is recommended to uninstall it immediately Ethical hacking experts report that the...
-

 387News
387NewsMEGA Chrome extension hacked with cryptocurrency malware
Cloud storage solution MEGA delivered Monero cryptocurrency malware. 21st-century technologies like blockchain are regarded as groundbreaking inventions. However, the security aspect of the...
-
 205Ransomware
205RansomwareA New .NET Ransomware Shrug2 Encrypts Files Around 76 Different Extensions
Malware authors find easy to develop malware using the Microsoft .Net framework, some infamous ransomware like SamSam, Lime and now Shrug2 ransomware...
-

 352Surveillance
352SurveillancePopular Android/iOS apps & Extensions collecting highly personal user data
In May this year, HackRead reported how an Israeli company Unimania was caught collecting personal, Facebook and browsing data of users through Android...
-

 236Incidents
236IncidentsVPN Hola Chrome Extension Hijacked
The uploaded spoof version of Chrome Web Store targeted users of MyEtherWallet, the popular encrypted online wallet service. The Google Chrome extension...






